Global Cyber Defenders Converge for Locked Shields 2026

NATO CCDCOE launches the world's largest live-fire cyber defense exercise, bringing together 4,000 experts to protect fictional Berylia against 8,000 real-time threats.
TALLINN, EE — More than 4,000 cyber defenders from 41 nations have concluded Locked Shields 2026, the world’s largest and most complex international live-fire cyber defense exercise. Organized by the NATO Cooperative Cyber Defence Centre of Excellence (CCDCOE), the annual event simulates a large-scale cyber conflict, testing the ability of multinational teams to protect critical national infrastructure under sustained, high-velocity attack.
Unlike traditional tabletop drills, Locked Shields is a "live-fire" simulation. This means that 16 multinational Blue Teams must defend real equipment and actual network configurations against an aggressive Red Team. The 2026 iteration involved approximately 8,000 real-time attacks, forcing defenders to manage technical crises while navigating complex legal, strategic, and media landscapes.
Breach Audit: Protecting a Fictional Nation’s Core
The exercise centers on the fictional nation of "Berylia," which is targeted by a sophisticated adversary aiming to destabilize its sovereign functions. To ensure the highest levels of realism, the CCDCOE collaborates with industry giants to integrate authentic hardware and industrial control systems (ICS).
Real Equipment, Real Consequences: The SANS Contribution
A standout feature of the 2026 exercise is the contribution from the SANS Institute. Rather than a software simulation, SANS designed and built a fully operational Power Generation System (PGS) featuring nearly 70 physical industrial control assets, including Programmable Logic Controllers (PLCs) and Human-Machine Interfaces (HMIs).
Defenders must maintain a steady supply of power to the fictional population of Berylia while the system is actively under fire. Every defensive error results in physical outcomes—turbines throttling, breakers opening, and generation capacity dropping in real-time. This "OT-under-fire" scenario highlights the persistent threat posed by nation-state actors targeting the physical foundations of modern society.
OPSEC Alert: The HNLMS Evertsen "Postcard Incident"
While Locked Shields 2026 focuses on high-end digital defense, a recent real-world incident involving the Dutch air-defense frigate HNLMS Evertsen serves as a stark reminder of "low-tech" vulnerabilities.
In April 2026, a journalist successfully tracked the $585 million NATO warship for 24 hours by simply mailing a postcard containing a $5 Bluetooth tracker to the crew. Because the Dutch Ministry of Defense guidelines at the time exempted postcards from X-ray screening, the device was brought aboard undetected. It then "leeched" off the signals of crew members' smartphones to broadcast the ship’s real-time coordinates as it sailed from Crete toward Cyprus.
This breach, which occurred while the Evertsen was escorting the French aircraft carrier Charles de Gaulle, highlights why exercises like Locked Shields must account for the intersection of physical mail and consumer tracking ecosystems.
The CyberSignal Analysis
Signal 01 — Beyond the Technical Silo
Locked Shields 2026 reinforces that cyber resilience is not just a technical problem. By embedding legal advisors and media strategists into the Blue Teams, NATO emphasizes that a national-level crisis requires a "whole-of-government" response. Technical success is moot if a nation loses the information war or violates international law during its defense.
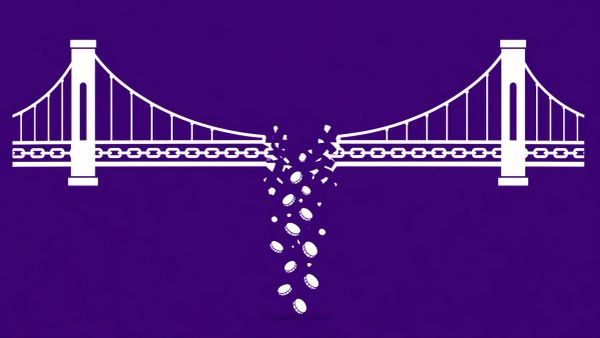
Signal 02 — The Public-Private Defense Model
The integration of industry partners like SANS, Siemens, and ReversingLabs proves that critical infrastructure protection cannot be achieved by the military alone. Because most critical assets are privately owned, these exercises are vital for developing standard operating procedures that allow government defenders to work seamlessly with private sector operators during a real-world breach.