AstraZeneca Investigates Major Data Theft by Lapsus Group

Global pharmaceutical leader AstraZeneca is investigating claims of a significant data breach after a cybercrime group alleged it successfully exfiltrated sensitive internal information, including proprietary source code and clinical data.
The extortion group, identified by security researchers as a contingent of the Lapsus$ hacking collective, posted evidence of the alleged intrusion on an encrypted messaging platform earlier today. The shared files purportedly include samples of internal communications, architectural diagrams of the company’s digital infrastructure, and snippets of code related to drug development platforms.
In a brief statement, AstraZeneca acknowledged it is "aware of the claims" and has launched an internal investigation to determine the validity and scope of the alleged breach. The company has not yet confirmed whether any patient data or sensitive intellectual property has been compromised.
"We take the security of our information extremely seriously and have robust measures in place to protect our systems," a company spokesperson said. "Our investigation into these claims is ongoing."
The Lapsus$ group is known for high-profile "extortion-only" attacks, previously targeting major technology firms such as Microsoft, NVIDIA, and Samsung. Unlike traditional ransomware groups that encrypt files to demand payment, this collective typically focuses on stealing sensitive data and threatening its public release unless a ransom is paid.
Preliminary analysis by third-party cybersecurity firms suggests the breach may have originated from a compromised developer account or a misconfigured internal repository. Security researchers at SOCRadar noted that the leaked samples appear to contain credentials and API keys, which could potentially grant further access to the company’s cloud environments if not immediately revoked.
AstraZeneca, which played a central role in the global response to the COVID-19 pandemic, has been a frequent target of state-sponsored and criminal cyber activity over the past three years. This latest incident highlights the sustained interest threat actors have in the pharmaceutical sector’s research and development data.
The company has notified relevant law enforcement authorities and regulatory bodies in both the United Kingdom and the United States. No disruptions to AstraZeneca’s manufacturing or supply chain operations have been reported at this time.
The CyberSignal Analysis
The alleged AstraZeneca breach serves as a critical indicator of the evolving "extortion-without-encryption" model that continues to plague the healthcare and life sciences sectors. Based on the available data regarding the incident and the threat actor's history, several strategic takeaways emerge:
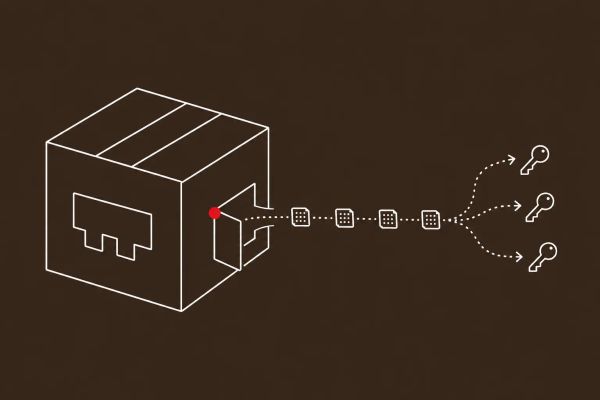
- Targeting the Supply Chain of Ideas: The focus on source code and architectural diagrams suggests that threat actors are shifting away from disrupting immediate operations toward stealing the "blueprints" of a company. For pharmaceutical firms, the loss of proprietary R&D data represents a long-term competitive risk that far outweighs the immediate cost of a system outage.
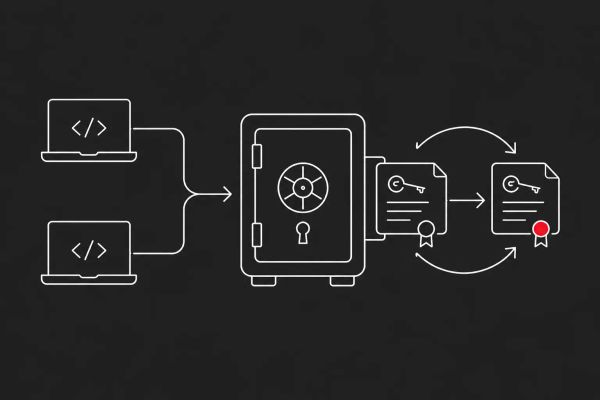
- The "Developer-First" Attack Vector: Evidence points toward the exploitation of developer environments — such as GitHub or internal GitLab instances — rather than traditional corporate workstations. This reinforces the need for CISOs to implement strict Multi-Factor Authentication (MFA) and secret-scanning tools to prevent API keys from being stored in plain text.
- The Lapsus$ Resurgence: This incident marks a notable return to activity for elements associated with the Lapsus$ group. Their methodology relies heavily on social engineering and the purchase of compromised credentials, suggesting that technical defenses alone are insufficient without robust identity and access management (IAM) strategies.
- Regulatory Scrutiny: Because AstraZeneca handles sensitive clinical trial data, this incident may trigger mandatory reporting under GDPR and HIPAA. The speed and transparency of the company's disclosure will likely be scrutinized by global regulators as a benchmark for pharmaceutical data stewardship.