Cybersecurity Threats: Understanding Modern Cyber Risks and How to Defend Against Them
Cybersecurity threats continue to evolve as organizations expand digital infrastructure, cloud environments, and connected devices across their operations. Cybersecurity threats are acts performed by individuals with harmful intent, whose goal is to steal data, cause damage to or disrupt computing systems. Security teams today must defend computer networks, critical systems, and customer data against increasingly sophisticated threat actors who exploit vulnerabilities, manipulate users through social engineering, and bypass traditional security measures.
The stakes are enormous. The global cost of cybercrime is projected to rise from $9.22 trillion in 2024 to $13.82 trillion by 2028. The financial impact of cybercrime is serious, exceeding the yearly damage caused by natural disasters and competing with the profits of the illegal drug trade. As organizations rely more heavily on digital infrastructure, understanding modern cyber threats and implementing strong security management practices has become essential to maintaining business operations and protecting sensitive information.
Introduction to Cyber Threats

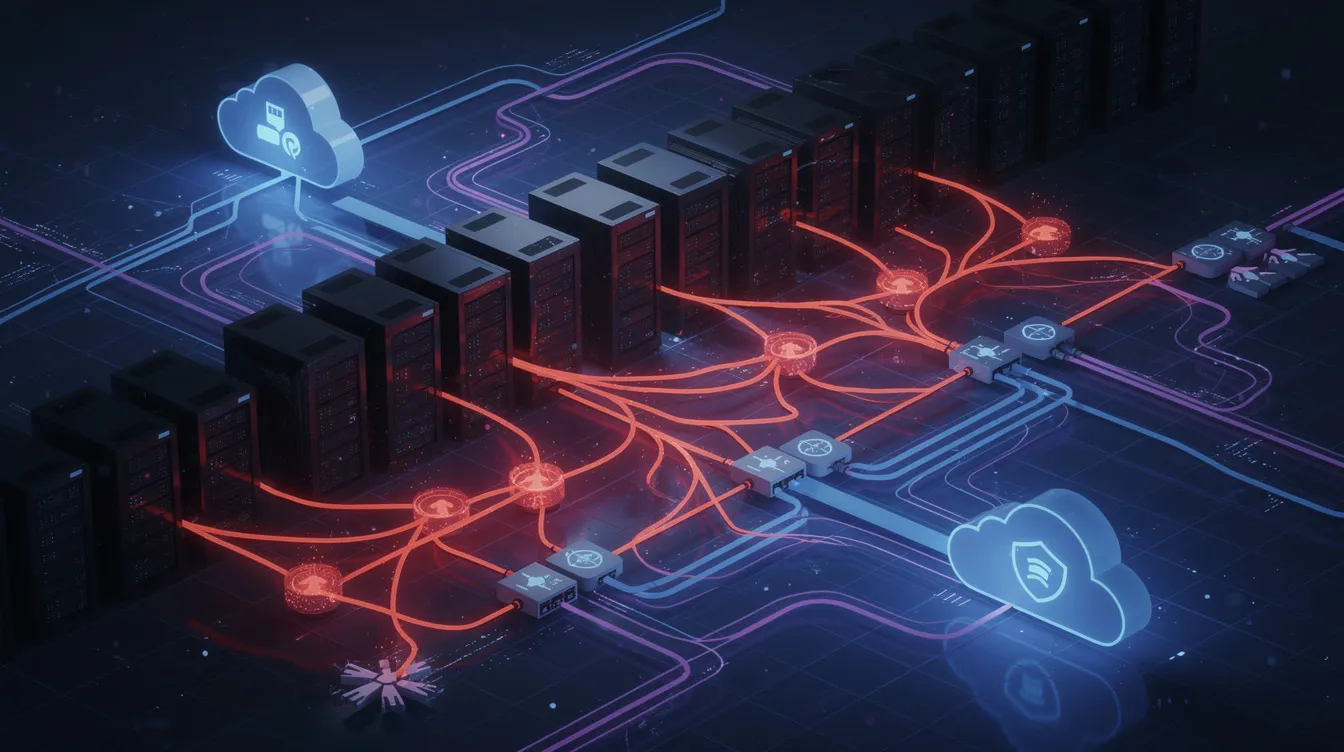
Today's cyber threat landscape represents a sophisticated ecosystem of deliberate attacks where adversaries — ranging from lone hackers to state-sponsored groups — systematically target computer systems, networks, and valuable data assets. These modern threats have evolved far beyond simple viruses, now encompassing advanced malicious software that can silently infiltrate enterprise environments, sophisticated social engineering campaigns designed to exploit human psychology and trick employees into surrendering credentials, and dangerous insider threats where trusted personnel leverage their legitimate access for malicious purposes. Perhaps most concerning for security teams is the surge in supply chain compromises, where attackers strategically infiltrate trusted third-party vendors and partners as a stepping stone into target organizations' critical infrastructure. The motivation driving these threat actors remains consistent: data theft, operational disruption, and unauthorized access to high-value systems that can yield significant financial or strategic advantage.
