Kimsuky's PebbleDash Now Hits Defense Sectors in Three Countries — And Its New Backdoor Was Coded With AI
Kaspersky found something unusual in a North Korean backdoor: comments that look written by an LLM, not a human. Combined with Kimsuky's expansion into defense targets across three countries, it is documented evidence that state malware development is borrowing AI.
Kaspersky found something unusual in the code of a North Korean backdoor: comments that look written by a large language model, not a human — emoji-laden debugging messages among them. Combined with Kimsuky's expansion into defense targets across three countries, it is documented evidence that state-sponsored malware development has started borrowing AI.
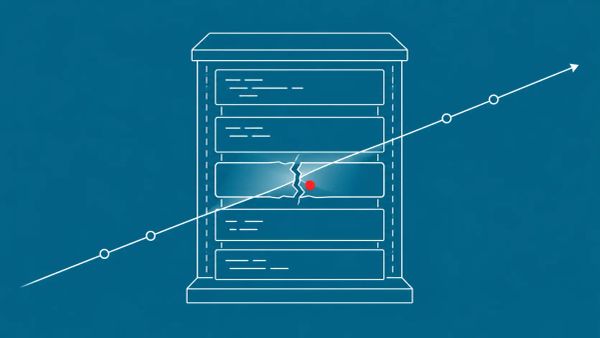
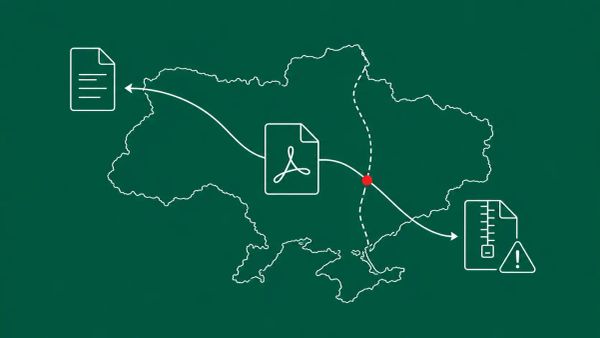
SEOUL, SOUTH KOREA — Kaspersky researchers disclosed on May 14, 2026 that Kimsuky — the North Korean state-sponsored APT also tracked as APT43, Emerald Sleet, and Velvet Chomilla — has continued developing its PebbleDash backdoor family with new tools targeting defense sector entities in South Korea, Brazil, and Germany. Kaspersky's analysis reveals connections between the PebbleDash cluster and Kimsuky's AppleSeed cluster, which targets government organizations and is shifting its focus toward GPKI certificate extraction — the South Korean government's public key infrastructure certificates used on government servers. PebbleDash and AppleSeed are described as the most technically advanced clusters in Kimsuky's toolset.
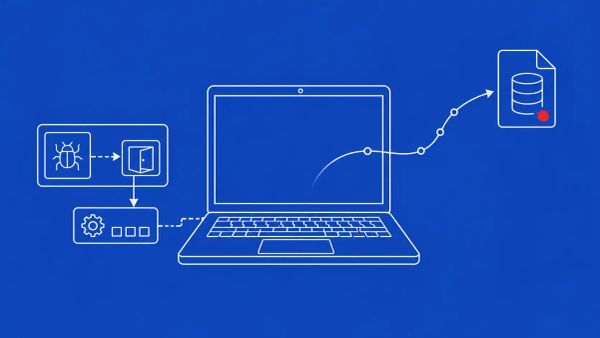
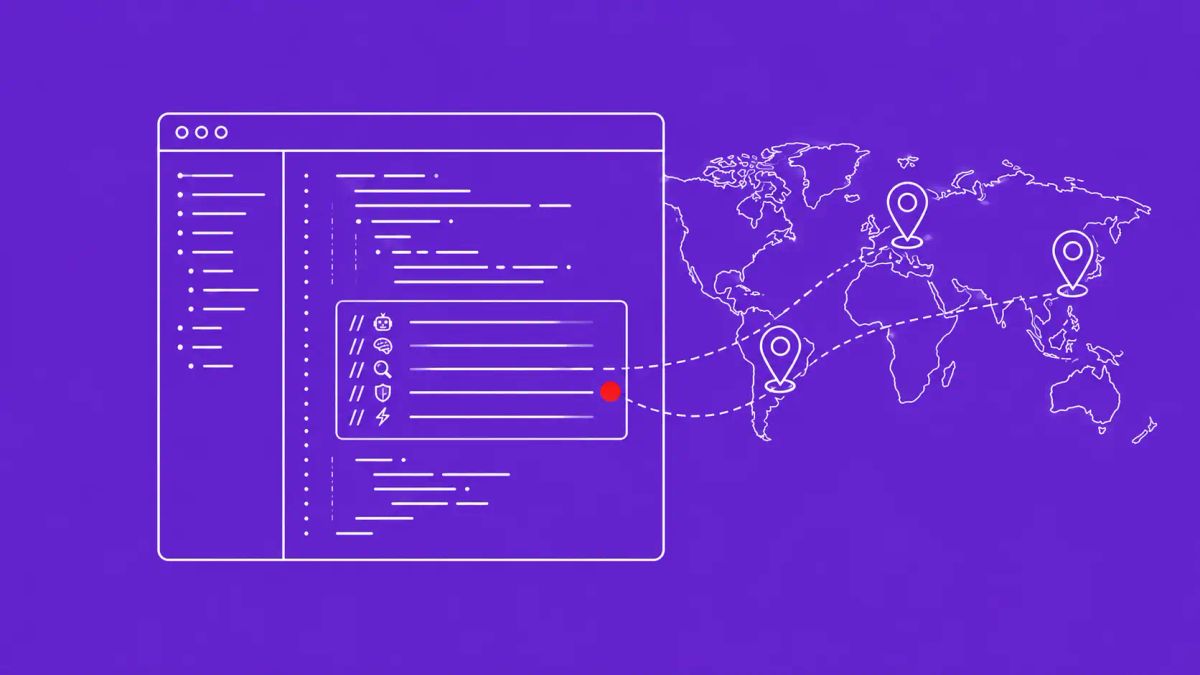
The finding that ties this disclosure to the broader AI weaponization story comes from Korea Times' parallel reporting: Kaspersky also identified that Kimsuky's HelloDoor backdoor contains comments that appear to have been generated by a large language model rather than a human developer. Kaspersky's basis for that assessment, in its own words, is "traces that include emojis used for logging debugging messages." Since 2024, Kimsuky has also been using Visual Studio Code Remote Tunneling — a legitimate Microsoft feature — to establish covert remote access instead of deploying malware directly. The PebbleDash and AppleSeed clusters masquerade as legitimate documents and application installers, manifest as JSE droppers or executables with .EXE, .SCR, and .PIF extensions, and occasionally use stolen legitimate certificates from South Korean organizations to avoid detection.
LLM-Developed Malware Is Now Documented Across Multiple State Actors
