Apple Patches iOS Bug FBI Exploited to Recover Deleted Signal Messages (CVE-2026-28950)
iOS 18.7.8 fixes a notification retention flaw after the FBI used Cellebrite to extract cached Signal message previews from deleted iPhone apps in a high-profile Texas criminal case.
CUPERTINO, CA — Apple has released a critical out-of-band security update — iOS 18.7.8 and iPadOS 26.4.2 — to patch a vulnerability (CVE-2026-28950) that allowed law enforcement to recover deleted Signal messages. The patch addresses a notification retention bug that the FBI successfully exploited in April 2026 during the investigation into a July 2025 Texas detention center attack.
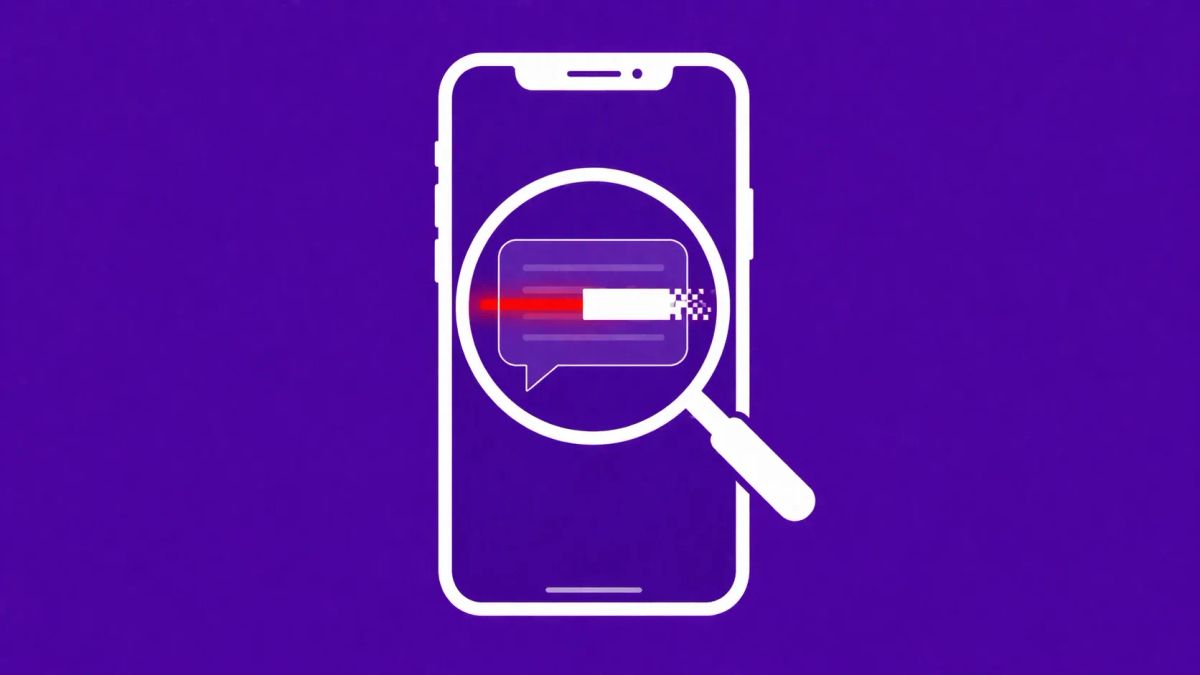
According to Apple’s official security documentation, the issue involved an "unexpected retention" of notifications marked for deletion. In practice, this allowed the FBI to use forensic tools, specifically Cellebrite Premium, to extract cached message previews from a local notification database — even after the Signal app had been uninstalled or messages were set to disappear.
The exploit gained public attention during the trial of Lynette Sharp, where FBI Agent Clark Wiethorn testified that the agency recovered incoming Signal message previews cached on the device for up to 30 days. This revelation prompted intense pressure from Signal CEO Meredith Whittaker, who argued that "notifications for deleted messages shouldn’t remain in any OS notification database."
Bypassing Encryption via OS Caching
The significance of CVE-2026-28950 lies in how it bypassed Signal’s end-to-end encryption (E2EE) without actually breaking the encryption protocol itself. While Signal’s app database remains secure, the iOS notification system — a separate OS-level process — was failing to purge the previews displayed on the lock screen.
This oversight created a forensic "paper trail" that survived even if the user deleted the message or the entire application. The FBI’s ability to recover this data highlights a growing tension between OS-level convenience and granular notification privacy and security. It serves as a reminder that the security of a communication app is only as strong as the operating system it resides upon.
Affected Devices & Remediation
Apple has confirmed that the bug affected a wide range of hardware, including:
- iPhone 11 and later
- iPad Pro (all models), iPad Air (3rd gen+), iPad (6th gen+), and iPad mini (5th gen+)
The fix, implemented in iOS 18.7.8, utilizes "improved data redaction" to ensure that once a notification is marked for deletion by an app or a user, it is wiped from the internal database. This patch follows a week of intense scrutiny after 404 Media first exposed the FBI’s technique.
The CyberSignal Analysis
Signal 01 — The "Last Mile" of Privacy
This incident proves that encryption is not a binary state. You can have mathematically perfect E2EE and still lose your privacy to an OS-level "caching leak." For defenders and privacy-conscious users, the lesson is that metadata and notification previews are often the weakest links in the chain. This evolution in the Apple-FBI encryption dispute shows that law enforcement is shifting focus away from "backdoors" and toward "side-doors" found in OS artifacts.
Signal 02 — The Speed of Disclosure
Apple’s decision to issue an out-of-band security update — rather than waiting for a major point release — signals how seriously the company took the public advocacy from Signal and the reporting by 404 Media. In a climate where Russia, Iran, and China are increasingly leveraging forensic exploits, Apple cannot afford to leave "known-exploited" bugs unpatched. For more on high-impact flaws, visit our vulnerability disclosure archive.