What Is Lateral Movement in Cyberattacks?
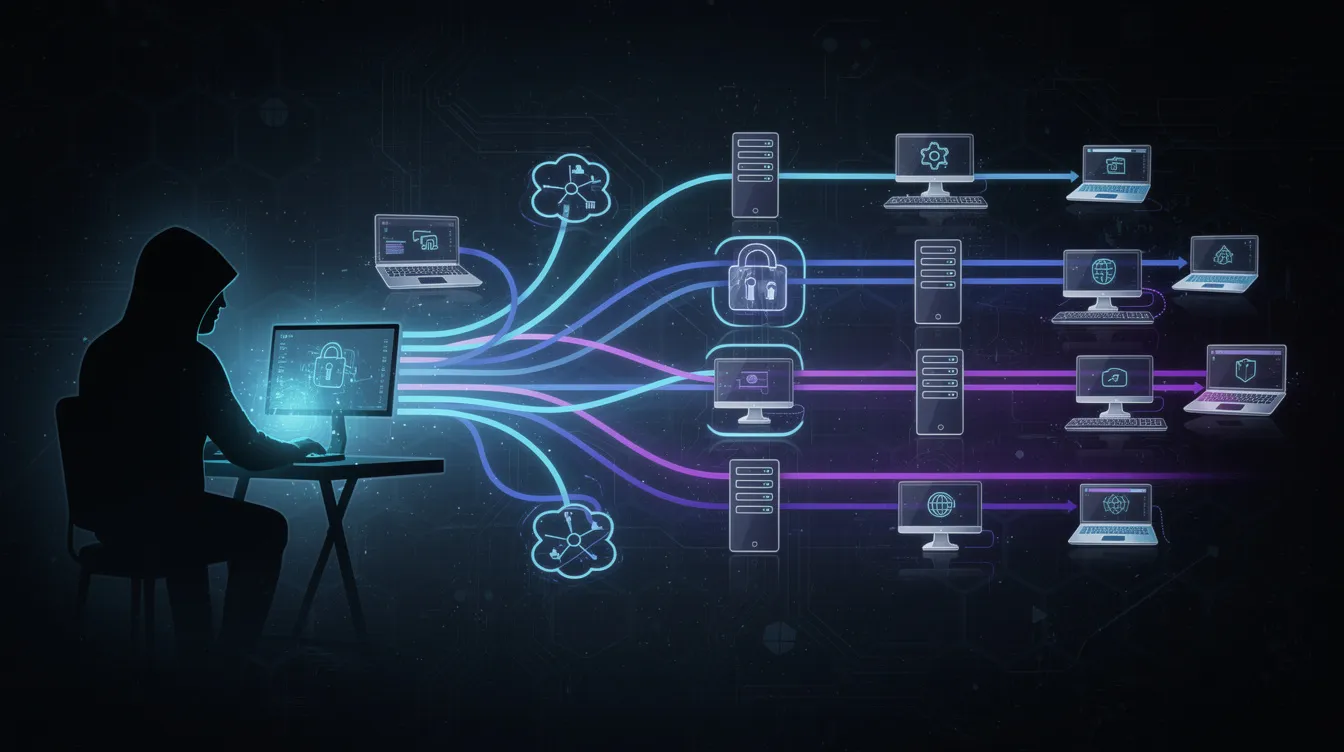
Lateral movement is a technique used by cyber attackers to navigate through a compromised network or system. It involves techniques that allow attackers to identify and compromise additional assets within a network.
Lateral movement is one of the most critical and dangerous stages of modern cyberattacks. It refers to the techniques attackers use to move through a compromised environment after gaining initial access, allowing them to expand control across multiple systems, access sensitive data, and ultimately compromise high-value assets. Specifically, malicious lateral movement describes how attackers seek to compromise high-value assets by navigating within networks and escalating privileges.

This guide is intended for IT professionals, security analysts, and organizational leaders seeking to understand and defend against lateral movement in cyberattacks. Understanding lateral movement is essential for organizations aiming to enhance their cybersecurity posture.
Lateral movement attacks work by first infiltrating a network, then expanding access through credential theft and exploiting vulnerabilities. Attackers often use stealth tactics, such as blending in with legitimate traffic, to evade detection as they move laterally within the environment.
In simple terms, lateral movement is how attackers go from “inside one machine” to “owning the entire network.” It is a core tactic used by advanced threat actors because it enables them to escalate attacks from a single compromised endpoint into full-scale breaches affecting critical systems, intellectual property, and corporate infrastructure. Advanced persistent threats are sophisticated, persistent attackers that use lateral movement to evade detection and achieve their objectives.
