Swift Containment in Cybersecurity: Why Speed Defines Breach Impact
Swift containment is one of the most critical phases of modern cybersecurity. In this blog post, we provide in-depth, accessible information about swift containment and its role in protecting organizations from evolving cyber threats. As cyber threats grow more sophisticated and attack surfaces expand across hybrid environments, organizations must respond rapidly to limit the scope of a cybersecurity incident and protect sensitive data.
Organizations must respond swiftly to cyber incidents to mitigate potential damage. The breach's impact — measured by the extent of operational and reputational damage — can be significantly limited when swift containment is achieved, as it prevents prolonged dwell time and widespread disruption.
When a cyber incident is detected, the difference between minor disruption and a full-scale data breach often comes down to containment time. Containment strategies specifically aim to reduce dwell time and restrict lateral movement, which directly mitigates the breach's impact. Organizations that can isolate affected systems quickly are far more likely to maintain operational continuity, reduce reputational damage, and preserve customer trust.
What Is Swift Containment in Cybersecurity?
Swift containment refers to the coordinated actions taken by security teams to isolate, limit, and control a cybersecurity incident after it has been detected. Breach containment refers to the strategies and actions taken to limit the scope and impact of a cybersecurity incident after it has been detected. It is a vital component of incident response and serves as the bridge between detection and full remediation.
Effective containment strategies focus on minimizing the breach’s impact while maintaining business operations. This means isolating compromised systems, restricting attacker access, and preventing further lateral movement across the network without disrupting unaffected services.
Understanding Data Breach Risks
Operational Impact of Data Breaches
Data breaches have emerged as one of the most significant operational threats facing modern enterprises. The numbers tell a stark story: incident frequency continues climbing while associated costs reach record highs, forcing organizations across every sector to confront an uncomfortable reality.
When attackers successfully penetrate corporate networks, the resulting damage extends far beyond immediate technical concerns. The consequences can include demolished customer confidence and cascading operational failures that can persist for months.
The Importance of Rapid Containment
Security researchers and federal agencies have consistently identified rapid containment as the critical factor separating manageable incidents from catastrophic breaches. The difference often comes down to minutes, not hours.
Effective response teams focus on immediate threat isolation, cutting off lateral movement before attackers can expand their foothold across interconnected systems.
This requires:
- Security operations centers equipped with automated detection capabilities
- Incident response playbooks that prioritize speed over perfection
Broader Implications of Data Breaches
The implications reach beyond corporate boardrooms. Public safety hangs in the balance when critical infrastructure providers suffer breaches, while consumer trust erodes each time personal information lands in criminal hands.
Today's threat actors exploit an expanding attack surface — from cloud misconfigurations to unpatched legacy systems — making adaptive defense strategies essential rather than optional.
Addressing Legacy Infrastructure Challenges
Legacy infrastructure presents particular challenges for security teams operating in hybrid environments. Older systems frequently lack the granular controls necessary for effective network segmentation, creating blind spots that skilled attackers readily exploit.
Forward-thinking organizations are addressing these gaps through:
- Microsegmentation deployments
- Zero Trust implementations
- Advanced orchestration platforms that extend modern security controls across their entire technology stack
Building a Coordinated Security Program
Successful cybersecurity programs demand more than sophisticated technology solutions. They require coordinated efforts spanning IT, legal, communications, and executive leadership teams, supported by continuous risk assessment processes that evolve alongside emerging threats.
Security considerations must be embedded into platform architecture from the ground up, with every department understanding their role in protecting critical assets and maintaining operational resilience.
The Evolving Cybersecurity Landscape
The cybersecurity landscape will only grow more complex as digital transformation accelerates and threat actors refine their techniques. Organizations that treat breach preparation as a strategic priority — investing in robust containment capabilities, fostering cross-functional collaboration, and maintaining proactive security postures — position themselves to weather inevitable incidents while preserving both customer relationships and business continuity in an increasingly dangerous digital environment.
Why Swift Containment Is Critical After a Data Breach
A data breach can escalate rapidly if not contained early. Attackers often move laterally across systems, accessing additional data and expanding the scope of compromise, which increases both financial and operational risk.
Swift containment helps reduce dwell time, limit exposure of sensitive data, and protect critical operations. It also plays a key role in ensuring compliance with breach reporting regulations, which now require many organizations to report incidents within strict timeframes.
Failure to act quickly can lead to regulatory penalties, legal consequences, and long-term reputational damage. For many organizations, the ability to contain a cyber incident quickly is essential for maintaining business continuity and public trust.
Containment Strategies to Reduce Lateral Movement
Containment strategies are designed to stop attackers from expanding their access within a network.
Key strategies include:
- Network segmentation: Divides systems into isolated zones to control traffic flow and restrict unauthorized access.
