OpenAI Just Launched Daybreak — and the AI Vulnerability Discovery Market Now Has Four Vendors and Twenty-Plus Partners
OpenAI launched Daybreak on May 11, 2026 — an AI vulnerability discovery platform with three GPT-5.5 models and a 20+ partner roster including Cisco, Cloudflare, CrowdStrike, Palo Alto, Snyk, Tenable, and Rapid7. The AI defender market just formed.
OpenAI just answered Anthropic's Mythos with Daybreak — three GPT-5.5 models including a permissive GPT-5.5-Cyber for red teaming, plus a partner roster that pulls in every major enterprise security vendor. With Microsoft's MDASH and F5's DepthFirst already operational, the AI vulnerability discovery market now has four serious vendors and a flotilla of integrations.
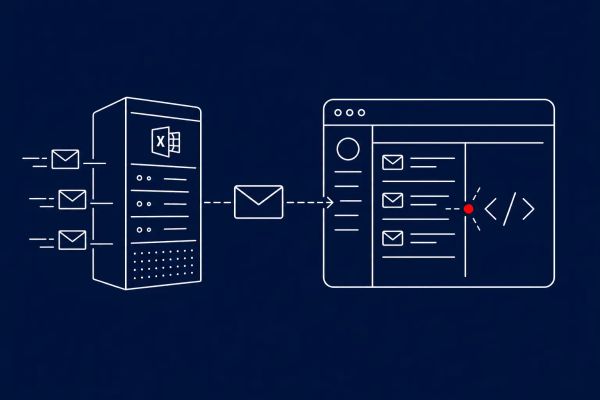
SAN FRANCISCO, CA — OpenAI launched Daybreak on May 11, 2026, a cybersecurity initiative that bundles its GPT-5.5 model family with Codex Security to identify vulnerabilities, validate patches, and feed audit-ready evidence back to enterprise security workflows. Daybreak ships with three model tiers: standard GPT-5.5 with default safeguards, GPT-5.5 with Trusted Access for Cyber for verified defensive work in authorized environments, and GPT-5.5-Cyber, a permissive model intended for red teaming, penetration testing, and controlled validation. The initiative builds on OpenAI's April 2026 GPT-5.4-Cyber release, which the company says has contributed to fixing more than 3,000 vulnerabilities. CEO Sam Altman framed the launch in a post on X: "AI is already good and about to get super good at cybersecurity; we'd like to start working with as many companies as possible now to help them continuously secure themselves."
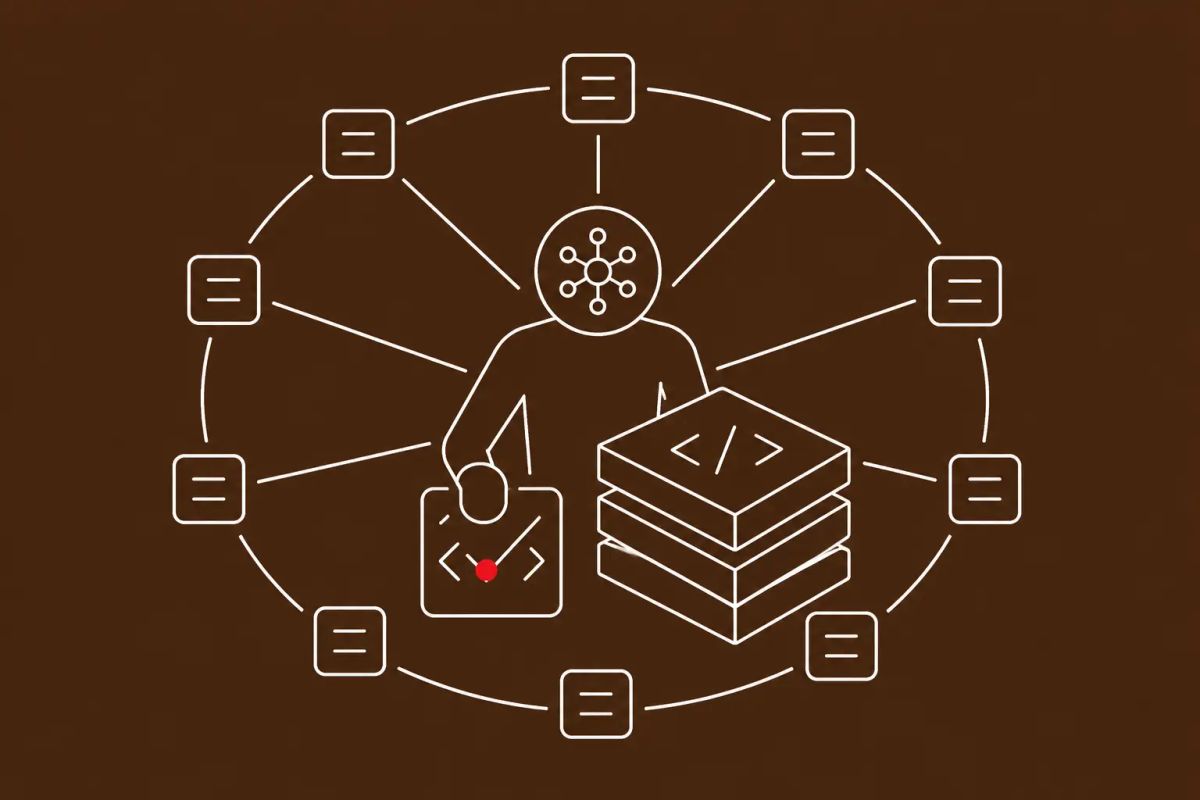
The partner roster is the part that should make the market structure obvious. Under the Trusted Access for Cyber program, OpenAI is integrating Daybreak capabilities with — at minimum — Akamai, Cisco, Cloudflare, CrowdStrike, Fortinet, Oracle, Palo Alto Networks, Zscaler, Intel, Qualys, Rapid7, Tenable, Trail of Bits, SpecterOps, SentinelOne, Okta, Netskope, Snyk, Gen Digital, Semgrep, and Socket. That is essentially the enterprise security industry. Daybreak lands alongside Anthropic's Mythos and Project Glasswing (publicly limited-preview since April 2026, with Apple, Microsoft, Google, and Amazon among the early users), Microsoft's MDASH, which found 16 of May's Patch Tuesday CVEs, F5/DepthFirst's autonomous auditor, which discovered the 18-year-old NGINX Rift critical RCE in roughly six hours, and Palo Alto Networks' Mythos-assisted internal scan that produced 75 flaws across 26 CVEs in a single run. Four vendors, one market, and the integrations stack from here are exactly the ones every CISO already buys from.
The Market Structure Just Formed
Four vendors in the same six weeks — Anthropic Mythos, OpenAI Daybreak, Microsoft MDASH, and F5/DepthFirst — is no longer a series of demos. It is a market. The CyberSignal has been tracking the operational side of AI vulnerability discovery as Microsoft and Palo Alto Networks pointed it at their own code and as F5's DepthFirst surfaced an 18-year-old critical RCE in NGINX in six hours. Daybreak is the entry of the largest frontier-model vendor with the broadest partner reach into the same category. With pricing undisclosed, the immediate competitive picture is about distribution and access tiers more than price — Daybreak is publicly available, Mythos remains in limited preview, MDASH is in limited private preview with select Microsoft customers, and DepthFirst is sold through F5. Buyers now have real choice.
The partner list is the part that signals where the integration battle will be fought. Daybreak's Trusted Access for Cyber roster is essentially the enterprise security stack: Cisco, Cloudflare, CrowdStrike, Palo Alto Networks, Fortinet, Akamai, Zscaler, Oracle, Tenable, Rapid7, Qualys, Snyk, SentinelOne, Okta, Netskope, Trail of Bits, SpecterOps, Semgrep, Socket, Gen Digital, Intel. That is the list of vendors most enterprises already buy from. If your existing security tooling pulls Daybreak's AI capability into its workflow under the partnership umbrella, you may already be a Daybreak customer indirectly — and your security data may already be flowing through OpenAI's processing layer. That is a vendor-management and data-flow question that should be on every CISO's near-term checklist, not a hypothetical.
GPT-5.5-Cyber Is a Permissive Model. That Is Both the Feature and the Question.
