Cryptojacking: Definition, Detection, and Prevention

As cryptocurrency adoption continues to grow, so does a lesser-known but highly impactful cyber threat: cryptojacking. Cryptojacking is a type of cyberattack in which cybercriminals hijack the computing resources of victims' devices to mine cryptocurrency without permission. Unlike traditional cyberattacks that focus on stealing data, cryptojacking silently hijacks a victim’s computing resources to generate digital money — often without the user ever knowing. Cryptocurrency is digital money that is generated by solving complex mathematical problems, known as hashes. Attackers target a wide range of computing devices, including PCs, servers, and mobile devices, to maximize their illicit mining operations.
Cryptojacking is a type of cyberattack in which cybercriminals hijack the computing resources of a victim’s computer or mobile device to mine cryptocurrency without permission. This allows attackers to profit directly from the victim’s processing power, electricity, and hardware — turning compromised systems into hidden mining machines. Bitcoin mining and other cryptocurrency mining processes require solving complicated math problems, which is why attackers seek out devices with available computing power.
Because cryptojacking attacks can run quietly in the background, they often remain undetected for long periods, causing performance degradation, increased energy consumption, and long-term financial impact. Cryptocurrency is digital money that is generated by solving complex mathematical problems, known as hashes, and cryptojacking exploits this process.
Introduction
This guide is for IT professionals, security teams, and anyone interested in understanding and preventing cryptojacking. We cover what cryptojacking is, how it works, real-world examples, detection methods, and prevention strategies. Cryptojacking is a type of cyberattack in which cybercriminals hijack the computing resources of victims' devices to mine cryptocurrency without permission. Cryptocurrency is digital money that is generated by solving complex mathematical problems, known as hashes.

Cryptojacking has emerged as one of the more insidious threats in today's cybersecurity landscape, deploying specialized malware to silently commandeer computing resources from unsuspecting victims. The attack method has gained significant traction alongside the meteoric rise of cryptocurrencies like Bitcoin and Monero, creating a lucrative opportunity for cybercriminals to monetize compromised systems. The mechanics are deceptively simple yet effective: attackers inject malicious cryptomining code into target devices, essentially turning victim machines into unwitting participants in cryptocurrency mining operations. This hijacked processing power gets redirected toward solving the computationally intensive cryptographic puzzles that validate blockchain transactions and mint new digital coins — all funneling profits directly to the attackers.
The consequences for victims extend well beyond system slowdowns, encompassing inflated electricity bills, severely degraded performance, and in some cases, permanent hardware damage from prolonged overuse. As organizations increasingly embrace digital currencies and remote work environments expand the attack surface, security professionals must recognize cryptojacking as a critical threat vector that demands immediate attention and robust defensive strategies.
Summary: What is Cryptojacking and How Can It Be Detected and Prevented?
What is cryptojacking?
Cryptojacking is a cyberattack where attackers secretly use a victim’s computing resources to mine cryptocurrency without their knowledge or consent.
How can cryptojacking be detected?
It can be detected by monitoring for signs such as high CPU usage, slow performance, overheating, rapid battery drain, and increased electricity bills. Security teams can also monitor network traffic for connections to known mining pools and use anomaly detection tools.
How can cryptojacking be prevented?
Prevention strategies include using ad-blockers and anti-cryptomining browser extensions, robust antivirus and endpoint protection, regular software updates, blocking JavaScript on untrusted sites, monitoring system performance, and educating users about phishing and safe browsing practices.
Next, we’ll dive deeper into how cryptojacking works and the specific methods attackers use.
How Cryptojacking Works
Cryptocurrency Mining Basics
To understand how cryptojacking works, it’s important to first understand cryptocurrency mining. Cryptocurrency is digital money generated by solving complex mathematical problems using computing power. The central processing unit (CPU) is often used for mining, but it is less efficient than specialized hardware like GPUs. These calculations validate transactions on a blockchain. The blockchain is a distributed database that records all transactions made with a specific cryptocurrency.
How Attackers Hijack Devices
Cryptojacking essentially offloads this mining process onto victims’ devices. Instead of attackers paying for hardware and electricity, they use compromised systems to perform the work. Attackers deploy cryptojacking software to hijack computational power from victims' devices, allowing them to mine cryptocurrency covertly.
Cryptojacking malware can embed itself within a computer system, mobile device, or web browser and use its resources to mine cryptocurrency. Mined cryptocurrency is typically sent to the attacker's digital wallet, which acts as a secure vault for digital assets. These attacks often rely on malicious code or cryptojacking scripts that run continuously in the background.
Consequences for Victims
The result is that attackers gain free money while victims experience reduced system performance, higher electricity bills, and potential hardware damage.
