A Spyware Investigator Turned a Signal Hijack Attempt Into a 13,500-Target Russian Campaign Map
Russian government hackers tried to hijack the Signal account of the wrong person. Donncha Ó Cearbhaill investigates spyware for a living — so he reverse-engineered the campaign and found himself one of 13,500+ targets. The 'snowball' methodology is the lesson.
Russian government hackers tried to hijack the Signal account of the wrong person. Donncha Ó Cearbhaill investigates spyware for a living — so instead of falling for the fake verification prompt, he reverse-engineered the campaign and found himself one of more than 13,500 targets. The "snowball" methodology he documented is the part every Signal user needs to understand.
DUBLIN, IRELAND — Donncha Ó Cearbhaill, head of Amnesty International's Security Lab and a researcher who investigates spyware attacks for a living, was targeted on Signal earlier this year by a phishing message reading: "Dear User, this is Signal Security Support ChatBot. We have noticed suspicious activity on your device, which could have led to data leak... To prevent this, you have to pass verification procedure, entering the verification code to Signal Security Support Chatbot. DON'T TELL ANYONE THE CODE, NOT EVEN SIGNAL EMPLOYEES." Rather than fall for the attempted account hijack, Ó Cearbhaill ran an investigation. TechCrunch's Lorenzo Franceschi-Bicchierai reported on May 14, 2026 that Ó Cearbhaill subsequently determined he was one of more than 13,500 targets in a campaign attributed to the Russian government. Other targets included journalists he had worked with and a colleague at Amnesty International.
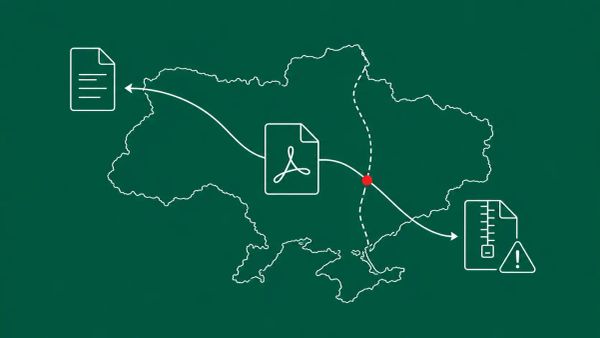
The campaign is consistent with the broader Russian state-sponsored Signal-and-WhatsApp account-hijacking operation that Dutch intelligence agencies AIVD and MIVD warned about on March 9, 2026, and that the FBI and CISA confirmed in a joint advisory later that month. The operation does not break Signal's end-to-end encryption. It walks around it — stealing access to individual accounts by abusing the "linked devices" feature, so the attacker's device receives the same messages as the legitimate user. Ó Cearbhaill's recommended defense is specific and free: enable Signal's Registration Lock, a feature that sets a PIN preventing anyone from registering your phone number on a different device. CyberSignal has tracked the same Russian campaign as it surfaced in Europe — including Germany blaming Russia for Signal phishing attacks on its MPs and the Signal phishing campaign that targeted Bundestag President Klöckner.
