Mazda Confirms Data Breach Exposing Employee and Business Partner Information
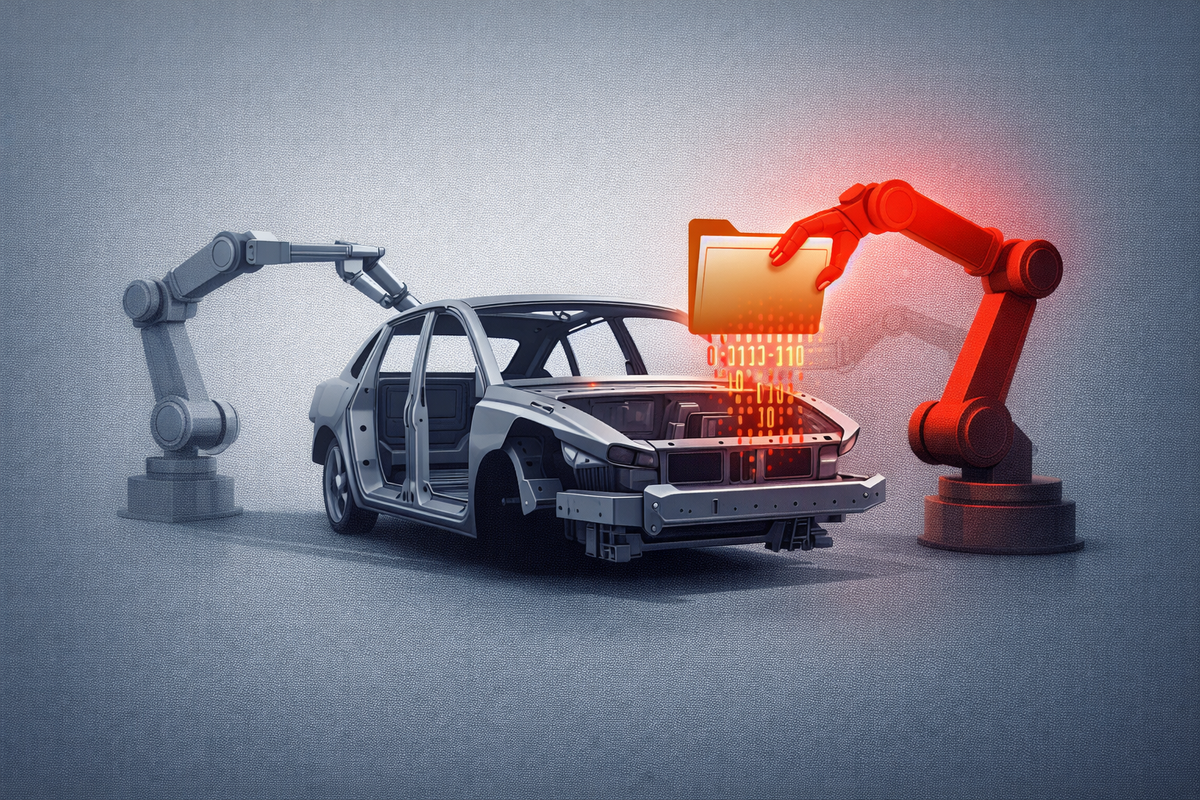
Mazda Motor Corporation has confirmed a cybersecurity incident that resulted in unauthorized access to its internal IT systems, leading to the exposure of personal information belonging to employees and business partners. The Japanese automaker disclosed that the breach was the result of a vulnerability in a warehouse management system, though it maintains that customer data appears unaffected at this stage.
Unauthorized Access and System Vulnerabilities
The breach was detected following suspicious activity within Mazda’s internal network. According to reporting from TechRadar, the intrusion leveraged a previously unidentified vulnerability in a server used for logistics and warehouse operations.
Forensic investigations revealed that threat actors gained access to files containing names, contact details, and professional identification for a significant number of staff and external contractors. Mazda has not publicly identified the specific threat actor behind the campaign, but SecurityWeek notes that the method of entry is consistent with opportunistic "initial access" brokers who target supply chain and logistics software.
Limited Data Exposure and Response
In official statements, Mazda emphasized that the incident was localized to specific internal business systems. The company stated that no evidence has been found suggesting that consumer-facing databases — such as those containing vehicle identification numbers (VINs) or owner financial records — were compromised.
Mazda has since patched the identified vulnerability and implemented enhanced monitoring protocols across its global IT infrastructure. The automaker is currently in the process of notifying the impacted individuals and has reported the matter to relevant data protection authorities in Japan and international jurisdictions where partners were affected.
Automotive Supply Chain as a Growing Target
The incident highlights the increasing pressure on the automotive sector’s digital ecosystem. As manufacturers integrate more sophisticated warehouse and logistics software, the "attack surface" for the global supply chain expands. Analysts at SC Media suggest that the focus on employee and partner data may be a precursor to social engineering attacks, where stolen professional credentials are used to gain deeper access into corporate finance or engineering networks.
Primary Intel & Reports: BleepingComputer, TechRadar, SecurityWeek, SC Media
The CyberSignal Analysis
The Mazda breach serves as a textbook example of Lateral Movement Risk and the vulnerability of non-consumer systems.
- Warehouse Systems as a Weak Link: Often, security teams prioritize customer databases (the "crown jewels") while leaving internal logistics or warehouse systems under-protected. For CISOs, this incident is a reminder that any server with network connectivity is a potential beachhead. If the warehouse system can "talk" to the corporate directory, the entire organization is at risk.
- The "Partner Data" Payload: Stolen business partner information is a high-value asset for BEC (Business Email Compromise) attacks. When an attacker knows exactly who a company’s contractors are, they can craft highly convincing fraudulent invoices. The CyberSignal recommends that all procurement teams implement secondary, out-of-band verification for any changes to partner payment details following this report.
- Operational Takeaway: Organizations must adopt Micro-segmentation. Administrative logistics systems should be isolated from corporate identity providers. If a vulnerability is found in a warehouse server, the "blast radius" should be contained to that specific function, preventing access to the wider employee database.