Mini Shai-Hulud Worm Compromises TanStack, Mistral AI, and 170 Packages
TeamPCP's Mini Shai-Hulud worm hit 170+ packages May 11, including TanStack, Mistral AI, and Guardrails AI. First npm worm to ship valid SLSA Build Level 3 provenance for malicious code.
The first npm worm to produce validly-attested malicious packages has compromised TanStack, Mistral AI, UiPath, and Guardrails AI in one day, and rewritten what SLSA Level 3 provenance is supposed to anchor.
SAN FRANCISCO — At 19:20 UTC on Monday, May 11, 2026, TeamPCP launched a coordinated supply chain attack that compromised more than 170 npm and PyPI packages in six minutes. Compromised namespaces included 42 TanStack packages — with @tanstack/react-router at roughly 12 million weekly downloads — 65 UiPath packages, Mistral AI's npm and PyPI clients, the OpenSearch JavaScript client, the Guardrails AI PyPI package, and more than a dozen Squawk packages. The campaign was dubbed "Mini Shai-Hulud: Here We Go Again" by the attacker and assigned CVE-2026-45321 with a CVSS score of 9.6.
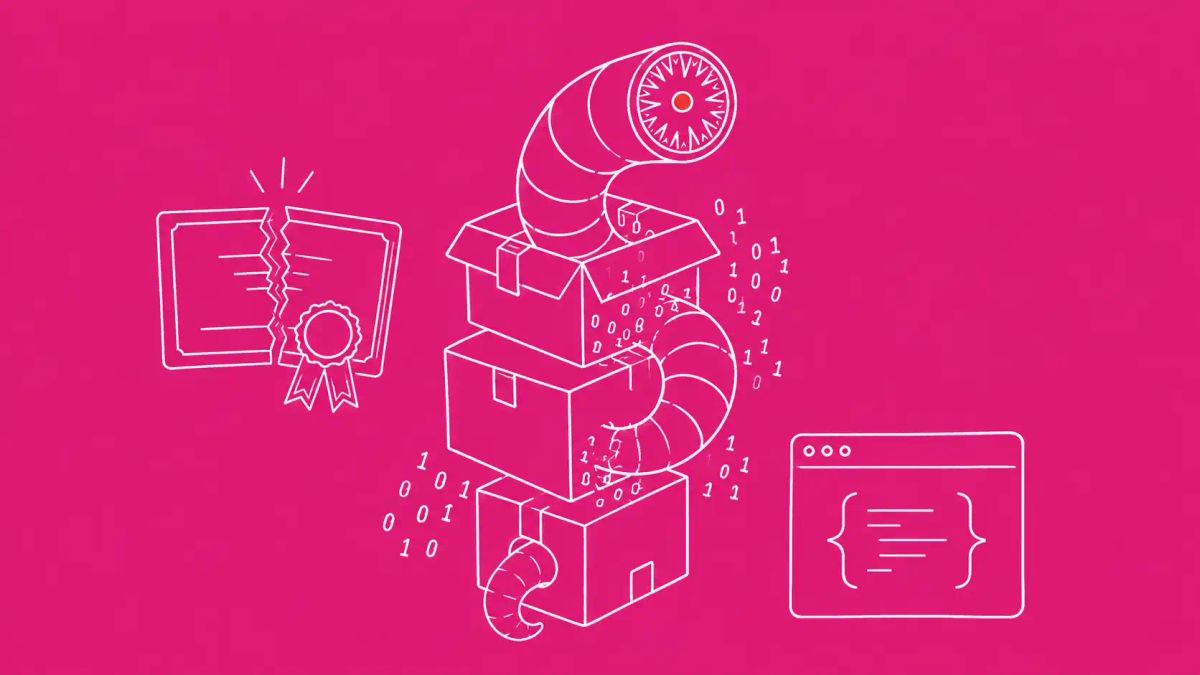
The category-shaping detail sits one layer below the package count. For the first time publicly documented, the malicious packages were published with valid SLSA Build Level 3 provenance attestations, generated through hijacked GitHub Actions OIDC tokens interacting with the legitimate Sigstore stack — Fulcio certificate authority, Rekor transparency log, in-toto statements. The provenance signature that defenders rely on as a final trust signal is no longer sufficient to guarantee a package is safe. This is the fourth TeamPCP campaign in six months, following the group's third Checkmarx compromise in three months, and represents a meaningful escalation from previous waves.
The SLSA attestation breakthrough
StepSecurity researcher Ashish Kurmi describes the attack chain in three steps. First, the attacker exploited a pull_request_target trigger in the TanStack release pipeline to gain read access to the GitHub Actions runner. Second, the attacker poisoned the GitHub Actions cache to inject malicious payload code into the build environment. Third, the attacker extracted the OIDC token directly from the runner process memory at runtime — a token Sigstore's Fulcio CA accepts as proof the build came from a trusted GitHub Actions workflow.
With that token, the attacker could request signing certificates from Fulcio, write entries to Rekor, and generate in-toto statements that any consumer verifying provenance with cosign or sigstore-go would accept as legitimate. The package npm displayed alongside its SLSA Build Level 3 badge was, in every cryptographic respect, a legitimately attested artifact. The substance of what it built was malicious. As Helixar's analysis puts it: "Provenance can tell you where the package was built. It does not prove the build was safe."
Four delivery mechanisms across four ecosystems
The campaign tailored its delivery technique to each compromised namespace. TanStack packages shipped a 2.3 MB single-line obfuscated JavaScript file (router_init.js) plus an optional GitHub-hosted dependency that executed a Bun-runtime payload through a prepare lifecycle hook. UiPath packages used a preinstall script (node setup.mjs) to download Bun and execute the payload. Mistral AI's npm package had its package.json rewritten to invoke setup.mjs through a preinstall hook. The Guardrails AI PyPI package took the most direct approach: 13 lines of new code in mistralai/client/__init__.py, executed on import, downloading a Python artifact from git-tanstack[.]com to /tmp/transformers.pyz and running it under python3 without integrity verification.
