Salt Typhoon Just Pivoted to Azerbaijani Oil and Gas — Chinese APT Targeting Now Follows Energy Geopolitics
Salt Typhoon spent three months inside an Azerbaijani oil and gas company — a target type it normally ignores. Bitdefender's assessment of why is the part that matters: Chinese APT targeting now follows energy geopolitics in real time.
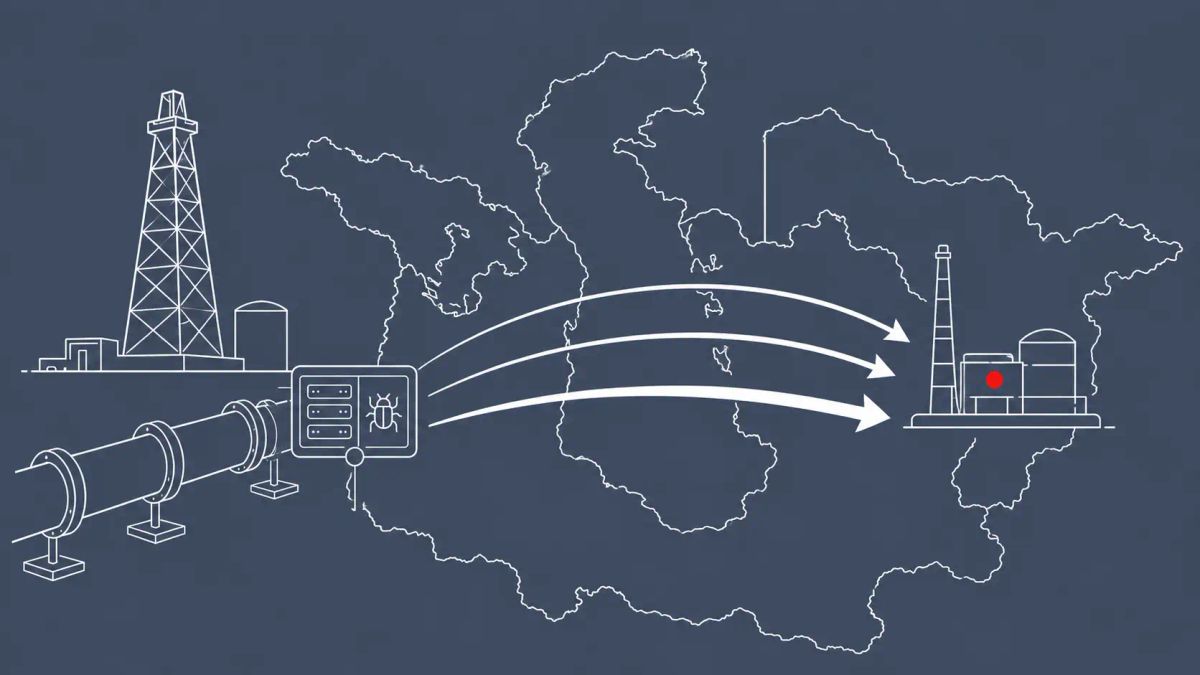
Salt Typhoon spent three months inside an Azerbaijani oil and gas company — a target type it normally ignores. Bitdefender's assessment of why is the part that matters: Chinese APT targeting now follows energy geopolitics in real time, and the lag between a market shift and a state-sponsored intrusion is measured in months.
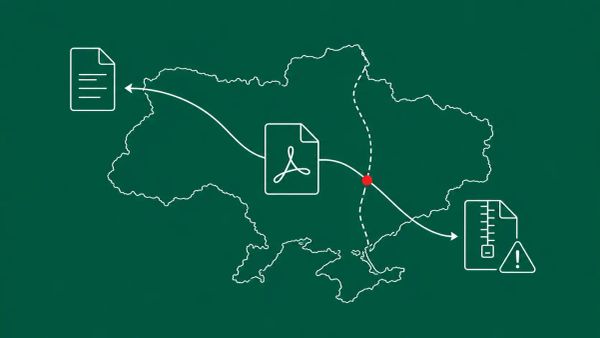
BAKU, AZERBAIJAN — Bitdefender researchers disclosed on May 14, 2026 that two China-linked state-sponsored APTs — Salt Typhoon and Twill Typhoon — have expanded their target sets and updated their malware tooling in recent campaigns. Salt Typhoon, also tracked as Earth Estries, FamousSparrow, GhostEmperor, and UNC2286, targeted an Azerbaijani oil and gas company between December 2025 and February 2026. That is a shift from typical Salt Typhoon activity, which has focused on government, telecom, and technology entities across the US, Asia, the Middle East, and Africa. Bitdefender assesses the shift is "likely triggered by Azerbaijan's recently increased role in European energy security" following Russia's Ukraine gas transit agreement expiration and recent Strait of Hormuz disruptions. Concurrently, Darktrace observed Twill Typhoon — also tracked as Bronze President, Camaro Dragon, Earth Preta, Mustang Panda, and TA416 — targeting Asia-Pacific entities with updated tooling between September 2025 and at least April 2026.
