JDownloader's Website Was Hacked. Anyone Who Downloaded the Installer May Need to Wipe Their Machine.
JDownloader's website was compromised between May 6 and 7, serving Windows installers signed under bogus publisher names that deployed a Python-based RAT. The CMS was the entry point — not the build pipeline. Anyone who installed during the window should reimage.
The build pipeline wasn't touched. The CMS was. That's the third software-distribution-site compromise in 30 days — and the lesson the broader supply chain hasn't learned yet.
BERLIN — JDownloader, a free download manager with millions of users worldwide, confirmed this week that its website was compromised between May 6 and 7, 2026, and used to distribute trojanized Windows and Linux installers from the official jdownloader.org domain. The Windows payload deployed a Python-based remote access trojan; the Linux installer downloaded additional binaries and ran malware as root.
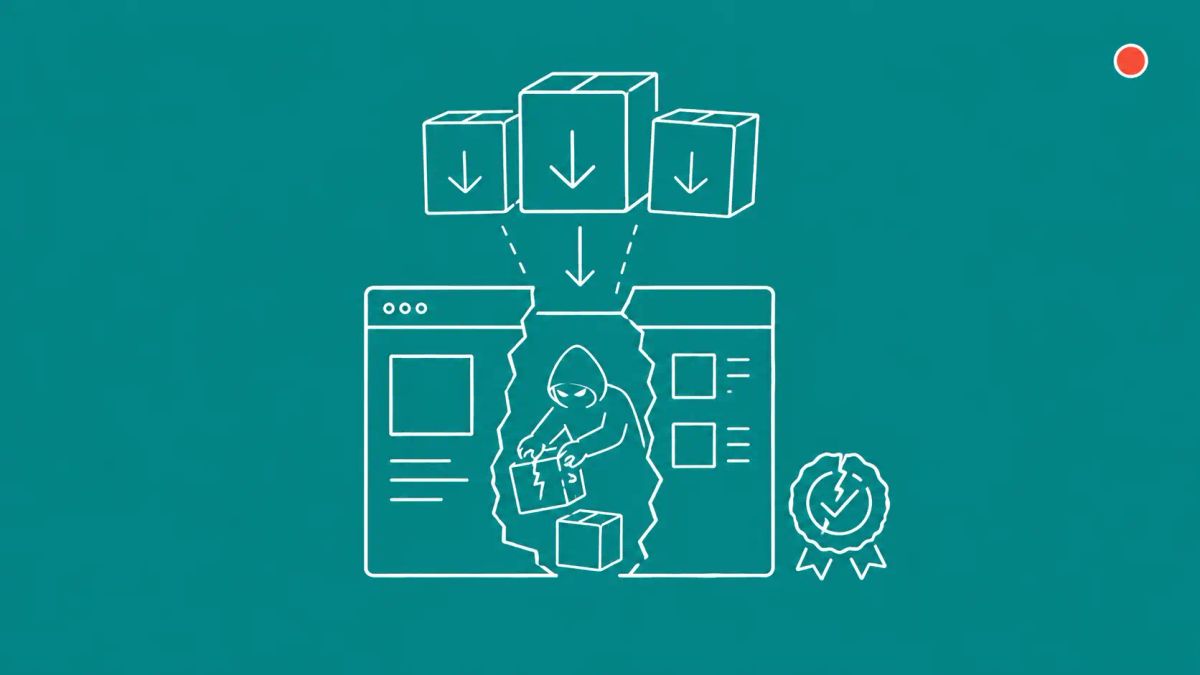
For a security practitioner, the immediate question is whether anyone in your environment downloaded JDownloader during the 24-plus hour window. The longer question is the one this incident actually illustrates: attackers never breached JDownloader's signing infrastructure or build pipeline. They modified download links through an unpatched flaw in the website's content management system, then served malware-laced installers signed under bogus publisher names that Windows SmartScreen flagged but did not block. This is the third software-distribution-site compromise in roughly 30 days, following the broader 2026 supply chain trust crisis that has put developer credentials, code-signing assumptions, and software publishing infrastructure all under simultaneous pressure.
The CMS was the entry point, not the build pipeline
JDownloader's incident report — posted to Reddit by the developer account jdownloader_dev within hours of disclosure — states that attackers exploited an unpatched vulnerability that allowed them to change website access control lists and content without authentication. The changes were made through the website's content management system and affected published pages and download links. The attacker did not gain access to the underlying server stack, the host filesystem, or operating-system-level control beyond CMS-managed web content.
