OpenAI Is Rotating Every Code-Signing Certificate It Has — Mini Shai-Hulud Reached Two Employee Laptops
OpenAI confirmed two employee devices were compromised in the Mini Shai-Hulud supply chain attack, exposing code-signing certificates for its apps. OpenAI is rotating every certificate, and macOS users must update before June 12, 2026.
The Mini Shai-Hulud supply chain campaign that compromised more than 170 npm and PyPI packages just claimed its most prominent confirmed victim. Two OpenAI employees installed a poisoned TanStack package, and the repositories they could reach held the certificates OpenAI uses to sign its desktop and mobile apps. Now the company is rotating all of them — and macOS users have a deadline.
SAN FRANCISCO, CA — OpenAI confirmed on May 14, 2026 that two employee devices in its corporate environment were compromised in the Mini Shai-Hulud supply chain attack — the TeamPCP-attributed campaign that poisoned more than 170 npm and PyPI packages beginning May 11, 2026, which The CyberSignal covered in our original reporting on the Mini Shai-Hulud worm. The two employees installed poisoned versions of TanStack packages during the roughly six-minute window in which 84 malicious package versions were published. OpenAI engaged a third-party digital forensics and incident response firm, which confirmed "unauthorized access and credential-focused exfiltration activity" in a limited subset of internal source code repositories the two employees could access. Those repositories contained code-signing certificates for OpenAI's iOS, macOS, Windows, and Android products — including ChatGPT Desktop, Codex, and Atlas.
As a precaution, OpenAI is rotating all of its code-signing certificates. The most time-sensitive consequence falls on macOS users: they must update ChatGPT Desktop, the Codex App, Codex CLI, and Atlas before June 12, 2026, after which Apple's notarization protections will block applications signed with the old certificates from launching or updating. Windows and iOS users are not affected and need to take no action. OpenAI says it has found no evidence that customer data, production systems, intellectual property, or deployed software were touched, and no evidence that the exposed certificates have been misused — though it has said it may accelerate revocation if misuse appears. The detail that should not be lost in the reassurance: the two compromised devices were in the middle of a phased rollout of new supply chain security controls OpenAI began after an earlier incident involving the Axios npm package, and had not yet received the updated configurations that would have blocked the malicious download.
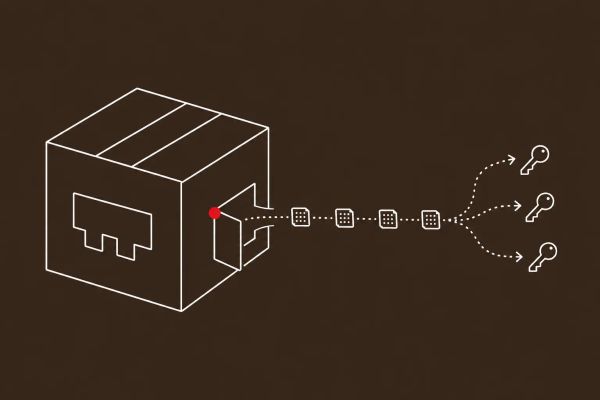
Code-Signing Certificates Are the Crown Jewels, and They Were in a Developer-Reachable Repo
The reason this incident matters more than the typical supply chain compromise is what the attackers reached. Code-signing certificates are the cryptographic proof that software genuinely comes from OpenAI — they are the trust anchor between the company and every end user who installs its apps. The forensic finding here is not that those certificates were stolen and used; OpenAI says it has seen no misuse. It is that the certificates were sitting in source code repositories that an ordinary developer endpoint could access, which means a single compromised employee laptop put platform-level signing infrastructure within reach. That is the structural lesson, and it generalizes far beyond OpenAI: if your code-signing certificates are reachable from a developer workstation, your signing infrastructure is exactly as secure as your least-patched developer's machine.
