Microsoft Confirmed an Exchange Server Zero-Day Is Under Active Attack — and the 2016/2019 Patch Will Only Reach Period 2 ESU Customers
Microsoft confirmed active exploitation of CVE-2026-42897, a high-severity XSS zero-day in on-prem Exchange OWA, with no permanent patch — only EEMS mitigation. The eventual fix for Exchange 2016 and 2019 will only reach Period 2 ESU customers.
Microsoft confirmed active exploitation of a high-severity cross-site scripting flaw in on-premises Exchange Server's web client. The temporary mitigation is automatic for most customers and breaks Print Calendar, inline images, and OWA light. The permanent patch — when it arrives — will reach Exchange 2016 and 2019 only through the Period 2 Extended Security Update tier. Period 1 customers will not get it.
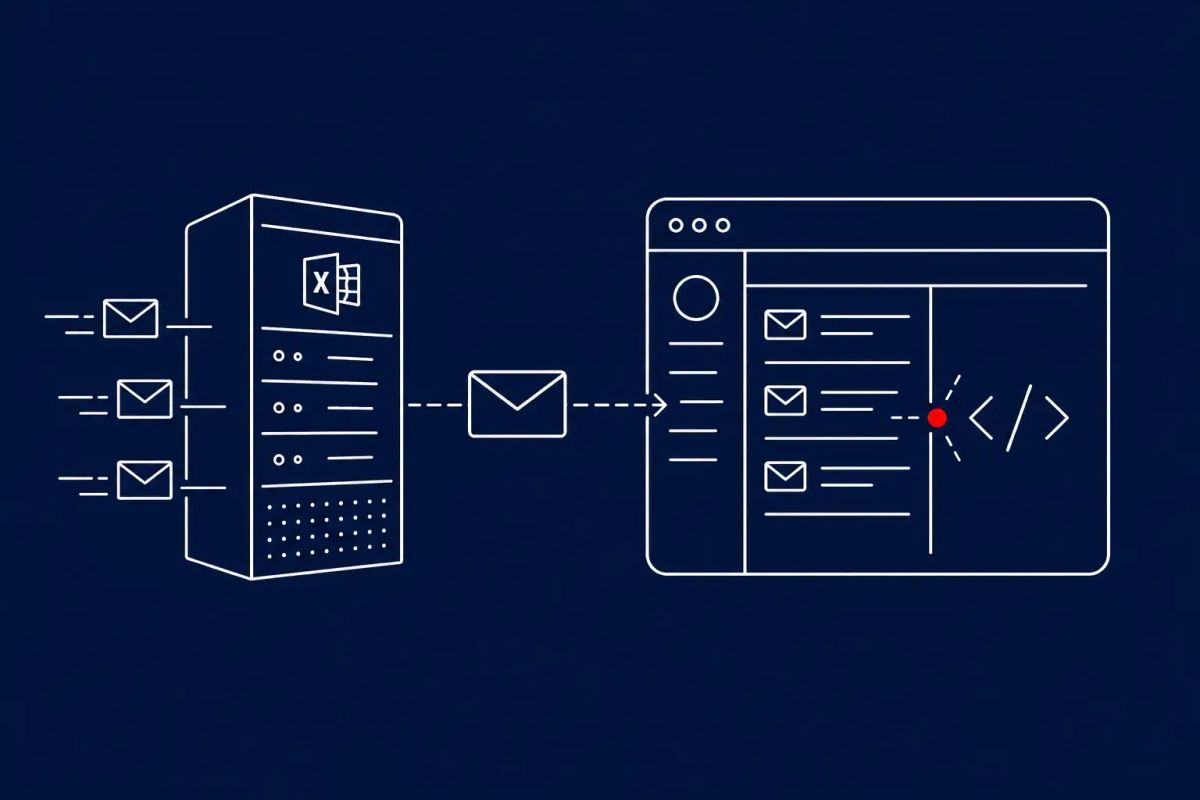
REDMOND, WA — Microsoft disclosed on May 14, 2026 that CVE-2026-42897 — a high-severity cross-site scripting and spoofing vulnerability in on-premises Exchange Server's Outlook Web Access, scored CVSS v3.1 8.1 — is under active exploitation in the wild. The company tagged the issue with its highest exploitation-confidence rating, "Exploitation Detected." Affected versions are Exchange Server Subscription Edition (SE) RTM, Exchange Server 2019 (CU14 and CU15), and Exchange Server 2016 (CU23); Exchange Online is not impacted. Microsoft has not yet released a permanent patch. The advisory and an Exchange team blog post point organizations to the Exchange Emergency Mitigation Service (EEMS) for an automatic temporary fix, and to the Exchange On-premises Mitigation Tool (EOMT) for air-gapped environments.
