CISA Expands KEV Catalog with Seven Actively Exploited Flaws Across Microsoft, Adobe, and Fortinet

The addition of both legacy vulnerabilities and 2026 zero-days signals a "two-front war" for defenders: securing modern cloud-facing infrastructure while purging decade-old exploits still being used in the wild.
WASHINGTON, D.C. — The Cybersecurity and Infrastructure Security Agency (CISA) has added seven new vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog. The update, released on April 13, 2026, mandates that Federal Civilian Executive Branch (FCEB) agencies remediate these flaws within two weeks — with one critical exception.
The latest additions highlight a diverse threat landscape where attackers are weaponizing everything from 2012-era Microsoft Office libraries to unauthenticated SQL injection flaws in modern enterprise management servers. While the KEV catalog serves as a "must-patch" list for federal agencies under Binding Operational Directive (BOD) 22-01, it has become the gold standard for private-sector prioritization in an era where the window from disclosure to exploitation has effectively collapsed.
April 2026 KEV Additions
The Critical Priority: Fortinet SQL Injection
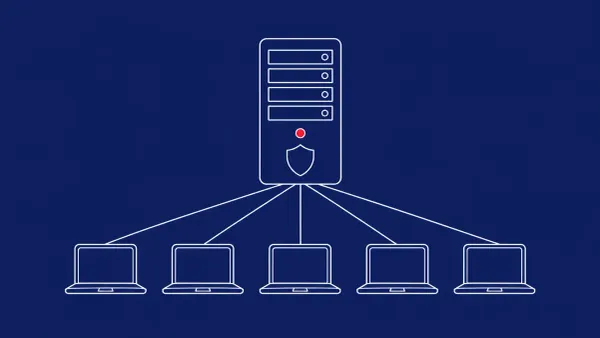
The most urgent entry in this batch is CVE-2026-21643, a critical SQL injection vulnerability in Fortinet’s FortiClient Enterprise Management Server (EMS). Unlike the other six entries, which have a standard two-week deadline, CISA has set an aggressive April 16, 2026 cutoff for this flaw.
The vulnerability allows an unauthenticated remote attacker to execute unauthorized code or administrative commands via specifically crafted HTTP requests. Because FortiClient EMS acts as a central hub for security policies across thousands of employee devices, a breach here provides a direct pathway for lateral movement throughout an entire corporate network.
The "Legacy" Threat: 14-Year-Old Exploits Return
In a move that surprised some analysts, CISA included CVE-2012-1854, a 14-year-old vulnerability in Microsoft Visual Basic for Applications (VBA). Its inclusion in 2026 confirms that threat actors are still successfully using "retro" exploits to target organizations running legacy documents or unpatched archive systems.
"Attackers don't always need a zero-day if the 'old-day' still works," noted one forensic researcher. "The inclusion of a 2012 CVE in a 2026 catalog is a reminder that technical debt is a security debt that eventually comes due."
The CyberSignal Analysis
Signal 01 — The "Collapse" of the Patch Window
The inclusion of these vulnerabilities in the KEV catalog so close to their initial disclosure highlights a critical trend: the window between a vulnerability’s public release and its active exploitation has effectively collapsed. For high-value targets like Fortinet EMS, threat actors are now weaponizing exploits within days, if not hours. This is a signal that "standard" patching cycles — such as once-monthly updates — are no longer sufficient for internet-facing management consoles. Organizations must pivot toward automated, high-priority patching for any asset listed in the KEV.
Signal 02 — Ransomware’s "Slow Burn" Phasing
The inclusion of CVE-2023-21529 (Microsoft Exchange) is particularly concerning. Microsoft recently linked this specific exploit to the Medusa ransomware gang. This confirms that ransomware groups are not just looking for the newest zero-days; they are systematically scanning for "year-old" flaws in mail infrastructure where they can hide in the noise of larger enterprise networks.