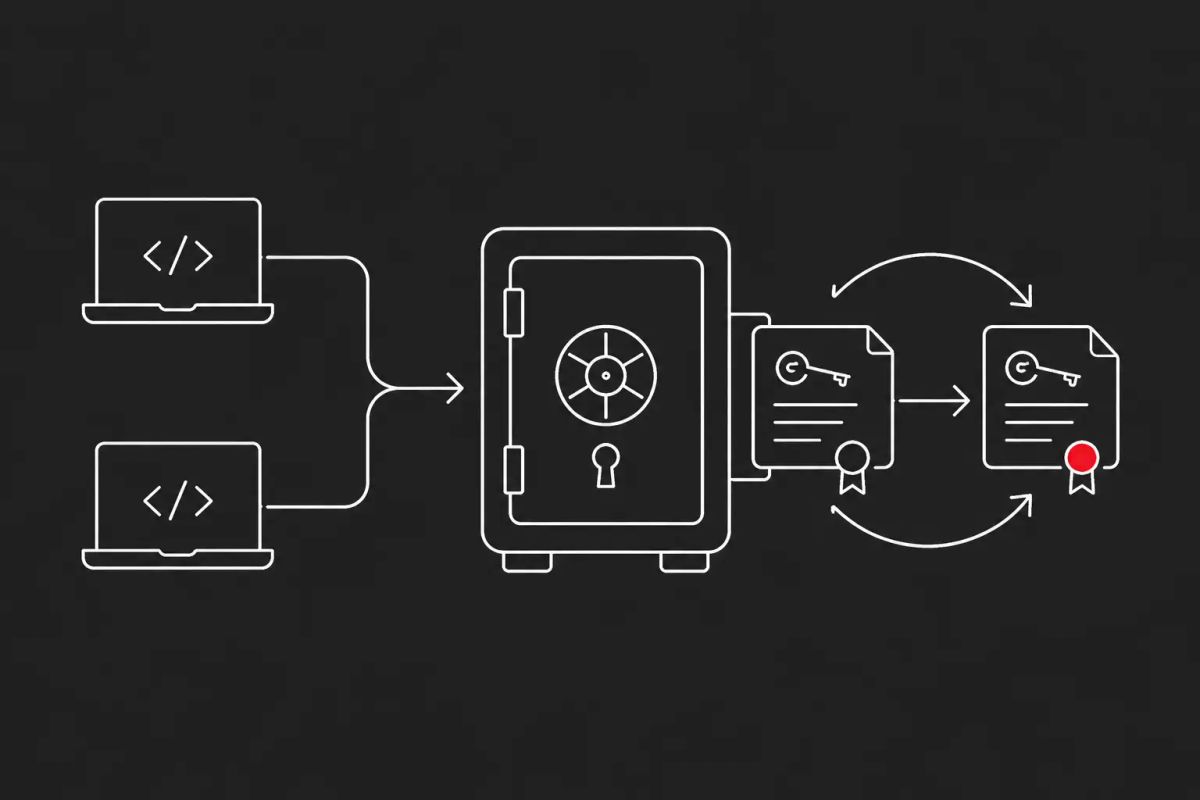
OpenAI's response is the right one and worth studying as a playbook. Rather than wait to see whether the certificates are abused, the company is rotating all of them and coordinating with Apple to halt new notarizations of macOS apps signed with the affected material. That coordination is the part most organizations are not prepared for — a code-signing compromise is not something you remediate alone, because the platform notarization layer (Apple, Microsoft, Google) is part of your trust chain. The June 12 macOS deadline exists because after that date Apple's notarization protections will actively block the old-certificate apps. Any vendor that signs software for distribution should pre-script this exact scenario: certificate rotation, platform-provider coordination, and a hard end-user update deadline.
The Failure Mode Is 'The Rollout Was Still in Flight'
The most instructive detail in OpenAI's advisory is also the most uncomfortable. After an earlier incident involving the Axios npm package — itself attributed to North Korean actors, which The CyberSignal examines separately — OpenAI accelerated a set of supply chain security controls: hardening sensitive credential material in its CI/CD pipeline, deploying package-manager configurations with controls like npm's minimumReleaseAge, and adding software to validate package provenance. The Mini Shai-Hulud compromise happened during that phased deployment. The two affected devices had not yet received the updated configurations that would have prevented the malicious package from installing. This is not a story about an organization that ignored supply chain risk — it is a story about one of the most security-mature companies in the world getting caught in the gap between detection and full operational hardening.