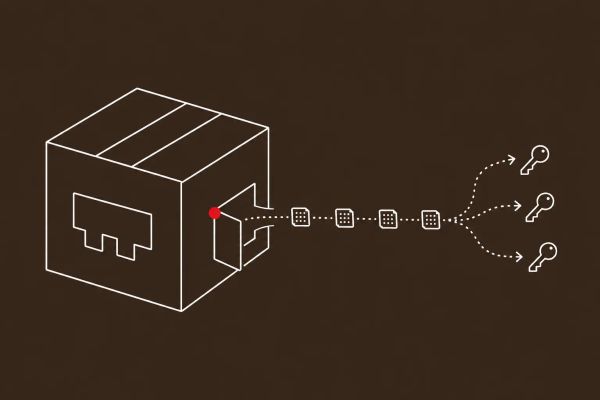
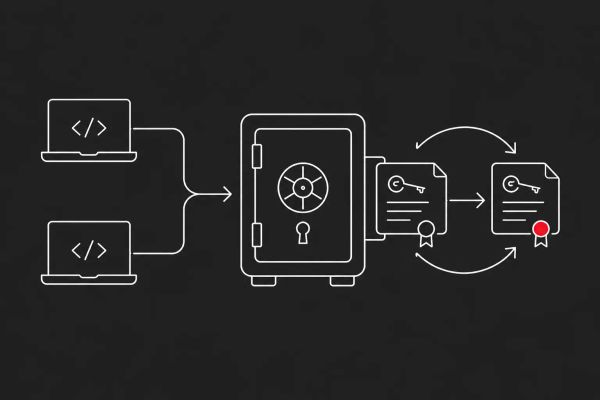
Daybreak's three-tier model is more meaningful than it looks. Standard GPT-5.5 keeps OpenAI's usual safeguards. GPT-5.5 with Trusted Access for Cyber is the middle tier, intended for verified defensive work in authorized environments. GPT-5.5-Cyber is the explicitly permissive model, designed for red teaming, penetration testing, and controlled validation. The capability split is honest about what the work requires — a model that will not help you build an exploit is no use to a red team trying to validate a patch — but it also means OpenAI now has a cyber-capable model in production whose entire premise is permissiveness about offensive operations within authorized contexts. The control surface is the "within authorized contexts" part.
The broader curve this fits into is the AI-on-both-sides dynamic The CyberSignal has been tracking: Google's disclosure of the first AI-generated zero-day in the wild, Germany's warning about a Chinese AI 'superhacker' under state development, Anthropic's own model-security incidents like ClaudeBleed, and Kaspersky's finding of apparently LLM-developed code in a North Korean Kimsuky backdoor. The honest read on Daybreak — and on Mythos, and on MDASH — is that the defensive tooling is the visible side of a capability that exists on the offensive side too. HackerOne CPO Nidhi Aggarwal told Cybernews that "AI-driven offensive security is going mainstream, and continuous testing is moving from competitive advantage to table stakes." Security researcher Himanshu Anand was more blunt, telling The Hacker News that "the 90 day disclosure policy is dead" in a world where "AI can turn a patch diff into a working exploit in 30 minutes." Defenders should plan for both.
What CISOs Should Actually Do About a Four-Vendor AI Defender Market
The operational response is less dramatic than the headlines suggest. Buyers now have a vendor-selection problem rather than a capability question. Pilot Daybreak through one of your existing partner relationships — Cisco, Cloudflare, CrowdStrike, Palo Alto Networks, Snyk, or whichever security vendor you already work with at scale — rather than starting from a direct OpenAI relationship. Compare it head-to-head with Anthropic Mythos integrations and Microsoft MDASH if you are a Microsoft enterprise customer. Gartner VP analyst John Watts told CIO Dive that Daybreak "competes more directly with application security, posture management and AI-enabled application security testing capabilities" and "will complement usage of these tools rather than fully replace them." That is the right level to evaluate at — Daybreak is not the new AppSec stack, it is a layer that sits inside or alongside it.