Understanding how lateral movement works — and how to detect and stop it — is essential for strengthening your organization’s overall security posture.
Lateral Movement and How Attackers Gain Access to Networks
Initial Access
Lateral movement begins after attackers successfully gain access to a system through phishing, malware, or exploitation of vulnerabilities. This stage is often referred to as initial access, where attackers compromise a user’s account or endpoint, leveraging the user's account for internal reconnaissance and lateral movement, and establish a foothold.
Internal Reconnaissance
Once inside, attackers begin internal reconnaissance. They scan internal systems, identify operating systems, and map out lateral movement paths, as well as identify other systems and understand access and permissions across them. This process includes identifying network hierarchies, understanding access controls, and locating credentials stored across systems.
Credential Theft Techniques
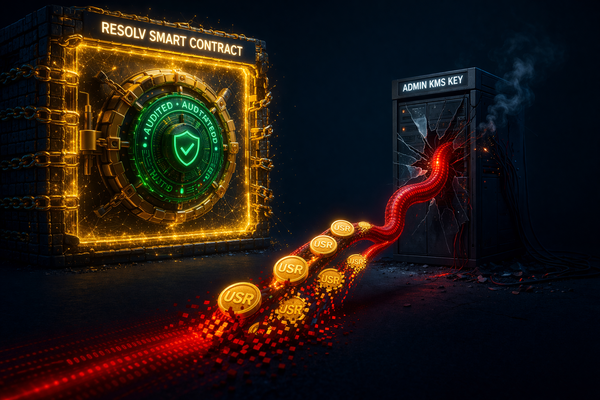
Attackers often use credential theft techniques to collect login credentials. Tools like Mimikatz extract credentials from memory, while pass-the-hash attacks allow attackers to authenticate without knowing the actual password. With valid user credentials, attackers can impersonate legitimate users. Attackers often use stolen login credentials to impersonate legitimate users during lateral movement and blend in with normal activity.
Because these actions often mimic legitimate behavior, lateral movement can be extremely difficult for security teams to detect. Attackers frequently operate within normal network traffic, making malicious activity appear indistinguishable from routine operations. Attackers may also hijack a legitimate user's ssh session to carry out malicious activities within encrypted tunnels, further complicating detection.
Lateral Movement Paths
When cybercriminals breach an enterprise network, their work has only just begun. Lateral movement paths represent the digital highways that threat actors use to traverse compromised environments, hopping from system to system as they hunt for crown jewel data and high-value intellectual property. These attack corridors typically emerge when adversaries weaponize stolen credentials, exploit unpatched vulnerabilities, or cunningly abuse legitimate administrative tools that most organizations rely on daily. Understanding these pathways has become critical as attackers increasingly demonstrate sophisticated techniques for expanding their foothold within targeted networks.
Mapping Attack Routes
Security practitioners face a challenging but essential task: mapping these potential attack routes before malicious actors can exploit them. The process demands rigorous analysis of network telemetry to spot anomalous traffic patterns, vigilant monitoring for credential abuse, and implementation of robust access controls that eliminate unnecessary system-to-system connectivity. Organizations that invest in proactive path mapping often discover surprising weaknesses in their infrastructure — connections and privileges that seemed harmless in isolation but create dangerous opportunities when viewed through an attacker's lens.
Disrupting Movement Patterns
The most effective defense strategies focus on disrupting these movement patterns through strategic access restrictions and continuous network monitoring. Security teams that thoroughly understand how adversaries might navigate their environment can implement targeted countermeasures that protect sensitive assets while maintaining operational efficiency. This intelligence-driven approach to network segmentation and access control has proven instrumental in reducing both the likelihood and impact of successful lateral movement campaigns, ultimately strengthening organizational resilience against sophisticated threat actors.