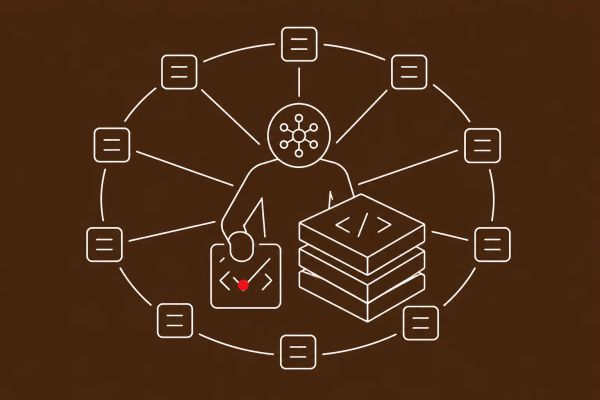
Exploitation works by sending a specially crafted email to a target; when the recipient opens it in Outlook Web Access under what Microsoft describes only as "certain interaction conditions," arbitrary JavaScript runs in the victim's browser context. Microsoft has not disclosed those conditions, the attackers' identity, the volume of confirmed compromises, or victim organizations. The vulnerability was reported by an anonymous researcher. The detail buried at the bottom of Microsoft's guidance is the one defenders should not miss: the eventual permanent patch for Exchange Server SE will be publicly available, but the patches for Exchange Server 2016 (CU23) and Exchange Server 2019 (CU14/CU15) will be released only to customers enrolled in the Period 2 Extended Security Update program. Period 1 ESU ended in April 2026. Customers who were on Period 1 only and did not enroll in Period 2 will not receive this update.
One Crafted Email, JavaScript in the Browser, No Patch Yet
The mechanics are uncomfortably simple. An attacker sends a crafted email; a recipient opens it in Outlook Web Access; under conditions Microsoft has chosen not to disclose, the message executes attacker-controlled JavaScript in the recipient's browser context. JavaScript running in the OWA session means access to whatever the user can do in OWA — read mail, send mail, manipulate calendars, in some configurations trigger flows that lead to further compromise. Microsoft tags the vulnerability with its "Exploitation Detected" assessment, the highest of its exploitation-confidence ratings, which means the company has direct evidence of attacks in the wild rather than just plausible exploitation. There is no permanent patch yet — only the temporary EEMS mitigation.
That this lands on on-premises Exchange specifically is the part that should not surprise anyone. Exchange Server has been a sustained nation-state target for years, from ProxyLogon and ProxyShell in 2021 through a steady cadence of high-severity zero-days since. Compromised Exchange is the position from which an attacker reads every executive email, harvests credentials, sets persistent inbox rules, and pivots into the rest of the environment. This is exactly the class of target on-prem Exchange has become — a piece of critical-infrastructure-grade software with a permanent place on every credible threat actor's roadmap, and a vendor response that increasingly leans on "apply this mitigation now, patch eventually."
The Permanent Patch Has a Price Tag for Exchange 2016 and 2019
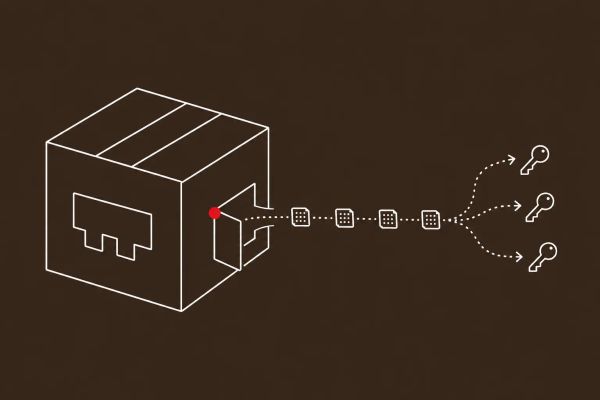
The detail most coverage missed is the part that will hurt budgets. Microsoft's guidance is explicit: when the permanent fix arrives, Exchange Server Subscription Edition will get a publicly available security update, but Exchange Server 2016 (CU23) and Exchange Server 2019 (CU14/CU15) will only receive the update through the Period 2 Extended Security Update program. Period 1 ESU — the entry tier — ended in April 2026. Organizations that bought only Period 1 ESU, or that never enrolled, will not receive this update. For an actively-exploited zero-day with no other path to a permanent fix, that is a material gap, and it is going to come up in finance conversations during the second half of this year.
The practical implications fork by version. If you are on Exchange Server SE, you will get a public patch in due course; your job is to keep EEMS enabled, accept the trade-offs, and watch for Microsoft's release. If you are on Exchange 2016 or 2019 with Period 2 ESU, you will get the patch and should plan its deployment now. If you are on Exchange 2016 or 2019 without Period 2 ESU, you have a hard decision: enroll, migrate to Exchange Server SE or Exchange Online, or operate indefinitely on the temporary EEMS mitigation against a vulnerability the vendor itself rates as actively exploited. Microsoft's "mitigation-first, patch-later" approach to Exchange is now standard. Brief your CFO.