The HelloDoor finding is the part of this disclosure with the broadest implications. Kaspersky's evidence — emoji-laden debugging comments and the formatting characteristics of LLM-generated text — is circumstantial rather than a confession, and it is worth noting that the brief does not establish which LLM was used or whether Kimsuky's AI use is operationally significant or still experimental. But circumstantial evidence of LLM involvement in a North Korean backdoor is itself a data point that matters, because it does not stand alone. Google's disclosure of the first AI-generated zero-day in the wild and the German warning about a Chinese AI 'superhacker' describe the same trend from different angles. Kimsuky's HelloDoor adds North Korea to the list.
AI weaponization in offensive operations is now documented across multiple geographic and political alignments — not a single-country or single-actor phenomenon. For SOC and threat-hunting teams, the practical consequence is that LLM-generated artifacts are becoming a hunting signal in their own right: emoji-laden comments, suspiciously clean formatting, hallucinated CVE references, and similar tells in code samples are worth flagging. Pre-script an "LLM-developed malware analysis" workflow — update YARA rules, detection heuristics, and attribution methodology to account for the possibility that the code in front of you was partly machine-written. The Kimsuky case, paired with prior reporting that Kimsuky was among state actors documented using OpenAI's ChatGPT, suggests North Korea has been operating in this space for more than a year.
Defense-Sector Targeting Has Expanded Well Beyond South Korea
Kimsuky's traditional focus has been South Korea and North Korean foreign affairs. The PebbleDash cluster's confirmed victims — Brazilian and South Korean defense organizations, plus a German defense firm — show that DPRK targeting has broadened geographically. For defense-sector organizations in Brazil, Germany, and South Korea specifically, this is a direct active threat, and the briefing for executives is that Kimsuky should now be in the threat model regardless of whether the organization has any obvious Korea nexus. Hunt for PebbleDash, AppleSeed, and HelloDoor indicators when Kaspersky publishes them, and audit Visual Studio Code Remote Tunneling sessions, which Kimsuky uses for covert access.
The AppleSeed cluster's shift toward GPKI certificate extraction is the South-Korea-specific dimension. GPKI is the South Korean government's authentication system used on government servers; harvesting those certificates gives an attacker a path to impersonate legitimate government identities. South Korean government organizations should audit GPKI certificate storage and access logs, implement enhanced detection for AppleSeed extraction tradecraft, and coordinate with KISA and South Korean cybersecurity authorities on indicator sharing. Kimsuky's broader 2026 toolkit also includes a customized RDP Wrapper utility and three proxy tools, delivered via spear-phishing emails with .LNK shortcut files disguised as PDF, Excel, and Word documents — often named with the specific names of targeted people or companies — with PowerShell or mshta.exe installing PebbleDash and RDP Wrapper.
