A CVSS 10.0 Cisco SD-WAN Auth Bypass Is Under Active Attack — and UAT-8616 Has Been in This Code Since 2023
Cisco disclosed a maximum-severity authentication bypass in Catalyst SD-WAN, actively exploited as a zero-day by UAT-8616 — the same actor that has targeted this service since 2023. CISA added it to KEV, and there are no workarounds.

Cisco's Catalyst SD-WAN controllers have a maximum-severity authentication bypass, and it is already being exploited. The technical flaw is almost mundane — the authentication code simply forgot to check one device type. The threat actor exploiting it is not mundane at all: UAT-8616 has been living in this exact service since 2023.
SAN JOSE, CA — Cisco disclosed on May 14, 2026 that CVE-2026-20182 — a maximum-severity authentication bypass scored CVSS v3.1 10.0 in Cisco Catalyst SD-WAN Controller (formerly vSmart) and Cisco Catalyst SD-WAN Manager (formerly vManage) — has been actively exploited as a zero-day since at least May 2026. Cisco Talos clusters the exploitation under UAT-8616, which it assesses with high confidence to be a "highly sophisticated cyber threat actor" — and the same actor that has been exploiting CVE-2026-20127, a separate CVSS 10.0 flaw in the same component, since at least 2023. CISA added CVE-2026-20182 to its Known Exploited Vulnerabilities Catalog the same day under Binding Operational Directive 22-01. There are no workarounds. Patching is the only remediation.
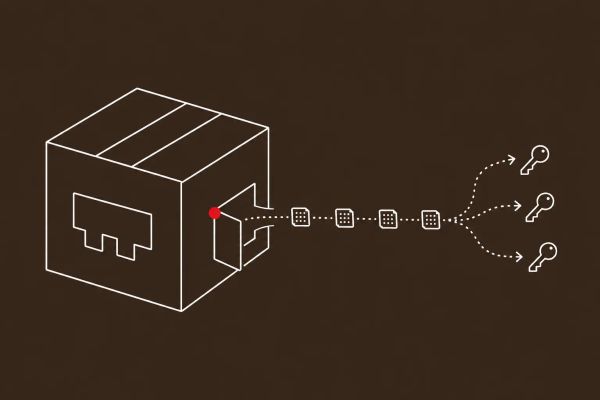
The flaw lives in the vdaemon service, reachable over DTLS on UDP port 12346 — the control-plane peering port that carries inter-controller and controller-to-edge communication, including Overlay Management Protocol messages and route advertisements. The root cause is a logic gap in the vbond_proc_challenge_ack() function: the authentication logic validates peers identifying as vSmart, vManage, and vEdge, but contains no verification code for vHub, device type 2. An attacker who sends a CHALLENGE_ACK packet claiming to be a vHub bypasses every certificate check, and the peer-authentication flag is set unconditionally to true. Critically, CVE-2026-20182 is not a patch bypass of CVE-2026-20127 — it is a distinct flaw in a similar part of the same networking stack, which is arguably worse news, because it means the attack surface itself, not a single bug, is what keeps producing maximum-severity vulnerabilities. The flaw was discovered by Stephen Fewer and Jonah Burgess of Rapid7, and it affects on-prem deployments, SD-WAN Cloud-Pro, Cisco Managed Cloud, and SD-WAN for Government (FedRAMP) alike.
The Vulnerability Is a Missing Check. The Exposure Is Your Entire SD-WAN Fabric.
The mechanics of CVE-2026-20182 are almost anticlimactic — an authentication routine that enumerates the device types it knows how to verify and simply has no branch for one of them. But the consequence is not anticlimactic at all. An unauthenticated, remote attacker who exploits it becomes an authenticated peer of the controller, and from there the path to full fabric control is short. Rapid7's analysis describes the attacker injecting an attacker-controlled public key into the vmanage-admin user's authorized SSH keys file, then logging into the NETCONF service over SSH on TCP port 830 as that high-privileged account and issuing arbitrary NETCONF commands to reconfigure the SD-WAN fabric. Control-plane access of this kind is the most valuable foothold in a network, because it does not just compromise one device — it lets an attacker rewrite the routing and trust relationships of every edge device the controller manages.
That is why this belongs in the same conversation as the year's other network-infrastructure disclosures. It lands alongside the NGINX Rift critical RCE and the wave of nation-state operations against routing and telecom infrastructure — the kind of targeting documented in Salt Typhoon's pivot to energy-sector networks. Network devices are not endpoints; they are the substrate every endpoint depends on, and a controller compromise is a strategic-level event. For any organization running Catalyst SD-WAN, CVE-2026-20182 is a patch-within-48-hours emergency, not a routine Patch Tuesday item.
UAT-8616 Has Been in This Service Since 2023 — That Is the Story
The single most important fact in this disclosure is not the CVSS score; it is the attribution. Cisco Talos clusters the exploitation of CVE-2026-20182 under UAT-8616 with high confidence — and UAT-8616 is not a new name. The same actor exploited CVE-2026-20127, a separate maximum-severity flaw in the same Catalyst SD-WAN component, going back to at least 2023. Two distinct CVSS 10.0 bugs, the same vdaemon networking stack, the same threat actor, three years apart. That pattern says something uncomfortable: UAT-8616 is not opportunistically scanning for whatever is exploitable this week. It has dedicated, sustained focus on Cisco SD-WAN control-plane infrastructure, and it has the capability to find maximum-severity authentication flaws in that stack faster than the vendor can harden it.
