Tycoon 2FA Disruption Drives Phishers Toward "Device Code" Exploitation
Following a coordinated global takedown of the Tycoon 2FA infrastructure, decentralized threat actors are abandoning traditional Adversary-in-the-Middle (AiTM) kits in favor of more resilient device code phishing tactics.
LONDON, UK — The landscape of Multi-Factor Authentication (MFA) bypass is undergoing a rapid transformation. Just weeks after an international law enforcement operation led by Europol and Microsoft severely disrupted the Tycoon 2FA phishing-as-a-service empire, security researchers are observing a significant "scatter" effect. Deprived of their primary infrastructure, Tycoon’s former affiliates are increasingly adopting Device Code Phishing — a sophisticated technique that leverages legitimate authentication flows to hijack enterprise accounts.
The transition marks the end of Tycoon’s long-standing reign as the "crown jewel" of phishing kits, but analysts warn that the replacement tactics may be harder for traditional security filters to detect.
Tactical Shift: AiTM vs. Device Code
The Post-Takedown Vacuum
Tycoon 2FA rose to prominence by automating Adversary-in-the-Middle (AiTM) attacks, allowing even low-skill criminals to intercept session cookies in real-time. According to reports from SpyCloud and The Hacker News, the takedown of Tycoon's central servers forced thousands of users to seek alternative methods.
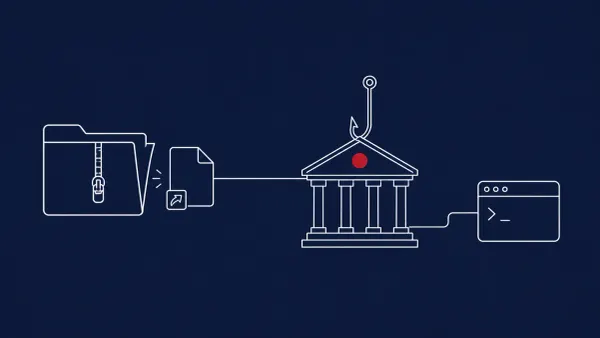
Rather than simply moving to a different AiTM kit, many have pivoted to Device Code Phishing (also known as "OAuth Device Flow Phishing"):
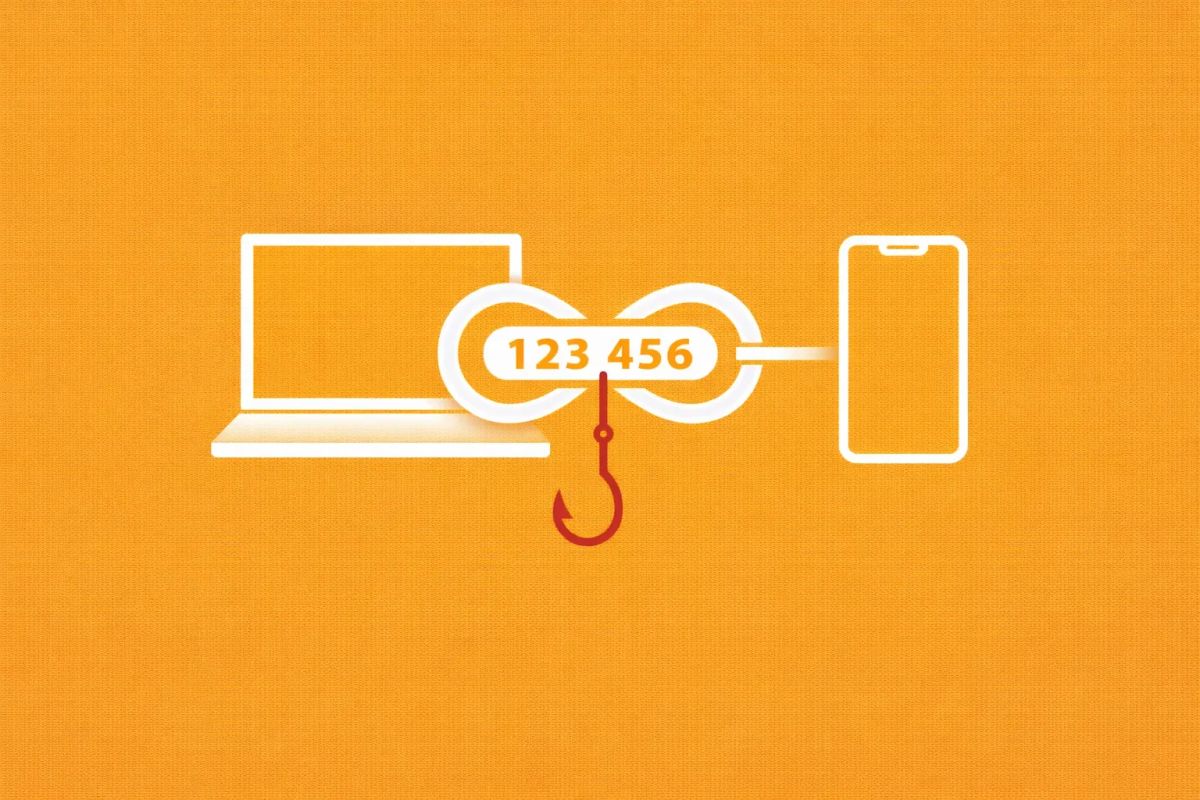
- The Mechanism: Instead of a fake login page, attackers send a message (often via email or Teams) asking the user to "verify" their device by visiting a legitimate Microsoft or Google URL and entering a specific code.
- The Deception: Because the URL (
microsoft.com/devicelogin) is authentic, the attack often bypasses email security gateways and doesn't trigger "suspicious site" warnings in browsers. - The Payoff: Once the user enters the code provided by the attacker, the attacker’s device is authorized to access the user’s account, granting them a persistent token that bypasses MFA entirely.
The disruption of Tycoon 2FA hasn't stopped the demand for session-hijacking tools; it has simply forced an evolution into more sophisticated automation. As we detailed in our report on Microsoft 365 Users Targeted by AI-Augmented EvilTokens Phishing Service, threat actors are now leveraging AI to scale "device code" attacks that bypass traditional MFA filters.
Rather than simply moving to a different AiTM kit, many former Tycoon affiliates have pivoted to these EvilTokens-style tactics — a technique that leverages legitimate authentication flows to hijack enterprise accounts.
The "Scottish Connection" and Financial Impact
The disruption of Tycoon-linked activities has also led to legal breakthroughs. As reported by The Hillingdon Times, a Scottish national recently admitted to a role in a £5.9 million ($7.4M) cyber fraud scheme that utilized similar credential-harvesting infrastructure. This case highlights the massive financial scale of the "phishing-as-a-service" economy that Tycoon helped build.
The CyberSignal Analysis
Signal 01 — The Resilience of the Phishing Economy
The "Signal" from the Tycoon takedown is that infrastructure disruption is a temporary fix, not a cure. The rapid pivot to device code phishing shows that the "Market" for stolen session tokens is too lucrative to disappear. For B2B organizations, the takeaway is that your security posture cannot rely on the "Takedown of the Week." You must assume your digital identity perimeter is under constant, adaptive pressure.
Signal 02 — Conditional Access is the New Firewall
Device code phishing exploits a legitimate feature intended for "headless" devices like smart TVs or printers. The "Signal" for IT administrators is that you must restrict the Device Code Flow using Conditional Access policies. If your employees don't need to sign into TVs or IoT devices with their corporate credentials, this feature should be disabled globally to close the exploit path used by Tycoon’s successors.