Across Party Lines and Industry, the Verdict Is the Same: CISA Is in Trouble
After more than a year of the second Trump administration, observers across the political spectrum told CyberScoop that CISA has been significantly diminished, losing roughly one-third of its personnel.
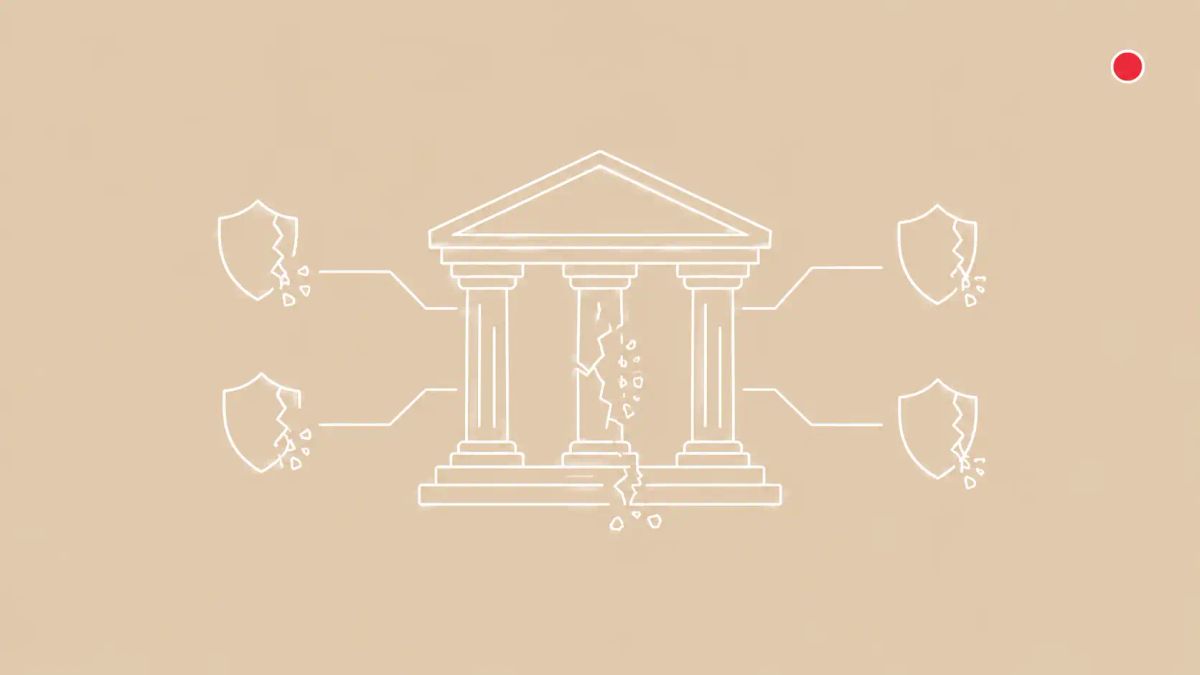
Sledgehammer, not scalpel. Even officials who agreed CISA needed reform say the second-term cuts have crossed a line that costs defenders real capability. Plankey withdrew. Gottumukkala was reassigned. Andersen is steering an agency operating at roughly 38 percent staff.
WASHINGTON, D.C. — More than a year into the second Trump administration, CyberScoop's Tim Starks reported a near-unanimous verdict from former CISA officials, industry partners, and bipartisan lawmakers: the Cybersecurity and Infrastructure Security Agency has been significantly diminished in its ability to fulfill its core missions. The agency has lost roughly one-third of its personnel since January 2025, shuttered entire divisions, and is operating at approximately 38 percent staff levels during the ongoing federal shutdown that began February 14, 2026. James Lewis at the Center for Strategic and International Studies summarized it: CISA needed surgery, but what it received was surgery with a sledgehammer rather than a scalpel.
The single most important fact is leadership. CISA has been without a permanent Senate-confirmed director since Trump entered office in 2025. Sean Plankey withdrew his nomination in April 2026 after 13 months waiting for Senate confirmation, citing a string of holds including one from Sen. Rick Scott unrelated to cybersecurity. Acting Director Madhu Gottumukkala was reassigned in late February 2026 to a strategic implementation role at DHS headquarters after a tumultuous tenure that included reports of uploading sensitive contract data to ChatGPT and failing a counterintelligence polygraph. Nick Andersen, the agency's executive assistant director for cybersecurity, now leads CISA in an acting capacity. The pattern aligns with CISA's reduced-capacity resilience push under CI Fortify and the broader federal cyber workforce crisis playing out across the SFS scholarship program.
| Who is affected | |
|---|---|
| Critical infrastructure operators CISA advisories, KEV updates, JCDC engagement all at reduced capacity | FCEB agencies and federal CISOs Coordination and threat hunting support diminished |
| State and local government cyber teams Two ISACs serving state and local governments lost funding | Sector ISACs and industry partners Coordination relationships described as broken or unanswered |
The scale of the cuts
CISA has lost approximately one-third of its workforce since Trump returned to office. The Trump administration has cut or plans to cut more than 1,000 personnel at the agency. The Stakeholder Engagement Division — the team responsible for the industry coordination relationships that defined the agency's approach during its first six years — lost 96 of 189 staff between January 2025 and early 2026, a 51 percent reduction. The election security team has been cut. Two Information Sharing and Analysis Centers serving state and local governments have lost funding.
