Microsoft Warns of Sharp Rise in Teams-Based Helpdesk Impersonation Campaigns
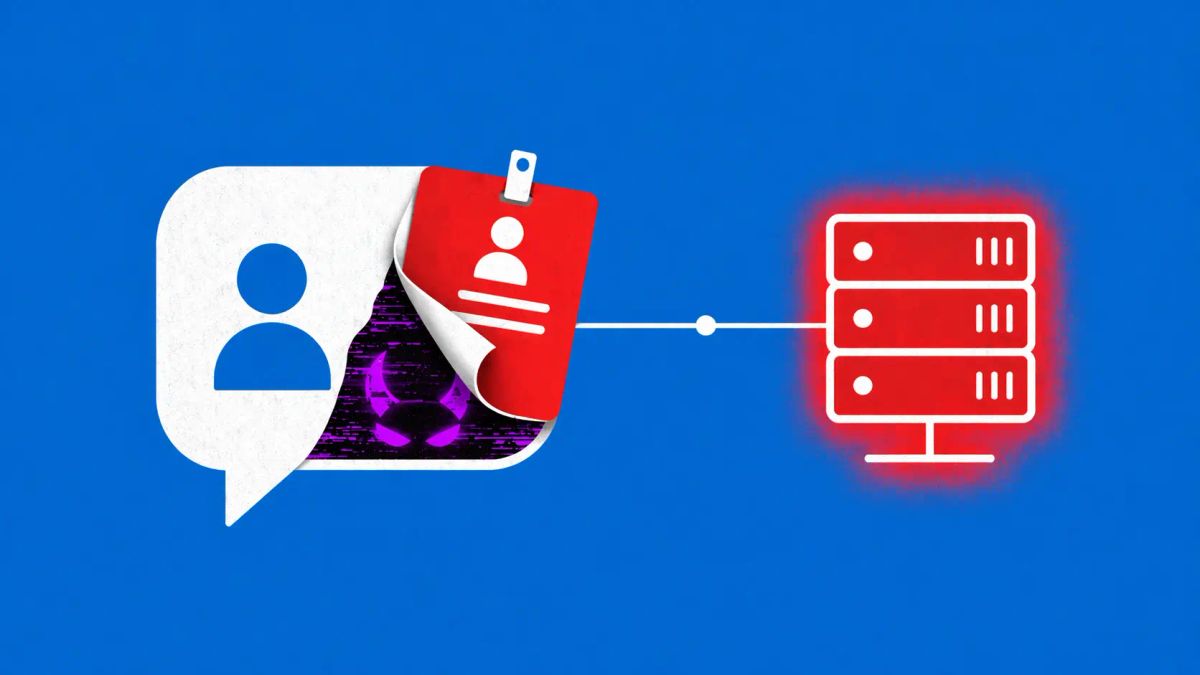
A new human-operated intrusion playbook leverages cross-tenant communication to bypass traditional email security, targeting high-privilege credentials through "Helpdesk" deception.
REDMOND, WA — Microsoft Threat Intelligence has issued a critical warning regarding a sophisticated surge in "Helpdesk Impersonation" attacks conducted via Microsoft Teams. The campaign, which targets enterprise employees, represents a tactical pivot by threat actors who are increasingly abandoning email-based phishing in favor of the perceived "trusted environment" of internal collaboration platforms.
According to a security bulletin released by Microsoft on April 18, 2026, the attackers are utilizing a "cross-tenant" intrusion playbook designed to exfiltrate data and gain persistent access to corporate networks.
Attack Tactics Overview
The Anatomy of the Teams Intrusion
Unlike traditional automated phishing, these are human-operated attacks that rely on high-pressure social engineering.
Security analysts at BleepingComputer and CSO Online have identified the core stages of the attack:
- The Bait: Attackers create a new Microsoft 365 tenant and name it something deceptive, such as "Technical Support" or "IT Helpdesk."
- The Request: Using the "External Access" feature in Teams (which is often enabled by default in many organizations), the attacker sends a direct message to a target employee. The message typically warns of a "security anomaly" or a "required account update."
- The Hook: The attacker requests the employee to approve a Multi-Factor Authentication (MFA) prompt or provide a "One-Time Password" (OTP) under the guise of verifying their identity.
- The Breach: Once the MFA is bypassed, the attacker gains full access to the victim’s account, allowing for lateral movement, data exfiltration, and the creation of new administrative backdoors.
Bypassing the "Email Shield"
The primary danger of this campaign is its ability to bypass standard Secure Email Gateways (SEGs). Because the interaction happens entirely within the Teams ecosystem, employees often feel a false sense of security. "Users are trained to be suspicious of external emails, but they often treat a Teams chat as an inherently 'internal' and safe communication," Microsoft noted in their threat report.
Microsoft suggests that these attacks are likely the work of sophisticated financially motivated groups, though some techniques mirror the "scattered spider" playbooks used in previous high-profile social engineering breaches.
The CyberSignal Analysis
Signal 01 — The Fallacy of the "Trusted Perimeter"
This incident is a definitive "Signal" for Identity & Access Management (IAM). In 2026, the perimeter is no longer your network; it is your identity. The fact that an external entity can message your employees through a "trusted" chat platform highlights a massive oversight in default SaaS configurations. For B2B leaders, the takeaway is clear: External Access in Teams must be restricted to "Allowed Domains" only. Leaving it open is the digital equivalent of leaving your office front door unlocked for anyone claiming to be the plumber.
Signal 02 — The Pivot to "Human-Operated" Deception
The "Signal" for security awareness teams is that automation is no longer the biggest threat — human persistence is. These attackers are willing to engage in real-time chat to manipulate victims. This highlights a critical need to move beyond "Phishing Simulations" toward Operational Resilience training. If your security relies on an employee never clicking a link or trusting a "Helpdesk" message, your security is fundamentally broken.