Microsoft: AiTM Phishing Hit 35,000 Users at 13,000 Orgs in Three Days — Tycoon 2FA Takedown Did Not Kill the Technique
Microsoft Defender Research disclosed a sophisticated AiTM phishing campaign that hit 35,000+ users at 13,000+ organizations across 26 countries in just three days. 92% of targets were in the U.S. The lure was a fake employee disciplinary case. The reverse proxy stole session tokens — bypassing MFA in real time.
The Microsoft Defender Research team published findings on May 4, 2026, on a credential-theft campaign observed between April 14 and 16, 2026 that targeted more than 35,000 users at over 13,000 organizations across 26 countries. The campaign used adversary-in-the-middle (AiTM) phishing infrastructure to harvest Microsoft 365 credentials and session tokens in real time, bypassing non-phishing-resistant multifactor authentication. Per Microsoft, 92 percent of targets were located in the United States, and the heaviest sectoral targeting was healthcare and life sciences (19 percent), financial services (18 percent), professional services (11 percent), and technology (11 percent).
The single most consequential framing: AiTM is back at scale. Two weeks ago, the prevailing narrative — including our own April 19 coverage of the Tycoon 2FA disruption — was that defenders had pushed AiTM operators toward device-code phishing as a more resilient alternative. Microsoft's new disclosure shows AiTM never went away. The infrastructure shifted, the lures evolved, and the same tradecraft now lands on tens of thousands of enterprise users in three days. The Tycoon 2FA takedown reduced volume; it did not change the technique class.
| AiTM "Code of Conduct" Campaign Profile | |
|---|---|
| Detail | Information |
| Disclosed by | Microsoft Defender Research Team / Microsoft Threat Intelligence (May 4, 2026) |
| Activity period | April 14–16, 2026 (three-day waves) |
| Users targeted | More than 35,000 |
| Organizations targeted | More than 13,000 across 26 countries; 92% U.S. |
| Top targeted sectors | Healthcare & life sciences (19%), financial services (18%), professional services (11%), technology & software (11%) |
| Lure theme | Fake employee "code of conduct" / disciplinary case notifications with PDF attachments |
| Sample subject lines | "Internal case log issued under conduct policy", "Reminder: employer opened a non-compliance case log" |
| Sample attacker domains | acceptable-use-policy-calendly[.]de, compliance-protectionoutlook[.]de |
| Anti-analysis tactic | Cloudflare CAPTCHA gating to impede sandbox detonation; second image-selection CAPTCHA after email submission |
| What was stolen | Microsoft 365 credentials and session tokens — bypasses non-phishing-resistant MFA via real-time token interception |
The Lure: Disciplinary Theater
The campaign's defining innovation is its lure design. Phishing emails impersonated internal HR and compliance communications, with display names like "Internal Regulatory COC" and "Workforce Communications." Subject lines invoked workplace conduct review processes — the kind of message most employees treat as personally consequential and time-sensitive. PDF attachments named like Awareness Case Log File – Tuesday 14th, April 2026.pdf and Disciplinary Action – Employee Device Handling Case.pdf reinforced the framing. Microsoft characterized the messages as using "polished, enterprise-style HTML templates with structured layouts and preemptive authenticity statements."
The psychological design matters because it widens the target pool past IT-savvy employees. A fake invoice or shipping notification can be flagged by an alert finance team. A fake disciplinary notice triggers a different kind of cognitive response — anxiety, urgency, the desire to resolve it privately before talking to a manager. Per Microsoft, "because the messages contained concerning accusations and repeated time-bound action prompts, the campaign created a sense of urgency and pressure to act." Help Net Security made the same observation: this lure was designed to alarm.
The CAPTCHA Gate Is the Sandbox-Evasion Layer
Recipients clicking the "Review Case Materials" link in the PDF were redirected to attacker-controlled domains using legitimate-sounding compliance-themed names (acceptable-use-policy-calendly[.]de, compliance-protectionoutlook[.]de). The first thing the user — and any sandbox following the link — encountered was a Cloudflare CAPTCHA, framed as a session-validation step. Microsoft's assessment: the CAPTCHA "likely served as a gating mechanism to impede automated analysis and sandbox detonation."
This is now standard tradecraft. CAPTCHA-gated phishing has evolved "rapidly" across payload types in early 2026, per Microsoft's email-threat telemetry. The gate works because most automated detection infrastructure cannot solve image CAPTCHAs at scale, and most sandboxes do not have the latency budget to retry a session that fails CAPTCHA validation. Once past the CAPTCHA, users were funneled through an intermediate page asking them to authenticate to view "encrypted" documents — and a second image-selection CAPTCHA was deployed after email submission to filter out additional automated traffic.
