CISA Tells Critical Infrastructure Operators to Plan for Weeks of Cyber Isolation
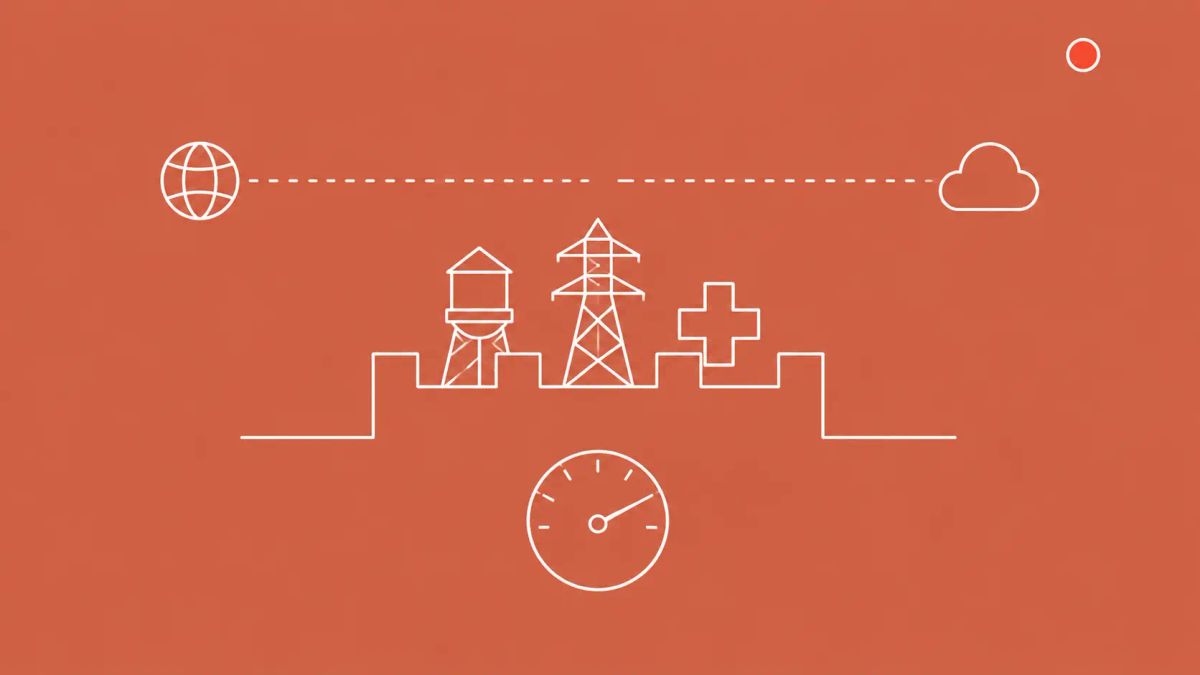
The Cybersecurity and Infrastructure Security Agency launched a new initiative on Tuesday, May 5, 2026, called CI Fortify that pushes critical infrastructure operators across all 16 federally-designated sectors to prepare for sustained operations during geopolitical conflict, including scenarios in which third-party connections become unreliable and adversaries gain partial access to operational technology networks. The initiative focuses on two emergency planning objectives, isolation and recovery, and explicitly tells operators to plan for weeks to months of safe operations while isolated from IT networks and third-party tools.
On Tuesday, May 5, 2026, CISA released CI Fortify as strategic guidance to help critical infrastructure entities across all sectors prepare to operate through a crisis or conflict, continuing vital service delivery even as their systems are under attack. The guidance is published at cisa.gov/topics/industrial-control-systems/ci-fortify and is paired with a CISA commitment to conduct targeted technical assessments of critical infrastructure entities. CISA Acting Director Nick Andersen framed the initiative as a response to a geopolitical-cyber-conflict threat environment in which Iranian-affiliated cyber actors have been exploiting programmable logic controllers in U.S. water, energy, and government services, and Russian military intelligence actors have been exploiting vulnerable routers to steal sensitive information from government, military, and critical infrastructure targets.
