Kraken Defies Extortion Attempt Following "Rogue Employee" Data Leak
The global crypto exchange confirms it is the target of a blackmail plot involving internal data, but maintains that core trading systems and client funds remain isolated and secure.
SAN FRANCISCO, CA — Kraken, one of the world’s largest cryptocurrency exchanges, is currently navigating an active extortion campaign after a former employee allegedly misappropriated internal data. Despite threats from a criminal group to leak the information, Kraken leadership has taken a hardline stance, refusing to pay the ransom and asserting that no client funds were ever at risk.
The incident, first detailed by Kraken Chief Security Officer Nick Percoco, underscores a growing trend in the fintech sector: the weaponization of "insider access" to bypass sophisticated perimeter defenses. While the exchange denies that a "breach" of its production systems occurred, it acknowledges that a rogue individual with authorized access to internal tools successfully extracted non-financial data before their credentials were revoked.
Who Was Affected
The Mechanics of the Extortion
The criminal group currently blackmailing the exchange claims to possess a cache of sensitive information. While the full extent of the data remains under investigation, early reports suggest it includes internal communications, system screenshots, and potentially limited customer PII (Personally Identifiable Information).
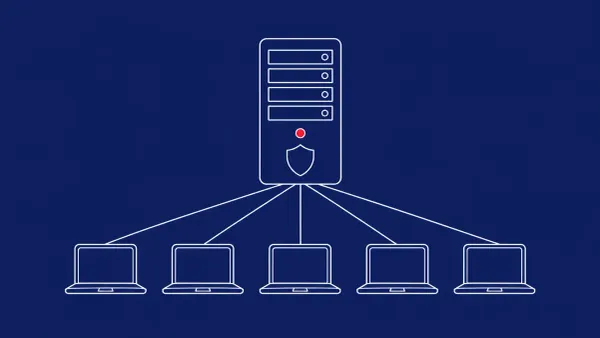
Crucially, Kraken’s security architecture — which utilizes strict air-gapping for cold storage and multi-party computation (MPC) for hot wallets — appears to have functioned as intended.
"Our systems are designed with the assumption that internal accounts can be compromised," Percoco stated. "Because of our defense-in-depth strategy, the rogue employee was never in a position to access the keys, wallets, or trading engines that power the exchange."
The "No Ransom" Policy
Kraken’s refusal to negotiate with the extortionists is a significant move in a landscape where many fintech firms quietly pay "protection money" to avoid reputational damage. By going public, Kraken is signaling to threat actors that the ROI (Return on Investment) for insider-based extortion on their platform is zero.
The exchange is currently working with federal law enforcement and digital forensics firms to track the movement of the stolen data and identify the external criminal group working with the former employee.
The CyberSignal Analysis
Signal 01 — The Resurgence of the Insider Threat
As we’ve discussed in ourFintech Security vertical, the most formidable "zero-day" is often a disgruntled employee. Kraken’s experience is a signal that even the most robust cryptographic defenses can be undermined by administrative access. For the broader fintech ecosystem, this highlights the need forUser and Entity Behavior Analytics (UEBA)to detect mass data exports in real-time.
Signal 02 — Reputational vs. Financial Risk
There is a clear distinction in this incident between financial loss and reputational loss. While the "signal" from Kraken is one of financial stability, the leak of internal documentation can provide future attackers with a blueprint of the company’s internal culture and software stack. This "secondary intelligence" is often sold on dark web forums to help facilitate more sophisticated social engineering attacks against employees later.