For everyone else — even organizations not planning to buy any of these tools directly — the secondary effects are the ones that change planning. Vendor patch cadences will continue to accelerate as more vendors point AI at their own code, as visible in Microsoft's May Patch Tuesday haul and Palo Alto's single-scan 26-CVE disclosure. Adversary capability is on the same curve. Patch SLAs written before this year were calibrated for a slower world and need to be tightened. Pre-script the "AI-discovered critical CVE in our stack" scenario, including the part where the AI that found it is a vendor your supplier already integrates with. And audit which of your existing security vendors are on Daybreak's partner list, Mythos's partner list, or both — that determines whose AI is running over your environment whether you signed an OpenAI contract or not.
The CyberSignal Analysis
Signal 01 — The AI Vulnerability Discovery Market Has Four Vendors. Treat It Like a Procurement Problem, Not a Hype Cycle.
Daybreak's launch closes the founder phase. Buyers now have four credible vendors — Anthropic Mythos, OpenAI Daybreak, Microsoft MDASH, F5/DepthFirst — and an enterprise-security partner roster that reaches every major vendor a typical CISO already uses. The right move is procurement discipline, not pilot-everything. Evaluate Daybreak through an existing partner relationship; compare it head-to-head with Mythos integrations and, for Microsoft customers, MDASH; treat Gartner's framing accurately, as complement to existing AppSec, posture management, and AI-enabled AST capabilities, not as a replacement stack. The "who is allowed to use my code as a prompt" question is also now a real vendor-data-flow question — if your CDN, EDR, and firewall vendors are all on Daybreak's list, OpenAI may be processing pieces of your environment whether you signed up or not.
Signal 02 — GPT-5.5-Cyber Is the Offensive-Mirror Reality CISOs Should Plan Around
Daybreak ships a permissive cyber model intended for red teaming and exploit validation. That same capability — minus the "authorized environment" wrapper — is what adversaries are pointing at the same codebases. The CyberSignal has tracked this pattern from Google's first AI-generated zero-day to Germany's Chinese 'superhacker' warning to Kaspersky's LLM-developed Kimsuky backdoor. The strategic implication for CISOs is patch-cadence: SLAs written in 2024 and 2025 assumed a slower threat-discovery curve than the one Daybreak, Mythos, and MDASH now make standard. Tighten critical-severity patch windows now, pre-script the "AI-discovered CVE in our stack" scenario, and brief boards that AI vulnerability discovery is now an operational reality on both sides — not a future risk.
What to Do This Week
- Audit which of your existing security vendors are on the Trusted Access for Cyber partner list — Akamai, Cisco, Cloudflare, CrowdStrike, Fortinet, Oracle, Palo Alto Networks, Zscaler, Intel, Qualys, Rapid7, Tenable, Trail of Bits, SpecterOps, SentinelOne, Okta, Netskope, Snyk, Gen Digital, Semgrep, Socket. If multiple of your vendors are on it, OpenAI is already in your security workflow indirectly; document the data-flow implications.
- If you are evaluating AI vulnerability discovery, treat it as a four-vendor selection problem — Anthropic Mythos, OpenAI Daybreak, Microsoft MDASH, F5/DepthFirst. Pilot Daybreak through an existing partner relationship rather than direct OpenAI; pricing is undisclosed and access tiers will shape the deal.
- For DevSecOps and AppSec teams: evaluate Daybreak's three-stage workflow (threat prioritization, scoped patch generation and testing, audit-ready evidence) against existing AppSec, SAST/DAST, and SCA tools. Per Gartner, Daybreak complements these tools rather than replacing them — fit it into the existing remediation kill chain, not on top of it.
- Tighten critical-severity patch SLAs to account for the compressed discovery-to-exploitation window AI tooling produces on both sides. Pre-script the "AI-discovered critical CVE in something we depend on" scenario in your vulnerability management playbook, and the "AI audit finds an old flaw in our own code" scenario alongside it.
- For procurement and vendor management: the access tiers — GPT-5.5, GPT-5.5 with Trusted Access for Cyber, GPT-5.5-Cyber — will have different pricing and governance profiles. Negotiate access tier explicitly, not just product. For organizations subject to EU AI Act or analogous regulation, GPT-5.5-Cyber's permissive red-teaming posture raises compliance questions worth raising with legal counsel.