- Microsegmentation: Applies granular controls at the workload level, ensuring that even if one system is compromised, the attacker cannot easily move to others.
- Hybrid environment controls: These strategies are especially important in hybrid environments, where infrastructure spans cloud, on-premises, and third-party systems.
By limiting lateral movement, organizations can significantly reduce the scope and impact of a breach while preserving the integrity of unaffected systems.
The Role of Incident Response in Swift Containment
Security teams and IT departments play a key role in incident response, working together to identify affected systems, assess the scope of the incident, and implement swift containment measures.
Steps in Incident Response for Swift Containment
- Identify threats and vulnerabilities: Early identification during the incident response lifecycle enables timely action and effective mitigation.
- Implement predefined containment actions: Use incident response plans with clear, predefined steps for isolating affected systems.
- Communicate across stakeholders: Establish clear communication protocols to ensure all relevant parties are informed and coordinated.
- Coordinate response efforts: Ensure that actions are consistent, efficient, and aligned with business priorities.
- Maintain public communication: Transparent reporting helps maintain customer trust and demonstrates accountability during a cybersecurity incident.
Proactive measures taken by the team and department in incident response can help prevent future cyber incidents.
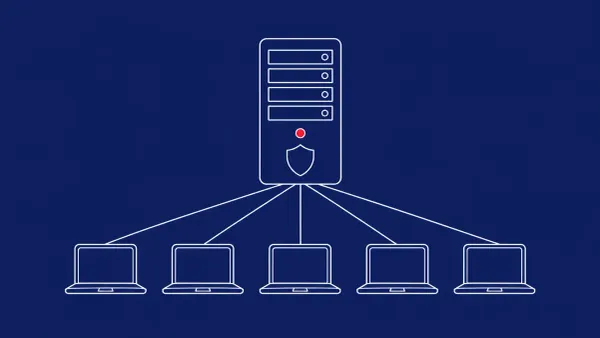
Real-Time Visibility and Detection in Cyber Incidents
Real-time visibility into network traffic is vital for detecting threats and enabling swift containment. Without visibility, organizations cannot accurately identify affected workloads or understand the scope of a compromise.
Modern security platforms rely on:
- Real-time telemetry
- Threat intelligence to detect anomalies and suspicious behavior
This allows security teams to respond proactively and contain threats before they escalate.
Continuous monitoring across systems, endpoints, and infrastructure ensures that organizations can detect emerging threats and act quickly to limit their impact.
Implementing effective containment practices helps organizations protect their assets, maintain compliance, and uphold stakeholder trust.
Automation and Orchestration in Containment
Automation plays a critical role in reducing containment time.
Automated responses can:
- Isolate compromised endpoints
- Revoke access
- Block malicious activity within seconds of detection
Orchestration tools further enhance containment by coordinating actions across multiple systems and platforms. This ensures that containment measures are applied consistently and efficiently across the entire environment.
By integrating automation into incident response, organizations can improve containment effectiveness and reduce the burden on security teams.
Challenges of Containment in Hybrid Environments
Hybrid environments introduce additional challenges for containment. Organizations must manage security across cloud platforms, on-premises infrastructure, and third-party services, all of which may have different controls and visibility levels.
Older systems can also create vulnerabilities, as they may lack modern security features or integration capabilities. This makes it more difficult to implement effective containment strategies and maintain control over the environment.
To address these challenges, organizations must adopt a proactive approach that includes:
- Continuous monitoring
- Vendor risk management
- Integration of security tools across platforms
The Role of Threat Intelligence in Swift Containment
In the evolving landscape of cybersecurity defense, threat intelligence has emerged as a critical foundation for effective containment operations. Security teams now rely heavily on current, actionable intelligence feeds to stay ahead of attackers who continuously refine their methods.
Benefits of Threat Intelligence in Containment
- Anticipates threat actor behavior patterns and implements defensive measures before vulnerabilities can be weaponized
- Enables rapid recalibration of containment protocols as new attack campaigns surface
- Reduces the window for lateral movement across network segments
- Provides additional layers of protection for sensitive data repositories
When incident response teams integrate threat intelligence directly into their operational workflows, they gain the decisive advantage needed to limit breach impact and maintain business continuity.
Organizations that successfully embed these intelligence streams into their security stack demonstrate:
- Improved threat detection capabilities
- Faster containment responses
- More effective threat neutralization
Measuring Containment Success
Key Metrics for Containment Success
Measuring containment success has become a critical discipline for security teams navigating today's threat landscape. Organizations that excel at incident response consistently track three core metrics:
- Time to containment: How quickly threats are isolated after detection
- Breach impact scope: The extent of systems and data affected by the incident
- Operational resilience: The ability to maintain business functions throughout the crisis
These performance indicators reveal whether current containment protocols can withstand real-world attacks — from ransomware campaigns that encrypt entire networks to APT groups conducting months-long data exfiltration operations.
