The Gentlemen’s Gambit: Systematic Scale Revealed as Ransomware Operation Integrates SystemBC
A joint forensic investigation has unmasked The Gentlemen, a rapidly expanding ransomware operation that leverages the SystemBC malware to automate enterprise-scale intrusions across more than 1,500 victims.
A joint forensic investigation has unmasked "The Gentlemen," a rapidly expanding ransomware operation that has successfully leveraged the SystemBC malware to automate enterprise-scale intrusions across 1,500 victims.
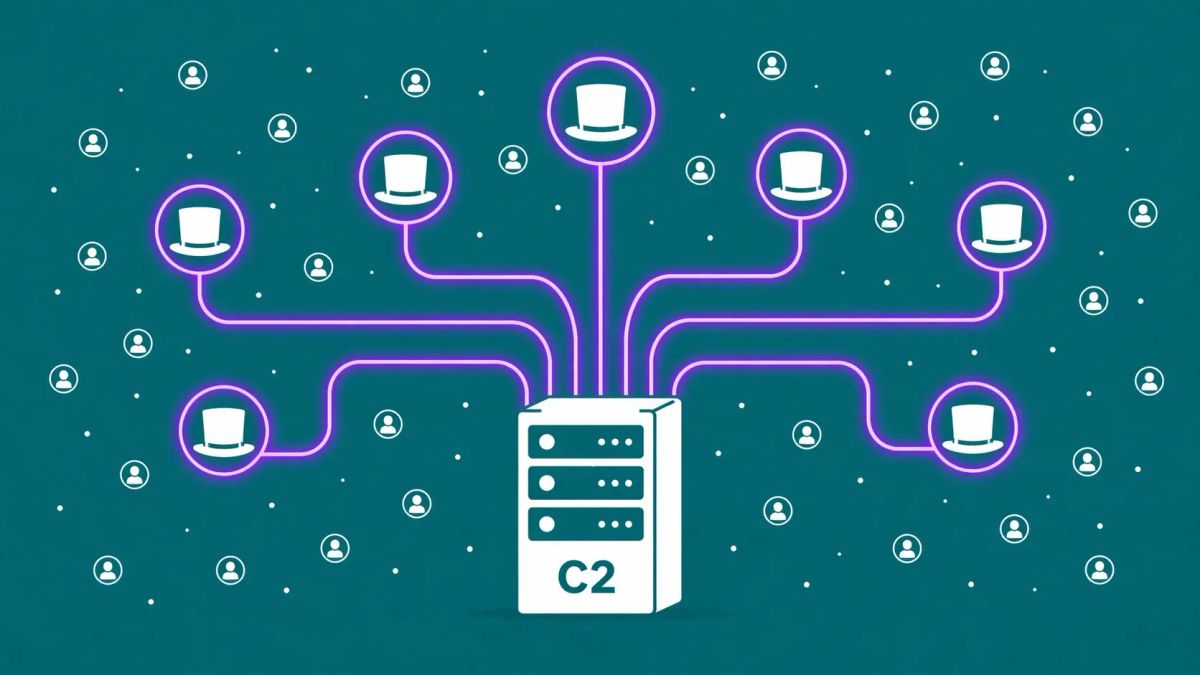
TEL AVIV, ISR — Security researchers have exposed the inner workings of a high-volume ransomware-as-a-Service (RaaS) affiliate known as The Gentlemen. In a detailed DFIR report released by Check Point Research, investigators revealed that the group’s meteoric rise is fueled by the integration of SystemBC, a sophisticated proxy malware and remote access trojan (RAT). By gaining access to a central Command & Control (C2) server used by the group, researchers discovered an active victim list exceeding 1,570 organizations, signaling a transition from manual "big game hunting" to automated, bot-powered extortion.
According to reporting from BleepingComputer and The Hacker News, the group has evolved beyond simple file encryption, utilizing a robust infrastructure designed for persistent access and mass data exfiltration.
The Gentlemen: Operation Infrastructure
The Mechanism: Proxy-Powered Persistence
The Gentlemen distinguish themselves through their reliance on SystemBC to maintain a stealthy foothold within victim networks. SystemBC acts as a SOCKS5 proxy, allowing the attackers to tunnel their traffic and bypass traditional firewall restrictions.
Based on analysis from Trend Micro and Infosecurity Magazine, the operation follows a distinct automated pipeline:
- The Initial Foothold: SystemBC is often dropped via third-party botnets or phishing campaigns, establishing a persistent connection to the attackers' infrastructure.
- Stealthy Tunneling: The malware uses the SOCKS5 protocol to hide Command & Control (C2) traffic, making it difficult for security teams to distinguish between malicious activity and legitimate network noise.
- Rapid Escalation: Once a stable connection is established, The Gentlemen deploy specialized tools for credential harvesting and lateral movement, culminating in the deployment of the ransomware payload on both Windows and Linux systems.
SC Media reports that the discovered C2 server contained detailed logs for over 1,500 victims, suggesting that the group’s "funnel" for potential ransomware targets is significantly larger than previously estimated.
An Expanding Arsenal
While "The Gentlemen" is a relatively new name in the RaaS landscape, their technical maturity is significant. They have been observed utilizing a variety of ransomware strains, including modified versions of Medusa and LockBit, proving an agnostic approach to payload delivery as long as the initial access via SystemBC remains secure.
The CyberSignal Analysis
Signal 01 — The Industrialization of Initial Access
The discovery of 1,570+ victims on a single C2 server proves that ransomware groups have transitioned from "hunting" to "farming" initial access. This systematic approach is a defining characteristic of modern threat actors who prioritize volume over surgical precision.
Signal 02 — The Proxy Paradox
By using SystemBC to tunnel traffic, The Gentlemen effectively hide in plain sight. This technique mirrors the ngate malware's use of relay gates to bypass financial security, proving that the weaponization of legitimate protocols is the preferred method for evading detection.
Signal 03 — The Scale of Modern Extortion
The Gentlemen’s ability to manage 1,500 targets simultaneously highlights a critical shift in RaaS efficiency. For a deeper look at the organizational structure behind these high-volume campaigns, see our guide on how do ransomware gangs operate?.