The 'Snowball' Methodology Is the Tradecraft That Matters
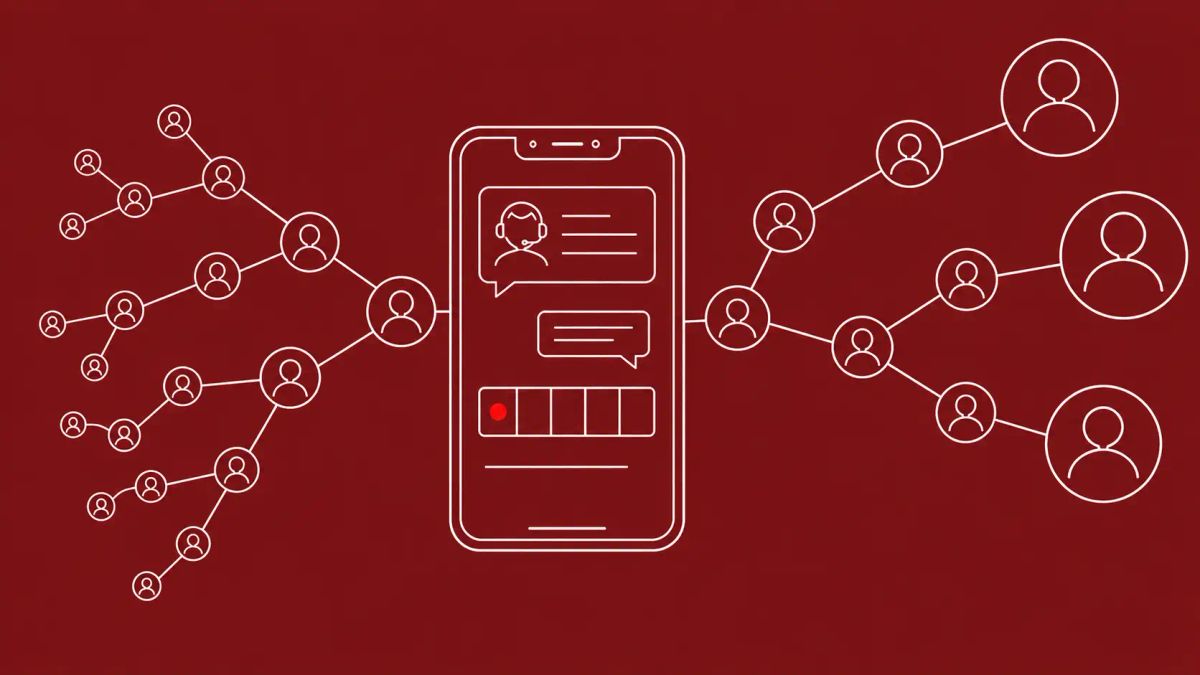
Ó Cearbhaill declined to reveal exactly how he identified the 13,500-target population — sensibly, to protect his hand against the hackers — but he did describe the campaign's growth mechanism. He calls it the "snowball hypothesis": the attackers compromise an early target, then mine that person's account for contacts and group memberships, which become the next wave of targets. Ó Cearbhaill assesses he was likely targeted not for any individual reason but because he was in a group chat with someone who had already been compromised, which handed the hackers his contact information.
That mechanism inverts how most people assess their own risk. The traditional question — "am I important enough to be targeted?" — no longer governs who ends up in the target set. Group membership does. Anyone in a group chat with a compromised user is now a discoverable target, regardless of whether they had any individual reason to be on a Russian intelligence list. For organizations with high-risk users — journalists, executives, dissidents, researchers, government officials — the operational implication is that a single compromised contact can expose an entire professional network. The campaign's 13,500-target scale is exactly what the snowball mechanism produces: each compromise widens the funnel.
Why Account Hijacking, Not Encryption-Breaking, Is the State-of-the-Art
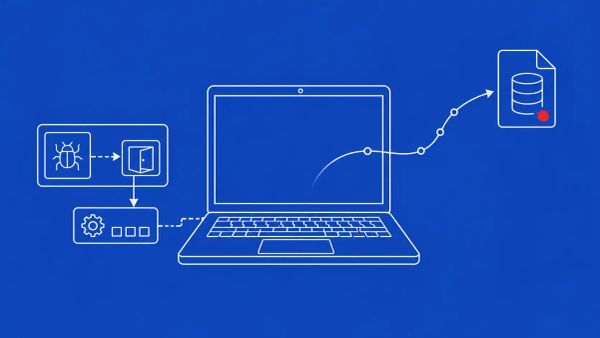
The FBI and CISA framing in their March advisory is the part defenders should internalize: the goal is to walk around end-to-end encryption by stealing access to individual accounts, not to break the encryption itself. The lure exploits Signal's legitimate "linked devices" function — the same feature that lets you use Signal on a desktop alongside your phone. The fake "Signal Support chatbot" message claims suspicious activity and asks the target to enter an SMS verification code or Signal PIN. If the target complies, the attacker links their own device to the victim's account and begins receiving the victim's messages in real time. Signal Support, for the record, never initiates contact via in-app messages, SMS, or social media to ask for a verification code or PIN. Any message that does is a hijack attempt.