Microsoft Threat Intelligence is independently investigating the @mistralai/mistralai PyPI v2.4.6 compromise, which downloads a remote payload from 83.142.209[.]194 to the same /tmp/transformers.pyz path. The compromise includes country-aware logic: the malware avoids executing in Russian-language environments and includes a one-in-six chance of triggering a destructive rm -rf / branch on systems in Israel or Iran. Both the geofencing and the bias-toward-destruction in specific countries are operational signatures that suggest the operator's risk tolerance differs by jurisdiction.
The 60-second poll and the rm -rf failsafe
Each victim machine receives a persistent daemon installation: a LaunchAgent on macOS, a systemd unit on Linux. The daemon polls GitHub every 60 seconds to check whether the stolen tokens it was set up against are still valid. If the daemon detects token revocation, it triggers a destructive routine that attempts rm -rf ~/ — recursive deletion of the user's home directory. The operational implication for incident response is sharp: do not revoke tokens before isolating and imaging the affected machine, or the malware will respond by destroying the developer's local environment. This is the first time a self-propagating npm worm has shipped with active anti-remediation logic at this level.
The credential targeting is also new in this wave. Beyond the standard CI/CD tokens, cloud credentials (AWS IMDSv2, GCP, Azure), Kubernetes service accounts, HashiCorp Vault, and package registry tokens, Mini Shai-Hulud now actively harvests 1Password and Bitwarden vaults plus cryptocurrency wallets. The combination tracks the broader 2026 pattern where developer endpoints are the highest-value credential targets, as documented in the Quasar Linux RAT (QLNX) developer-credential profile from earlier this month.
TeamPCP's accelerating campaign tempo
Mini Shai-Hulud is the fourth public TeamPCP supply chain campaign in six months. Prior waves include the March 2026 Trivy supply chain compromise, the April 2026 SAP npm "Mini Shai-Hulud" wave, three Checkmarx compromises (GitHub Actions in March, KICS Docker Hub and VS Code extensions in April, Jenkins AST Plugin in May), the Bitwarden CLI npm package, and the Intercom Node.js SDK at 361,510 weekly downloads. The pattern is industrial-scale: each wave builds on the previous wave's technical sophistication, and the campaign tempo is accelerating, not decelerating.
Socket detected and flagged the compromised artifacts within six minutes of publication. StepSecurity's AI Package Analyst also surfaced detections in the same window. Both detections beat the typical incident response time for supply chain compromises by an order of magnitude — but the SLSA-attested versions had already begun propagating to dependency caches before takedown began. The broader cloud-credential theft pattern PCPJack established earlier this month applies here too: detection speed is no longer sufficient when the harvest happens at package-install time.
The CyberSignal Analysis
Signal 01 — SLSA provenance is no longer a sufficient trust signal on its own
For five years, the supply chain security community has been pushing SLSA, Sigstore, and signed provenance as the answer to package trust. Mini Shai-Hulud demonstrates that the answer is incomplete. Valid provenance proves where a package was built, by which workflow, and with what inputs — but it does not prove the workflow itself was uncompromised at build time. When the OIDC token used to request signing certificates is stolen from a poisoned GitHub Actions runner, every downstream signature is structurally valid and substantively malicious. Defender posture has to incorporate post-installation behavior monitoring, lifecycle script auditing, and runtime detection. Add npm config set ignore-scripts true to your CI/CD baseline this week, and treat SLSA provenance as one input to a layered trust architecture rather than a sufficient final check.
Signal 02 — Token revocation is now an incident response trap, not the first step
The 60-second polling daemon and rm -rf failsafe invert standard IR workflow. The first instinct after detecting credential theft is to revoke the stolen credentials immediately. Mini Shai-Hulud weaponizes that instinct: revocation triggers home-directory destruction. The correct sequence is now to isolate the affected machine first, image it second, identify the daemon and disable it third, and only then proceed with credential rotation. Update your IR runbook explicitly. Document the new sequence with your SOC, your engineering teams, and your password-manager incident workflows. The next campaign that adopts this pattern will not announce itself; the runbook update has to happen before it lands.
What to do this week
- Audit your dependency tree for compromised package versions published between May 11, 2026 19:20 UTC and the takedown window. Pin to known-clean alternatives: the confirmed clean TanStack families are @tanstack/query*, @tanstack/table*, @tanstack/form*, @tanstack/virtual*, and @tanstack/store. For other compromised namespaces, revert to versions published before 19:20 UTC May 11.
- Rotate all environment secrets accessible to installations from May 11 onward. Treat CI/CD tokens, cloud credentials, password vault exports, and cryptocurrency wallets as potentially compromised. Critical: isolate and image developer machines first, before revoking tokens, to avoid triggering the rm -rf failsafe.
- Search GitHub organizations for unauthorized repositories with description "A Mini Shai-Hulud has Appeared" — these are the dead-drop exfiltration channels. Block DNS to git-tanstack[.]com, *.getsession.org, and the IP 83.142.209[.]194 across all egress.
- Hunt for the persistence daemon on developer workstations: macOS LaunchAgent or Linux systemd units polling GitHub at 60-second intervals. Look for processes that read your password manager vault files or wallet directories. Audit your 1Password and Bitwarden activity logs for unexpected export events.
- Add npm config set ignore-scripts true to CI/CD configuration. Pin optional dependencies with exact SHAs in lockfiles. Brief developers on the OIDC token theft pattern and the pull_request_target risk. Update your SLSA verification framework to treat provenance as necessary but not sufficient.