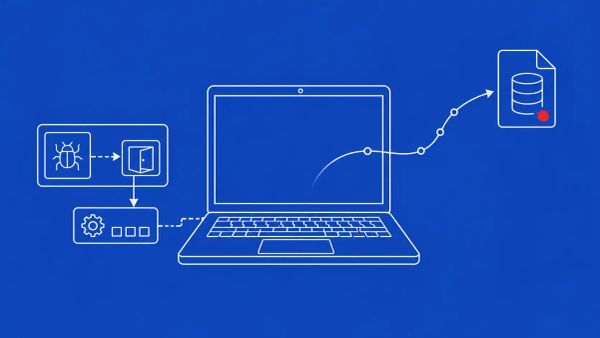
The Salt Typhoon campaign deployed an updated version of Deed RAT and the TernDoor backdoor, which Cisco Talos researchers have linked to the group. Bitdefender's reconstruction describes a sustained and adaptive operation: an initial compromise and Deed RAT deployment, followed roughly a month later by the operators accessing the initially compromised server again to deploy TernDoor, and then at the end of February 2026 a third access in which the APT attempted to redeploy Deed RAT using the same execution chain. Bitdefender characterizes the pattern as "an actor that repeatedly sought to regain and extend access" — the kind of multi-wave operation that ordinary eviction often fails to fully close out.
Why the Azerbaijan Pivot Is the Story
Salt Typhoon does not normally target Caspian-region oil and gas. The group's documented history runs through government, telecom, and technology entities. The pivot to an Azerbaijani energy company is, in Bitdefender's framing, a direct response to a geopolitical shift: Azerbaijan has become materially more important to European energy security as Russia's Ukraine gas transit agreement expired and disruptions hit the Strait of Hormuz. The defender takeaway is specific and uncomfortable — critical infrastructure cyber threat now follows energy geopolitics in real time, and the lag between an energy-market change and a corresponding state-sponsored intrusion is measured in months, not years.
For organizations in oil and gas, energy infrastructure, or any sector where critical infrastructure intersects with geopolitical events, this is a documented case study rather than a hypothetical. If your organization operates in a country whose energy posture has shifted between 2024 and 2026 — Azerbaijan, the broader Caspian region, Central Asia, or anywhere else where chokepoint dynamics have changed — your threat model should now assume Chinese APT interest. The same logic that put a Caspian energy company on Salt Typhoon's target list applies to any energy entity whose strategic relevance has risen. This is the operational corollary of the broader picture of Chinese state cyber capability that Germany's recent warning sketched out: the capability is real, and its targeting is responsive to events.
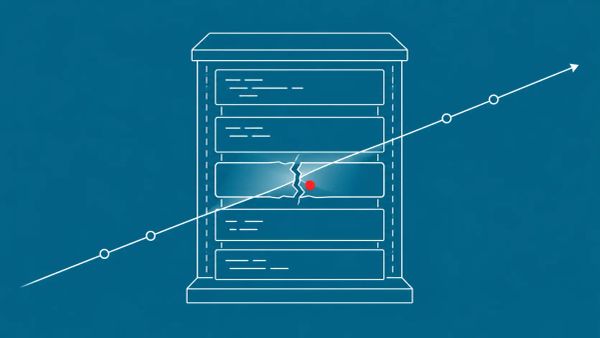
The Multi-Wave Access Pattern and What It Says About Eviction
The most operationally instructive detail in Bitdefender's reconstruction is the three-wave intrusion timeline. Deed RAT went in, then was removed from at least one host. About a month later the operators were back on the initially compromised server, deploying TernDoor. At the end of February, they returned a third time and tried to redeploy Deed RAT using the same execution chain. That repetition tells defenders two things. First, Salt Typhoon treats eviction as a temporary setback, not an endpoint — the group expects to be removed and plans to re-enter. Second, if the operators were comfortable reusing the same execution chain on the third attempt, they had reason to believe the defensive posture had not changed enough to block it.