Next, we'll explore the specific methods attackers use to deliver cryptojacking malware.
Cryptojacking Malware and Attack Methods
Common Malware Delivery Methods
Cryptojacking malware is the most common method used in these attacks. This type of mining malware is typically delivered through phishing emails, malicious links, fake apps, or compromised software packages. Cryptojacking malware is often designed to evade detection by security tools, using advanced techniques to remain hidden.
Once installed, the malicious cryptomining software begins using the device’s CPU or GPU to mine cryptocurrency. Many cryptojacking operations use Monero due to its privacy features and lower computational requirements. Cryptojacking malware is usually embedded with worm-like characteristics, allowing it to spread throughout networks.
Types of Cryptojacking Attacks
Cryptojacking attacks can be carried out in several ways:
- Malware-based attacks: Installing mining software directly onto a victim’s device.
- Binary-based attacks: Attackers deliver malicious executable files to the target systems, which operate as an independent process.
- Browser-based cryptojacking: Injecting JavaScript code into web pages that executes mining operations while the user is browsing.
- Supply chain cryptojacking: Attackers compromise legitimate software distribution channels to insert cryptomining code into applications or updates.
- Fileless cryptojacking: Operates entirely in system memory, making it harder for security tools to detect.
- Cloud infrastructure cryptojacking: Targets misconfigured cloud systems to scale mining operations rapidly.
Supply chain cryptojacking hijacks authentic software distribution channels to deliver mining malware. Cloud hijacking involves attackers stealing API keys or exploiting misconfigurations in cloud infrastructure to mine cryptocurrency. Monitoring for unauthorized mining activities is crucial for identifying such attacks.
Next, we’ll look at browser-based cryptojacking and how web exploits are used in these attacks.
Browser-Based Cryptojacking and Web Exploits
Browser-based cryptojacking has become one of the most common forms of attack. In this method, attackers inject cryptomining scripts into web pages or compromised websites.
When a user visits the infected site, the script automatically begins using the browser’s computing power to mine cryptocurrency. This type of attack does not require installing software, making it more difficult for users to detect.
Notable examples include The Pirate Bay, which ran JavaScript mining code using Coinhive, and the Los Angeles Times website, which was found to contain hidden cryptojacking code in 2018.
Because these attacks rely on browser activity, they often stop when the user closes the tab. However, during the session, they can significantly impact system performance and resource usage.
Next, we’ll discuss how to recognize the signs of cryptojacking and methods for detection.
Signs and How to Detect Cryptojacking
Knowing how to detect cryptojacking is critical for both individuals and organizations. These attacks are designed to remain hidden, but they often leave behind clear signs.
Common Signs of Cryptojacking
Look for the following indicators:
- Unusually high CPU usage (can be observed in Task Manager or Activity Monitor)
- Device running slowly or experiencing poor performance
- Overheating
- Rapid battery drain on mobile devices and laptops
- Persistent slowdowns
- Unexplained increases in utility costs or electricity bills
- Constant loud fan noise due to the system operating at maximum capacity
Even a slow computer can be exploited for cryptojacking, as attackers can use weak or older devices to mine cryptocurrencies or verify transactions without significant hardware resources. Victims of cryptojacking often experience significant increases in their electricity bills due to the high energy consumption of mining activities. For organizations, operational costs can rise sharply because of increased electricity usage and cloud compute bills.
Detection Methods
- Security teams can detect cryptojacking activity by monitoring network traffic for connections to known mining pools.
- Anomaly detection tools can identify unusual patterns in system behavior.
- Machine learning can be used in security tools to improve detection of cryptojacking by recognizing unusual patterns and behaviors that may indicate an attack.
- Monitoring CPU and GPU usage is essential, as cryptojacking attacks rely heavily on processing power.
Persistent slowdowns, overheating, unexplained performance degradation, and high electricity bills are strong indicators of infection.
Next, we’ll examine real-world cryptojacking attacks and their impact.
Cryptojacking Attacks and Real-World Examples
Cryptojacking attacks have impacted a wide range of organizations and platforms over the years. These real-world examples highlight how widespread and damaging these attacks can be.
In 2017, the fact-checking site PolitiFact was compromised using Coinhive mining scripts. In 2018, a European water utility experienced system disruptions due to cryptomining malware.
The Smominru botnet has infected hundreds of thousands of Windows systems worldwide, mining cryptocurrency at scale. In 2019, Graboid targeted unsecured Docker containers to mine Monero.
More recently, researchers observed a spike in cryptojacking images in open source repositories like Docker Hub, demonstrating how attackers are targeting modern development environments.
These incidents show that cryptojacking can affect everything from personal devices to critical infrastructure.