For cybersecurity professionals defending against this constantly shifting threat environment, success demands continuous vigilance, robust monitoring capabilities that can detect subtle indicators of compromise, and proactive security measures that anticipate rather than simply react to emerging attack vectors.
Cybersecurity Threats
Cybersecurity threats now target every layer of the modern enterprise, from operating systems and network servers to employee devices and cloud infrastructure. The most common cybersecurity threats today include ransomware, sophisticated phishing, credential theft, and supply chain attacks. Threat actors continuously develop new attack methods designed to gain unauthorized access to computer systems and intercept data moving across corporate networks.
Malware is the most common type of cyberattack and includes viruses, worms, trojans, spyware, and ransomware. Malware is an abbreviation of "malicious software", which includes viruses, worms, trojans, spyware, and ransomware, and is the most common type of cyberattack. These forms of malicious software often deliver additional malware after initial compromise, allowing attackers to move laterally through a target's network and access sensitive data.
Cybersecurity threats have shifted toward highly automated operations that target identity systems. In 2026, identity has replaced the network perimeter as the primary attack surface in cybersecurity, with 75% of breaches involving compromised credentials. Attackers frequently steal login credentials through phishing, brute force attacks, or credential theft campaigns before using legitimate access to escalate privileges within a victim's computer system.
AI-powered cyber-attacks are emerging as a significant challenge in the cybersecurity arena. AI-powered social engineering attacks use generative AI to create hyper-personalized phishing emails and realistic deepfake impersonations. Deepfake technology is quickly becoming a powerful tool for cybercriminals seeking to impersonate executives, manipulate financial transactions, or compromise business communications.
Cyber Threat Landscape
Today's cybersecurity battlefield shifts constantly, as threat actors deploy increasingly sophisticated techniques that challenge even well-prepared organizations. Modern cybercriminals have expanded far beyond basic attacks, leveraging targeted spear phishing campaigns and relentless brute force operations alongside devastating payloads like ransomware and next-generation malware designed to evade conventional defenses. The insider threat problem persists as a critical vulnerability — whether stemming from malicious employees or simple human error, these incidents continue driving major data breaches across industries. Meanwhile, supply chain compromises have emerged as attackers' preferred infiltration vector, allowing them to poison trusted software distributions and hardware components to establish persistent, undetected access to high-value targets. Security professionals recognize that staying ahead requires implementing layered defense architectures, delivering comprehensive security awareness programs across all organizational levels, and establishing around-the-clock monitoring capabilities for networks and critical infrastructure. Organizations that embrace this multifaceted defensive strategy position themselves to identify and neutralize emerging threats before attackers can compromise sensitive data or disrupt essential business functions.
Cyber Threats
Cyber threats refer to the broad spectrum of malicious activities that attempt to exploit vulnerabilities in computer networks, operating systems, and connected devices. Cybercriminals commit cybercrimes mostly for financial gain, including ransomware attacks and phishing scams. These attacks often target intellectual property, financial records, or customer data that can be monetized on the dark web.
Phishing is the best-known and most pervasive form of social engineering, using fraudulent emails to trick people into sharing personal data. Phishing is a type of social engineering attack that uses fraudulent communications to trick individuals into revealing sensitive information such as login credentials or payment details. Attackers may also deploy spear phishing, which targets specific employees through personalized messages that appear legitimate.
