The PowerSchool Breach: 20-Year-Old Face of a "Historic" Academic Cyberattack

Matthew Lane, the hacker behind a massive intrusion into student information systems, admits to federal crimes, highlighting the fragile state of K-12 and collegiate data security.
CHICAGO, IL — Matthew Lane, a 20-year-old former college student, has admitted to orchestrating one of the most expansive cyberattacks on the American educational system in recent history. The breach, which targeted the PowerSchool student information platform, exposed the records of millions of students, ranging from kindergarteners to college seniors, across thousands of school districts.
In a rare and candid public admission, Lane described his actions as a compulsive "addiction" to finding system vulnerabilities. His arrest by the FBI ends a multi-year spree that saw sensitive student data — including grades, disciplinary records, and social security numbers — systemically exfiltrated from school servers across the country.
The "Minor Mayhem" Phenomenon
The case against Lane is part of a broader federal investigation into "Gen Z" hackers, often dubbed "Minor Mayhem" by law enforcement. Unlike state-sponsored actors, these individuals frequently operate from their bedrooms, driven by a mix of curiosity, peer recognition on platforms like Discord, and financial gain.
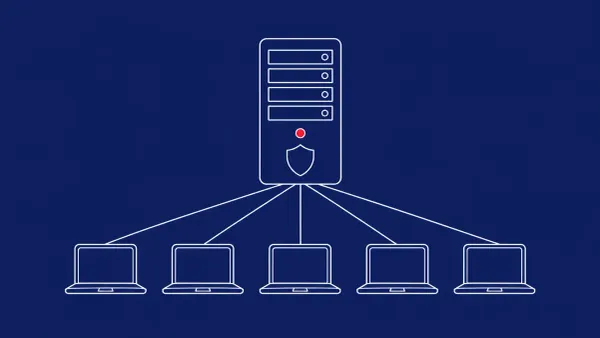
Lane’s method involved exploiting credential-based vulnerabilities in PowerSchool, a platform utilized by over 50 million students globally. By gaining administrative-level access, Lane was able to bypass traditional security perimeters, effectively "living off the land" within the school networks. The data collected was then reportedly indexed or sold on underground forums, creating a long-term identity theft risk for a generation of students whose data was compromised before they even reached adulthood.
A Systemic Wake-Up Call
Educational institutions have long been considered "soft targets" by the cybersecurity community. Underfunded IT departments and a vast, interconnected user base make school districts particularly vulnerable to the exact type of credential harvesting Lane employed.
Federal prosecutors emphasized that Lane’s breach was not a sophisticated zero-day attack, but rather a persistent exploitation of known security gaps and weak authentication protocols within the education sector. Lane himself expressed a sense of relief upon his capture, stating to investigators that he "needed to be stopped" as his obsession with breaching new networks had spiraled out of control.
The CyberSignal Analysis
Signal 01 — The Institutional "Soft Target"
The PowerSchool incident is a signal that the educational sector remains a primary target for low-complexity, high-impact attacks. While much focus is placed on protecting financial or healthcare data, student data is arguably more valuable on the dark web because it provides "clean" identities that can go unmonitored for years. This highlights a critical need for zero trust implementation in K-12 environments.
Signal 02 — The Ethics of "Addictive" Hacking
Lane’s admission of a "hacking addiction" mirrors a growing trend in juvenile cybercrime. The gamification of vulnerability research in Discord communities has created a pipeline where young talent drifts into felony-level activity without a clear understanding of the legal consequences. Organizations must look beyond technical patches and consider the human element of insider threat prevention when dealing with student-operated networks.