NCSC Issues High-Priority Warning Over State-Linked Messaging App Campaigns

The UK’s National Cyber Security Centre (NCSC), in coordination with Microsoft, has issued an urgent advisory regarding a sophisticated campaign targeting users of encrypted messaging applications. The warning highlights an increase in "highly targeted" social engineering attacks on platforms including WhatsApp and Signal, linked to advanced persistent threat (APT) actors with suspected ties to Russian intelligence.
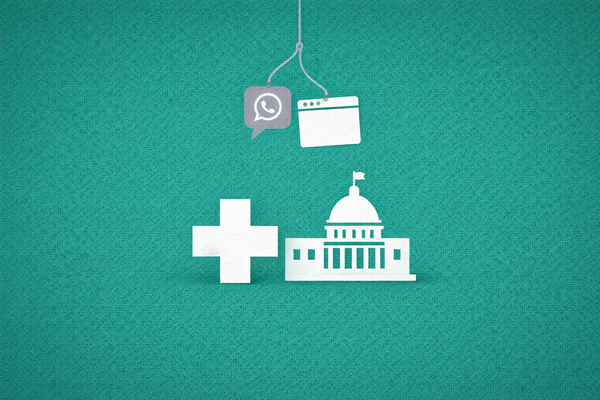
Malicious MSI Packages and Deceptive Lures
The core of the threat involves the distribution of malicious Windows Installer (MSI) packages. According to reports from The Register, attackers are initiating conversations on mobile messaging apps to build rapport before pivoting to a request that requires the victim to download a file on a desktop environment.
These MSI files are often disguised as legitimate software updates, job descriptions, or "secure" document viewers. Once executed, the packages deploy a suite of information-stealing malware designed to exfiltrate browser cookies, saved passwords, and local files. IT Pro reports that the campaign specifically seeks to compromise individuals in government, defense, and non-governmental organizations (NGOs).
Attribution to State-Linked Actors
The UK Defence Journal notes that the NCSC has linked this activity to threat groups historically associated with Russian state interests, specifically those focused on espionage and political intelligence gathering. The advisory suggests that these actors are increasingly utilizing "Bring Your Own Device" (BYOD) vulnerabilities—leveraging the casual nature of mobile messaging to bypass the more stringent security filters found in corporate email systems.
Microsoft’s threat intelligence team has tracked the campaign under several temporary identifiers, noting that the attackers often utilize "spoofed" personas of known colleagues or industry experts to increase the likelihood of a successful file execution.
Primary Intel & Reports: NCSC Official Advisory, The Register, UK Defence Journal, IT Pro
The CyberSignal Analysis
The NCSC warning signals a strategic shift in Threat Intelligence, where the "Trusted Circle" of messaging apps is being weaponized at scale.
- The Mobile-to-Desktop Pivot: This campaign utilizes a sophisticated "Cross-Platform" attack vector. By starting a conversation on a mobile app (where users are often less vigilant) and moving the payload to a desktop (where they have more sensitive data), attackers are effectively bypassing traditional perimeter defenses.
- The Erosion of Encrypted Trust: The primary selling point of apps like Signal and WhatsApp is end-to-end encryption. However, encryption only protects the transit of data. It does not protect against a malicious file sent through that encrypted tunnel. Attackers are exploiting the psychological "halo effect" where users assume a platform is safe because it is encrypted.
- Operational Takeaway: Organizations must enforce Application Whitelisting on corporate endpoints. If a user downloads an unapproved MSI package from a personal WhatsApp Web instance, the system should automatically block its execution. Furthermore, "Security Awareness" training must evolve beyond email phishing to include the nuances of social engineering on instant messaging platforms.