Senior leaders have departed across counter-ransomware initiatives, threat hunting, and secure software development. Contracts at risk include threat detection in critical infrastructure networks, vulnerability tracking, and industry team collaboration. During the shutdown, hundreds of CISA personnel were reassigned to other DHS components to support immigration enforcement work.
The leadership instability
Plankey's April 2026 withdrawal closed a 13-month chapter in which the agency could not get a confirmed director seated. Senate holds during Plankey's nomination came from multiple senators including Sen. Rick Scott, who blocked the nomination over a Coast Guard contract matter unrelated to cybersecurity. Gottumukkala's reassignment came after what one former CISA employee described as amateur hour, with reports including uploading sensitive government documents to ChatGPT, failing a counterintelligence polygraph, and attempting to oust longtime agency CIO Robert Costello. Andersen — described by CISA employees and Plankey himself as one of the most competent cybersecurity people in the country — now runs the agency from the cybersecurity division he was previously leading.
Industry side: broken coordination
Starks's reporting captures the operational consequence in the words of former officials and industry partners: broken relationships, unanswered requests for help, and serious questions about whether CISA can handle a major crisis. The programs at greatest risk are the ones CISA built specifically to support sector-by-sector coordination: High-Value Asset assessments, attack-path modeling, the Joint Cyber Defense Collaborative, State, Local, Tribal, and Territorial services, ransomware readiness assessments, vulnerability scans, tabletop exercises, election infrastructure support, and the Center for Internet Security's MS-ISAC coordination. None of these can be reconstituted from outside the agency on a short timeline.
Andersen's pushback, and the bipartisan budget fight
Andersen publicly disputed the diminished-capability framing in a September 2025 Billington Cybersecurity Summit speech, saying there was not a single instance he could think of where CISA had failed to connect a partner with the right level of resources. Industry observers accept Andersen's good faith but note that an acting director with one-third less staff and a 17 percent budget cut proposal cannot deliver the same operational tempo CISA delivered in 2023 or 2024. The Trump fiscal 2026 budget proposal called for a 491 million dollar cut to CISA, nearly 17 percent of the agency's 3 billion dollar budget. House Appropriations approved a scaled-back 135 million dollar reduction in a bipartisan resistance to deeper cuts.
The CyberSignal Analysis
Signal 01. Bipartisan and bi-industry consensus is rare and significant
Cyber policy in Washington is normally a target-rich environment for partisan framing. The unusual feature of the CISA debate in 2026 is the lack of disagreement across the political spectrum and across industry about the operational reality. Republicans including Rep. Andy Garbarino are arguing for restoring CISA capacity. Industry voices from CSIS, the Cyberspace Solarium Commission successor, and former officials from both Republican and Democratic administrations are saying the same thing.
Signal 02. Re-architect, do not just supplement
Defenders depending on CISA's KEV catalog, JCDC engagement, and sector ISAC coordination need to treat those services as degraded rather than absent. The right response is not to wait for restoration but to re-architect: commercial vulnerability intelligence as primary, CISA inputs as one of several feeds; sector ISAC engagement as primary, JCDC as supplemental; commercial IR retainers as primary, CISA coordination as supplemental.
Signal 03. Plan around 3-5 years
The combination of personnel cuts that have already happened, budget reductions through fiscal 2026 and proposed fiscal 2027, no permanent director, and the SFS scholarship pipeline collapse means CISA's coordination capability will not return on the timeline of an election cycle. Some institutional knowledge is gone permanently. Plan around 3-5 years of degraded federal cyber coordination as the baseline.
What to do this week
- Re-rank your threat intelligence sources. Supplement CISA-issued KEV catalog updates with commercial intelligence, sector ISAC advisories, and vendor security advisories. KEV remains valuable but should not be your sole indicator.
- Pre-script your IR playbook for a CISA-cannot-help scenario. Pre-establish relationships with your sector ISAC, commercial IR retainer firms, state government cybersecurity coordinators, and your industry trade association.
- For organizations with international critical infrastructure exposure, increase reliance on Five Eyes partner coordination — NCSC UK, ACSC Australia, CSE Canada, and NCSC New Zealand.