Visual Studio Code Tunneling and the .LNK Problem
The Visual Studio Code Remote Tunneling tradecraft, in use since 2024, is the quieter operational evolution. Rather than dropping a custom backdoor that an EDR product might flag, Kimsuky establishes covert remote access through a legitimate, signed Microsoft developer tool. This is the same legitimate-tooling pattern visible across the week's other state-sponsored disclosures — adversaries riding trusted software rather than fighting endpoint defenses head-on. For all organizations, not just those with an obvious DPRK nexus, the defensive guidance is to audit Visual Studio Code Remote Tunneling sessions for unusual contexts and to treat tunneling activity from non-developer accounts or unexpected hosts as suspicious.
The .LNK delivery vector is the other broadly applicable lesson. Kimsuky disguises .LNK shortcut files as PDF, Excel, and Word documents, and the highly targeted file names — using the specific names of people or companies the operators are after — are designed to survive a quick glance. The defensive controls are straightforward and apply to every organization: audit .LNK file handling at the email gateway and endpoint, detect on PowerShell-plus-mshta.exe execution chains originating from user-initiated processes, and monitor for RDP Wrapper installations, since Kimsuky's customized version is a primary persistence mechanism. Add IOCs for HelloDoor, PebbleDash, and AppleSeed to the detection stack when Kaspersky publishes them.
The CyberSignal Analysis
Signal 01 — State-Sponsored LLM-Developed Malware Is Now Documented Across DPRK, and AI Artifacts Are a Hunting Signal
Kaspersky's HelloDoor finding puts North Korea alongside the other state and criminal actors documented using AI in offensive operations. The evidence is circumstantial — emoji-laden debugging comments, LLM-style formatting — and defenders should hold it at that confidence level rather than overclaiming. But the trend is the point: AI weaponization in malware development is multi-alignment and operational. SOC and threat-hunting teams should add LLM-generated artifacts to their hunting heuristics — emoji-laden comments, unnaturally clean formatting, hallucinated CVE or API references — and pre-script an LLM-developed-malware analysis workflow that updates YARA rules, detection logic, and attribution methodology for the possibility that a sample was partly machine-written.
Signal 02 — Kimsuky's Defense-Sector Targeting Is Now Multi-Country, and Its Tradecraft Rides Legitimate Tools
PebbleDash victims in Brazil, Germany, and South Korea confirm DPRK targeting has expanded well past its traditional Korea focus. Defense-sector CISOs in those countries — and arguably anywhere — should put Kimsuky in the threat model now. The operational hardening is concrete: audit Visual Studio Code Remote Tunneling sessions for unusual contexts; audit .LNK file handling and detect PowerShell-plus-mshta.exe chains from user-initiated processes; monitor for RDP Wrapper installations; and for South Korean government organizations specifically, audit GPKI certificate storage and access logs against the AppleSeed extraction tradecraft. Coordinate with KISA and your national CERT on indicators. Kimsuky rides legitimate tooling — VS Code tunneling, RDP Wrapper, stolen code-signing certificates — so detection has to focus on anomalous use of trusted software, not just on novel malware.
What to Do This Week
- For defense-sector organizations in Brazil, Germany, and South Korea: brief executives that Kimsuky has expanded geographic targeting beyond its traditional South Korean focus. Put Kimsuky in the threat model and hunt for PebbleDash, AppleSeed, and HelloDoor indicators when Kaspersky publishes them.
- Audit Visual Studio Code Remote Tunneling sessions across your environment. Kimsuky has used this legitimate Microsoft feature for covert access since 2024. Treat tunneling from non-developer accounts or unexpected hosts as suspicious.
- Harden .LNK handling and detect the execution chain. Audit .LNK files arriving as email attachments disguised as PDF, Excel, or Word documents; detect PowerShell-plus-mshta.exe combinations from user-initiated processes; and monitor for RDP Wrapper installations as a persistence indicator.
- For South Korean government organizations: audit GPKI certificate storage and access logs, implement enhanced detection for AppleSeed extraction tradecraft, and coordinate with KISA and South Korean cybersecurity authorities on indicator sharing.
- Add LLM-generated artifacts to your threat-hunting heuristics — emoji-laden comments, unnaturally clean formatting, hallucinated CVE references in code samples. Pre-script an "LLM-developed malware analysis" workflow updating YARA rules, detection logic, and attribution methodology. State-sponsored AI use in malware development is now documented across multiple alignments.