Ghostwriter Now Geofences Its Phishing Lures — Only Ukrainian IPs Get the Malware
Ghostwriter built operational security into its phishing lure. Send the campaign's malicious PDF to a Ukrainian IP and it triggers the attack chain. Send it anywhere else — including to the analysts investigating it — and they get a harmless document.

Ghostwriter built operational security into its phishing lure. Send the campaign's malicious PDF to a Ukrainian IP address and it triggers the attack chain. Send it to anyone outside Ukraine — including the analysts who investigate it — and they get a harmless document about telecom regulations. Geofencing is now state-sponsored tradecraft, and it changes how defenders detonate samples.
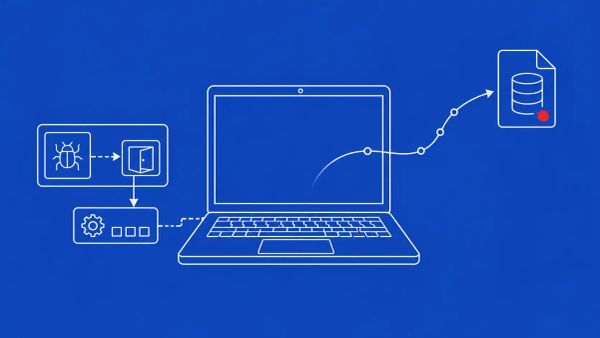
KYIV, UKRAINE — ESET Research disclosed on May 14, 2026 that the Belarus-aligned threat group Ghostwriter — also tracked as FrostyNeighbor (ESET), UNC1151 (Mandiant), UAC-0057 (CERT-UA), TA445, PUSHCHA, and Storm-0257 (Microsoft) — has launched a new campaign targeting Ukrainian governmental organizations, beginning in March 2026 and ongoing as of disclosure. The campaign's defining feature is geofenced PDF phishing: recipients with Ukrainian IP addresses receive a malicious RAR archive that initiates the attack chain, while recipients outside Ukraine receive a benign PDF described as relating to "regulations in the field of electronic communications from 2024 to 2026." The malicious PDFs impersonate Ukrtelecom, Ukraine's monopolist telephone company, with a message claiming Ukrtelecom "guarantees reliable protecting of customer data" and a download button leading to attacker-controlled delivery servers.
The final stage of the chain is a JavaScript dropper for Cobalt Strike, the red-team penetration testing tool long favored by adversaries. The compromise chain uses a JavaScript version of PicassoLoader — the latest iteration of a malware family that has been exclusively associated with Ghostwriter since at least 2022, previously delivered through Macropack-obfuscated VBA macros and ConfuserEx-obfuscated .NET downloaders, and now reduced to a simplified JavaScript implementation. ESET notes the operators perform server-side validation of victims before delivering the final payload. Ghostwriter has been active since at least 2016 and is closely linked with Belarusian government espionage; Mandiant assessed in 2021 a "high confidence" link to the Belarusian government.
Geofencing As Built-In Operational Security
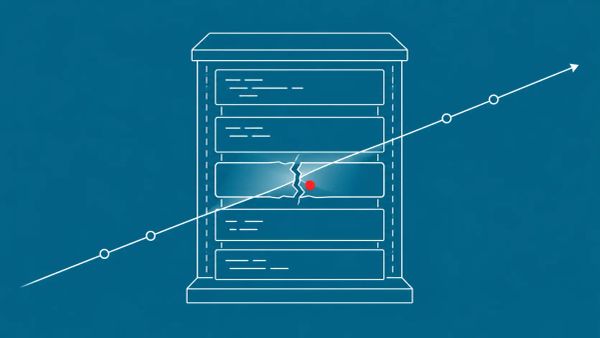
The geofenced PDF tradecraft is the operational evolution defenders should mark. By delivering different content based on the recipient's IP geolocation, Ghostwriter has built operational security directly into the lure. Security researchers and analysts outside Ukraine who receive a sample email — or who pull one from a threat intelligence feed and detonate it from a non-Ukrainian sandbox — may see only the benign telecom-regulations PDF and conclude the email is harmless. The actual malicious payload is gated to Ukrainian IP space. The campaign's true scope is invisible to anyone investigating it from the wrong vantage point.
This is a direct attack on the detection-and-response workflow itself. Incident response teams analyzing Ghostwriter samples need to recognize that submission from a non-Ukrainian IP can yield false-negative results — the maliciousness only triggers for in-region victims. The practical countermeasure is to detonate suspected Ghostwriter samples from Ukrainian-region testing infrastructure: a VPN endpoint or sandbox located in Ukraine. More broadly, geofenced phishing being operational at the state-sponsored level means sandbox testing infrastructure can no longer assume a single geographic vantage point is sufficient. Multi-region detonation is moving from a nice-to-have to a requirement for any organization that investigates regionally-targeted campaigns.
Ukrtelecom Impersonation and the JavaScript PicassoLoader Chain
The lure's choice of Ukrtelecom is deliberate. As Ukraine's monopolist telephone company, Ukrtelecom is an organization nearly every Ukrainian government employee has a plausible reason to receive communications from, and the impersonation message — claiming Ukrtelecom "guarantees reliable protecting of customer data" — is exactly the kind of reassuring administrative language that lowers a recipient's guard. The lure PDF itself has been described as blurry, a small tell, but the social engineering frame carries it. For Ukrainian organizations, the immediate defensive guidance is to verify any communication purporting to come from Ukrtelecom through an out-of-band channel before acting on it, and to brief staff specifically on this impersonation pattern.
