The Voice of Deception: New ATHR Platform Automates Vishing via AI Agents

A sophisticated "Vishing-as-a-Service" (VaaS) platform named ATHR has surfaced, utilizing high-fidelity AI voice clones to automate large-scale credential theft and bank fraud.
SAN FRANCISCO, CA — Security researchers have uncovered a potent new threat in the social engineering landscape: ATHR, a specialized vishing (voice phishing) platform that leverages generative AI to conduct end-to-end automated attacks. Unlike traditional vishing, which requires human callers, ATHR uses realistic AI voice agents capable of holding convincing, real-time conversations with victims to extract one-time passwords (OTPs) and login credentials.
The platform is being marketed in underground forums as a scalable solution for "callback phishing" (TOAD) attacks, targeting users of major services including Google, Microsoft, and various cryptocurrency exchanges.
ATHR Platform Capabilities
How ATHR Automates the "Art of the Con"
ATHR represents a significant shift from manual "boiler room" operations to algorithmic deception. According to technical reports from Abnormal Security and BleepingComputer, the platform functions as a streamlined dashboard for cybercriminals.
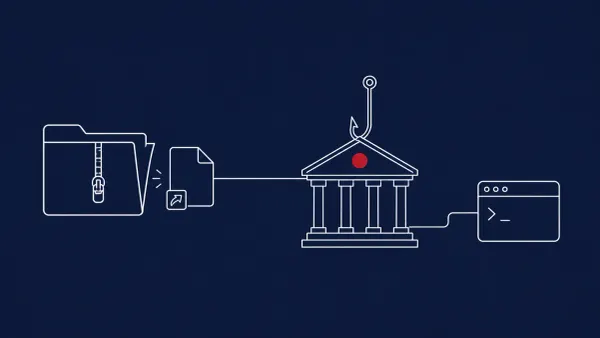
The attack sequence typically follows a "TOAD" (Telephone-Oriented Attack Delivery) model:
- The Hook: The victim receives a fraudulent email or SMS — often a "subscription renewal" or "unauthorized login" alert — containing a customer service phone number.
- The Connection: When the victim calls the number, they are connected to the ATHR platform’s AI agent rather than a human.
- The AI Dialogue: The AI agent uses Natural Language Processing (NLP) to respond to the victim's questions. It is programmed to create a sense of urgency, eventually asking the victim to "verify" their identity by providing a code sent to their phone.
- The Extraction: As the victim speaks the OTP or types it into their keypad, ATHR’s backend captures the data in real-time, allowing the attacker to bypass Multi-Factor Authentication (MFA) and hijack the account.
The Asterisk and VoIP Connection
Research from Captech Group indicates that ATHR is specifically designed to integrate with Asterisk, an open-source VoIP framework. This integration allows attackers to spoof local caller IDs and manage thousands of concurrent calls, making the operation significantly more resource-efficient than traditional phishing.
The AI voices used by ATHR are noted for their lack of "robotic" cadence, incorporating realistic stammers, breathing sounds, and professional "customer service" tones that can deceive even tech-savvy users.
The CyberSignal Analysis
Signal 01 — The End of the "Accent" Heuristic
For years, employees were trained to spot vishing by listening for specific accents or "noisy" backgrounds typical of offshore call centers. ATHR effectively kills this heuristic. The "Signal" for organizations is that digital identity can no longer be verified by voice alone. High-fidelity AI clones mean that "Who is on the other end of the line" is now a purely technical question, not a gut feeling.
Signal 02 — Moving Toward Phishing-Resistant MFA
ATHR’s success relies on the victim handing over a temporary code (OTP). This incident is a massive "Signal" that SMS and voice-based MFA are no longer sufficient for high-value accounts. To counter platforms like ATHR, B2B enterprises must accelerate the transition to hardware security keys (FIDO2) or passkeys, which are inherently resistant to vishing because there is no "code" for a victim to repeat to an AI agent.