ADT Data Breach: ShinyHunters Steals Millions from Security Giant

America's largest home security provider confirms breach after vishing attackers claim 10M customer records. Okta SSO → Salesforce attack chain exposes PII and partial SSNs.
BOCA RATON, FL — In a stinging blow to the world’s most recognized name in physical security, ADT Inc. (NASDAQ: ADT) has confirmed a significant data breach affecting its customer database. The incident, linked to the notorious ShinyHunters threat group, highlights a growing trend: even $5 billion security leaders are falling victim to low-tech vishing attacks that bypass multi-million dollar perimeters.
While ShinyHunters claims to have exfiltrated 10 million records, ADT’s official statement describes the exposure as a "limited subset" of data. Regardless of the final tally, the breach has triggered a brand trust crisis for a company whose entire value proposition is based on protection.
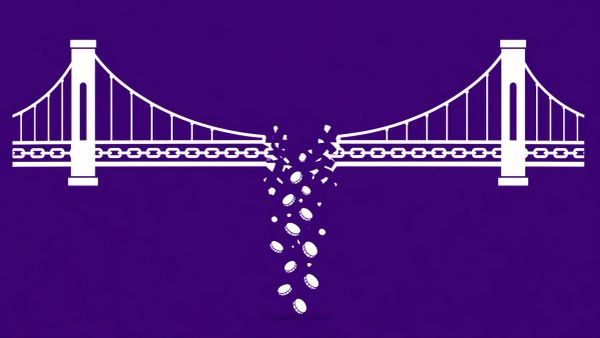
The Attack Chain: From Vishing to Salesforce
The breach was not the result of a zero-day exploit or a complex malware payload. Instead, it followed a disciplined social engineering path that has become a ShinyHunters hallmark.
- The Vishing Hook: English-speaking attackers placed calls to ADT employees, impersonating internal IT support to harvest login credentials.
- SSO Compromise: These credentials granted the attackers access to ADT’s Okta-protected Single Sign-On (SSO) environment.
- Database Exfiltration: Once inside, the group pivoted to the company’s Salesforce instance, where customer and prospect databases were stored.
- Extortion: On April 23, the group listed the data on BreachForums, threatening a full leak by April 27 if an undisclosed ransom is not paid.
ADT Confirmed Exposure: What Was Lost?
ADT detected the unauthorized access on April 20 and moved to terminate the intrusion. However, the forensic audit revealed that significant Personal Identifiable Information (PII) was moved off-site.
- Standard Data: Names, phone numbers, and physical addresses.
- High-Risk Data: In limited cases, dates of birth and the last four digits of Social Security Numbers (SSN) or Tax IDs.
- Safety Check: ADT emphasizes that no payment information (credit cards/bank accounts) was stolen, and crucially, no home security systems were compromised.
ShinyHunters: A History of Scale
ShinyHunters, a threat group with historical ties to the former IndianAPT41, has pivoted away from traditional ransomware in favor of pure, high-volume data extortion. By prioritizing supply chain vulnerabilities and SSO targets, they maximize their leverage while minimizing the technical friction of encrypting local networks.
While their resume includes historic strikes on AT&T (37M) and Ticketmaster (560M), recent investigations by The CyberSignal reveal a group operating at an industrialized scale:
- The Rockstar Games Leak: Following a refusal to pay a ransom, ShinyHunters leaked 78 million records exfiltrated via stolen analytics tokens.
- The "Pay or Leak" Triple Ultimatum: Earlier this month, the group issued simultaneous threats to Zara, Carnival, and 7-Eleven, allegedly exfiltrating 9 million records through a shared third-party service provider.
- The European Commission Breach: A significant escalation in target profile, where the group successfully compromised cloud infrastructure to access sensitive administrative data.
This ADT incident confirms a terrifyingly consistent pattern: ShinyHunters is systematically exploiting the "identity layer"—using vishing and stolen tokens to bypass the very security perimeters they were designed to protect.
The CyberSignal Analysis: Strategic Signals
Signal 01 — The Vendor Paradox
This is ADT’s third major security incident in under two years, following breaches in August and October 2024. For a company that monitors over 6 million homes, the inability to secure its own internal employee portals creates a massive brand disconnect. The irony that the world's largest security provider cannot secure itself is not lost on the market.
Signal 02 — Vishing is the New Zero-Day
Perimeter defenses are failing because the human element remains the weakest link. By using native English speakers and sophisticated scripts, ShinyHunters has turned vishing into a high-yield enterprise entry tool that renders traditional MFA less effective.
Signal 03 — Targeted Physical Risk
Unlike a retail breach, an ADT breach carries physical security implications. Stolen names and addresses linked to a "security giant" essentially provide a high-value "hit list" for physical burglars, identifying homes that likely contain valuable assets worthy of an ADT system.