Identity Under Fire: ANTS Portal Breach Exposes Millions to Phishing and Identity Theft
The French National Agency for Secure Documents (ANTS) has confirmed a significant security incident targeting its central portal, as threat actors move to monetize a database allegedly containing millions of sensitive user records.
PARIS, FRA — The French government is grappling with a severe compromise of its digital identity infrastructure. The Agence Nationale des Titres Sécurisés (ANTS) — the body responsible for issuing passports, driver’s licenses, and residency permits — officially confirmed a breach of its ants.gouv.fr portal on Tuesday. The disclosure follows claims by a prominent threat actor on a dark web forum to be selling a database containing the personal information of nearly 19 million French citizens.
According to reporting from BleepingComputer and The Record, the agency detected the intrusion after anomalous activity was identified within its user-management systems. While the agency initially downplayed the scope, the scale of the data offered for sale suggests a systematic exfiltration of user metadata.
Data Exposure Profile: ANTS 2026
The Anatomy of the Leak: What was Compromised?
The ANTS portal serves as a critical "walled garden" for French administrative life. The breach does not appear to have compromised the core biometric production systems, but rather the web-facing layer where citizens manage their applications.
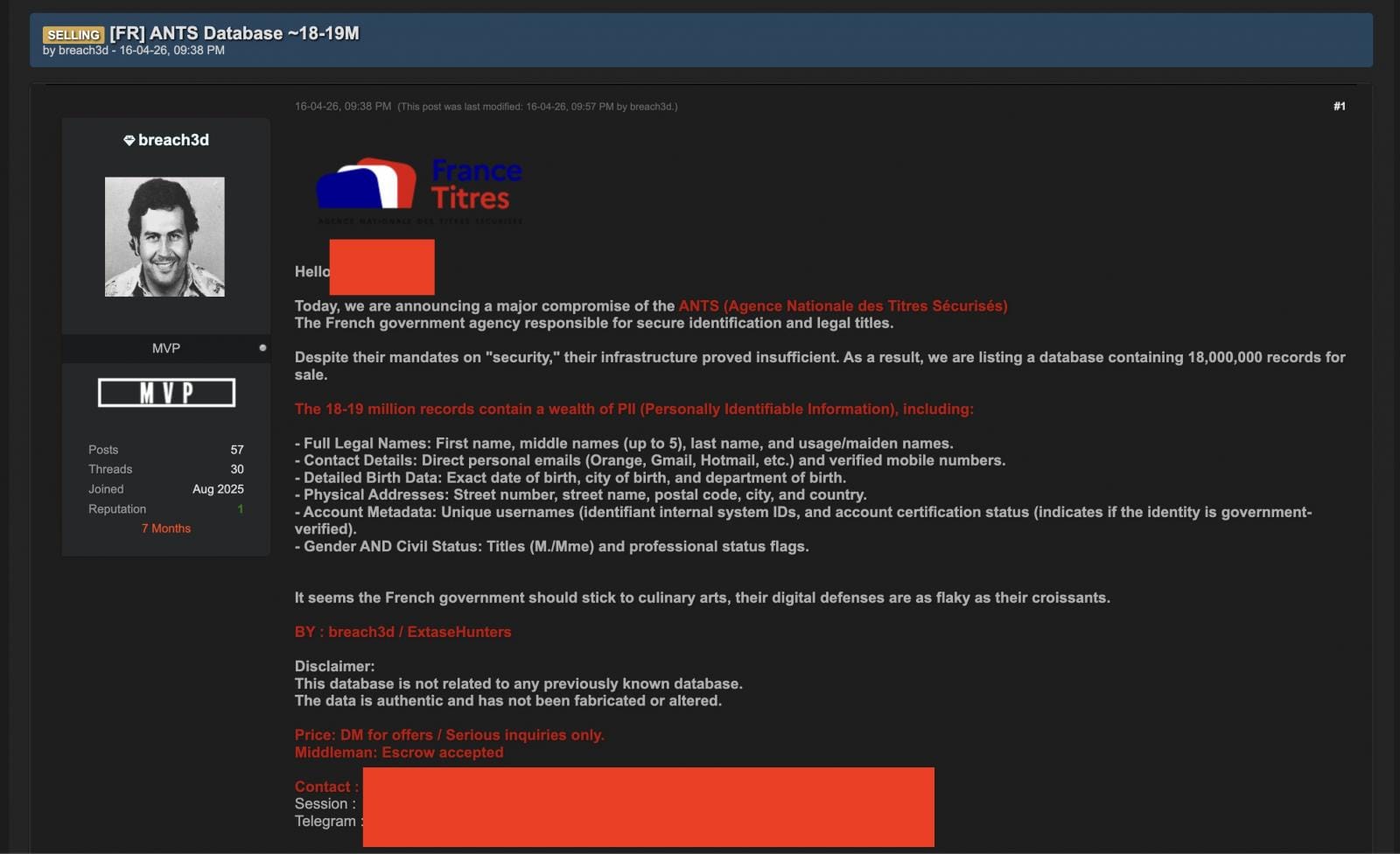
Based on analysis from CyberNews and Security Affairs, the data currently circulating in criminal markets includes:
- Personal Identifiers: Full names, dates of birth, and places of birth.
- Contact Metadata: Email addresses, physical addresses, and phone numbers.
- Administrative Details: Partial information regarding pending or historical document applications.
Le Figaro reports that the breach may be the result of a coordinated effort between disaffected local threat actors and established international cybercriminal networks, specifically targeting high-traffic government portals to fuel secondary phishing campaigns.
The Vishing Connection
The primary risk for French citizens is not just the loss of data, but the weaponization of that data for vishing. With accurate physical addresses and document types in hand, scammers can launch highly personalized "support" scams that mirror the apple notification fatigue attacks recently seen in the private sector.
The CyberSignal Analysis
Signal 01 — The "Governance Gap" in Digital ID
This incident is a definitive signal for identity & access management (IAM). As governments centralize identity services, they create single points of failure. The ANTS breach proves that the security of a citizen's identity is only as strong as the web portal managing it. For B2B leaders, the signal is that "Single Sign-On" (SSO) systems are now the highest-priority targets for threat actors seeking high-fidelity data sets.
Signal 02 — The Weaponization of Administrative Trust
This is a high-fidelity signal for third-party risk. For millions of citizens, the French government is their primary third-party vendor. When that vendor fails, the resulting "signal" is a surge in downstream phishing. Much like the fakewallet infiltration of the apple app store, this breach weaponizes the victim's trust in an official institution to lower their guard for future social engineering.
Signal 03 — Data as a Precursor to Kinetic Crime
This represents a significant signal for threat intelligence. By harvesting physical addresses and identity details, threat actors are moving closer to bridging the gap between digital theft and physical fraud. As we move toward a world of agentic AI development, the ability for attackers to automate the cross-referencing of this leaked data with other breaches (like the recent NGate activity) means that the "time to exploit" for a leak of this size has dropped from months to minutes.




