Mustang Panda Expands Espionage to India’s Banking Sector and Korea-Themed Diplomacy
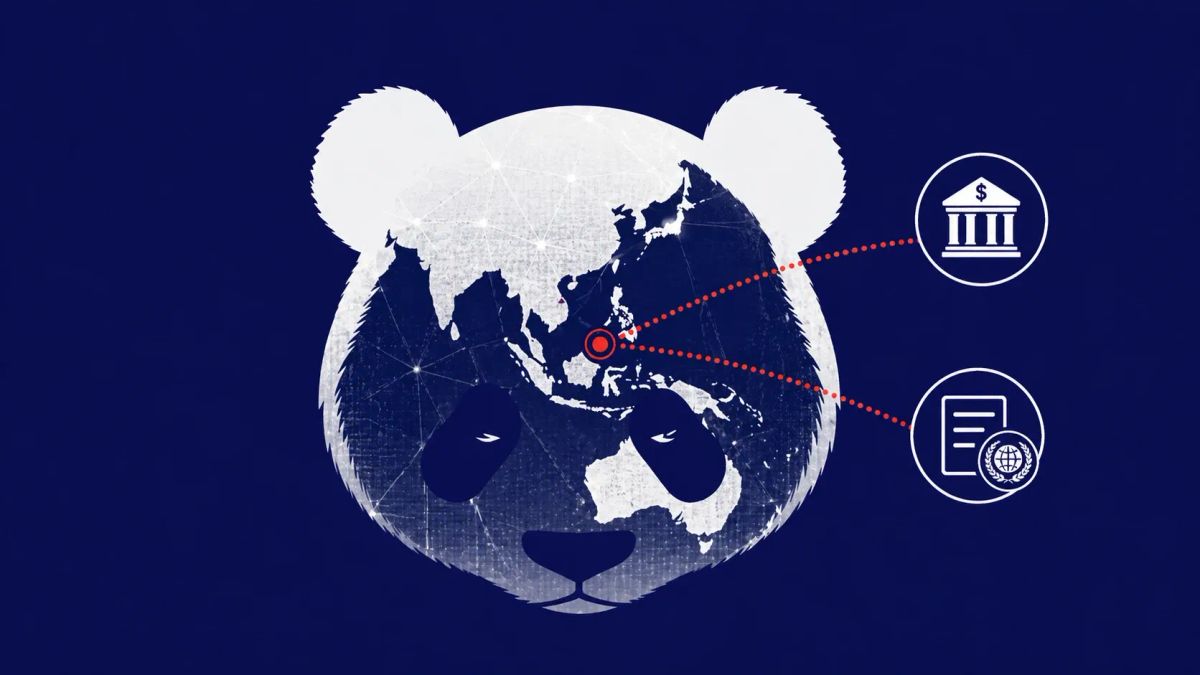
China-linked Mustang Panda (TA416 / RedDelta) has broadened its targeting from predominantly government and policy entities in the West to India’s banking sector and Korean peninsula policy actors. Using an updated LOTUSLITE backdoor delivered via CHM files and DLL sideloading of legitimate Microsoft-signed executables, the campaign marks a strategic shift toward financial infrastructure and regional security lures.
ARLINGTON, VIRGINIA — Mustang Panda, a prolific China-aligned espionage group also known as TA416 or RedDelta, has launched a sophisticated new campaign cluster targeting the Indian financial sector and diplomatic circles involved in Korean Peninsula affairs. Researchers at the Acronis Threat Research Unit (TRU) identified the shift in March 2026, noting that the group is now utilizing an evolved version of its LOTUSLITE backdoor to maintain long-term access to high-value targets.
While Mustang Panda is historically known for targeting NGOs and government bodies in Europe and the U.S., this latest activity reveals a tactical pivot. In India, the group is impersonating HDFC Bank branding to lure banking professionals, while in South Korea, it has adopted the identity of prominent diplomatic figures to infiltrate policy discussions.
Threat Intelligence: Mustang Panda Campaign Profile
The Attack Chain: Legitimate Binaries, Malicious Intent
The infection begins with spear-phishing emails containing Compiled HTML (CHM) files, such as Request_for_Support.chm. When opened, these files execute JavaScript that drops a legitimate, Microsoft-signed executable — Microsoft_DNX.exe — into a local directory alongside a malicious rogue DLL.
The attack leverages DLL Sideloading, where the trusted Microsoft binary is tricked into loading the malicious library instead of the intended system file. This allows the LOTUSLITE backdoor to run silently in memory, bypassing many signature-based endpoint protections.
Once established, LOTUSLITE provides the attackers with:
- Remote Shell Access: Full command-line control of the compromised host.
- File Manipulation: Stealthy exfiltration of sensitive banking data or policy documents.
- Session Management: Persistent access that survives system reboots through registry modifications.
Strategic Implications for the Indo-Pacific
This campaign demonstrates a deepening interest by state-aligned actors in the economic and security postures of India and South Korea. By targeting India’s financial infrastructure, the group gains insights into regional economic stability and regulatory communications. Similarly, the focus on Korean Peninsula policy dialogues — often involving U.S. diplomats — provides a window into high-level strategic planning regarding North Korea and Indo-Pacific alliances.
The CyberSignal Analysis: Strategic Signals
Signal 01 — Geopolitical Expansion of the "Mustang" Beat
This campaign is a significant evolution from the TA416 operations in Europe we covered previously. While the core actor remains the same, the shift from government targets to the private banking sector in India suggests a broadening of mission parameters to include economic espionage alongside traditional political spying.
Signal 02 — The Continued Abuse of Signed Binaries
The use of Microsoft_DNX.exe highlights a persistent gap in modern defenses: the inherent trust placed in signed executables. This follows a pattern of Chinese APT tradecraft where "Living off the Land" (LotL) techniques are used to blend malicious activity with legitimate administrative processes.
Signal 03 — Convergence of Financial and Diplomatic Risk
The dual-pronged nature of this attack — hitting banks and diplomats simultaneously — shows that state actors view financial data as a strategic intelligence asset. Infiltrating a bank is no longer just about theft; it’s about understanding the financial leverage and economic underpinnings of a geopolitical rival.