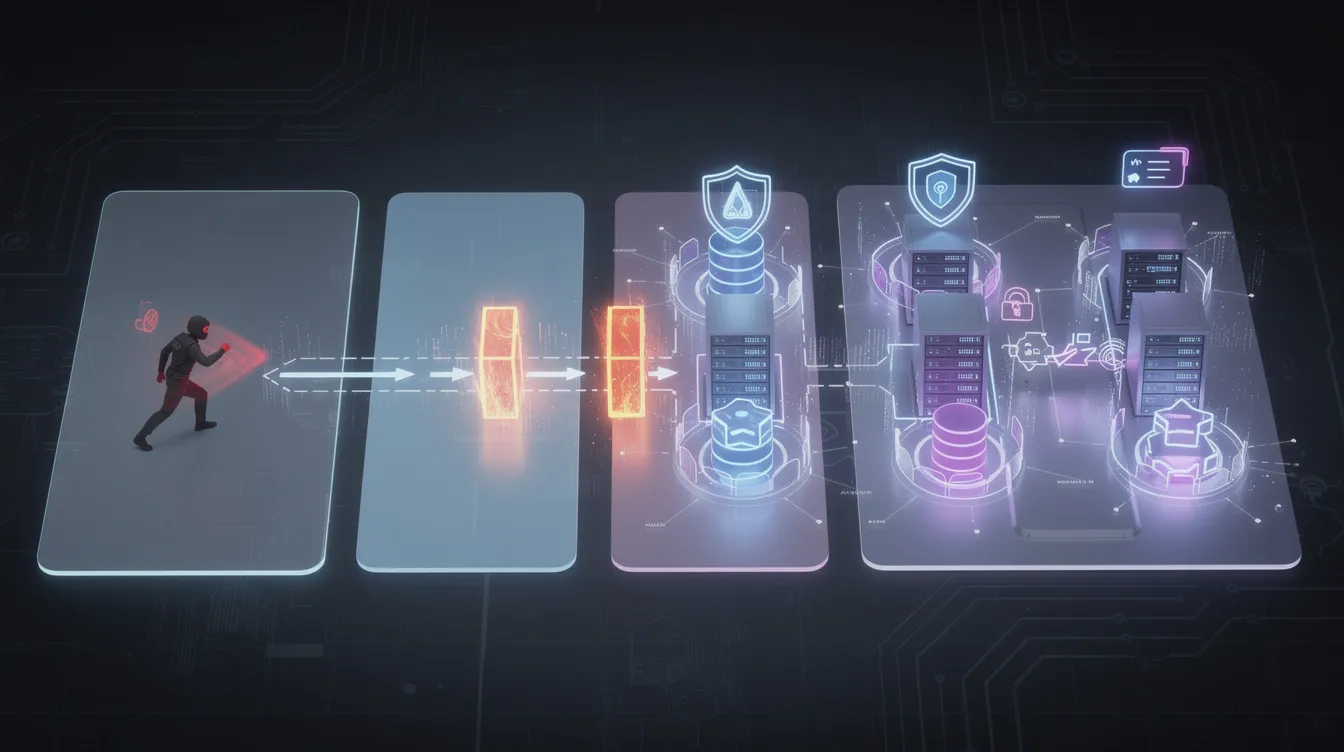
Stages of Lateral Movement in Cyberattacks
The stages of lateral movement typically follow a structured progression that allows attackers to expand access systematically.
These stages can be broken down into the following steps:
- Step 1: Initial Access
- Attackers establish initial access through compromised credentials, malware, or exploited vulnerabilities.
- Step 2: Reconnaissance
- Once inside, attackers conduct reconnaissance to identify systems, users, and sensitive data locations.
- Step 3: Credential Harvesting and Privilege Escalation
- Attackers begin credential harvesting and privilege escalation. By exploiting weak permissions or misconfigurations, they gain elevated access to additional systems. This often involves abusing built-in system tools like PowerShell or leveraging legitimate administrative tools to avoid detection. Attackers also abuse living-off-the-land binaries (LOLBins), which are legitimate tools, to evade detection during lateral movement. Implementing least-privilege access limits users to only the resources they need, making privilege escalation more difficult. Using multi-factor authentication (MFA) can prevent attackers from using stolen credentials for lateral movement.
- Step 4: Lateral Movement
- Attackers begin moving laterally across the network using remote services such as remote desktop protocol (RDP), secure shell (SSH) sessions, and server message block (SMB), as well as exploiting remote access points such as misconfigured remote services. These protocols allow attackers to connect to remote systems and expand their reach.
- Step 5: Targeting Critical Assets
- Attackers target critical data and high-value systems, often preparing for data exfiltration, ransomware deployment, or long-term persistence.
The speed of these attacks is increasing. The average dwell time for lateral movement attacks has decreased to around 21 days, meaning attackers are becoming faster and more efficient in achieving their objectives. Lateral movement can significantly increase the dwell time of attackers within a network, allowing them to conduct extensive reconnaissance and data exfiltration.
Common Lateral Movement Techniques and Attack Vectors
Attackers use a wide range of lateral movement techniques to navigate networks and compromise additional systems.
Common methods include:
- Credential-based movement: Attackers use stolen credentials to log into systems using legitimate tools like remote desktop, SSH, or Windows admin shares. This allows them to move across systems without triggering traditional security alerts.
- Use of living-off-the-land binaries (LOLBins): Built-in system tools that attackers abuse to execute commands and avoid detection. Tools like PowerShell enable attackers to execute malicious commands, change configurations, and gather additional credentials.
