CISA Adds Critical Apache ActiveMQ RCE Flaw to KEV Catalog Following Active Exploitation
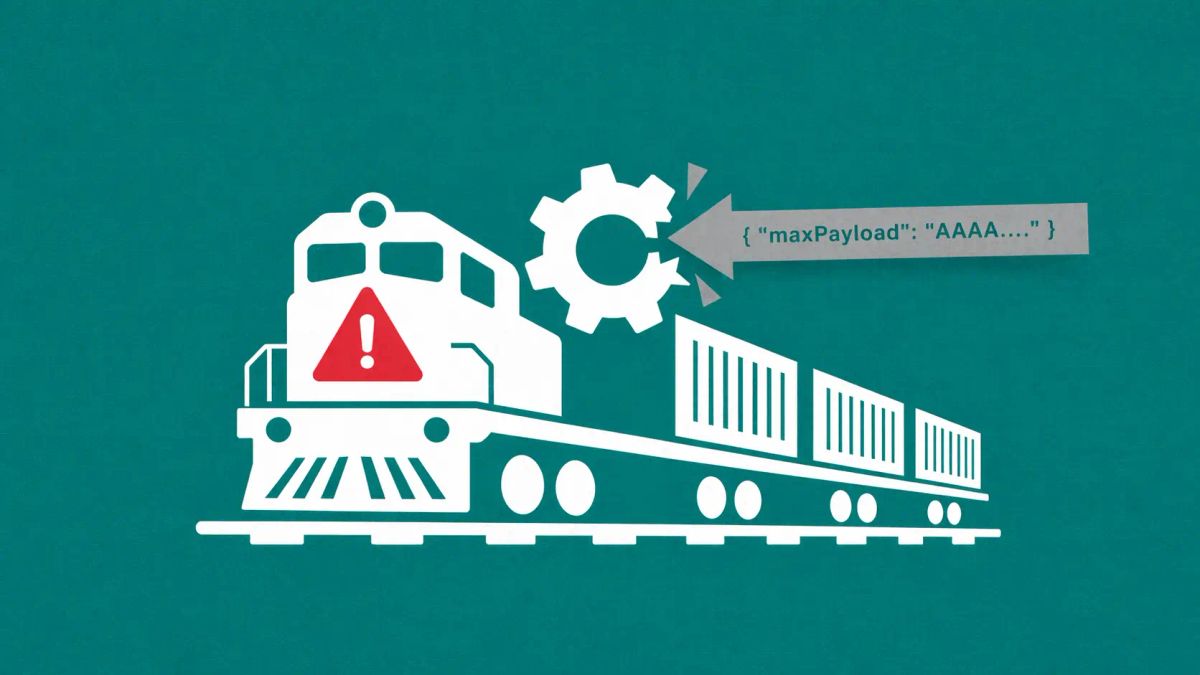
The "Jolokia" vulnerability allows for unauthenticated Remote Code Execution, posing a significant risk to the message-brokering infrastructure that underpins global finance and logistics.
WASHINGTON, D.C. — The Cybersecurity and Infrastructure Security Agency (CISA) has officially added a critical input validation vulnerability in Apache ActiveMQ to its Known Exploited Vulnerabilities (KEV) catalog. The flaw, tracked as CVE-2026-34197, allows attackers to execute arbitrary code remotely by exploiting the Jolokia JMX-over-HTTP bridge integrated into the platform.
The move by CISA signals that this is no longer a theoretical risk; threat actors are actively leveraging the vulnerability to gain initial access to enterprise networks, potentially disrupting the real-time data flows that move everything from stock market trades to supply chain manifests.
ActiveMQ Vulnerability Profile
The Mechanism of Attack: The Jolokia Bridge
Apache ActiveMQ is a widely used open-source message broker. The vulnerability resides in how the broker handles input through its Jolokia component, which is designed to provide an HTTP interface for JMX (Java Management Extensions).
According to technical analysis from Horizon3.ai and The Hacker News:
- Unauthenticated Access: Attackers can reach the Jolokia endpoint without valid credentials if the service is exposed to the internet.
- Input Validation Failure: By sending a specially crafted HTTP request, an attacker can bypass security filters and force the server to load malicious Java classes from a remote source.
- Full Takeover: Successful exploitation results in full Remote Code Execution (RCE) under the privileges of the ActiveMQ service, allowing for lateral movement, data exfiltration, or ransomware deployment.
Federal Directive and Remediation
Under Binding Operational Directive (BOD) 22-01, Federal Civilian Executive Branch (FCEB) agencies are mandated to patch or mitigate this vulnerability within a strict three-week window. While the directive applies specifically to federal agencies, CISA strongly urges all private sector organizations — particularly those in critical infrastructure — to prioritize this update.
"ActiveMQ is the 'glue' that holds many industrial and financial systems together," noted a security researcher at SecurityWeek. "When the broker is compromised, the integrity of every message passing through that system is called into question."
The CyberSignal Analysis
Signal 01 — The Resurgence of "Middleman" Attacks
CVE-2026-34197 highlights a growing trend: threat actors are moving away from targeting end-user devices and toward the Message Broker layer. Because ActiveMQ sits between multiple applications, a compromise here allows an attacker to "listen in" on or manipulate data traffic before it is even encrypted or logged by the receiving application. The "Signal" for CISOs is to audit every "bridge" component (like Jolokia) that exposes internal management logic to HTTP traffic.
Signal 02 — KEV as the New "Priority One"
CISA’s KEV catalog has become the most important document in vulnerability management. If a bug is on this list, it means the exploit code is stable and being used in the wild. For B2B organizations, seeing ActiveMQ on this list should trigger an immediate "stop-work" to verify the patch status of all middleware.