CISA Issues Urgent Patch Mandate for SharePoint Zero-Day and ‘Ancient’ Excel Bug

Following a massive Patch Tuesday release addressing 169 vulnerabilities, federal authorities have added two high-risk Microsoft flaws to the Known Exploited Vulnerabilities (KEV) catalog — including a legacy bug from 2009.
WASHINGTON, D.C. — The Cybersecurity and Infrastructure Security Agency (CISA) has expanded its Known Exploited Vulnerabilities (KEV) catalog, adding a critical SharePoint zero-day and a 17-year-old Microsoft Excel vulnerability. The move comes as Microsoft’s April 2026 Patch Tuesday addressed a staggering 169 flaws, two of which were confirmed to be under active exploitation before fixes were available.
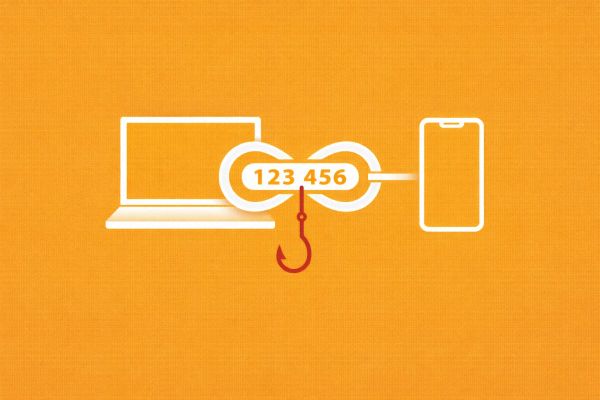
The two additions represent a growing trend of threat actors utilizing a "dual-track" strategy: weaponizing the latest software architectural gaps while reaching back nearly two decades to exploit legacy code that remains embedded in modern enterprise environments.
The SharePoint Breach: CVE-2026-32201
The primary focus of the April update is CVE-2026-32201, an "Improper Input Validation" (Spoofing) vulnerability in Microsoft SharePoint Server. Despite being rated as "Medium" severity by CVSS standards, Microsoft and CISA elevated its priority after confirming "exploitation detected" in the wild.
The flaw allows an attacker to bypass security prompts or hijack sessions within a SharePoint environment, potentially serving as a gateway for lateral movement into broader Microsoft 365 tenants. Federal agencies have been ordered to remediate this flaw by April 28, 2026.
The 17-Year-Old "Ghost": CVE-2009-0238
In a move that surprised some security researchers, CISA also added CVE-2009-0238, a Remote Code Execution (RCE) vulnerability in Microsoft Office Excel 2007. The bug, which involves an "invalid memory pointer" error, was once a staple of early malware campaigns like Trojan.Mdropper.AC.
Its sudden reappearance in the KEV suggests that state-sponsored actors or sophisticated ransomware groups are successfully targeting older versions of Office still found in air-gapped systems or industrial control environments that lack modern endpoint protection.
The CyberSignal Analysis
Signal 01 — The Resurgence of Legacy Exploits
The inclusion of a 2009 bug is a stark reminder that vulnerabilities don't "expire." For CISOs, this is a signal that "vulnerability management" cannot just focus on the latest CVEs. Threat actors are performing "archaeological" security research, betting that organizations have stopped monitoring for exploits that were supposedly "solved" during the Windows 7 era.
Signal 02 — The SharePoint Perimeter
SharePoint remains a "soft target" for identity-based attacks. Because it sits at the intersection of external collaboration and internal file storage, even a "Spoofing" vulnerability like CVE-2026-32201 can be leveraged to steal high-value credentials or exfiltrate sensitive IP. The speed of this KEV addition (less than 48 hours after Patch Tuesday) indicates that the volume of active attacks is significant.