What Is a Zero-Day Vulnerability?

In the world of cybersecurity, some of the most dangerous threats are the ones we don’t see coming. A zero-day vulnerability is a software weakness that is found by attackers before the vendor has discovered the flaw. A zero-day vulnerability is a type of software vulnerability that attackers identify before vendors are aware of it, allowing them to exploit the issue before any fix is available. Because the developers have had “zero days” to fix the issue, these flaws represent a massive security risk to organizations and individuals alike.
This guide is intended for IT professionals, security teams, and anyone interested in understanding the risks and defenses associated with zero-day vulnerabilities. Understanding zero-day vulnerabilities is crucial for these audiences because it enables them to recognize, mitigate, and respond to one of the most serious and unpredictable threats in cybersecurity.
A zero-day vulnerability exists in a version of an operating system, app, or device from the moment it is released, but the software vendor or hardware manufacturer doesn’t know it yet. These unknown vulnerabilities can remain undetected for days, months, or even years until someone finds them. The longer a zero-day vulnerability remains undetected, the more time attackers have to exploit it without interference. Zero-day vulnerabilities can surface in any business, in any system, at any time, making them a constant threat. Once malicious actors identify the flaw, they move to exploit zero-day vulnerabilities before a security patch can be created. It is crucial to keep the vulnerability secret until a patch is ready, to reduce the risk of exploitation.
During the early days of the COVID-19 pandemic, the rapid adoption of remote work tools like Zoom led to the discovery of several zero-day vulnerabilities, highlighting how quickly new threats can emerge when technology is widely and suddenly adopted.
Understanding the Zero-Day Lifecycle and Exploit
A zero-day exploit is a cyberattack vector that takes advantage of an unknown or unaddressed security flaw in computer software, hardware, or firmware. Knowledge of any new zero-day flaw starts a race between security professionals working on a fix and hackers developing a zero-day exploit that leverages the vulnerability to break into a system. Hackers often develop exploits faster than security teams can create patches, increasing the risk of advanced attacks such as Chrome zero-day attacks.
The zero-day lifecycle typically follows these stages:
- Discovery: A researcher or attacker finds an unpatched vulnerability in the software code. Attackers may use methods such as reverse engineering, vulnerability scanning, or leveraging sensitive information from insiders to identify these vulnerabilities.
- Exploitation: Threat actors develop malicious code to gain unauthorized access. These hacker exploits are used before a patch is available, making them especially dangerous.
- Identification: The software developers or security researchers become aware of the flaw.
- Public Disclosure: The vulnerability is publicly disclosed, often alongside a temporary workaround. Once a zero-day vulnerability becomes public knowledge, attackers often analyze the patch to understand the vulnerability it addresses.
- Patch Development: The vendor begins the patch development process, which can take days, weeks, or months. Security researchers and vendors act quickly to develop patches once a zero-day vulnerability is discovered.
- Remediation: A security patch is released, but the security risk remains until patch management is completed by the end-user. When software vendors and cybersecurity researchers discover a zero-day vulnerability, they act quickly to design and implement a security patch.
Anatomy of a Zero-Day Attack
Zero-day attacks represent one of cybersecurity’s most formidable challenges, unfolding through a precisely orchestrated sequence that weaponizes unknown vulnerabilities against unsuspecting targets.

The critical window opens when a previously undiscovered flaw surfaces — whether through legitimate security research or, more ominously, through the reconnaissance efforts of threat actors actively hunting for exploitable weaknesses. Armed with this intelligence, attackers race against time to maximize their advantage before vendors can issue patches, deploying sophisticated exploitation frameworks designed to penetrate defenses and establish persistent footholds in targeted environments. These footholds often allow attackers to access sensitive data stored within affected systems, increasing the risk of data breaches and information theft.
Attack Vectors
The attack vectors employed in these campaigns span the full spectrum of modern threat landscapes. Cybercriminals leverage everything from meticulously crafted spear-phishing operations that social-engineer victims into executing malicious payloads, to strategically compromised websites that function as silent exploit delivery platforms through drive-by downloads.
Consequences of Zero-Day Attacks
Once these zero-day campaigns achieve initial compromise, the consequences can be devastating — from large-scale data exfiltration and advanced persistent threat deployment to operational disruption that can cripple business continuity. This inherent stealth advantage, where attackers operate with vulnerabilities that security tools cannot yet recognize, underscores why organizations must prioritize threat hunting capabilities and incident response readiness that can identify anomalous behaviors even when signature-based defenses fail.
Notable Examples of Zero-Day Attacks
History is filled with examples of zero-day breaches that have caused massive data breaches and compromised critical infrastructure.
- Stuxnet: Perhaps the most famous zero-day, this sophisticated computer worm exploited four zero-day vulnerabilities in Microsoft Windows to target Iranian nuclear facilities.
- Sony Pictures (2014): A zero-day attack targeted Sony Pictures, bringing down its network and leaking sensitive corporate data and intellectual property.
- RSA Employees (2011): Attackers used an unpatched vulnerability in Adobe Flash Player to gain entry into the network of the security vendor RSA.
