Defending the Defender: Three Microsoft Zero-Days Leaked and Exploited in the Wild
A disgruntled security researcher has publicly released proof-of-concept code for three critical vulnerabilities in Microsoft Defender, leaving over a billion users exposed as two flaws remain unpatched.
REDMOND, WA — The global cybersecurity community is on high alert following the unauthorized leak and subsequent exploitation of three zero-day vulnerabilities within Microsoft Defender, the default antivirus solution for the Windows ecosystem. The leaks, attributed to a researcher operating under the handle "RedSun," have triggered a wave of active attacks as threat actors race to weaponize the flaws before Microsoft can issue comprehensive patches.
While Microsoft has managed to address one of the vulnerabilities in a rapid out-of-band update, two remain "Zero-Day" status, meaning no official fix is currently available to the public.
Defender Zero-Day Status Tracker
The "RedSun" Trilogy: RedSun, BlueHammer, and UnDefend
The vulnerabilities — colloquially named RedSun, BlueHammer, and UnDefend by the research community — target the core engine of Microsoft Defender. Rather than bypassing the antivirus, these exploits essentially "turn the defender against itself."
According to technical breakdowns from BleepingComputer and The Hacker News:
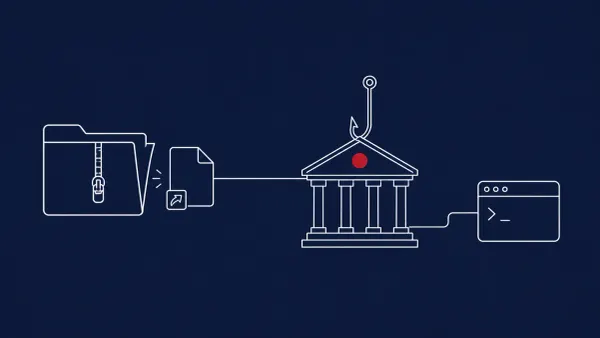
- RedSun (Privilege Escalation): This flaw allows an attacker with limited access to a machine to escalate their permissions to SYSTEM level — the highest possible privilege in Windows. By tricking the Defender service into "restoring" a malicious file from quarantine into a protected system folder, the attacker can execute code with full administrative rights.
- BlueHammer (Remote Code Execution): Currently the most dangerous of the three, BlueHammer targets the network inspection driver. Analysts report it can be triggered remotely, potentially allowing for "zero-click" infection if a user simply visits a compromised website.
- UnDefend (Persistence): This exploit focuses on disabling Defender’s "Tamper Protection" without triggering an alert, allowing malware to remain undetected indefinitely.
This localized chaos is compounding a historically difficult month for Windows administrators. These leaks arrive alongside our recent coverage of CVE-2026-32201, a critical SharePoint spoofing zero-day that CISA recently added to its Known Exploited Vulnerabilities (KEV) catalog.
A Breakdown in Disclosure
The leak appears to be the result of a fractured relationship between the researcher and Microsoft’s Bug Bounty program. Reports from TechRadar and CSO Online suggest the researcher felt "childish games" were being played regarding the severity and payout for the bugs. In retaliation, the researcher bypassed the standard Responsible Disclosure window and posted the Proof-of-Concept (PoC) code directly to GitHub.
"They mopped the floor with me... and they did ruin my life," the researcher reportedly claimed in a post accompanying the leak. This "scorched earth" approach has drawn criticism from the security industry, as it provides a ready-made toolkit for ransomware groups.
The CyberSignal Analysis
Signal 01 — The "Trust Gap" in Bug Bounties
This incident is a massive "Signal" that the industry's reliance on private Bug Bounty programs is fragile. When researchers feel marginalized, the risk shifts from "coordinated patching" to "public chaos." For B2B firms, the takeaway is that your security stack — even if it's from a vendor like Microsoft — can become your primary attack vector overnight due to human conflict. This is evidenced by the "Old vs. New" strategy we analyzed in our report on Legacy Excel Flaws (CVE-2009-0238), where threat actors are pairing 17-year-old bugs with brand-new zero-days to bypass modern defenses.
Signal 02 — Prioritize EDR "Tamper Protection" Monitoring
With UnDefend targeting the ability to turn off antivirus silently, the "Signal" for IT leaders is to move beyond "Prevention" and toward vulnerability management and active monitoring. If your security software stops reporting data, it shouldn't be treated as a "glitch" — it should be treated as a high-severity indicator of compromise (IoC). This is especially critical given the broader wave of RCE flaws in Office products we’ve tracked this month, which allow for "zero-click" infections via simple file previews.