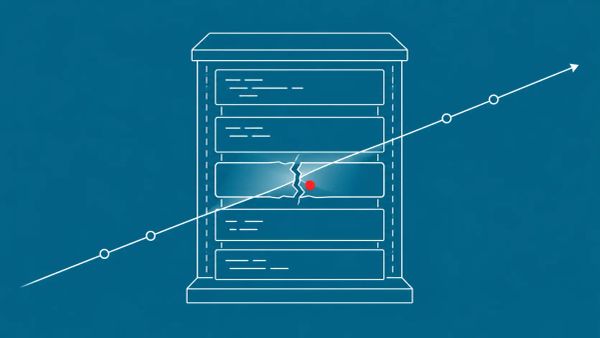
The pattern echoes the Microsoft Teams social engineering tradecraft documented in the Iranian MuddyWater false flag campaign — state actors riding legitimate platform features and authenticated sessions rather than exploiting code vulnerabilities. And it is one half of a documented two-pronged Russian effort against Signal specifically: the account-hijack campaign covered here, plus the Kazuar backdoor used by Russian actor Secret Blizzard, which specifically steals Signal Desktop message files from compromised endpoints. Account-level interception and endpoint-level file theft are being pursued in parallel. Signal's encryption is doing its job; the attackers have simply moved the fight to the device and the account.
Active Defense Produced the Intelligence Breakthrough
The most instructive detail in the TechCrunch reporting is not the campaign — it is the response. Ó Cearbhaill did not simply block the message and move on. He treated the hijack attempt as a lead and ran an investigation that exposed a campaign affecting more than 13,500 people. He told TechCrunch he doubts the hackers will come after him again, and that they "probably regret going after him in the first place." His parting line — "I welcome future messages, especially if they have zero-days they would like to share" — is the posture of someone who has turned a targeting attempt into an asset.
Most users cannot and should not run active investigations against state-sponsored attackers; for the average high-risk user the right move is to block, report, and harden. But for organizations with security teams, the lesson is that attempted account takeovers are intelligence opportunities, not just nuisances to be filtered. The same investigative posture defenders bring to the broader state-sponsored espionage landscape — documenting tradecraft, mapping infrastructure, sharing indicators — applies to messaging-app hijack attempts. AIVD and MIVD published concrete detection guidance worth circulating: check whether any contact appears twice in a group's member list, have group admins remove both identical-looking accounts so the real one can rejoin, and alert members to display-name changes, since a hijacked account may rename itself to "Deleted account" to avoid notice.
The CyberSignal Analysis
Signal 01 — Group Membership, Not Individual Prominence, Now Defines the Target Population
The snowball methodology obsoletes the traditional "am I a target" risk assessment. For CISOs at organizations with high-risk users, the briefing your staff needs is blunt: you do not have to be personally important to a foreign intelligence service to end up in its target set — you only have to share a group chat with someone who does. Build the organizational guidance around that fact. Roll out mandatory Signal Registration Lock and WhatsApp linked-device review for any staff in journalism, executive, research, government-facing, or activism roles. Audit group memberships for duplicate contacts. The defensive unit is no longer the individual; it is the contact graph.
Signal 02 — Attempted Account Takeovers Are Intelligence Opportunities, and Signal's Encryption Is Not the Weak Point
Ó Cearbhaill's investigation turned one hijack attempt into a 13,500-target campaign map. Organizations with security teams should pre-script a Signal/WhatsApp account-hijack response that treats the attempt as a lead — preserve the message, document the infrastructure, share indicators with Citizen Lab, Amnesty Security Lab, and Access Now's Digital Security Helpline. And the strategic point for boards: Signal's end-to-end encryption is working exactly as designed. Russian state actors are not attacking the cryptography — they are attacking the account and the endpoint. Your secure-communications policy needs to defend those two surfaces, because that is where the actual fight is.
What to Do This Week
- Enable Signal Registration Lock on every high-risk user's account today. Settings → Account → Registration Lock → set a 4-20 digit PIN. Do the equivalent linked-device hardening on WhatsApp. This is the single defense Ó Cearbhaill specifically recommends and it is free.
- Audit linked devices on every Signal and WhatsApp account in scope. Settings → Linked Devices. Remove any device the user does not recognize. A hijack via verification-code phishing shows up here as an unfamiliar linked device.
- Brief high-risk staff that any "Signal Support" message is phishing. Signal Support never initiates contact to request a verification code or PIN. The same applies to WhatsApp. Treat the "don't tell anyone, not even employees" framing as a definitive red flag.
- Audit group memberships for the snowball indicators AIVD and MIVD published: a contact appearing twice in a group member list, accounts renamed to "Deleted account," and unexplained display-name changes. Have group admins remove duplicate accounts so the legitimate user can rejoin.
- Pre-script a messaging-app account-hijack incident response. Treat attempts as intelligence leads, not just spam. Establish working relationships with Amnesty Security Lab, Citizen Lab, and Access Now's Digital Security Helpline for high-risk-user support before you need them.