Next, we’ll discuss the broader impact of cryptojacking on systems and businesses.
The Impact of Cryptojacking on Systems and Businesses
Cryptojacking has serious consequences beyond just slower devices. The impact can be financial, operational, and even environmental.
High CPU usage leads to increased electricity costs and hardware wear and tear. Cryptojacking can cause financial losses from hardware wear and tear as the mining process overworks processing cores. Victims often experience significantly higher energy bills because their systems are running at full capacity for extended periods.
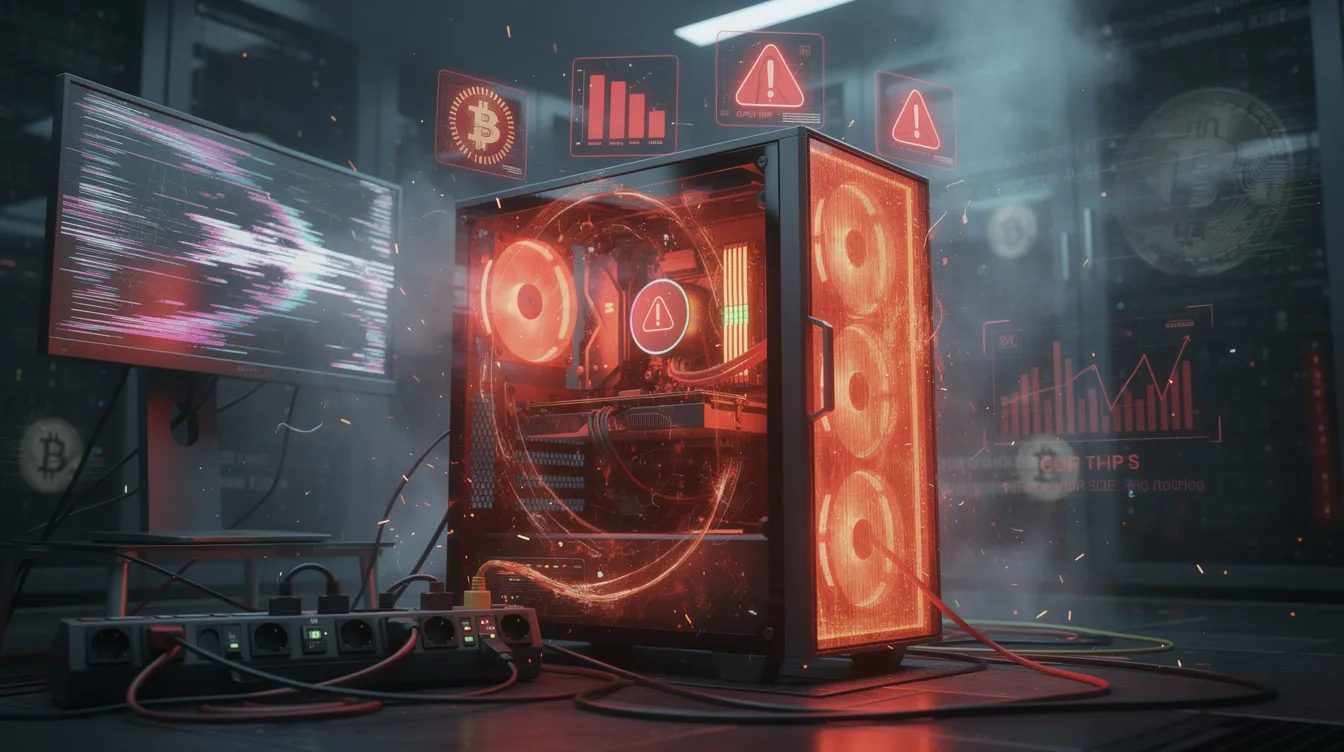
For businesses, the impact is even greater. Operational slowdowns, system crashes, and downtime can disrupt critical services. Cryptojacking can lead to severe performance issues, impacting critical operations, especially in regulated industries like healthcare. It can also result in potential data privacy violations for businesses.
Organizations may also face reputational damage if customers are affected by compromised systems, leading to a loss of public trust and potential future business. Additionally, cryptojacking can expose underlying security vulnerabilities that could be exploited for more serious attacks, such as ransomware or data theft. The costs associated with cryptojacking can compound over time, as attacks often go undetected for months, making it difficult to assess their true financial impact.
The environmental impact is also significant, as increased energy consumption from mining activities contributes to higher carbon emissions. Cryptojacking is different from other types of cybercrime because it effectively steals processing power and electricity rather than user data.
Next, we’ll look at recent news and trends in cryptojacking.
