ICE Agents Now Carry a 20 Million-Person Palantir List on Their iPhones
ICE Assistant Director Matthew Elliston disclosed at the Border Security Expo that agents now reach a 20-million-person list from their iPhones via Palantir's ELITE system. The Mobile Fortify accuracy claim is in tension with 404 Media's January reporting.
The operational scale of Palantir's ELITE deployment just got disclosed publicly at the Border Security Expo, and it represents the documented mobile-field rollout of mass-scale federal surveillance technology that vendor-risk and civil-liberties programs now have to plan around.
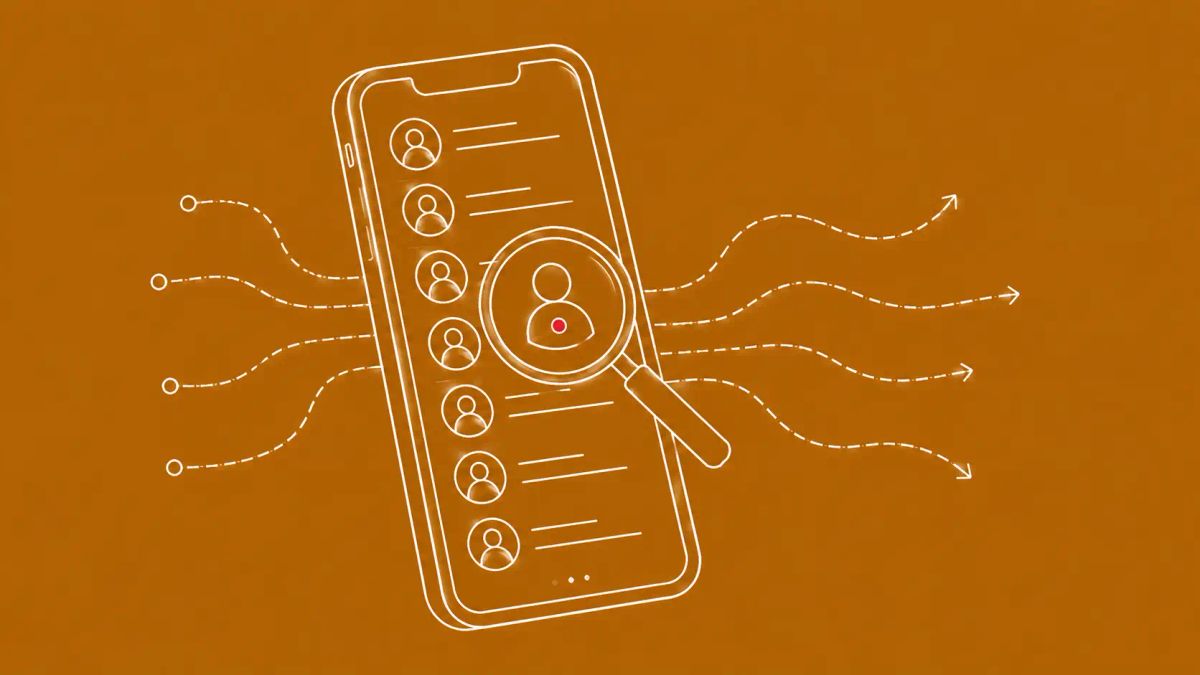
PHOENIX, AZ — Matthew Elliston, Assistant Director of Law Enforcement Systems and Analysis at US Immigration and Customs Enforcement, told attendees at the Border Security Expo the week of May 5, 2026 that ICE agents can now reach a list of approximately 20 million people directly from their iPhones in the field, via Palantir's ELITE system. The remarks were reported by 404 Media's Joseph Cox on May 11. Palantir's own description of ELITE, posted to a company blog, frames the system as a tool "used for prioritized enforcement to surface the likely addresses of specific individuals, such as those with final orders of removal or with high severity criminal charges."
For CISOs, privacy officers, and vendor-risk teams, the news has implications beyond the immigration policy frame. A 20-million-record list reachable from a federal agent's mobile device is the documented operational state of mass-scale government surveillance technology, and it is now a baseline that vendor-management, employee-protection, and government-affairs programs need to plan around. The disclosure also lands alongside other 2026 federal technology developments worth tracking together, including the FCC's foreign router ban extension and the California GM OnStar data minimization settlement, which together sketch the federal-versus-state-versus-vendor surveillance technology landscape entering the second half of 2026.
What Elliston disclosed at the Expo
404 Media spoke to four attendees of the Border Security Expo, a two-day Phoenix conference where vendors pitched technology to ICE and other Department of Homeland Security agencies. Elliston's statements as reported include the 20-million-record iPhone scale figure, a claim that the Mobile Fortify facial-recognition app has been used roughly 200,000 times with a 0 percent mismatch rate, and an open invitation to vendors interested in selling to ICE to message him on LinkedIn. 404 Media noted that Elliston's accuracy claim is in tension with the publication's own January 2026 reporting, which documented that Mobile Fortify had misidentified a woman twice. Reporter Joseph Cox framed the gap directly: "The officials' comments may need to be taken with a pinch of salt, but still reflect ICE's position that Palantir is allowing the agency to identify people to arrest and locations to raid faster."