- Log4Shell (2021): A day vulnerability in Log4J, an open-source Java library. This flaw was present since 2013, but hackers didn't start zero-day exploitation until 2021.
- Google Chrome (2022): North Korean hackers exploited a zero-day remote code execution vulnerability to execute code remotely on potential victims' machines.
Why Threat Actors Prize Zero-Day Threats
Cybercriminals highly prize zero-day exploits because they represent a golden opportunity to launch undetected attacks. These exploits are often traded on the black market for significant sums; in 2020, hackers were selling Zoom zero-days for as much as USD 500,000.
Zero-day vulnerabilities are often used in targeted attacks against high-value targets such as government agencies and large organizations. Nation-state actors often seek out zero-day flaws and may choose not to disclose them, preferring to use them for their own purposes.
Zero-day attacks are some of the most difficult cyberthreats to combat because they can be exploited before their targets even know about them. In 2021, a record 83 zero-day exploits were reported, a massive increase that highlights the growing security vulnerabilities in our increasingly connected world. The rise in zero-day attacks is linked to the increasing complexity of company networks and the growing number of connected devices.
Zero-Day Attack Trends
Zero-day attacks are escalating at an alarming pace, becoming more sophisticated with each passing year. The spike in these previously unknown exploits stems from several converging factors. Software codebases continue growing in complexity, creating more potential entry points for attackers. Meanwhile, cloud adoption has expanded the attack surface exponentially, while the Internet of Things (IoT) has connected billions of new devices — many with minimal security oversight. Each expansion of our digital infrastructure creates fresh opportunities for threat actors to uncover vulnerabilities that security teams don't yet know exist.
Factors Driving Zero-Day Trends
Behind this surge lies a thriving criminal marketplace where zero-day exploits command premium prices. Threat actors now operate sophisticated procurement networks, paying substantial sums for exclusive access to these powerful attack tools. This underground economy has transformed vulnerability discovery into a profitable enterprise, creating financial incentives that often outpace legitimate security research efforts. Organizations hoping to stay ahead of this threat landscape need comprehensive strategies that go beyond reactive patching. Security teams must embrace proactive vulnerability management programs, integrate real-time threat intelligence feeds, and establish rigorous input validation protocols. The stakes couldn't be higher — as zero-day attacks continue evolving, the window between discovery and exploitation continues shrinking.
Vulnerability Management and Prevention Strategies
While a zero-day refers to an unknown flaw, zero-day attack prevention is possible through a multi-layered defense. Security teams must move beyond known vulnerabilities and adopt proactive measures.
- Patch Management and Rapid Remediation: Organizations should implement a formal patch management program to stay abreast of critical updates. When a patch exists, timely remediation is the only way to reduce exposure.
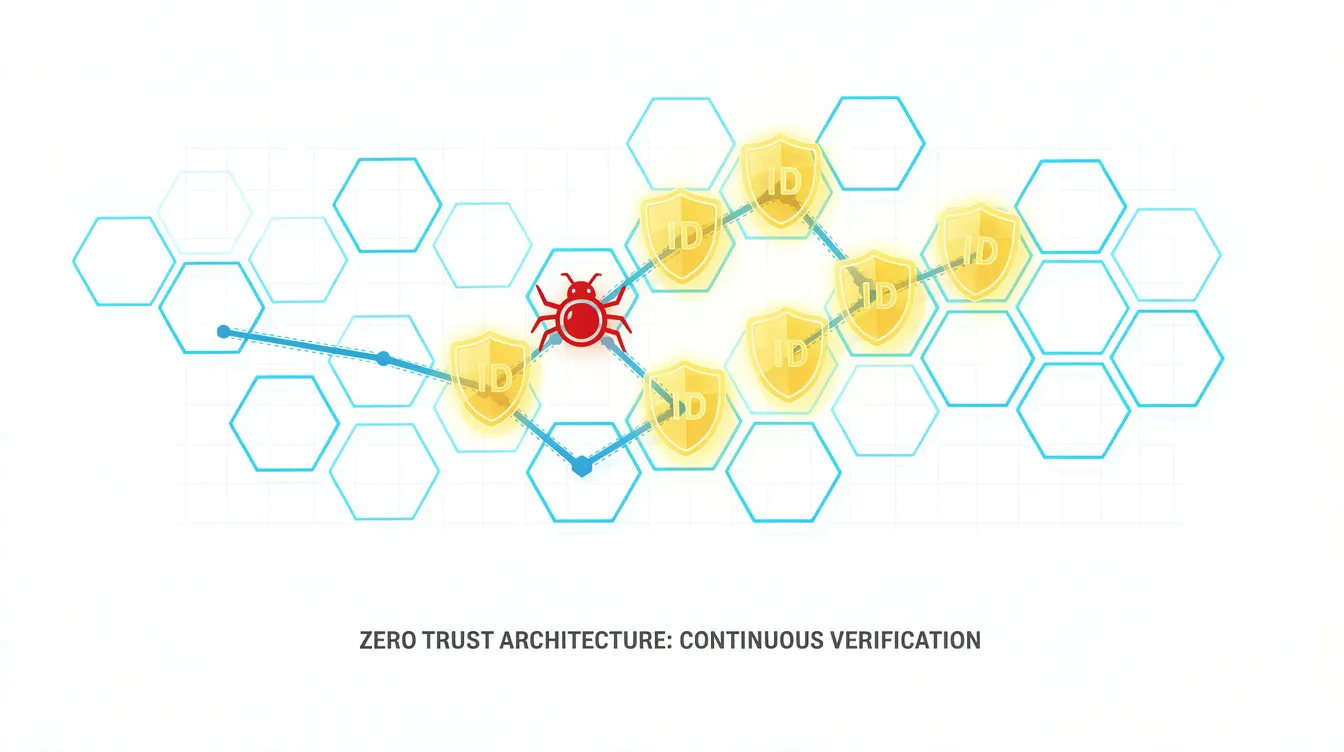
- Zero Trust Architecture: Implementing zero trust principles can limit damage if a hacker uses a day attack to break into a network. A zero trust architecture assumes that every user and device is a potential threat, requiring continuous verification before allowing threat actors to gain access to sensitive data.