For every CISO, that is the takeaway that should change behavior. Supply chain security controls do not protect anyone until they have actually reached every endpoint. A phased rollout is, by definition, a window of partial coverage — and attackers operating at the speed of the Mini Shai-Hulud campaign, which published 84 malicious versions in roughly six minutes, will land inside that window. The same lesson runs through The CyberSignal's recent coverage of developer workstations as the new attacker beachhead: the developer environment is now crown-jewel infrastructure, and "we are in the middle of deploying the fix" is not a defense. If you have a supply chain hardening program in flight, the urgent question is not whether it is good — it is which endpoints it has not reached yet.
What macOS Users and Software Vendors Need to Do
For anyone running OpenAI's macOS applications, the action is simple and time-bound: update ChatGPT Desktop, the Codex App, Codex CLI, and Atlas before June 12, 2026, and do it only through the apps' built-in update mechanisms or openai.com. The deadline creates a predictable social-engineering opportunity — attackers impersonating "urgent OpenAI certificate update" prompts — so the rule for users is to update through known-good channels and ignore any update solicitation that arrives by email or from an unfamiliar source. Windows and iOS users have nothing to do.
For software vendors, the broader instruction is to treat OpenAI's incident as a free tabletop exercise. Audit where your code-signing certificates actually live: if they are in repositories reachable from developer endpoints, that is the finding to fix this quarter. Implement hard separation between code-signing infrastructure and developer environments, so certificates are never accessible from a workstation. Audit your build infrastructure's OIDC trust scope — the Mini Shai-Hulud campaign succeeded upstream in part because TanStack's trusted-publisher configuration granted trust at the repository level rather than to a specific protected branch and workflow. And write the certificate-rotation runbook now, including the platform-provider coordination step, because the time to figure out how to reach Apple's notarization team is not during the incident.
The CyberSignal Analysis
Signal 01 — If Code-Signing Certificates Are Reachable From a Developer Laptop, Rotation Is Only a Matter of Time
OpenAI's breach reduces to one structural fact: platform-level code-signing certificates were stored where a compromised developer endpoint could reach them. Every software vendor should run that audit this quarter. Code-signing infrastructure should be isolated from developer environments entirely, with certificates accessible only through tightly controlled, logged, separate systems. Pre-script the full rotation scenario — revoke, re-sign, coordinate with Apple, Microsoft, and Google notarization teams, and communicate a hard update deadline to end users — because a code-signing compromise is not a solo remediation, and the coordination steps are the ones organizations are least prepared for. OpenAI executed this well; the lesson is to be able to execute it before you need to.
Signal 02 — A Supply Chain Hardening Program That Is Still Rolling Out Is a Window, Not a Wall
The most transferable lesson is the failure mode. OpenAI was actively deploying the controls — minimumReleaseAge, provenance validation, CI/CD credential hardening — that would have stopped this, and the breach landed on the devices the rollout had not yet reached. For CISOs with supply chain programs in flight, the operational priority is coverage velocity and gap visibility: know exactly which endpoints lack the new configuration, and treat that population as your highest-risk surface until the rollout completes. The Mini Shai-Hulud campaign published 84 malicious versions in roughly six minutes — attackers move at a speed that punishes partial deployment. Pair this with The CyberSignal's coverage of developer workstations as the strategic beachhead: the developer environment is crown-jewel infrastructure, and partial hardening is the attack window.
What to Do This Week
- If you run OpenAI's macOS apps — ChatGPT Desktop, Codex App, Codex CLI, Atlas — update them before June 12, 2026, using only the built-in update mechanism or openai.com. Ignore any "certificate update" prompt that arrives by email or from an unfamiliar source.
- All software vendors: audit where your code-signing certificates live. If they are in repositories reachable from developer endpoints, isolate them now — code-signing infrastructure should never be accessible from a developer workstation.
- Write or rehearse your code-signing certificate rotation runbook, including the step most organizations miss: coordinating with platform notarization providers (Apple, Microsoft, Google) and communicating a hard end-user update deadline.
- If you have a supply chain security program in phased rollout — npm minimumReleaseAge, provenance validation, CI/CD credential hardening — inventory exactly which endpoints have not yet received it, and treat that population as your highest-risk surface until coverage is complete.
- Audit your build infrastructure's OIDC trust scope. Trusted-publisher configurations should grant trust to a specific protected branch and workflow, not at the repository level — the broad scope is part of how Mini Shai-Hulud succeeded upstream.