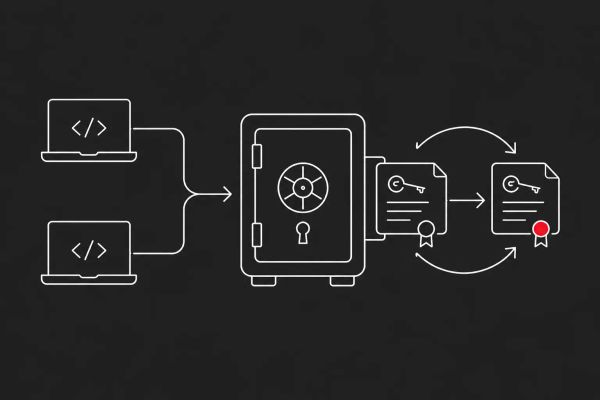
UAT-8616's post-compromise tradecraft is consistent across both campaigns and worth memorizing for threat hunting. The actor adds SSH keys to the vmanage-admin user's authorized_keys file, modifies NETCONF configurations, and escalates to root using deployed helper scripts — Talos names one, loot_run.sh, which checks for successful escalation with a hardcoded password and an su root -c id command, verifying the result by looking for the uid=0(root) string. UAT-8616 also operates from Operational Relay Box infrastructure, a layer of compromised intermediary hosts that obscures the true origin of the activity. Talos has not publicly attributed UAT-8616 to a specific nation-state, and defenders should not fill that gap with speculation — but the discipline, the multi-year focus, and the ORB tradecraft are all consistent with a well-resourced operation.
Patch Now: CISA KEV, No Workarounds, and What to Hunt For
There is no configuration change, access-control tweak, or mitigation that closes CVE-2026-20182 — Cisco is explicit that patching to a fixed software release is the only remediation. CISA's decision to add the vulnerability to the Known Exploited Vulnerabilities Catalog on May 14, the same day as disclosure, sets a Binding Operational Directive 22-01 deadline for federal civilian executive branch agencies; commercial organizations should treat that same two-week window as an operational baseline, not a federal-only obligation, given that exploitation is already underway. If immediate patching is genuinely impossible, restricting access to the DTLS UDP port 12346 control-plane interface to trusted internal networks and authorized IP addresses reduces exposure, but it is a stopgap, not a fix.
Cisco has published concrete detection guidance, and it is specific enough to act on tonight. Audit /var/log/auth.log for Accepted publickey for vmanage-admin entries originating from IP addresses you do not recognize. Run show control connections detail or show control connections-history detail and look for any peer in state:up alongside challenge-ack: 0 — that combination means a peer was authenticated without completing the challenge handshake, which is the signature of this exploit. Cross-reference the peer system IPs in those logs against the System IPs you have actually configured. If you find evidence of compromise, treat the device as compromised: open a Cisco TAC case at Severity 3 with the CVE in the title, generate an admin-tech file for review, and hunt for the UAT-8616 post-compromise artifacts — loot_run.sh, unexpected vmanage-admin SSH keys, and NETCONF configuration changes.
The CyberSignal Analysis
Signal 01 — CVE-2026-20182 Is a 48-Hour Emergency, Not a Patch Tuesday Item
This is a maximum-severity, unauthenticated, remote authentication bypass that is already being exploited in the wild, in a product class — network control-plane infrastructure — where a single compromise cascades across every managed edge device. Identify every Catalyst SD-WAN Controller and Manager deployment you operate, on-prem and cloud, and patch to the fixed release this week. There are no workarounds, so there is no slower path. Federal contractors running SD-WAN for Government should coordinate with their FedRAMP compliance teams immediately and document patch evidence for audit. If you cannot patch within days, restrict UDP port 12346 to trusted networks as a stopgap and escalate the patch internally as an incident, not a maintenance task.
Signal 02 — Network Infrastructure Is a Sustained Zero-Day Target, and UAT-8616 Proves It
The deeper lesson is the multi-year pattern. UAT-8616 has now exploited two separate CVSS 10.0 flaws in the same Cisco SD-WAN service three years apart, which means the threat is not a bug — it is an actor with durable focus on this attack surface and the capability to keep finding maximum-severity flaws in it. CISOs should update their vendor risk register to treat Catalyst SD-WAN as a known high-value, actively-hunted target, invest in detection capability for network devices that goes beyond endpoint EDR, and brief boards on the strategic risk: control-plane compromise enables broad, quiet lateral movement that endpoint-centric defenses will never see. Pre-script the "Cisco SD-WAN compromise" scenario in your incident response playbook now, including network-device forensics and chain-of-custody, because the pattern says there will be a CVE-2026-20182-class disclosure again.
What to Do This Week
- Identify every Cisco Catalyst SD-WAN Controller (vSmart) and SD-WAN Manager (vManage) deployment — on-prem and cloud — and patch to the fixed software release immediately. There are no workarounds, and exploitation is already underway.
- If you cannot patch within days, restrict access to the DTLS UDP port 12346 control-plane interface to trusted internal networks and authorized IP addresses as a stopgap — but treat patching as an open incident, not a maintenance window.
- Hunt for compromise now: audit /var/log/auth.log for unrecognized "Accepted publickey for vmanage-admin" entries, run "show control connections detail" and look for peers in "state:up" with "challenge-ack: 0", and cross-reference peer system IPs against your configured System IPs.
- If you find indicators of compromise, treat the device as compromised — open a Cisco TAC case at Severity 3 with CVE-2026-20182 in the title, generate an admin-tech file, and hunt for UAT-8616 artifacts: the loot_run.sh script, unexpected SSH keys, and NETCONF configuration changes.
- Federal contractors: the CISA KEV listing sets a BOD 22-01 deadline — coordinate with your FedRAMP compliance team for SD-WAN for Government deployments and document patch evidence for audit. Commercial organizations should treat the same two-week window as an operational baseline.