HeartlessSoul Wants Map Data. Russian Aerospace and Drone Operators Are Giving It to Them.
Kaspersky disclosed cyber espionage group HeartlessSoul on May 11, targeting Russian aerospace firms and drone operators through SourceForge malvertising to steal GIS shape files, GPS data, and terrain models. The operational ground truth Russian analysts use is the prize.
Kaspersky frames this carefully: the targets are Russian. The data is operational ground truth. The downstream value is asymmetric and goes to whoever can read what Russian analysts are looking at — in a war where terrain awareness is currency.
MOSCOW, RUSSIA — Kaspersky Lab researchers disclosed on May 11, 2026 that a cyber espionage group dubbed HeartlessSoul has been compromising Russian aerospace firms, drone operators, and government agencies to steal Geographic Information System (GIS) shape files, digital geographic relief files, GPS data, and proprietary GIS mapping files. The group has been active since at least September 2025, using specially-crafted phishing and malvertising campaigns that plant fake projects on SourceForge, a legitimate download service, and create domains hosting malware that appears to be installers for legitimate aviation software. Once attackers gain access to databases and workstations used for GIS analysis, they download common document types alongside the unusual GIS, GPS, and terrain data.
Kaspersky's analysis identified links between HeartlessSoul and another hacking group known as Goffee, which has previously targeted Russian systems and was known for stealing sensitive files from flash drives connected to infected computers. The overlap may indicate coordinated or related operations. Independent Russian cybersecurity analyst Oleg Shakirov noted on his Telegram channel that the same malware was also distributed through files disguised as FPV drone simulators and tools designed to bypass restrictions on the Starlink satellite internet service — suggesting targeting extends to drone operators, communications specialists, and potentially military personnel beyond the named aviation industry focus. The campaign reflects the broader pattern of defense contractor security exposure documented in the Schemata DoD case from earlier this month, where the underlying data targeting reveals the operational objective.
The targeting and what HeartlessSoul takes
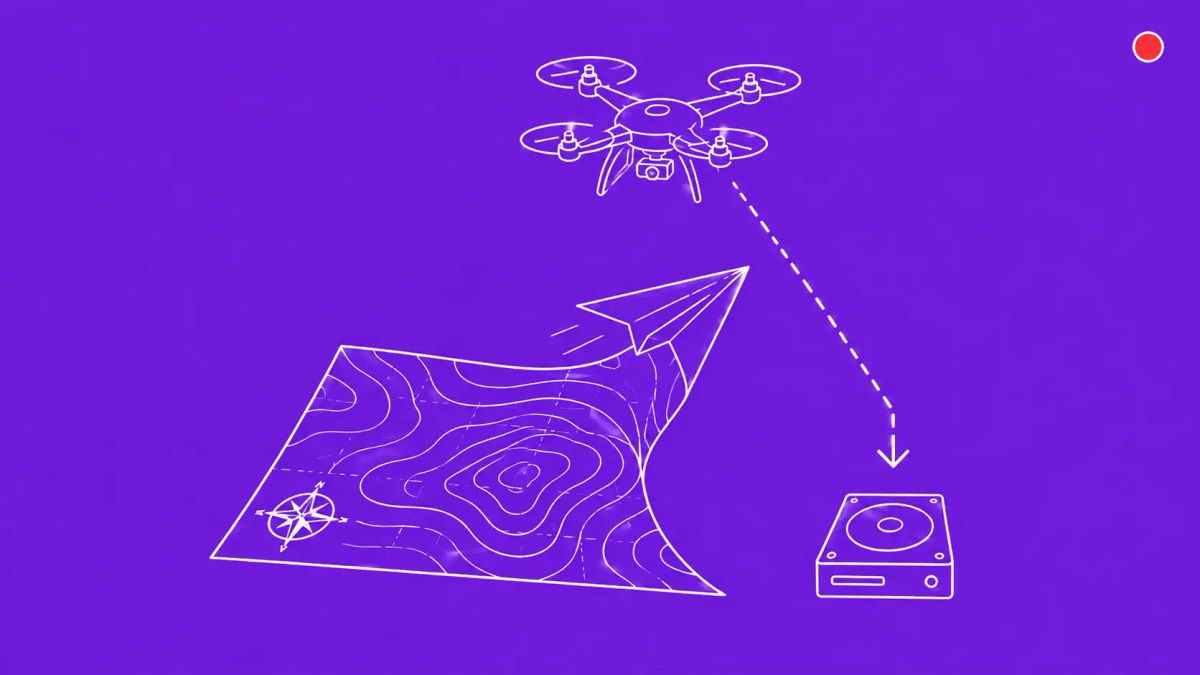
Once attackers gain access to databases and workstations used for GIS analysis, HeartlessSoul downloads a variety of common document types alongside several unusual categories: GPS data, GIS shape files, digital geographic relief files, and proprietary GIS mapping files. In Kaspersky's analysis (published in Russian), the company stated through Google translation that such GIS files allow attackers to obtain information about infrastructure — roads, engineering networks, terrain, and strategic objects — and provide confidential data used by engineering, government, and industrial organizations. Dark Reading's framing of the strategic value adds the editorially distinctive layer: the most under-appreciated value in GIS theft is operational ground truth — the adversary gets to see exactly what the victim's own analysts believe about terrain, infrastructure, and routes, which lets them model gaps in the victim's own awareness.
This is meaningfully different from typical aerospace cyber espionage targeting design schematics, trade secrets, or intellectual property. Design data tells an adversary what the victim builds. GIS data tells an adversary what the victim sees. In an active conflict environment where the victim is making targeting, routing, or infrastructure decisions based on the GIS data, knowing exactly what they're looking at gives the adversary a precise model of the victim's situational awareness — and its gaps.