CI Fortify is built around two emergency planning objectives. The first is isolation: proactively disconnecting from third-party and business networks to safeguard operational technology, such as industrial control systems, from cyber attack during a crisis. The second is recovery: quickly restoring any systems that an adversary may successfully compromise. The threat-model assumption underpinning both objectives is the operationally consequential element. CISA tells operators that, for planning purposes, they should assume that in a conflict scenario third-party connections, including telecommunications, internet, vendors, service providers, and upstream dependencies, will be unreliable, and that threat actors will have some access to the operational technology network.
The single most operationally consequential element of CI Fortify is the duration framing. CISA is now publicly telling U.S. critical infrastructure operators to plan for sustained operation in cyber-isolation from the broader internet, for weeks to months, during a geopolitical conflict scenario. That represents a significant policy shift from the typical patch-and-detect posture toward an assume-breach, sustain-operations posture, and it pairs with parallel international efforts in Australia, Poland, and the European Union to suggest a global recalibration of critical infrastructure cyber-resilience expectations.
| CISA CI Fortify Profile | |
|---|---|
| Detail | Information |
| Launched | Tuesday, May 5, 2026 (CISA) |
| Format | Strategic guidance (not a Binding Operational Directive); paired with targeted CISA technical assessments |
| Primary attribution | CISA Acting Director Nick Andersen |
| Sectoral scope | All 16 federally-designated critical infrastructure sectors, including water utilities, energy, transportation, healthcare, nuclear facilities, food and agriculture |
| Two planning objectives | Isolation (proactively disconnect OT from third-party and business networks); Recovery (rapid restoration of compromised systems) |
| Operating duration | Weeks to months while isolated from IT networks and third-party tools |
| Threat-model assumption | Third-party connections will be unreliable; threat actors will have some access to the OT network |
| Cited Iranian threat | CyberAv3ngers and other Iranian-affiliated actors exploiting PLC vulnerabilities in U.S. water, energy, and government services (April 2026 joint advisory) |
| Cited Russian threat | Russian military intelligence actors exploiting vulnerable routers to steal sensitive information from government, military, and critical infrastructure (April 2026 NSA/FBI joint advisory) |
| Geopolitical context | Threats detected following U.S. and Israel attacks on Iran beginning February 28, 2026 |
| Implementation feature | Operators encouraged to maintain clear system documentation to reduce recovery time and lower IR costs |
| International parallels | Australia Cyber Incident Review Board (CIRB); Poland's ABW public report on Russian water-utility intrusions; EU Cyber Solidarity Act |
The Threat-Model Shift That Changes Everything
For most of the past decade, U.S. critical infrastructure cyber posture has been built around a patch-and-detect model: identify vulnerabilities, deploy patches, monitor for indicators, respond to incidents. CI Fortify does not abandon that model, but it adds a new and operationally distinct layer on top of it. The new layer assumes the patch-and-detect model has failed at the third-party boundary, that an adversary already has some access to OT, and that telecommunications and internet connectivity will become unreliable for an extended period. The defender's job, under this model, is no longer to keep the adversary out, it is to continue delivering critical services anyway.
That assumption set is jarring on first read. Operators are accustomed to threat models that say credible adversaries might breach IT, possibly pivot to OT, and need to be detected and ejected. CI Fortify says, in effect, plan for a world where ejection is impossible on the relevant timescale, where the third-party tools you ordinarily depend on are not available, and where you will need to operate the water utility, the regional power system, the hospital network, or the rail dispatcher's office for weeks to months in that condition. The implication is that resilience-by-design has to be designed in now, not assembled under pressure.
What Isolation Actually Means Operationally
Isolation, in CI Fortify's framing, is not the air-gap-by-default architecture some OT environments aspire to. It is a deliberate, time-bounded, posture-shift action: when a conflict crisis begins, operators proactively disconnect OT from third-party and business networks to safeguard control systems. The implications cascade through the operational stack. Cloud-based historian, vendor remote-support tunnels, internet-based monitoring dashboards, software-license validation calls home, EDR agent telemetry, identity-provider federation: all of these become unavailable on the operator's side of the firewall once isolation is invoked. Many will not work at all without those links; some will fail in unexpected ways; a few will degrade silently.