That pattern argues for two changes in incident response practice. Eviction protocols for suspected Chinese APT activity need to assume the actor will attempt re-entry and should be paired with extended detection capability that watches for the second and third waves, not just the first. And the execution chain itself — not just the individual malware samples — needs to be the unit of detection, because Salt Typhoon's willingness to reuse it suggests the chain is the durable, reusable asset. Hunt for Deed RAT and TernDoor indicators when Bitdefender and Cisco Talos publish them, but build the detection logic around the multi-stage behavior, because the samples will rotate and the tradecraft will not.
Twill Typhoon, Alias Confusion, and the Asia-Pacific Dimension
The second half of the disclosure — Darktrace's observation of Twill Typhoon activity against Asia-Pacific entities with updated tooling from September 2025 through at least April 2026 — is a reminder that the alias problem is itself a defensive risk. Twill Typhoon is Microsoft's name for the group the rest of the industry tracks as Bronze President (Secureworks), Camaro Dragon (Check Point), Earth Preta (Trend Micro), Mustang Panda (CrowdStrike), and TA416 (Proofpoint). Salt Typhoon carries a similar pile of vendor names. If your threat intelligence aggregation does not reconcile these aliases, you can read five reports about what you think are five actors and miss that you are looking at one persistent campaign against your sector.
The broader pattern Bitdefender identifies — that China-linked APTs adapt their targeting to current political events — is the strategic frame boards should absorb. Chinese state-aligned cyber operations are now actively responsive to geopolitics, which makes them a strategic risk to track alongside policy developments, not just an operational nuisance to be filtered at the firewall. The networking-equipment policy environment that produced the FCC's evolving stance on foreign-manufactured routers and the espionage tradecraft documented in recent state-sponsored campaigns against critical sectors are both part of the same picture: state cyber operations and geopolitics are now a single risk surface.
The CyberSignal Analysis
Signal 01 — Critical Infrastructure Cyber Threat Now Follows Energy Geopolitics on a Months-Long Lag
The Salt Typhoon Azerbaijan pivot is the clearest documented case this year of Chinese APT targeting shifting in direct response to a geopolitical event. For CISOs in energy, oil and gas, and adjacent critical infrastructure sectors, the briefing for executives is that your threat model needs a geopolitical input. When your country's or your company's strategic relevance to global energy markets changes, assume Chinese APT interest will follow within months. Build the monitoring and detection investment to match — and specifically extend it to organizations operating in any region whose energy posture has shifted in the 2024-2026 window.
Signal 02 — Multi-Wave Access Is the Chinese APT Default, and Your Eviction Playbook Probably Assumes a Single Intrusion
Salt Typhoon's three-wave pattern over three-plus months — including a willingness to reuse the same execution chain on the third attempt — should reset incident response assumptions. Pre-script the "Chinese APT regains access after eviction" scenario. Audit your eviction protocols against the question of whether they would actually close out a second and third re-entry attempt, or just the first. Make the execution chain, not the individual malware sample, the unit of detection, because the samples rotate and the tradecraft persists. And coordinate with national intelligence agencies — FBI, CISA, and equivalent national authorities — on Chinese APT incidents, because the multi-wave pattern is exactly the kind of long-dwell activity that benefits from shared visibility.
What to Do This Week
- If your organization operates in oil and gas, energy infrastructure, or energy-adjacent sectors — especially in Azerbaijan, the broader Caspian region, or any country whose energy posture has shifted in 2024-2026 — brief executives that Chinese APT targeting now follows energy geopolitics in real time, and update the threat model accordingly.
- Hunt for Deed RAT and TernDoor indicators when Bitdefender and Cisco Talos publish them. Build the detection logic around the multi-stage execution chain and the three-wave access pattern, not just the individual malware samples, since Salt Typhoon rotates samples but reuses tradecraft.
- Audit your eviction protocols against the multi-wave assumption. Pre-script the "Chinese APT regains access after eviction" scenario and verify your protocols would actually close out a second and third re-entry attempt. Pair eviction with extended detection capability that watches for follow-on waves.
- Reconcile vendor aliases in your threat intelligence aggregation. Salt Typhoon = Earth Estries = FamousSparrow = GhostEmperor = UNC2286; Twill Typhoon = Bronze President = Camaro Dragon = Earth Preta = Mustang Panda = TA416. Without this reconciliation you can read multiple reports about one campaign and think you are seeing several.
- For Asia-Pacific organizations: refresh your threat intelligence on Twill Typhoon (Mustang Panda), which Darktrace observed actively updating tooling. Coordinate with your local CERT for indicators, and brief boards that Chinese state-aligned cyber operations are now a strategic risk responsive to geopolitical events, not just an operational concern.