Microsoft's Kazuar Analysis Shows Russia's Secret Blizzard Wants Your Signal Desktop Files
Microsoft's new Kazuar analysis names one capability that ties it to the other Russian Signal operation in the news: Kazuar steals Signal Desktop message files. Encryption protects the conversation in transit — not the database on a compromised laptop.
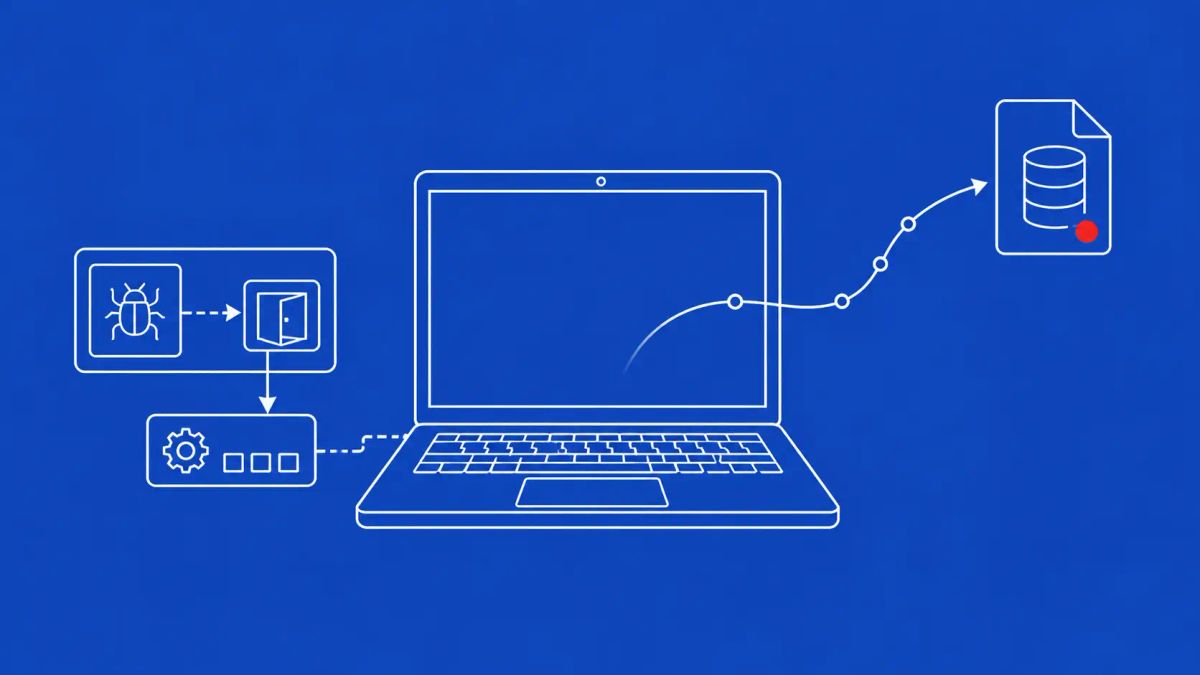
Microsoft's new analysis of the Kazuar backdoor names one capability that ties it directly to the other Russian Signal operation in the news this week: Kazuar steals files containing Signal Desktop messages. End-to-end encryption protects the conversation in transit. It does not protect the message database sitting on a compromised laptop.
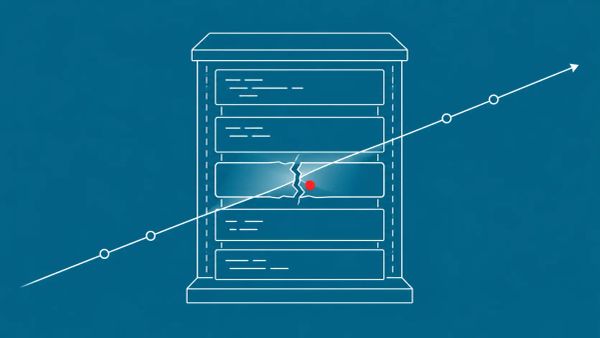
REDMOND, WA — Microsoft Threat Intelligence published an updated analysis on May 14, 2026 titled "Kazuar: Anatomy of a nation-state botnet," documenting the evolution of the Kazuar backdoor family used by the Russian state actor Secret Blizzard — also tracked as Turla, Snake, Uroburos, Waterbug, Venomous Bear, and KRYPTON. The Kazuar family, including the current KazuarV2 variant, is a modular backdoor supporting more than 40 functions: credential theft, authentication-data harvesting, proxy and cookie exfiltration, and data retrieval from operating system logs. CISA has linked Secret Blizzard to Center 16 of Russia's FSB security agency. The backdoor is typically injected into legitimate system processes such as explorer.exe or opera.exe to evade detection, with the companion Tavdig loader loaded into kavp.exe.
