ShinyHunters Hits Udemy: 1.4M Records After ADT Breach

Same group behind ADT 10M breach claims 1.4M Udemy users via SaaS vishing. Education sector PII and corporate data at risk. April 27 leak deadline looms.
SAN FRANCISCO, CA — Less than a week after the ADT data breach exposed 10 million records, the notorious threat collective ShinyHunters has claimed another high-profile victim: global EdTech giant Udemy.
On April 24, the group posted a "Pay or Leak" ultimatum on BreachForums, claiming to have exfiltrated 1.4 million user records along with sensitive corporate data. The group has set a deadline of April 27, 2026, threatening to release the full dataset if a ransom is not met. While Udemy has not yet officially confirmed the breach, the group's recent successful strikes on the retail and security sectors suggest a highly credible threat.
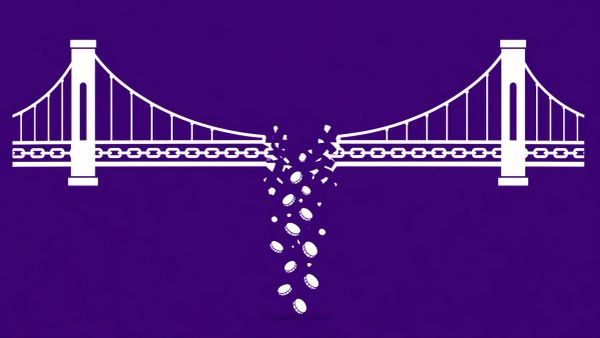
The Pattern: SaaS Vishing and MFA Bypass
The Udemy incident appears to be a direct expansion of the ShinyHunters 2026 campaign, utilizing the same identity-centric supply chain attack vector documented in our ADT coverage.
- Vishing Reconnaissance: Attackers utilize English-speaking social engineering to target employees via phone, impersonating IT support.
- SSO Pivot: By harvesting credentials or session tokens, the group bypasses MFA to enter the enterprise Single Sign-On (SSO) environment (suspected Okta/Auth0).
- SaaS Exfiltration: The group pivots to critical SaaS platforms — in this case, suspected Salesforce or Zoho CRM instances — to pull massive user datasets.
- Extortion-Only Model: Consistent with their ransomware pivot, no files are encrypted; the "product" is the data itself.
Claimed Exposure: Education PII as a High-Value Asset
The 1.4 million records claimed represent approximately 2% of Udemy’s 70 million global users, suggesting the group may have exfiltrated a specific regional or corporate training database.
The Education Sector "Resale" Pipeline
This is not ShinyHunters' first strike on education. In 2025, they targeted the Indian platform Unacademy, stealing 10 million records. In the EdTech sector, data has a unique resale value: course completion data is often used to generate fake professional certifications, which then flood LinkedIn and job boards, undermining the integrity of professional credentials.
The ShinyHunters 2026 Campaign Tracker
The strike on Udemy is the latest in a relentless Q2 blitz that has seen ShinyHunters compromise over 100 million records in less than 30 days. The CyberSignal continues to track this group, identified by Google Mandiant as the UNC6240 cluster, notorious for their industrialized vishing playbooks and "identity-first" pivot tactics.
By moving from high-value physical security (ADT) to global education (Udemy), the group is demonstrating an ability to scale social engineering across diverse industry verticals with near-simultaneous execution.
Udemy Response: The Silence Strategy
As of publication, Udemy has not issued a formal press release. However, their internal security and account troubleshooting pages have seen increased activity, suggesting a proactive defense against credential stuffing.
For corporate training customers, the risk is higher. The inclusion of "internal configurations" in the ShinyHunters claim could provide a roadmap for future intrusions into the corporate networks of Udemy’s enterprise clients.
The CyberSignal Analysis: Strategic Signals
Signal 01 — The "Education-to-Enterprise" Pivot
ShinyHunters is no longer just chasing bulk PII; they are targeting the SaaS relationship. By hitting Udemy, they gain access to the learning histories of thousands of corporate employees. This data is a goldmine for secondary vishing campaigns, where attackers can call an employee and cite their specific "completed courses" to build immediate, irrefutable rapport.
Signal 02 — Credential Integrity Collapse
The exfiltration of course certificates represents a direct attack on professional trust. In the supply chain of human talent, verified learning is a currency. If ShinyHunters floods the dark web with 1.4 million valid certificate templates and completion IDs, the resale value for "fake-but-verified" credentials creates a long-term fraud tail for the EdTech industry.
Signal 03 — The Q2 Identity Blitz
The speed of these strikes — moving from ADT to Udemy in days — suggests the group has industrialized their vishing "playbook." They aren't looking for technical vulnerabilities in the code; they are exploiting the "identity layer." For CISOs, this confirms that even the best perimeter security is irrelevant if an employee can be talked into bypassing their own MFA.