The technical chain is notable for what it simplified. PicassoLoader has been Ghostwriter's exclusive downloader toolkit since at least 2022, and earlier iterations were delivered through layers of obfuscation — Macropack-obfuscated VBA macros inside Excel workbooks, ConfuserEx-obfuscated .NET downloaders. This iteration strips that down to a JavaScript implementation. The simplification is its own signal: Ghostwriter is iterating its delivery mechanism while keeping the underlying toolkit constant, which means defenders should build detection around the PicassoLoader-to-Cobalt-Strike behavior pattern rather than chasing the obfuscation-layer-of-the-month. The pattern of state actors riding legitimate tooling and authenticated trust echoes the Iranian MuddyWater false flag tradecraft — Cobalt Strike, like Microsoft Teams, is a legitimate tool turned operational asset.
The Belarus-Russia-Ukraine Cyber Theater
Ghostwriter operates for Belarus and is broadly aligned with Russian state objectives, and its targeting history maps directly onto the Belarus-Russia-Ukraine conflict: Ukrainian government and military, plus attacks on Lithuania, Latvia, and Poland, with a documented February 2025 campaign against Ukrainian government and Belarusian opposition activists. This March 2026 campaign is the newest entry in a decade-long operational record. It lands in the same theater as the Russian state-sponsored Signal account-hijacking campaign and the Kazuar backdoor operations of Russian actor Secret Blizzard against Ukrainian military targets — three distinct but aligned operations against Ukraine and NATO-adjacent organizations running concurrently.
For organizations with Ukrainian operations or Ukrainian staff, the campaign is a direct active threat, not a regional curiosity. Ghostwriter also conducts disinformation campaigns alongside its cyber espionage — a hybrid model that does not rely on social networks for distribution but uses compromised content management systems and spoofed emails. Organizations supporting Belarusian opposition or pro-democracy efforts should note that Ghostwriter has directly targeted Belarusian opposition activists in prior campaigns, and coordinate with Access Now and Citizen Lab for at-risk-individual protection.
The CyberSignal Analysis
Signal 01 — Geofenced Phishing Breaks the Analyst's Detonation Workflow, and Multi-Region Testing Is Now Mandatory
Ghostwriter's geofencing is a documented state-sponsored attack on the detection workflow itself. Incident response teams must recognize that detonating a suspected Ghostwriter sample from a non-Ukrainian IP can produce a false negative — the analyst sees a benign PDF and the campaign's true scope stays hidden. Build Ukrainian-region detonation capability into your sandbox infrastructure (a VPN endpoint or in-region sandbox), and more broadly treat multi-region sample detonation as a standard requirement for investigating any regionally-targeted campaign. Expect geofenced delivery to spread beyond Ghostwriter; the technique works, and other state actors will adopt it.
Signal 02 — Build Detection Around the Toolkit, Not the Obfuscation Layer
Ghostwriter has kept PicassoLoader as its exclusive downloader since at least 2022 while repeatedly changing the delivery wrapper — VBA macros, .NET downloaders, and now JavaScript. The lesson for SOC and threat-hunting teams is to anchor detection on the durable element: the PicassoLoader-to-Cobalt-Strike behavioral chain and the server-side-validated payload delivery pattern. Maintain detection rules for JavaScript-based PicassoLoader, but do not let the current obfuscation layer become the detection signature, because Ghostwriter will change it again. For Ukrainian organizations specifically, harden the email gateway against RAR-archive payloads and JavaScript executables embedded in PDFs, and add ESET's Ghostwriter indicators to the detection stack when published.
What to Do This Week
- For Ukrainian organizations: implement enhanced email filtering for PDF attachments, especially any impersonating Ukrtelecom. Block RAR-archive payloads and JavaScript executables embedded in PDFs at the email gateway. Add ESET's Ghostwriter / FrostyNeighbor indicators to your detection stack when published.
- Brief staff — especially Ukrainian government employees and anyone with Ukrainian operations — on the Ukrtelecom impersonation pattern. Verify any communication purporting to come from Ukrtelecom through an out-of-band channel before acting on it.
- Update your sample-detonation infrastructure for geofencing. For suspected Ghostwriter samples, detonate from Ukrainian-region testing infrastructure (a VPN endpoint or in-region sandbox), because submission from a non-Ukrainian IP can yield benign content and a false negative.
- Build detection around the durable toolkit, not the delivery wrapper. Maintain rules for JavaScript-based PicassoLoader and the PicassoLoader-to-Cobalt-Strike behavioral chain, since Ghostwriter has changed its obfuscation layer repeatedly while keeping the underlying toolkit constant since at least 2022.
- For organizations supporting Belarusian opposition or pro-democracy efforts: Ghostwriter has directly targeted Belarusian opposition activists in past campaigns. Coordinate with Access Now and Citizen Lab for at-risk-individual protection, and implement enhanced personal device security for those individuals.