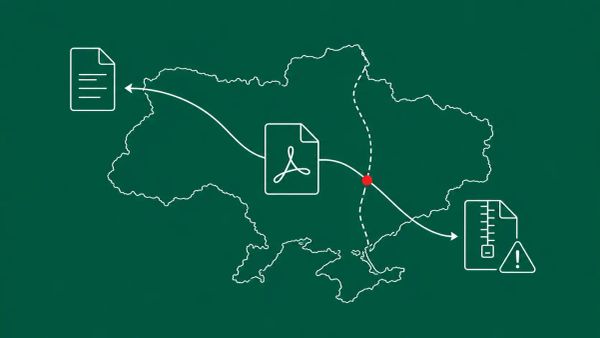
Two elements of Microsoft's reporting matter most for defenders. First, Kazuar is specifically built to steal files containing Signal Desktop messages, giving the same Russian state actor that runs the Kazuar botnet a direct technical path to read private Signal chats once a host is compromised. Second, Secret Blizzard's modus operandi includes hijacking other threat actors' infrastructure: Microsoft has documented the group commandeering the Amadey botnet (linked to cybercriminal Storm-1919), the Storm-1837 PowerShell backdoor, and Storm-0156 infrastructure to deploy Kazuar on Ukrainian military targets. The group also conducts adversary-in-the-middle campaigns through Russia's domestic intercept system SORM, and is the only known APT confirmed capable of conducting ISP-level AiTM espionage from inside Russian borders.
The Signal Desktop File Theft Is the Detail That Ties Two Russian Operations Together
Microsoft's documentation of Kazuar's interest in Signal Desktop message files is the single most consequential finding for any organization using Signal for sensitive communications. Signal's end-to-end encryption protects messages while they are in transit between devices. It does not protect the local message database once an attacker has code execution on the endpoint — and that is precisely what Kazuar is built to harvest. The same Russian state apparatus is pursuing two parallel paths to the same target. The Russian Signal account-hijacking campaign exposed this week intercepts messages at the account level by abusing the linked-devices feature; Kazuar reads the message files directly off the compromised device. Account-level interception and endpoint-level file theft, run in parallel, against the same encrypted-messaging surface.
The defensive implication for high-risk users is that Signal's threat model has to be stated precisely. Signal protects the conversation in transit. It does not protect a compromised endpoint, and a compromised endpoint is exactly what a Kazuar infection produces. For organizations whose executives, researchers, or government-facing staff use Signal Desktop for sensitive work, the endpoint security posture of those machines is now part of the secure-communications posture — they are not separable. The strategic line for boards is that no messaging app's encryption substitutes for endpoint hardening, and Russian state actors have built tooling that proves the point. CyberSignal's earlier reporting on Germany blaming Russia for Signal phishing attacks on its MPs tracked the account-level half of this same two-pronged Russian effort.
The 'Freeloader' Pattern Complicates Attribution and Incident Response
Secret Blizzard's habit of hijacking other threat actors' infrastructure — what Microsoft calls its "freeloader" approach — is the operational wrinkle that makes this group unusually hard to evict and to attribute. Rather than always building its own initial-access infrastructure, the group commandeers access that criminal and other state actors have already established. Microsoft has documented it using the Amadey botnet associated with cybercriminal Storm-1919, the Storm-1837 PowerShell backdoor, and Storm-0156 infrastructure, all to land Kazuar and the Tavdig loader on Ukrainian military devices. Microsoft's assessment is that commandeering other actors' access "highlights Secret Blizzard's approach to diversifying its attack vectors."
For incident response teams, this breaks a comfortable assumption. When your environment shows signs of a commodity botnet like Amadey, the working hypothesis is usually a criminal actor after credentials or cryptocurrency. The freeloader pattern means that commodity-malware foothold can be the delivery vehicle for an FSB backdoor. Pre-script the scenario where a Russian state actor is riding infrastructure you have attributed to someone else, and treat Amadey or similar commodity botnet activity in a high-value environment as a potential Secret Blizzard precursor, not just a nuisance infection. This is the same legitimate-tooling, borrowed-trust pattern visible across the Iranian MuddyWater false flag operation and the Belarus-aligned Ghostwriter campaign against Ukraine — state actors increasingly operate through someone else's footprint.