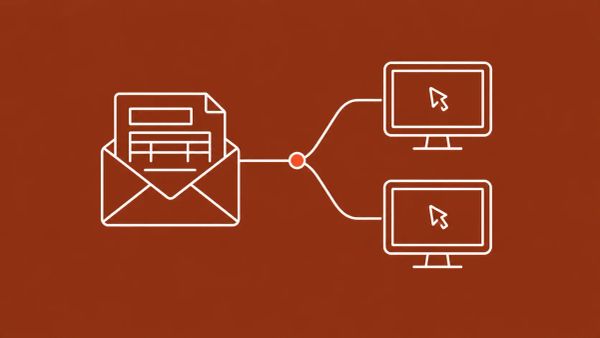
How the Real-Time Token Theft Works
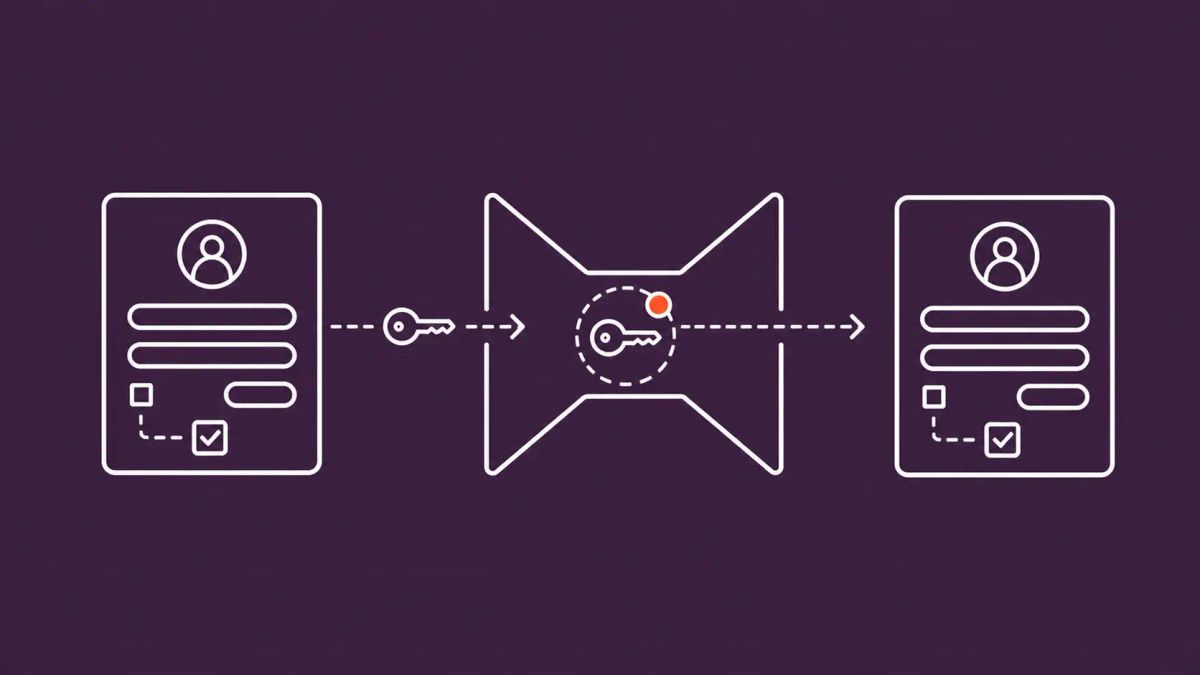
The final stage is what makes this AiTM, not credential phishing. After completing the CAPTCHAs and clicking "Sign in with Microsoft," the user reached what looked like a Microsoft login page. The page was actually an attacker-controlled reverse proxy that silently relayed every credential and MFA factor in real time to the genuine Microsoft sign-in service. Once the user completed authentication — including any MFA prompt — the proxy captured the resulting session token and the attackers used it to access the account, no password or second factor required.
Help Net Security summarized the mechanism precisely: "Access credentials and code-based authentication factors submitted into the fake sign-in page were silently proxied to the real one, allowing the attackers to intercept session tokens after authentication was completed. These captured tokens allowed the attackers to access the victims' account without knowing their password or possessing their second factor."
The implication for defenders is the same one Tycoon 2FA exposed and the same one this campaign reinforces: SMS, app-based push, and TOTP-based MFA do not protect against real-time AiTM proxying. The token is captured after the second factor is submitted. Only phishing-resistant authentication — FIDO2 security keys, Windows Hello for Business, certificate-based authentication — defends against this attack class, because the cryptographic challenge is bound to the legitimate domain and cannot be replayed through a proxy.
Why This Story Updates the Tycoon 2FA Narrative
In April, the cybersecurity press — including our coverage — reported that the international Tycoon 2FA takedown had pushed phishing operators toward device-code phishing. Microsoft's own data confirmed a 15 percent volume decrease in AiTM phishing following the Tycoon 2FA disruption in March 2026. The narrative was that AiTM was being structurally displaced by lower-friction techniques.