That distinction matters. JDownloader's signing infrastructure was never breached. The trojanized Windows installers were not signed under JDownloader's legitimate publisher signature, AppWork GmbH. They were signed under bogus publisher names — "Zipline LLC," "The Water Team," and "Peace Team" — which is exactly what allowed Windows SmartScreen to flag them as suspicious to the Reddit user who first noticed something was wrong. The flag was a low-confidence reputation signal rather than a hard block, and the file ran anyway for users who clicked through.
The compromised binaries were limited to the Windows "Download Alternative Installer" links and the Linux shell installer. JDownloader confirmed that in-app updates, macOS downloads, Flatpak, Winget, Snap packages, the main JDownloader JAR, and existing installations were not affected, because those paths run through separate infrastructure.
What the malware does
Cybersecurity researcher Thomas Klemenc analyzed the Windows payload and described it as a heavily-obfuscated Python-based RAT acting as a modular bot framework. The malware allows attackers to execute Python code delivered from command-and-control servers, with two C2 endpoints identified in Klemenc's analysis: parkspringshotel[.]com/m/Lu6aeloo.php and auraguest[.]lk/m/douV2quu.php. The Linux payload is a shell script that downloads an archive from checkinnhotels[.]com disguised as a legitimate file, then runs malware as root and establishes persistence.
JDownloader's own remediation guidance is unambiguous and the most important operational fact in the incident report: anyone who ran a malicious installer should reinstall the operating system, and reset all passwords stored or accessed on the affected device. The development team said full malware analysis was outside the project's scope but archived the malicious installers for community analysis.
The 30-day pattern this incident extends
JDownloader is the third publicly disclosed compromise of a free-software distribution website in roughly 30 days. In April, attackers compromised the CPUID website and replaced legitimate CPU-Z and HWMonitor installers with malicious versions. In early May, the DAEMON Tools website was compromised and trojanized installers with a backdoor were served from the official domain — covered in our reporting on the broader pattern of typosquatting and trust-vector attacks against developer ecosystems. JDownloader on May 6–7 makes it three.
None of the three required attackers to breach the publisher's build pipeline or signing infrastructure. All three modified the download path or installer artifact through web-layer access — CMS exploitation in JDownloader's case, similar website-layer access in the others. For defenders, the operational implication is that the trust signal that matters is not "the file came from the official site." It is "the file came from the official site, was signed by the legitimate publisher, and matches a known-good hash."
The CyberSignal Analysis
Signal 01 — Publisher-only trust is failing
Three software-distribution-site compromises in 30 days is enough of a pattern to update fleet-management policy. Application allow-listing that trusts a signed binary because it carries any valid Authenticode signature, rather than a specific known publisher, will catch the JDownloader case (the bogus publishers should never have been on the allow list) but will miss the CPUID and DAEMON Tools cases (which used legitimate publisher signatures). The defensible control is publisher-and-version pinning for critical-path software, with file-hash validation against the publisher's own signed manifest where one exists.
Signal 02 — The CMS is the new build pipeline for attackers
Compromising a build server, signing certificate, or update mechanism is hard. Compromising a marketing CMS that publishes download links is easier and produces the same outcome from the user's perspective. If your organization distributes software, the CMS that hosts your download page now needs the same patching cadence, access control, and integrity monitoring as your build infrastructure — because the attack surface they collectively present is functionally equivalent.
Signal 03 — SmartScreen was the only thing that caught it
The JDownloader incident was discovered by a Reddit user who noticed a Windows SmartScreen warning citing unfamiliar publisher names. That is a low-confidence reputation signal that depends on an end user paying attention to a UI element most users dismiss. Enterprises should not rely on this. The detection that would have caught the bogus publishers earlier is endpoint allow-listing on a publisher-name basis, with alerting when an unfamiliar publisher signature appears in installer execution telemetry.
What to do this week
- Search your endpoint telemetry for any JDownloader installation events between May 6 and 7, 2026, particularly Windows binaries signed under "Zipline LLC," "The Water Team," or "Peace Team." Reimage any affected machine and rotate credentials accessed from it. Cleanup is not a sufficient response.
- Add the three known C2 domains —
parkspringshotel[.]com,auraguest[.]lk, andcheckinnhotels[.]com— to your egress monitoring and DNS blocklists, and look back 14 days for any prior outbound connections. - If your organization runs a CMS-fronted software download page, audit it this week. Patch level, admin credentials, MFA status, and integrity monitoring on download-link database tables are the four checks that would have stopped this incident.




