The AI-Weaponization Era: Mexican Government Targets Hit by Surge in LLM-Assisted Cyberattacks
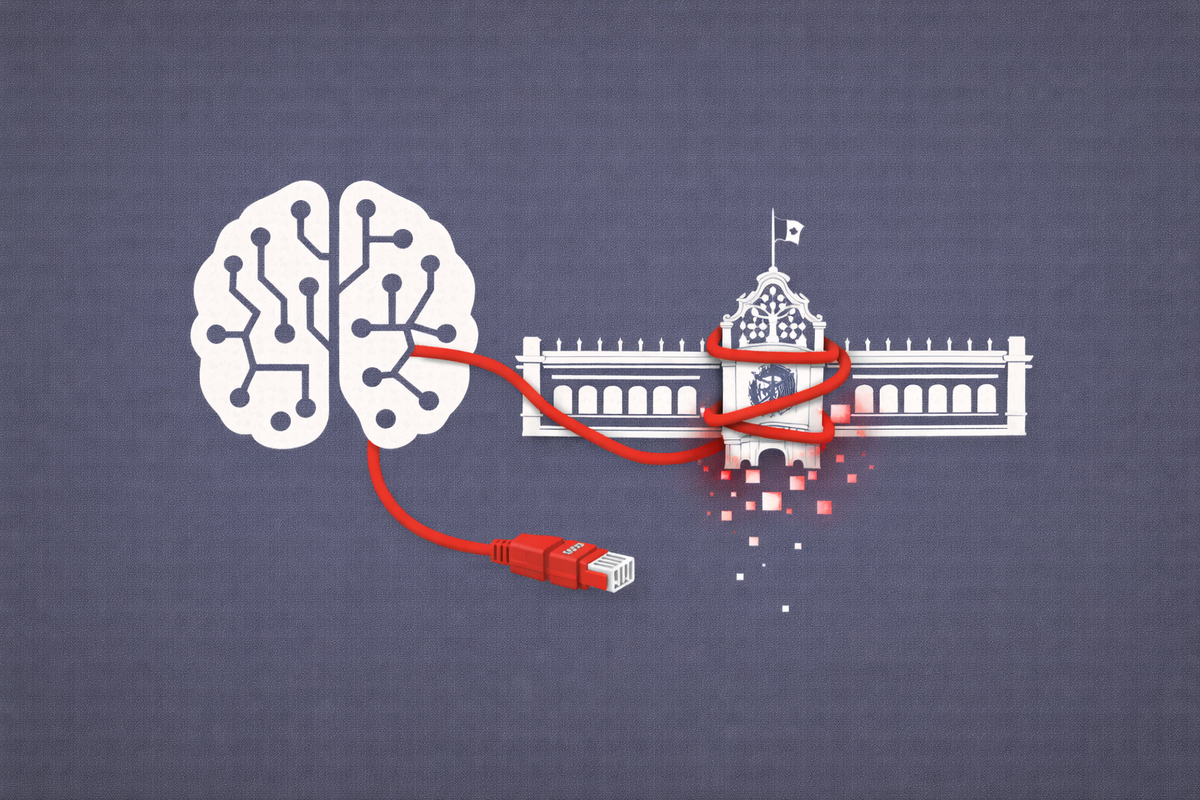
A series of sophisticated breaches over the past month, including a 150GB data theft and a disruption of the country's busiest port, reveals how threat actors are leveraging Large Language Models (LLMs) to dismantle state defenses.
MEXICO CITY — The Mexican government is reeling from a wave of high-impact cyberattacks that have exposed the vulnerabilities of its national digital infrastructure. Over the past 30 days, threat actors have successfully targeted both sensitive administrative databases and critical logistics hubs, utilizing a combination of traditional exploits and pioneering AI-assisted social engineering and code generation.
The most alarming development for global security analysts is the confirmed use of advanced AI chatbots — including Anthropic’s Claude and OpenAI's GPT-4 — to facilitate the extraction of government records and the automation of attack infrastructure.
The Timeline of the Attacks
The "Claude" Breach: 150GB of Stolen State Data
In what researchers are calling a milestone for AI-powered cybercrime, a threat actor successfully exfiltrated 150GB of sensitive data from Mexican government servers. Forensic analysis suggests the attacker utilized Claude to bypass security filters and generate specialized scripts that identified "blind spots" in the government's security stack.
The stolen archive reportedly includes:
- Confidential Diplomatic Communications: Internal memos regarding regional security and trade.
- Sensitive Citizen Data: Records that could be leveraged for large-scale identity theft or further targeted phishing.
- Security Credentials: Encrypted hashes and system configurations that provide a roadmap for future intrusions.
While AI providers have strict guardrails against "jailbreaking" for malicious purposes, the attacker reportedly used sophisticated prompt-injection techniques to trick the model into assisting with code optimization that was ultimately used for the breach.
Port Infrastructure Under Fire: The Manzanillo Incident
Concurrent with the AI-driven data thefts, the National Port Administration (ASIPONA) in Manzanillo — Mexico's most vital gateway for Pacific trade — activated emergency cybersecurity protocols following a breach of its Port Community System (PIS).
The attack on the PIS platform created an immediate risk of:
- Logistics Disruption: Interference with the automated scheduling of cargo and vessel movements.
- Fraudulent Documentation: The potential for attackers to alter manifests or redirect high-value shipments.
- Supply Chain Contagion: The risk of the malware spreading to the private logistics firms and shipping lines integrated with the port’s network.
Manzanillo officials have since moved the system to a restricted "fail-safe" mode, though the incident has reignited concerns regarding the cybersecurity maturity of Mexico’s critical infrastructure.
The CyberSignal Analysis
Signal 01 — AI Guardrails are Not Absolute
The use of Claude and GPT-4 in these attacks confirms that "Adversarial AI" is no longer a theoretical threat. For policy-makers, this is a signal that AI Governance must move beyond ethics and into active defense. If attackers can use LLMs to find "blind domains" in a security stack, defenders must use the same tools to find them first.
Signal 02 — Critical Infrastructure as a Geopolitical Lever
The targeting of the Manzanillo port follows a global trend of "Quiet Sabotage." By disrupting a nation's logistics platform, attackers can cause economic damage far exceeding the value of a ransom. As we noted in our Investigation into the Anodot Supply Chain breach, the interconnected nature of modern trade means a single government breach can have cascading effects on global commerce.