Business email compromise attacks have become particularly dangerous for organizations. Business Email Compromise (BEC) is a highly targeted form of phishing where attackers mimic executives to initiate fraudulent transfers. Business email compromise schemes have evolved to convincingly mimic internal communications, often combining social engineering with stolen credentials to manipulate employees through email, phone calls, or text messages.
Identity theft also plays a central role in modern cyber threats. Identity theft includes stolen Social Security numbers and passwords auctioned on the dark web. Attackers frequently create fake websites designed to harvest credentials or distribute malicious links that infect a user's device with malicious code.
Data Breach
A data breach occurs when unauthorized individuals gain access to sensitive information stored within an organization's systems. Data breaches frequently involve customer data, intellectual property, or confidential corporate records that attackers can exploit for financial gain.
Insider threats are an often overlooked cause of data breaches. Insider threats arise from individuals within an organization who misuse their access to systems and data, either maliciously or through negligence. Insider threats can be categorized into unintentional mistakes and deliberate sabotage.
Many insider threats occur due to human error, such as unwittingly installing malware or losing a company-issued device. Malicious insiders may abuse access privileges for monetary gain or out of spite or revenge. Insider breaches can be just as costly as external attacks, averaging $4.99 million per incident.
External attackers also use a variety of tactics to steal data. Ransomware attacks remain among the most financially damaging cyber incidents. The average cost of an extortion or ransomware incident is around $5 million. In 2023, ransomware incidents peaked with 1,512 incidents and $1.1 billion in payments, marking a 77% jump from 2022.
Many ransomware operations now use triple extortion tactics. Triple extortion used in ransomware attacks includes encryption of data, threat of data leakage, and attacking public services. These strategies increase pressure on victims to pay ransom demands quickly.
Distributed Denial of Service
Distributed Denial-of-Service attacks represent one of the most disruptive cyber attack methods affecting organizations today. A Denial-of-Service (DoS) attack overwhelms a target system with excessive traffic, making it unavailable to legitimate users. A Denial-of-Service attack overloads the target system with a large volume of traffic, hindering the ability of the system to function normally.
Distributed Denial-of-Service (DDoS) attacks use a network of internet-connected, malware-infected devices to overwhelm a target system. These devices often include compromised IoT devices, servers, or personal computers that form botnets capable of generating massive traffic floods.
DDoS attacks are becoming more sophisticated, overwhelming networks with excessive traffic to deplete resources. These attacks can target critical infrastructure, financial institutions, and government systems, disrupting services and damaging public trust.
Cyber Security
Effective cyber security strategies rely on strong security controls, proactive threat intelligence, and continuous monitoring of network traffic across enterprise environments. Organizations must protect computer systems, cloud environments, and connected devices through layered defense strategies that reduce risk and prevent attackers from gaining access.
Zero Trust Architecture requires continuous authentication for every access request. Identity and access management systems play a crucial role in ensuring that only authorized users can interact with sensitive systems. Implementing multi-factor authentication can significantly reduce the risk of successful breaches originating from social engineering tactics.
Organizations must also deploy security awareness training to reduce the impact of social engineering attacks. Training employees to recognize and respond to threats is essential, as human error is a significant factor in many breaches. Employee training is essential for identifying suspicious emails, links, and phishing attempts.
Emerging Threats
The cyber threat landscape continues to evolve rapidly as attackers adopt new technologies and attack methods. Emerging threats increasingly focus on exploiting identity systems, software supply chains, and connected devices.
Supply chain attacks are on the rise, targeting trusted relationships to breach multiple entities in a single attack. Supply chain attacks exploit the interconnected systems of organizations, leveraging trusted relationships to breach multiple entities in a single attack. Supply chain attacks are a new type of threat to software developers and vendors, aiming to infect legitimate applications and distribute malware.
Zero-day exploits also represent a growing threat. Zero-day exploits take advantage of unpatched security flaws in software, hardware, or firmware. Real-time patching is crucial as the time from the publication of a vulnerability to exploitation has decreased significantly.
Internet of Things attacks continue to grow as well. Internet of Things attacks exploit vulnerabilities in connected devices to take over the device or steal data. These attacks can target smart devices, industrial control systems, or corporate infrastructure.
