Blacklisted and Breached: Sanctioned Grinex Exchange Shuts Down Following $13.7M Heist

The Russia-linked exchange halts all operations after a high-precision attack empties its hot wallets, with leadership blaming Western intelligence services for the collapse.
MOSCOW, RUSSIA — Grinex, a prominent cryptocurrency exchange previously blacklisted by international regulators for its alleged role in money laundering and sanctions evasion, has officially suspended all trading operations. The collapse follows a devastating cyberattack that siphoned $13.74 million in digital assets from the platform’s hot wallets in a matter of minutes.
The incident has quickly evolved from a standard financial breach into a geopolitical flashpoint. In a statement released shortly after the outage, Grinex leadership attributed the hack to "foreign intelligence services," claiming the breach was a state-sponsored act of economic sabotage rather than a criminal theft.
Grinex Breach Overview
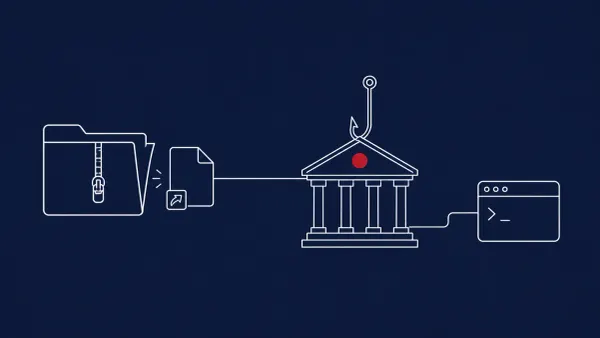
The Anatomy of the Drain
Blockchain analytics firms, including Elliptic and Chainalysis, tracked the movement of funds across multiple chains starting late on April 16. The attack was characterized by its speed and surgical precision, suggesting the attackers had deep, persistent access to the exchange’s private key infrastructure.
Key technical details reported by The Hacker News and CoinDesk include:
- Multi-Asset Theft: The attackers targeted a variety of assets, primarily focused on USDT, Ethereum (ETH), and Bitcoin (BTC).
- Instant Dispersal: Stolen funds were immediately moved through "peeling chains" and decentralized mixers to obscure the trail, a hallmark of sophisticated nation-state or advanced persistent threat (APT) groups.
- Internal Compromise: Preliminary forensics suggest the breach may have originated from a compromised administrative account or a sophisticated supply chain attack targeting the exchange’s internal wallet management software.
Sanctions and the "No-Rescue" Zone
Grinex was already operating under a cloud of legal pressure. Having been sanctioned for providing a financial lifeline to restricted entities, the exchange was largely isolated from the global banking system.
"The irony of the Grinex hack is that because they are sanctioned, they have zero recourse," noted a researcher at Elliptic. "They cannot call upon international law enforcement, and most major centralized exchanges will automatically freeze any funds linked to their addresses, whether they were stolen or not."
The CyberSignal Analysis
Signal 01 — The Weaponization of Hacking in Geopolitics
The Grinex hack represents a shift in the "Signal" of cyber warfare. Whether the hack was actually state-sponsored or simply a criminal group taking advantage of a "lawless" target, the result is the same: the total neutralization of a sanctioned financial hub. For B2B firms operating in high-risk jurisdictions, the "Signal" is that being "off-grid" or sanctioned doesn't protect you from hackers — it makes you a "free-fire" target with no legal shield.
Signal 02 — Digital Identity is the Perimeter
Just as we saw in the DraftKings account takeover cases, the Grinex breach likely boiled down to a failure of digital identity governance. If an intelligence agency or APT group can compromise a single high-level credential, the entire "Air-Gap" or blockchain security model becomes irrelevant. Identity isn't just a part of the network — it is the network.