That is why the practical work of CI Fortify is not future-tense planning, it is present-tense documentation and rehearsal. CISA's guidance specifically encourages operators to maintain clear system documentation to reduce recovery time and lower incident-response costs. Documentation here means manual operating procedures, paper runbooks, locally-cached schematics, off-platform backups, and the institutional knowledge that lets a control-room operator run a water plant or substation without the cloud-based dashboards they have come to depend on. For most operators, that documentation has atrophied since digitization. Reconstructing it is the actual deliverable.
Why CISA Is Naming Iran and Russia
CI Fortify cites two specific motivating threats. The first is an April 2026 CISA-led joint advisory documenting Iranian-affiliated cyber actors, including the group tracked as CyberAv3ngers, exploiting vulnerabilities in programmable logic controllers used across U.S. critical infrastructure sectors, including government services, water and wastewater systems, and energy facilities. The second is an April 2026 NSA and FBI joint advisory documenting Russian military intelligence actors exploiting vulnerable routers to steal sensitive information from government, military, and critical infrastructure targets. CISA explicitly ties the threat environment to a geopolitical crisis posture, with U.S. and Israel attacks on Iran beginning February 28, 2026, as the inflection point for the current threat landscape.
What is editorially distinct about CI Fortify is the framing. CISA is not saying these threats might materialize, the agency is saying they are already active, that the threat actors already have at least partial access to PLCs and routers, and that the question for operators is no longer prevention, it is graceful degradation. That is a substantially harder posture for executives to deprioritize than the typical worst-case scenario framing.
The Global Recalibration That CI Fortify Sits Inside
CI Fortify is the third major critical-infrastructure cyber-resilience policy event of May 2026 and the most consequential of the three for U.S. operators. The first was Australia's launch of the Cyber Incident Review Board on May 5, also covered in The CyberSignal's coverage of the Australian CIRB, which establishes a no-fault post-incident review function modeled on aviation safety boards. The second was the public disclosure by Poland's ABW of detailed Russian-linked attacks on Polish water-utility systems, covered in detail by The CyberSignal, which documents the very threat scenario CI Fortify is designed to address. Adding the EU Cyber Solidarity Act, which empowers ENISA with a similar review function, the international picture is one of coordinated allied recalibration of CI cyber posture.
That coordination has not been formally announced, but the timing and substance overlap is hard to read as coincidental. Allied governments are converging on a common posture: that CI cyber-resilience for the next decade has to be planned around sustained adversary access, partial connectivity, and prolonged conflict scenarios, and that post-incident learning has to be institutionalized rather than ad-hoc. The CyberSignal's threat-intelligence coverage tracks how this threat actor and policy landscape has matured across 2025 and 2026.
Voluntary in Name, Practically Mandatory
CI Fortify is published as guidance, not a Binding Operational Directive. That voluntariness affects the compliance picture, but operators should not read it as a license to delay. CISA has committed to conducting targeted technical assessments of critical infrastructure entities, and the assessments will surface which operators have implemented the isolation-and-recovery posture. Sector-specific regulators, including FERC for electricity, TSA for transportation, EPA for water, and NRC for nuclear, all have separate critical-infrastructure cyber rulemakings in progress. CI Fortify's voluntary guidance will inevitably influence those rulemakings; engaging now is materially more effective than reacting to final rules.
The launch context is also operationally relevant. CISA released CI Fortify against a backdrop of staffing reductions and a recent multi-month operational disruption. The agency is, in effect, prioritizing the most consequential of the resilience initiatives within constrained capacity. That makes CI Fortify either a notable comeback signal or a strategic prioritization despite reduced resources, and operators should plan accordingly. The targeted technical assessments will not be ubiquitous; they will be selective. Being one of the early-engaged operators is materially better than being one of the operators discovered later by an assessment to have not implemented the guidance.