Cryptojacking is another stealthy cyber threat. Cryptojacking is a stealthy threat that hijacks computer resources to mine cryptocurrency without the victim's knowledge.
Injection Attacks
Polymorphic malware further complicates detection. Polymorphic malware can modify its own code in real-time to evade signature-based detection systems. This makes traditional security tools less effective and requires organizations to rely on behavioral threat detection and advanced monitoring tools.
However, existing tools are often insufficient for comprehensive security, as they may not detect advanced threats or sophisticated attack techniques. Human expertise is essential to complement automated systems and identify breaches that existing tools might miss.
Cyber Attacks

Cyber attacks come in many forms and often involve multiple techniques working together to compromise an organization.
Common cyber attacks include:
- Ransomware
- Phishing
- Malware attacks
- Brute force password attacks
- Man-in-the-middle attacks
A Man-in-the-Middle attack involves intercepting communication between two parties to steal data or manipulate the communication. A Man-in-the-Middle attack involves intercepting the communication between two endpoints, such as a user and an application.
Attackers frequently combine multiple attack methods to maximize their chances of success. For example, a phishing campaign may steal login credentials, allowing attackers to gain access to a corporate network before deploying ransomware or data exfiltration tools.
The escalating threat of cybercrime endangers innovation, business investment, and economic stability. Global cybercrime costs are projected to reach $10.5 trillion annually by 2026. Organizations must therefore treat cybersecurity as a critical component of operational resilience and risk management.
Distributed Denial
Distributed denial attacks target the availability of systems rather than the confidentiality of data. By overwhelming a network server or application with excessive traffic, attackers can prevent legitimate users from accessing services.
These attacks may target financial platforms, online services, or critical infrastructure systems where downtime can cause severe economic damage. Attackers often launch distributed denial attacks using botnets composed of compromised connected devices.
Denial of Service Attack
A denial of service attack can cripple an organization's digital infrastructure by exhausting system resources. These attacks are frequently used as distraction techniques during larger cyber attacks, allowing attackers to exploit vulnerabilities elsewhere within the network.
Organizations must deploy network monitoring and traffic filtering tools capable of identifying abnormal traffic patterns and mitigating attacks before they impact business operations.
DDoS Attacks
DDoS attacks represent a large-scale version of denial of service attacks that use thousands or even millions of compromised devices to generate traffic floods. These attacks often rely on botnets built from malware-infected devices distributed across the internet.
Security teams must use threat intelligence, traffic analysis tools, and cloud-based mitigation services to defend against modern DDoS campaigns. Continuous monitoring of network traffic can help identify attack patterns early and trigger incident response plans before services are disrupted.
Cybersecurity Framework and Risk Management
Building an effective cybersecurity framework isn't just a technical necessity — it's become the cornerstone of organizational survival in today's threat landscape. The process starts with comprehensive risk assessments that pinpoint vulnerabilities across your infrastructure, allowing security teams to focus resources on protecting the crown jewels: sensitive data and mission-critical systems. Organizations are increasingly deploying layered security controls, from multi-factor authentication and strict access management to robust encryption protocols, creating multiple barriers against unauthorized intrusion and malicious activity.
When breaches inevitably occur, well-crafted incident response plans separate the survivors from the casualties, enabling rapid containment and minimizing business disruption. Security audits and penetration testing serve as reality checks, exposing weaknesses that attackers could exploit before they actually do. Companies that embrace this structured approach to cybersecurity frameworks, combined with proactive risk management, dramatically improve their defensive posture and protect what matters most — their reputation, operations, and bottom line.
Cybersecurity Awareness and Training
The cybersecurity landscape continues to evolve rapidly, yet one fundamental truth remains constant: human-centered security awareness represents the cornerstone of effective organizational defense strategies. Security professionals across industries recognize that employees function as the critical first barrier against increasingly sophisticated cyber threats. This reality has prompted organizations to prioritize comprehensive education initiatives covering contemporary attack vectors, particularly phishing campaigns, social engineering tactics, and ransomware operations that have dominated recent threat intelligence reports.
Importance of Employee Training
Modern security teams are implementing systematic awareness programs designed to enhance staff capabilities in threat recognition, incident reporting protocols, robust authentication practices, and multi-factor authentication deployment.