Palantir did not respond to 404 Media's request for comment. The company's own public blog post on ELITE characterizes the system as supporting "prioritized enforcement to surface the likely addresses of specific individuals, such as those with final orders of removal or with high severity criminal charges." That framing presents a narrower target population than the 20-million-record list Elliston referenced. The DHS statement to 404 Media took a similar narrowing posture: "Like other law enforcement agencies, ICE employs various forms of technology while respecting civil liberties and privacy interests." April 2026 data shows that 70.8 percent of the 42,722 people in ICE detention had no criminal conviction, a data point Cox cited in his reporting as relevant context.
Why operational scale and mobile deployment matter for defenders
The two operational details that matter most for defender programs are scale and mobility. A 20-million-record list is larger than the population of New York State; the underlying data architecture has to be a composite of multiple federal databases queried through Palantir's data integration platform, with cached subsets pushed to agent-issued iPhones. That deployment pattern, mass-scale composite database queried from a mobile field interface, is the operational signature of contemporary government surveillance technology, and it is increasingly the architecture vendors are pitching at events like the Border Security Expo. Elliston's open invitation to vendors at the Expo confirms the procurement pipeline is active.
For CISOs and chief privacy officers, three implications matter. First, the workforce protection question. Organizations with significant immigrant or refugee employee populations should understand that a 20-million-record list reachable in the field affects employees personally. HR and legal teams should be briefed. Second, the vendor risk question. Palantir products, including Gotham, Foundry, and AIP, are widely used in enterprise contexts beyond government deployment. Update your vendor risk register to reflect Palantir's broader operational context, regardless of which Palantir products your organization uses. Third, the data-sharing question. Organizations that participate in identity verification, immigration-status checks, or similar federal-data-flow programs should audit whether their internal data is structurally usable as input to systems like ELITE, and document that posture for legal and compliance teams. The broader policy and government technology environment is moving toward more federal data integration, not less.
What is not confirmed in the public record
Several specific claims warrant the caveat 404 Media itself attached. Elliston's 0 percent Mobile Fortify mismatch rate is contradicted by 404 Media's January 2026 reporting on misidentified individuals; treat as marketing language until independently verified. The 20 million figure is not paired with publicly disclosed source databases, so the composite architecture is inference rather than confirmation. Palantir's ELITE blog framing references final orders of removal and high-severity criminal charges as the target population; ICE's broader detention data shows 70.8 percent of detainees have no criminal conviction. The gap between Palantir's stated criteria and the operational detention population is the civil-liberties concern multiple oversight observers have flagged. Congressional and inspector-general scrutiny of these systems, accuracy audits, and the specific contractual terms between Palantir and ICE are areas where the public record is currently thin.
The CyberSignal Analysis
Signal 01 — Mobile-field surveillance technology is now the documented baseline, not a future scenario
For most of the last decade, mass-scale federal surveillance technology has been discussed in defender circles as a hypothetical or as a feature of specific high-profile programs. The Elliston disclosure makes the mobile deployment of a 20-million-record list the documented operational state at one federal agency, and the Border Security Expo procurement pipeline indicates other agencies are following similar paths. Update your threat models, employee-protection programs, and vendor risk frameworks accordingly. The defender posture that treats government surveillance technology as a hypothetical is no longer accurate.
Signal 02 — Vendor accountability frameworks need to incorporate operational deployment context
Palantir is one example of a category of technology vendors whose operational deployment to government customers is increasingly visible and increasingly consequential. Vendor risk assessments need to reflect not just the vendor's information security posture but the vendor's deployment context, customer base, and operational reputation. CISOs should brief boards on the broader vendor-accountability framework: which vendors does the organization rely on, what are those vendors known to be doing operationally, and what is the reputational and legal-compliance exposure if a vendor's broader work draws regulatory or public scrutiny. The Elliston disclosure is a useful conversation starter for that briefing.
What to do this week
- Update your vendor risk register to include operational deployment context for Palantir products (Gotham, Foundry, AIP) and for any other surveillance-technology-adjacent vendors. Document what each vendor is known to be doing operationally, beyond their direct relationship with your organization.
- Brief HR and legal teams on the workforce-protection implications. Organizations with significant immigrant or refugee employee populations face employee-experience questions that the 20-million-record list disclosure makes more concrete. Pre-script the employee-communication framework.
- Audit your organization's federal data-sharing posture. If you participate in identity verification, immigration-status checks, or similar federal-data-flow programs, document which internal data could structurally serve as input to systems like ELITE, and confirm that posture with legal and compliance.
- Brief boards on the federal-technology-environment evolution. The combination of mass-scale mobile surveillance deployment, state-level consumer privacy enforcement (the GM CCPA precedent), and national-security equipment restrictions (the FCC waiver) is a coherent 2026 landscape. Update your strategic risk briefing accordingly.
- Engage with industry associations and policy coalitions tracking vendor accountability for surveillance technology. The 404 Media disclosure is one data point in a longer-term trend; coalition-level engagement is more durable than incident-driven response.