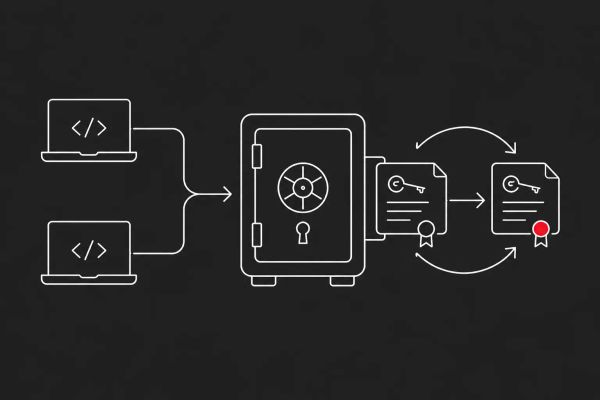
Apply EEMS Today, Accept the Trade-Offs, and Verify
There is no exotic remediation here. For most organizations EEMS has been enabled by default since September 2021, which means mitigation M2.1.x should already be in place. The job is to verify it. Run the Exchange Health Checker script and inspect the EEMS section of the HTML report; if M2.1.x shows as "Applied," the server is covered. The "Mitigation invalid for this exchange version" note in the Description field is cosmetic — Microsoft has confirmed mitigation still applies when status is "Applied." For air-gapped or disconnected environments, run the Exchange On-premises Mitigation Tool script — Get-ExchangeServer | Where-Object { $_.ServerRole -ne 'Edge' } | .\EOMT.ps1 -CVE 'CVE-2026-42897' is the all-fleet form, with Edge role correctly excluded. Pre-March-2023 Exchange Server versions will not pull new mitigations from EEMS and need the manual path regardless.
Accept the functional trade-offs, brief your IT operations team, and document them. OWA Print Calendar will not work; users should screenshot calendars or use Outlook Desktop. Inline images may not render correctly in the OWA reading pane; senders should attach images instead. OWA light, accessed via the /?layout=light URL, will not work properly — Microsoft notes it is a deprecated feature and not for production. None of these are good user-experience outcomes, but all of them are acceptable trade-offs to keep an actively-exploited zero-day mitigated. This is the same critical-infrastructure-vulnerability pressure visible in the Cisco Catalyst SD-WAN CVSS 10.0 authentication bypass that is also under active exploitation right now and the NGINX Rift critical RCE — on-prem foundational software is the 2026 zero-day battleground.
The CyberSignal Analysis
Signal 01 — Apply EEMS Now, Then Verify. Cosmetic 'Invalid' Messages Are Not the Problem; Disabled EEMS Is.
CVE-2026-42897 is a high-severity, actively-exploited zero-day with no permanent patch. The first action this week is to verify EEMS is enabled (it is by default, but may have been disabled by your team), confirm M2.1.x is in "Applied" status via the Exchange Health Checker report, and accept the OWA Print Calendar, inline image, and OWA light side effects. For air-gapped environments, run the EOMT script with CVE-2026-42897. For Exchange versions older than March 2023, EEMS will not pull new mitigations and EOMT is required. Brief IT operations on the functional trade-offs and document them — this is acceptable temporary cost, not a reason to delay.
Signal 02 — The Period 2 ESU Exclusion Is a Finance Decision, Not an IT One
The eventual permanent patch for Exchange Server 2016 and 2019 will be available only to customers enrolled in the Period 2 Extended Security Update program. Period 1 ESU ended in April 2026; Period 1-only customers will not get this update. For organizations with significant on-prem 2016/2019 dependencies, that is a budget conversation that needs to happen now, with three options: enroll in Period 2 ESU, migrate to Exchange Server SE or Exchange Online, or operate indefinitely on EEMS mitigation against an actively-exploited bug with no permanent fix. Brief CFOs and boards on the trade-off explicitly; this is a strategic-level Exchange decision, not a Patch Tuesday line item.
What to Do This Week
- Verify EEMS is enabled on every on-prem Exchange Server — it is by default since September 2021, but may have been disabled. Run the Exchange Health Checker script and confirm mitigation M2.1.x shows as "Applied" in the HTML report.
- If EEMS is disabled or the server is air-gapped or disconnected, run the Exchange On-premises Mitigation Tool (EOMT) script with CVE-2026-42897 as the parameter. For Exchange versions older than March 2023, EOMT is required regardless because EEMS will not pull new mitigations.
- Brief IT operations on the functional trade-offs and document them: OWA Print Calendar, inline images in the OWA reading pane, and OWA light (/?layout=light) may break. Workarounds: screenshot calendars or use Outlook Desktop; send images as attachments; OWA light is deprecated and should not be used in production anyway.
- Inventory your Exchange Server fleet by version, cumulative update, and ESU enrollment tier. If you are on Exchange 2016 (CU23) or Exchange 2019 (CU14/CU15) without Period 2 ESU, the permanent patch will not reach you — open a finance conversation now about enrolling in Period 2, migrating to Exchange Server SE or Exchange Online, or accepting indefinite mitigation-only status.
- For SOC and threat-hunting teams: audit OWA access logs for unusual session activity and credential-reset patterns. Hunt for unusual JavaScript execution patterns in OWA sessions. Add CVE-2026-42897 indicators of compromise to detection as Microsoft and partners publish them, and pre-script the "Exchange OWA compromise" scenario in your incident response playbook — the forensics differ from ProxyLogon and ProxyShell.