Key Training Topics
Key topics for employee cybersecurity training include:
- Recognizing phishing emails and social engineering tactics
- Understanding ransomware and how to respond
- Incident reporting protocols
- Robust authentication practices
- Multi-factor authentication deployment
Continuous Improvement
The strategic cultivation of security-minded organizational cultures has proven instrumental in minimizing human-factor vulnerabilities — consistently identified by researchers as primary contributors to successful cyber incidents. Continuous training methodologies ensure workforce readiness against emerging threat patterns while building institutional capacity for appropriate incident response, ultimately reinforcing enterprise-wide security frameworks that adapt to the current threat environment.
Cybersecurity Policy and Procedures
Strong cybersecurity policies and well-defined procedures remain the cornerstone of effective defense against today's evolving threat landscape. Organizations that get this right understand their security policies must do more than check compliance boxes — they need to establish clear incident response frameworks, robust security controls, and streamlined access management that actually work under pressure.
Policy Development
The most effective approaches weave in practical guidelines for employee conduct, from acceptable use standards to straightforward reporting mechanisms for suspicious activity, creating a security-aware culture where accountability becomes second nature.
Incident Response Frameworks
What separates successful organizations from those making headlines for breaches is their commitment to treating these policies as living documents, regularly updating them as attack vectors shift and new vulnerabilities emerge.
Employee Conduct Guidelines
When properly implemented and consistently enforced, comprehensive cybersecurity policies transform reactive security teams into proactive defenders, enabling organizations to stay ahead of threats while protecting the critical systems and sensitive data that keep their operations running.
Cybersecurity Best Practices
Strong cybersecurity best practices help organizations reduce the risk of cyber incidents and protect critical systems from compromise.
Organizations should adopt a layered security approach that includes:
- Regular software updates
- Comprehensive end-user education
- Advanced threat detection systems
- Rigorous access controls
Other best practices include:
- Conducting risk assessments that identify what matters most for effective threat management
- Setting up threat intelligence to stay ahead of attackers and inform risk assessments and incident response plans
- Monitoring, reviewing, and improving security measures continuously to adapt to evolving threats
- Implementing multi-factor authentication
- Deploying endpoint protection systems
- Maintaining strong access management policies to reduce the likelihood of successful attacks
- Implementing comprehensive cybersecurity training programs to mitigate insider threats and strengthen security awareness among employees
- Training employees to recognize suspicious emails, malicious links, and phishing attempts to reduce the risk of social engineering attacks
ISO 27001 provides a systematic approach to managing information security risks and helps businesses become risk-aware and proactively spot security weaknesses.
Employing a comprehensive cybersecurity strategy can help organizations prevent or quickly remediate cyberattacks and minimize their impact on business operations.
Individuals should:
- Avoid clicking on suspicious links
- Use complex, unique passwords for every account
Combined with security awareness training and modern identity systems, these practices strengthen an organization's overall security posture and protect sensitive information from threat actors seeking unauthorized access.
FAQ
What are cybersecurity threats?
Cybersecurity threats are malicious activities intended to damage systems, steal sensitive data, disrupt services, or gain unauthorized access to computer networks and digital infrastructure.
What are the most common cyber threats today?
The most common cyber threats today include:
- Ransomware attacks
- Phishing campaigns
- Credential theft
- Supply chain attacks
- Malware infections
- Distributed denial-of-service attacks
How do ransomware attacks work?
Ransomware attacks encrypt files or systems and demand payment in exchange for a decryption key. Many attackers now use triple extortion techniques that combine encryption, data theft, and public exposure threats.
What is a distributed denial-of-service attack?
A distributed denial-of-service attack uses thousands of compromised devices to flood a target system with traffic, preventing legitimate users from accessing services.
How can organizations reduce cybersecurity risks?
Organizations can reduce cybersecurity risks by:
- Implementing multi-factor authentication
- Deploying threat detection systems
- Conducting regular risk assessments
- Providing employee training
- Maintaining strong incident response plans
Why are identity systems a major cybersecurity risk today?
Identity systems are a primary attack surface because stolen credentials allow attackers to bypass traditional security controls and gain legitimate access to networks and sensitive systems.