Benefits of Smart Containment Strategies
Smart containment strategies deliver benefits far beyond immediate threat mitigation. When security teams successfully isolate threats without disrupting core business functions, they:
- Preserve customer confidence
- Protect brand reputation
- Identify process weaknesses before they become crisis points
The most mature organizations treat containment metrics as intelligence, analyzing response patterns to improve future incident response and maintain operational stability.
Containment and Eradication: Beyond the Initial Response
When security teams successfully contain a cyber incident, their work is far from over. The critical next phase — eradication — demands swift action to completely remove threats from compromised systems.
Steps for Effective Eradication
- Conduct detailed forensic analysis: Map the full attack timeline and understand adversary movement.
- Remove malicious code and backdoors: Ensure no threats remain hidden in the infrastructure.
- Restore trusted system baselines: Use orchestration platforms and automated response capabilities to accelerate eradication, especially in hybrid environments.
Organizations that take a comprehensive approach to eradication — rather than quick fixes — position themselves to restore trusted system baselines and significantly reduce the likelihood of reinfection.
Compliance, Reporting, and Regulatory Impact
Containment is not just a technical requirement — it is also a regulatory necessity. Recent regulations require organizations to report cybersecurity breaches within four days of discovery, increasing the importance of rapid detection and response.
Failure to contain breaches promptly can result in significant fines and legal consequences under frameworks such as GDPR, HIPAA, and PCI-DSS. Implementing effective containment practices demonstrates compliance and a commitment to protecting customer data.
Timely reporting also supports transparency and accountability, helping stakeholders make informed decisions and maintain confidence in the organization.
Building a Proactive Approach to Swift Containment
Organizations must move beyond reactive responses and adopt proactive measures to improve containment.
Key components of a proactive approach include:
- Threat intelligence: Integrate up-to-date intelligence feeds to anticipate and counter emerging threats.
- Real-time monitoring: Continuously monitor systems, endpoints, and infrastructure for suspicious activity.
- Automation: Use automated tools to accelerate detection and containment.
- Strong identity controls: Enforce robust authentication and access management policies.
These elements work together to enhance resilience and reduce the risk of large-scale breaches. By focusing on prevention and preparedness, organizations can strengthen their ability to respond to cyber incidents and minimize their impact.
Lessons Learned from Past Breaches
Best Practices from Past Incidents
Past security incidents serve as a critical roadmap for organizations looking to bolster their incident response capabilities and containment strategies. The data is clear: proactive measures make all the difference.
Best practices include:
- Trust enforcement: Implement strict access controls and authentication.
- Consistent system patching: Regularly update and patch systems to close vulnerabilities.
- Well-rehearsed response protocols: Conduct regular incident response drills to ensure readiness.
These practices directly correlate with faster containment times and significantly reduced operational disruption when attacks inevitably occur.
The Value of Communication and Knowledge Sharing
The most effective incident responses come from sectors like law enforcement and public safety, where clear communication channels and decisive action are mission-critical requirements. These organizations:
- Keep stakeholders informed during a cyber incident
- Share knowledge through blog posts and educational content to highlight vulnerabilities and drive home the importance of robust cybersecurity practices
This approach builds organizational resilience while educating customers about the threat landscape they're navigating.
Implementing Lessons Learned
Organizations that emerge stronger from security incidents share a common trait: they actually implement the lessons learned from previous breaches. This means:
- Improving protection of critical data and services
- Enhancing threat response capabilities
- Maintaining the trust that customers and partners place in them as threats evolve
The Future of Swift Containment in Cybersecurity
Swift containment is evolving as organizations adopt more advanced technologies and strategies. Modern approaches are becoming more predictive, leveraging AI and analytics to identify threats before they cause significant damage.
Threat containment is increasingly embedded across the technology stack, enabling faster response times and more effective isolation of threats. As cyber threats continue to evolve, the ability to contain incidents quickly will remain a defining factor in cybersecurity success.
Ultimately, organizations that prioritize swift containment will be better positioned to protect their assets, maintain operational continuity, and build long-term resilience.
FAQ: Swift Containment in Cybersecurity
What is swift containment in cybersecurity?
Swift containment refers to the rapid actions taken to isolate and control a cybersecurity incident to limit damage and prevent further spread.
Why is containment important after a data breach?
Containment reduces the impact of a breach by limiting access, preventing lateral movement, and protecting sensitive data and business operations.
How can organizations reduce containment time?
Organizations can reduce containment time by using automation, real-time monitoring, and well-defined incident response plans.
What role does automation play in containment?
Automation enables faster responses by instantly isolating affected systems and blocking malicious activity.
How does containment support compliance?
Effective containment helps organizations meet regulatory requirements by limiting damage and enabling timely breach reporting.