- Access token manipulation: Used to impersonate privileged users, allowing attackers to bypass access controls and execute commands with higher privileges.
- Vulnerability exploitation: Attackers frequently exploit vulnerabilities in operating systems, applications, and misconfigured services. Remote services exploitation is particularly common, where attackers leverage insecure configurations in RDP or SMB to move laterally.
Because attackers often use legitimate tools and protocols, their activity blends into normal operations, making detection extremely challenging.
Privilege Escalation and Credential Theft
Cybercriminals have perfected a devastating one-two punch in their attack playbooks: privilege escalation paired with credential theft. These techniques serve as the foundation for lateral movement campaigns that can devastate enterprise networks.
Initial Breach and Credential Theft
The initial breach often starts predictably enough — phishing emails that trick employees, malware deployments, or exploitation of unpatched vulnerabilities. But what happens next separates sophisticated threat actors from script kiddies. Once attackers secure those first user credentials, they immediately begin hunting for pathways to administrative access, transforming a basic user account compromise into a full-scale network infiltration.
Privilege Escalation Methods
The potency of this dual approach lies in its ability to render traditional security measures ineffective. When attackers successfully steal credentials, they essentially become digital shapeshifters — operating under the guise of legitimate users while security systems remain none the wiser. Combine this invisibility cloak with elevated administrative privileges, and suddenly access controls become meaningless barriers. The result is a nightmare scenario for security teams: attackers moving freely between systems, accessing sensitive databases, and expanding their foothold across the network while appearing as authorized users in security logs.
Enterprise defenders aren't powerless against these tactics, but they need to think strategically. The principle of least privilege remains the cornerstone of effective defense — employees should only access systems and data essential to their specific job functions, nothing more. Multi-factor authentication has proven its worth as a critical safeguard, significantly raising the bar for attackers attempting to leverage stolen passwords. Perhaps most importantly, organizations must invest in behavioral monitoring and network traffic analysis capabilities. These systems can spot the subtle anomalies that indicate privilege escalation attempts or credential abuse, giving security teams the early warning they need to prevent attackers from accessing crown jewel data and mission-critical infrastructure.
Why Lateral Movement Is So Dangerous
Lateral movement is dangerous because it transforms a minor compromise into a major security incident. Once attackers begin moving laterally, they can access as many devices as possible, increasing their control over the environment.
Unchecked lateral movement allows attackers to escalate privileges, compromise privileged accounts, and gain access to critical systems. This can lead to large-scale data breaches, exposure of intellectual property, and disruption of business operations.
Additionally, attackers can use lateral movement to avoid detection. By spreading activity across multiple systems and blending into legitimate network traffic, they can remain hidden for extended periods.
The financial impact can be severe. Lateral movement often contributes to breaches costing millions of dollars, along with regulatory fines and reputational damage. Organizations that fail to address lateral movement risks may experience long-term loss of customer trust.
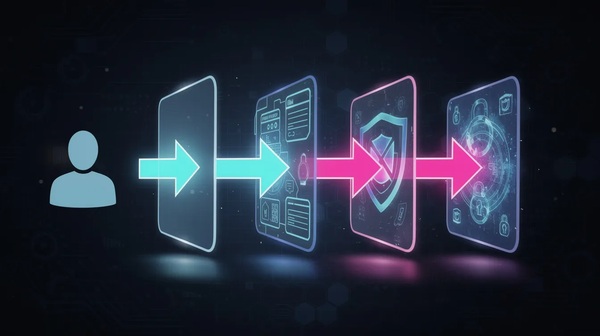
Detecting Lateral Movement and Abnormal Behavior
Detecting lateral movement requires visibility into internal network activity, especially east-west traffic — the communication between systems inside the network.
Traditional security tools often focus on perimeter defenses, but once attackers are inside, monitoring internal movement becomes critical. Organizations must analyze unusual network traffic, abnormal administrative tasks, and suspicious login activity.
Endpoint detection and response (EDR) solutions play a key role by monitoring endpoints for anomalous behavior. These tools can identify unusual commands, suspicious processes, and unauthorized access attempts.
User and Entity Behavior Analytics (UEBA) solutions use machine learning to analyze user behavior and detect anomalies that may indicate lateral movement. For example, if a user suddenly accesses systems they have never interacted with before, it may signal an attack.
Organizations should also monitor for indicators such as credential dumping, abnormal network protocols, and unexpected remote connections. These signals can help alert security teams to potential lateral movement attempts.
Preventing Lateral Movement and Strengthening Security Controls
Lateral movement prevention is a key aspect of cybersecurity strategies, focusing on detection and mitigation techniques to stop attackers from moving laterally within a network.