ISP-Level AiTM and What It Means for Anyone Operating Inside Russia
The capability that sets Secret Blizzard apart from every other documented APT is its ability to conduct adversary-in-the-middle attacks at the ISP level from inside Russian borders, facilitated by SORM — the System for Operative Investigative Activities, Russia's legally-mandated domestic intercept system. Microsoft's reporting describes a recent operation targeting foreign embassies in Moscow via ISP-level AiTM, redirecting victims through captive portals to deploy the ApolloShadow malware, which installs a fake Kaspersky root certificate to gain elevated privileges. Once an actor can manipulate traffic at the ISP layer, ordinary network-security assumptions collapse: TLS validation, trusted-network designations, and traffic-origin checks all become unreliable.
The operational guidance for any organization with a presence inside Russia — diplomatic missions, defense-adjacent businesses, journalists, NGOs — is concrete and comes directly from Microsoft's recommendations: route all traffic through an encrypted tunnel or trusted VPN service, apply least privilege rigorously, enforce MFA across all accounts, audit privileged account activity regularly, and block execution of scripts and unapproved executables. Secret Blizzard's broader toolset also includes strategic web compromises, spear phishing as its most common initial-access vector, and DLL side-loading with vulnerable Symantec binaries. The group has been active since at least 2006; the durability is the point. This is patient, well-resourced espionage infrastructure, and it is not going away.
The CyberSignal Analysis
Signal 01 — Signal's Encryption Protects the Conversation, Not the Endpoint, and Russia Is Attacking Both
Brief executives that Russian state actors have a documented, purpose-built technical capability to read Signal Desktop messages on compromised endpoints, and that this is one of two parallel Russian efforts against Signal — account hijacking on one side, endpoint file theft on the other. Update your high-risk-user threat model so it states the boundary precisely: Signal end-to-end encryption protects messages in transit, not on a compromised device. For staff who use Signal Desktop for sensitive work, the endpoint security of their machines is now inseparable from the secure-communications posture. No messaging app's cryptography substitutes for endpoint hardening — and Kazuar is the proof.
Signal 02 — The Freeloader Pattern Means a Commodity-Malware Foothold Can Be an FSB Delivery Vehicle
Secret Blizzard's practice of hijacking other actors' infrastructure breaks the usual incident-response triage shortcut. SOC and threat-hunting teams should treat Amadey botnet activity, and similar commodity-malware footholds, in high-value environments as a potential Secret Blizzard precursor rather than a self-contained criminal nuisance. Hunt for kavp.exe execution and unusual code loading into explorer.exe or opera.exe; detect on the Tavdig-to-KazuarV2 injection chain; and implement DLL side-loading detection for legitimate Symantec binaries. Pre-script the "a Russian state actor is riding infrastructure we attributed to someone else" scenario, and coordinate with Microsoft DART and national authorities on suspected Secret Blizzard incidents — the freeloader pattern means attribution benefits from shared visibility.
What to Do This Week
- Brief executives and high-risk users that Russian state actors can read Signal Desktop message files on compromised endpoints. Pair this with the Russian Signal account-hijacking campaign — Russia is pursuing both vectors. Restate the threat model: Signal encryption protects messages in transit, not on a compromised device.
- For any organization operating inside Russia — diplomatic, defense-adjacent, journalism, NGO — follow Microsoft's recommendations: route traffic through an encrypted tunnel or trusted VPN, apply least privilege, enforce MFA on all accounts, audit privileged account activity, and block execution of scripts and unapproved executables. ISP-level AiTM via SORM breaks ordinary network-trust assumptions.
- Hunt for Kazuar, KazuarV2, and Tavdig indicators. Look for kavp.exe execution, unusual code loading into explorer.exe or opera.exe, and the Tavdig-to-KazuarV2 injection chain. Implement DLL side-loading detection for legitimate Symantec binaries.
- Treat Amadey botnet activity, and similar commodity-malware footholds, in high-value environments as a potential Secret Blizzard delivery vehicle — not just a criminal nuisance. Pre-script the freeloader scenario in your IR playbook and coordinate with Microsoft DART and national authorities on suspected incidents.
- For Ukrainian organizations: hunt for Kazuar and Tavdig indicators specifically, and audit STARLINK-connected systems for unusual activity, since Microsoft documents Secret Blizzard targeting front-line military systems using STARLINK IPs.