The SourceForge tradecraft and what it suggests about operational sophistication
HeartlessSoul's initial-access tradecraft is technically unsophisticated but strategically precise. Specially-crafted phishing campaigns and malvertising campaigns drive targets toward domains and sites that host malware appearing to be installers for legitimate aviation software and resources. A fake project planted on SourceForge produced a malicious archive download. The technique is well within reach of most criminal operators — what distinguishes HeartlessSoul is the discriminating targeting: aerospace, drone operators, and GIS analysts specifically, with the malware payload built to identify and exfiltrate niche file formats that most criminal operations would ignore.
Kaspersky characterizes the actor as sophisticated based on the combined multi-stage infection, fileless execution, and the data the group targets — concluding it is not just a hacktivist or criminal group, but a motivated group posing a serious threat to organizations. The Goffee overlap, if confirmed, places HeartlessSoul within the broader cluster of operations targeting Russian systems with apparent intelligence-collection objectives. The Shakirov observation about FPV drone simulator and Starlink-bypass tool malware extends the targeting beyond aviation specifically to drone operators and communications specialists.
Why GIS theft is operationally distinct from typical IP theft
Most enterprise security programs treat crown-jewel data as patents, financial systems, executive communications, or customer databases. GIS, mapping, terrain, and operational ground-truth data sit in a different category — they describe how the organization sees the world rather than what the organization knows or owns. For an aviation company, GIS data covers flight corridor information, airport ground layouts, terrain elevation models, no-fly zones, and approach navigation reference points. For a drone operator, GIS data covers route planning, mission rehearsal terrain models, target area infrastructure layouts, and ground station network topology. For a logistics or defense contractor, GIS data covers supply route models, facility layouts, and asset position tracking.
Each of these is operational rather than commercial. The asymmetric value to an adversary is exactly the modeling capability Dark Reading highlighted: knowing what the victim's analysts believe about terrain and infrastructure allows the adversary to predict the victim's decisions and model the gaps in the victim's awareness. For defenders, this means GIS workstations and databases need a different security posture than typical engineering workstations — one calibrated to the operational consequence of compromise rather than the IP value of the data.
The Kaspersky source and a note on attribution
The primary source for this disclosure is Kaspersky Lab's report (published in Russian, with English coverage primarily through Dark Reading and The Record). Kaspersky is a Russian cybersecurity firm and has been the subject of US government bans since 2017 over concerns about ties to Russian intelligence services. Russian-published research on attacks against Russian targets warrants the standard caveat that defenders should weigh the analysis with appropriate context about the source. That said, the technical tradecraft documented — SourceForge plants, malvertising, fake aviation installers, GIS-specific exfiltration — is consistent with corroborating reporting from independent Russian analysts and aligns with broader patterns observed by Mandiant, Google Threat Intelligence Group, and other Western threat intelligence providers tracking aerospace and drone-sector targeting in 2026.
The CyberSignal Analysis
Signal 01 — GIS data is a documented crown-jewel category now
Re-baseline your crown-jewel data inventory if your organization operates GIS, mapping, terrain, or operational ground-truth data. The HeartlessSoul campaign documents specific targeting of file formats that most security programs do not classify as crown-jewel data. The defensible response is to elevate GIS workstation and database security posture: identity-bound access, egress monitoring for niche file formats, and segmentation of GIS systems from general business networks. The asymmetric investment is small; the targeting is now documented.
Signal 02 — SourceForge and similar legitimate-software-host vectors are documented attack surfaces
The fake aviation software project on SourceForge is the operationally specific finding worth carrying forward. SourceForge, like other legitimate-software-distribution sites (CodePlex, GitHub releases, OpenVSX), is now a documented adversary attack surface for sectoral targeting. Audit your developer and engineering workstation software inventory for unofficial or recently-installed packages from these sources, particularly in aviation, defense, drone, and logistics contexts.
Signal 03 — Low-technical-complexity, high-strategic-payoff is the model to plan against
HeartlessSoul's technical sophistication is moderate; its strategic targeting is precise. This is the low-technical-complexity, high-strategic-payoff pattern that defenders should expect more of in 2026 and beyond, particularly in defense-and-logistics-adjacent organizations. Cyber-physical operational risk is now on the strategic risk register for organizations whose own analysts depend on GIS and mapping data for operational decisions.
What to do this week
- Identify your GIS analyst workstations and treat them as confirmed high-value targets. Apply identity-bound access controls to crown-jewel GIS systems specifically. Implement egress monitoring to detect anomalous data exfiltration patterns, particularly for unusual file formats (shapefiles, GPS data files, digital geographic relief data).
- Segment GIS engineering networks from general business networks. This isolates the highest-value workstations from broader corporate compromise and limits lateral movement scope if a phishing email succeeds elsewhere in the organization.
- Audit recent software installations on GIS, aviation, and drone-operations workstations for unofficial packages from SourceForge or similar legitimate-software-distribution sources. Look specifically for aviation-themed software with unusual maintainer profiles or recent publication dates.
- For SOC and threat-hunting teams: add detection rules for downloads from SourceForge-hosted projects that resemble legitimate aviation software, and for outbound connections from GIS workstations to unusual external destinations. File-format-based exfiltration patterns (shapefiles, GPS data, terrain relief data) are unusual outbound from typical enterprise endpoints and should generate alerts.
- For organizations with export-control exposure: brief legal and compliance teams on the implications of GIS data exfiltration. ITAR and EAR considerations apply to US-headquartered organizations; equivalent regimes apply internationally. GIS data containing infrastructure mapping or operational ground truth may carry export-control sensitivity that incident response teams need to factor into breach disclosure.