Preventing lateral movement requires a layered security strategy that limits access, reduces attack surfaces, and improves visibility.
- Implement the principle of least privilege: Restrict users to only the resources they need. This reduces the risk of privilege escalation and limits the damage of compromised accounts.
- Multi-factor authentication (MFA): By requiring additional verification, MFA prevents attackers from using stolen credentials to access systems.
- Network segmentation and microsegmentation: By dividing networks into isolated zones, organizations can stop lateral movement and prevent attackers from moving freely across systems. Implementing a Zero Trust architecture further minimizes the attack surface and prevents lateral movement by verifying every connection attempt. Using allowlisting for software installation can also help prevent lateral movement by ensuring that only approved applications are used.
- Monitor east-west traffic and visualize internal network activity: Helps organizations identify suspicious behavior in real time. Deception technologies can further enhance detection by redirecting suspicious behavior to high-interaction deception engines, allowing IT teams to learn more about lateral movement attacks for threat hunting.
- Regular patching and vulnerability management: Many lateral movement attacks rely on exploited vulnerabilities, so closing security gaps reduces the risk of compromise. Malware can exploit system vulnerabilities to enable lateral movement, making regular software updates and patches essential for lateral movement prevention.
- Strong password management policies: Helps prevent credential theft, which is essential for stopping lateral movement.
- Conduct regular red team exercises: Helps organizations test their defenses and improve their ability to detect and respond to lateral movement. Conducting regular red team exercises helps test how well systems detect and respond to lateral movement, surfacing visibility gaps and improving rapid containment.
Lateral movement can happen in cloud environments as well, where attackers may exploit misconfigurations and vulnerabilities to navigate through cloud infrastructure.
Lateral movement defenses are a critical aspect of cybersecurity strategies, including monitoring, testing, and continuously improving defenses through best practices like red team exercises, policy refinement, incident response planning, and integrating security into development processes.
Incident Response and Stopping Lateral Movement
An effective incident response strategy is essential for containing lateral movement once it is detected. Organizations must quickly isolate affected systems, revoke compromised credentials, and restrict access to prevent further spread.
Security teams should map lateral movement paths to understand how attackers moved through the network and identify all affected systems. This helps ensure that attackers are fully removed from the environment.
Continuous monitoring, threat intelligence, and rapid response capabilities are critical for minimizing the impact of lateral movement attacks and restoring system integrity.
Conclusion
Lateral movement represents one of the most dangerous phases of any cyberattack, turning initial network breaches into full-scale data exfiltration and system compromise scenarios. Once attackers establish their foothold inside an organization's perimeter, their ability to traverse internal networks determines whether a minor security incident escalates into a devastating breach. Security teams today face the challenge of detecting these stealthy movements across their infrastructure, requiring sophisticated monitoring capabilities that can spot unusual network patterns, analyze behavioral anomalies, and maintain granular access controls throughout their environment. The most effective defense strategies focus on understanding exactly how threat actors exploit internal pathways, abuse elevated privileges, and steal credentials to expand their reach.
Organizations serious about stopping lateral movement attacks must deploy layered security architectures that combine multiple defensive technologies and operational practices. Intrusion detection systems, advanced endpoint protection, and multi-factor authentication form the technical backbone of these defenses, but their effectiveness depends heavily on proper implementation and continuous monitoring. Security teams that regularly audit their internal network pathways and enforce strict access controls create significant obstacles for attackers attempting to move freely through compromised environments. This comprehensive approach not only protects sensitive data repositories and critical infrastructure but also limits the potential business impact when breaches do occur, helping organizations maintain operational continuity even under attack.
FAQ
What is lateral movement in cybersecurity?
Lateral movement refers to techniques attackers use to move through a network after gaining initial access, allowing them to access additional systems and sensitive data.
Why is lateral movement dangerous?
Lateral movement allows attackers to expand their access, escalate privileges, and compromise critical systems, often leading to large-scale data breaches.
How do attackers perform lateral movement?
Attackers use techniques such as credential theft, remote desktop access, access token manipulation, and exploitation of vulnerabilities to move across systems.
How can organizations detect lateral movement?
Organizations can detect lateral movement by monitoring internal network traffic, analyzing user behavior, and using tools like EDR and UEBA to identify anomalies.
How can lateral movement be prevented?
Preventing lateral movement requires least privilege access, multi-factor authentication, network segmentation, continuous monitoring, and strong security controls.
What is east-west traffic?
East-west traffic refers to data moving between systems inside a network. Monitoring this traffic is critical for detecting lateral movement.