Cryptojacking News and Trends
The cybersecurity landscape continues to witness an alarming escalation in cryptojacking incidents, as threat actors refine their techniques to exploit both individual users and enterprise networks for unauthorized cryptocurrency mining operations. Several high-profile compromises have demonstrated the pervasive nature of these attacks and their ability to infiltrate trusted digital properties. The Los Angeles Times fell victim to such an attack in 2018, when malicious actors embedded cryptojacking scripts within the publication's Homicide Report section, silently harvesting Monero from unsuspecting visitors' devices. A year earlier, PolitiFact — a respected political fact-checking platform — suffered a similar breach through Coinhive, the now-defunct but once-ubiquitous cryptojacking service that became synonymous with browser-based mining abuse. The threat landscape extends far beyond individual website compromises, however. Large-scale operations like the Smominru botnet have successfully compromised hundreds of thousands of Microsoft Windows systems, while the Graboid worm demonstrated how attackers can pivot to exploit misconfigured Docker container environments. These evolving attack vectors highlight the critical need for comprehensive defensive strategies, including deployment of robust security solutions, selective JavaScript disabling in high-risk environments, and ongoing user education initiatives to safeguard organizational computing resources against unauthorized mining activities.
Next, we’ll discuss why cryptojacking is increasing and what makes it so attractive to attackers.
Why Cryptojacking Is Increasing
Cryptojacking has grown in popularity due to the rise of decentralized finance and the increasing acceptance of digital currencies. As cryptocurrency becomes more valuable, attackers have more incentive to exploit computing resources.
Cryptojacking is particularly attractive because it does not require stealing data or interacting directly with victims. Instead, attackers profit silently by using victims’ devices to mine cryptocurrency.
The ability to scale attacks across cloud infrastructure, containers, and distributed systems has also made cryptojacking more effective and widespread.
Next, we’ll outline practical steps you can take to prevent cryptojacking.
How to Prevent Cryptojacking
To prevent cryptojacking, organizations and individuals must implement multiple layers of security.
Key prevention methods include:
- Installing ad-blockers and anti-cryptomining browser extensions to block malicious scripts
- Using robust antivirus and endpoint protection tools to detect and stop mining malware before it spreads
- Keeping software updated and applying regular patch management to reduce the attack surface
- Blocking JavaScript on untrusted or high-risk websites (note: this may limit some website functionality)
- Using a whitelist of trusted websites to reduce exposure to malicious code
- Monitoring system performance and network activity for early signs of cryptojacking
- Implementing rate limiting, anomaly detection, and network traffic analysis to identify suspicious behavior
- Educating users through security awareness programs about phishing emails, malicious links, and safe browsing practices
- Enabling passwordless authentication and strong access controls to prevent unauthorized access to systems
Next, we’ll answer some frequently asked questions about cryptojacking.
Conclusion
Cryptojacking attacks have emerged as a persistent and evolving threat vector that continues to impact enterprise environments and individual systems alike, driving up operational costs through increased electricity consumption while degrading system performance and expanding organizational attack surfaces. Effective defense against these stealth mining operations requires deploying comprehensive endpoint protection solutions alongside specialized browser-based security extensions that can detect unauthorized cryptocurrency mining scripts. Organizations must implement continuous monitoring protocols to track system resource utilization and identify anomalous CPU activity patterns that often signal active mining malware.
Security awareness training remains a critical component of any defense strategy, as educating end users about the mechanics of cryptojacking attacks and reinforcing fundamental security hygiene practices significantly reduces successful infection rates across the threat landscape. Threat intelligence gathering through industry reporting and security research helps security teams stay ahead of emerging cryptojacking techniques and toolkits, enabling more proactive defensive postures. The most effective approach to combating this threat combines these technical controls with collaborative information sharing across the cybersecurity community, creating a more resilient defense ecosystem that can better identify, contain, and mitigate cryptojacking incidents before they cause significant operational impact.
Cryptojacking FAQs
What is cryptojacking?
Cryptojacking is a cyberattack where attackers use a victim’s computing resources to mine cryptocurrency without their knowledge or consent.
How do cryptojacking attacks work?
Cryptojacking attacks use malware or browser-based scripts to hijack computing power and perform cryptocurrency mining in the background.
What are the signs of cryptojacking?
Common signs include:
- High CPU usage
- Slow performance
- Overheating
- Rapid battery drain
- Increased electricity bills
Is cryptojacking dangerous?
Yes, cryptojacking can cause hardware damage, financial losses, operational disruptions, and increased exposure to other cyber threats.
How can you prevent cryptojacking?
You can prevent cryptojacking by:
- Using antivirus software
- Enabling security tools
- Keeping systems updated
- Monitoring for unusual activity