North Korean Actors Linked to Massive Supply Chain Attack via Axios NPM Package
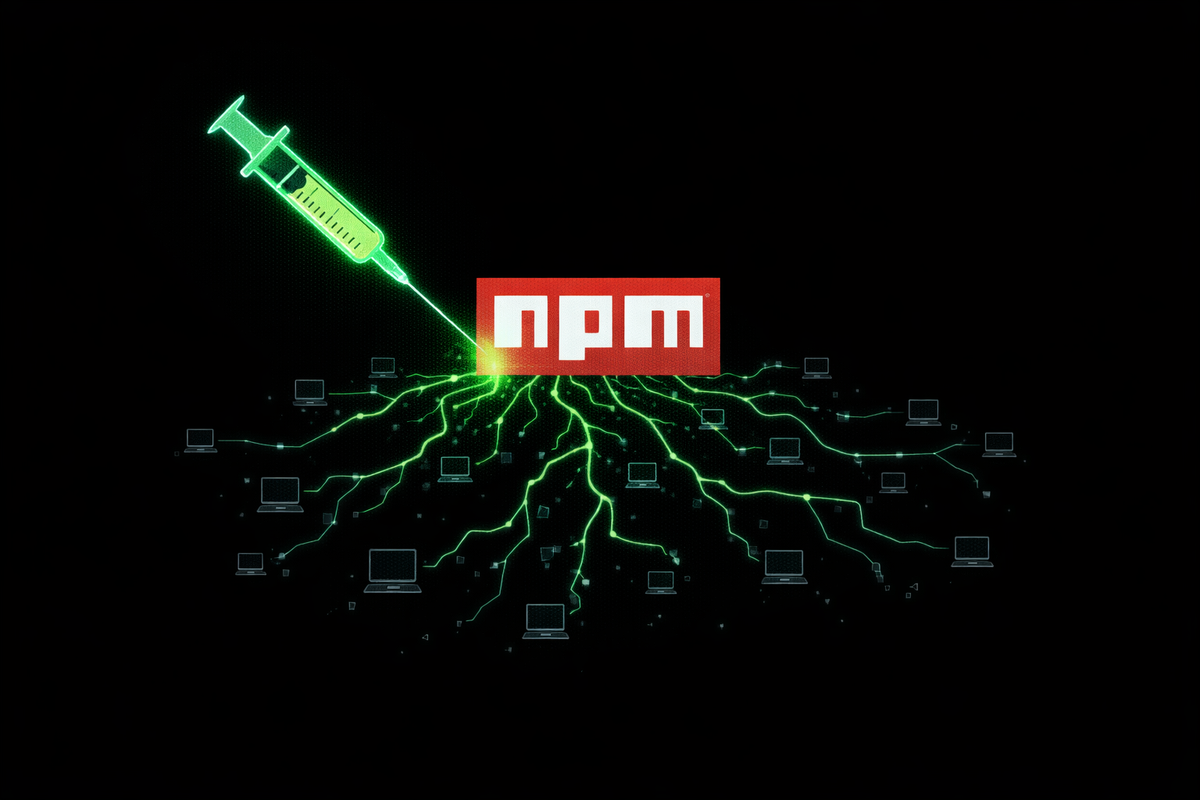
In one of the most consequential supply chain compromises of the year, security researchers have identified a sophisticated campaign to "poison" the widely used Axios software package. The attack, which targeted the npm registry used by millions of web developers, has been attributed by Google’s Threat Analysis Group (TAG) to state-sponsored actors operating out of North Korea.
The Anatomy of the Hijack
Axios is a critical, "largely invisible" piece of software infrastructure — a library used by developers to make HTTP requests. With over 100 million weekly downloads, its reach is vast. The breach occurred when a single maintainer's account was compromised, allowing the attackers to publish a malicious version of the library (v1.8.2) directly to the official registry.
Once installed, the poisoned package deployed a cross-platform Remote Access Trojan (RAT). This malware was designed to identify high-value targets, specifically those in the cryptocurrency, defense, and government sectors, to facilitate data exfiltration and financial theft.
Attribution to North Korea
The technical indicators — including the command-and-control (C2) infrastructure and specific code obfuscation techniques — point toward the Lazarus Group or a related North Korean entity. While the primary goal appears to be the theft of cryptocurrency to fund the regime's weapons programs, the breadth of the access granted by the Axios library provided the attackers with a "god-view" of millions of development environments worldwide.
Immediate Remediation and Impact
The malicious versions were identified and removed within hours of being reported, but the "blast radius" is significant. Any developer or CI/CD pipeline that pulled the compromised version during that window may be infected. Security teams are currently being urged to audit their node_modules and rotate any environment variables or API keys that may have been exposed.
Industry analysts have described the incident as a "wake-up call" for the open-source ecosystem. Despite its critical role in modern web architecture, the Axios project — like many others — relies on a small group of volunteers, making the compromise of a single set of credentials a global security event.
Primary Intel & Reports: The Wall Street Journal, Reuters, Axios, The Hacker News, TechCrunch
The CyberSignal Analysis
The Axios hijack underscores the inherent fragility of the modern software development lifecycle (SDLC).
- Identity as the Perimeter: This was not a failure of the code itself, but a failure of identity security. When a single set of stolen credentials can compromise 100 million systems, Phishing-Resistant MFA for all package maintainers is no longer an option — it is a global necessity.
- The "Invisible" Dependency Risk: Most organizations are unaware they even use Axios, as it is often a "transitive dependency" (a tool used by another tool). CISOs must implement Software Bill of Materials (SBOM) visibility to immediately identify where these libraries exist within their enterprise.
- Operational Takeaway: Organizations should transition to "Pinning" and "Vendoring" dependencies. Rather than automatically pulling the "latest" version from a public registry, teams should pull to a private repository, scan the code, and then approve it for use.