Defender Actions for the Next 90 Days
- Conduct an isolation tabletop exercise. Simulate a scenario in which all third-party network connections (cloud SaaS, vendor remote-support, internet-based monitoring, telecommunications) are unavailable for 72 hours. Document what services your organization can continue delivering, which fail, and which fall into a degraded-but-functional state. The output of the tabletop is the input to the rest of the planning work.
- Inventory and harden the OT-IT boundary. CI Fortify's threat model assumes attackers will have some access to OT networks. Your defensive posture should not depend on a perfect IT-OT segmentation; assume compromise of the IT side and design OT controls that work regardless. Network-level segmentation, separate authentication systems for OT, and air-gappable engineering workstations are the practical controls.
- Document and rehearse manual-mode operations. For water utilities this means manual valve operation, manual chemical-dosing, manual sampling protocols. For energy, this means manual switching and local-instrument-only operations. For transportation, this means analog-radio dispatch. CI Fortify implicitly assumes operators have these procedures; if they have atrophied since digitization, restoring them is the immediate priority. Include training and rotation; documented procedures that no current staff has executed are an unfunded liability.
- Establish out-of-band communications. Phone, satellite, HF/VHF radio, designated meeting points. A scenario where the internet is unreliable means standard incident-response coordination fails. Preposition the alternatives and rehearse the procedures that activate them. Include cross-organizational coordination with sector ISAC partners, neighboring utilities, mutual-aid networks, and CISA regional coordinators.
- Reduce supply-chain exposure to designated adversary countries. The CI Fortify threat model explicitly assumes adversary access via supply-chain pathways. Components, software, services, or workforce sourced from designated adversary countries are now legacy risks that need active remediation, not gradual transition. Audit your component supply chain, software bill of materials, and managed-service vendors with that lens.
The CyberSignal Analysis
Signal 01 - The threat model is now public, and that changes the executive conversation
Until CI Fortify, the case for cyber-resilience investment in CI was framed as incident prevention. CI Fortify reframes it as national security continuity during conflict. That reframing is materially harder for executives to defer, because it moves the question from speculative risk management to specific scenario planning, with named adversaries (Iran, Russia), named threat actors (CyberAv3ngers, Russian military intelligence), named target categories (water, energy, transportation, healthcare), and named operating-duration expectations (weeks to months). For boards considering whether to fund the resilience work CI Fortify implies, the framing has shifted from build a business case to align with national policy. Use this initiative as the catalyst for unblocking previously-deferred resilience investments.
Signal 02 - The voluntary-but-assessed structure is the year's clearest CISA enforcement signal
CI Fortify is technically voluntary, but the targeted technical assessment commitment converts the voluntariness into selective enforcement. CISA can, in practice, assess any operator and surface compliance gaps, and those gaps will then be visible to sector regulators that are concurrently writing rules. The combined posture, voluntary guidance plus selective assessment plus regulatory cross-pollination, is more enforceable than a pure BOD because it scales with available capacity rather than requiring uniform application. Operators that engage early shape the assessment criteria; operators that wait are evaluated against criteria they did not influence. The structural advantage of early engagement is real and time-bounded.
Signal 03 - Manual-mode operations are the year's most underrated CI capability
The hardest implication of CI Fortify is also the most quietly transformative. Operators are being told to plan for weeks-to-months operations under partial isolation. That implies functional manual-mode procedures, trained staff who have rehearsed them, paper runbooks, locally-cached schematics, and the institutional knowledge that 25 years of digitization has made optional in most CI environments. Restoring that capability is expensive and slow, but it is the actual difference between an organization that can deliver service in the CI Fortify scenario and an organization that cannot. CISOs and operations leaders who have inherited a digitization roadmap that assumed permanent connectivity should treat CI Fortify as the trigger for a partial reversal: not a return to analog, but a deliberate retention of analog-capable fallback that the digitization era had quietly let lapse. The operators who get this right will be the ones still delivering service when others cannot.