What the May 4 disclosure shows is more nuanced. AiTM volume dropped, but the technique did not retire — operators rebuilt infrastructure on alternative hosting providers, refined lures, and ran a 35,000-user campaign in three days. Microsoft's own report on Tycoon 2FA's resilience, published the same day, notes that "Tycoon 2FA moving away from Cloudflare as a hosting service and now hosts most of its domains across a variety of alternative platforms, suggesting the group is attempting to find replacement services that offer comparable anti-analysis protections." The current campaign may or may not be Tycoon-derived — Microsoft did not attribute it to a specific actor — but it lives in the same ecosystem.
For defenders, the lesson is that infrastructure-disruption operations buy time, not safety. The technique class survives the takedown of any individual kit. Our broader phishing coverage tracks how that ecosystem adapts. The structural defense — phishing-resistant authentication — is what eliminates the attack, not the specific kit's removal from the market.
Defender Actions for This Week
- Deploy phishing-resistant MFA for high-privilege and high-risk accounts. FIDO2 security keys (YubiKey, Google Titan, Feitian, etc.) and Windows Hello for Business are the only authentication methods that defeat real-time AiTM token theft. Push-based MFA, SMS codes, and TOTP apps are all bypassed by the technique. Prioritize executives, finance, IT administrators, and any user with broad access to sensitive data.
- Configure Conditional Access policies that bind sessions to managed-device state and require re-authentication for risky sign-ins. Microsoft Entra ID's Conditional Access can detect impossible-travel sign-ins, unfamiliar IP locations, and sign-ins from unmanaged devices — high-fidelity signals that a captured token is being used from attacker infrastructure.
- Enable Continuous Access Evaluation in Microsoft Entra ID. CAE shortens the window during which a stolen token remains valid by re-evaluating session state when risk signals change. Without CAE, a stolen token can persist for the full token lifetime even after defenders detect the compromise.
- Add "workplace disciplinary" and "HR compliance" lures to phishing-simulation catalogs. Most awareness programs train users on invoice fraud, package delivery, and password reset lures. Disciplinary lures exploit a different cognitive pathway — one most users have not been primed to recognize as phishing. Run a simulation; measure the click-through delta.
- Enable Safe Links and Safe Attachments in Microsoft Defender for Office 365 if not already deployed; turn on Zero-hour Auto Purge (ZAP) to retroactively remove malicious messages from inboxes after detection. The current campaign's lures used legitimate email-delivery services and attacker-controlled domains; ZAP retro-removal is the practical fallback when initial filters miss messages.
- Hunt for the indicators Microsoft published. Check email gateway logs for sender display names containing "Internal Regulatory COC" or "Workforce Communications," for PDF attachments matching the published filename patterns, and for sign-in events from the published attacker-domain landing IPs. Even partial hits warrant session-token revocation and password reset for the affected account.
The CyberSignal Analysis
Signal 01 — AiTM is structurally durable; takedowns don't kill the technique class
The strongest signal in this disclosure is the speed at which AiTM rebounded after Tycoon 2FA's March disruption. Six weeks between a coordinated international takedown and a 35,000-user campaign hitting 13,000 organizations is not a recovery — it is the baseline. The reverse-proxy phishing model is too economically valuable and too easily reconstituted on commodity hosting infrastructure to be eliminated by takedowns of individual kits or operators. Defenders who built remediation roadmaps around "Tycoon is gone, AiTM is reduced" need to revise. The technique class persists; the operators rebuild faster than the disruption cycle.
Signal 02 — The lure innovation is more important than the infrastructure innovation
The technical components of this campaign — reverse-proxy phishing, CAPTCHA gating, attacker-controlled domains — are not new. What is new is the lure quality and targeting precision. "Polished, enterprise-style HTML templates" that impersonate internal HR communications signal that operators have moved past invoice fraud and toward content that requires defenders to consider how their own internal communications could be impersonated. The defensive lesson is that user-awareness training built on "suspicious sender / suspicious link" pattern matching is structurally inadequate against well-crafted internal-impersonation lures. The training pivot is toward "verify out-of-band before authenticating" for any unexpected sensitive request, regardless of how legitimate the message looks.
Signal 03 — The U.S. concentration is a defender-prioritization signal, not a comfort
92 percent of the campaign's targets were in the United States. That is not a coincidence — it is a market signal. Operators target where the highest-value session tokens live: U.S. enterprises with broad Microsoft 365 deployments, mature MFA programs that disproportionately use non-phishing-resistant factors, and the largest collection of payroll-fraud and BEC-extraction surfaces. For U.S.-based CISOs, the campaign is not a foreign threat to monitor; it is a present-tense exposure. For non-U.S. organizations, the lower targeting rate is not a defense — it is a delay before the same tradecraft scales internationally. Microsoft's data shows AiTM operators iterate on lures and infrastructure faster than most enterprise security programs iterate on phishing-resistant MFA rollouts. That gap is the real risk window.