- Anomaly Detection and Machine Learning: Because zero-day malware has no known signature, traditional antivirus is largely ineffective. Anomaly-based detection and machine learning can catch a zero-day attack occurs by spotting suspicious activity in real-time.
- Threat Intelligence: Organizations should stay informed by monitoring external threat intelligence. Hearing about emerging threats early allows security teams to act quickly to protect against zero-day strikes.
Patch Development for Zero-Day Vulnerabilities
The discovery of a zero-day vulnerability triggers an urgent response across the cybersecurity ecosystem, setting off a high-stakes race between defenders and attackers. While software vendors and security researchers scramble to develop protective measures, threat actors are simultaneously working to weaponize the newly exposed flaw. This critical window — where systems remain vulnerable until patches arrive — demands seamless coordination between security teams and vendors to assess the vulnerability's scope, engineer an effective solution, and validate that remediation efforts don't inadvertently create additional attack surfaces or operational disruptions.
The patch development lifecycle follows a methodical yet time-pressured approach that begins with comprehensive vulnerability assessment. Security researchers must rapidly dissect the flaw's potential impact and map possible attack vectors before developers can craft targeted fixes. Rigorous testing phases follow in isolated environments, where teams verify that proposed patches effectively neutralize threats without destabilizing critical systems. This validation process, though essential, extends the vulnerability window — making speed and accuracy equally crucial.
Day Vulnerability Detection
Vulnerability detection remains the backbone of any robust security program, yet the landscape continues to evolve in ways that challenge traditional approaches. Security teams have long depended on established methods — vulnerability scanners, penetration testing frameworks, and threat modeling — to hunt down known exploits and patch management gaps. These day vulnerabilities, while dangerous, follow predictable patterns that security professionals have learned to anticipate and counter effectively.
Day vulnerabilities are known software flaws for which patches or mitigations exist, while zero-day vulnerabilities are unknown to the vendor and have no available fix at the time of discovery. The real test comes with zero day threats, where attackers leverage previously unknown flaws that exist completely outside the radar of security vendors and research communities. Organizations today are turning to behavioral analysis and machine learning platforms that can spot the telltale signs of exploitation attempts, even when traditional signature-based detection falls short.
How to Protect Against Zero-Day Exploitation
To prevent zero-day attacks, companies must minimize their attack surface.
- Input Validation: Prevents improperly formed data from entering a vulnerable system.
- Vulnerability Management: Regular penetration tests and vulnerability management assessments help find flaws before malicious actors do.
- Web Filtering: Blocking access to file sharing sites or suspicious domains can disable the delivery mechanism for malicious code.
Incident Response Planning
Organizations facing the growing threat landscape understand that robust incident response planning represents the difference between a contained security event and a business-disrupting catastrophe when zero day exploits strike. Security teams must establish comprehensive detection protocols that can identify anomalous behavior patterns, implement rapid containment measures to prevent lateral movement, systematically eradicate malicious code from compromised systems, and execute recovery procedures that restore normal operations. The most effective response frameworks incorporate thorough post-incident analysis — a critical step that transforms each attack into actionable intelligence for strengthening future defensive postures.
Communication During Incident Response
The communication dimension of incident response often determines whether an organization emerges stronger or suffers prolonged reputational damage. Security professionals must orchestrate information flows across multiple stakeholder groups, ensuring employees, customers, and business partners receive timely, accurate updates that maintain trust while avoiding panic. Regular tabletop exercises and simulation scenarios prepare response teams to execute under pressure.
Security Awareness and Training
Building effective defenses against zero-day attacks fundamentally depends on creating a workforce capable of identifying threats before they escalate into breaches. Security awareness training serves as a critical first line of defense, equipping employees to spot the telltale signs of compromise — from sophisticated phishing campaigns that leverage social engineering tactics to anomalous system behaviors that often precede payload deployment. Organizations that invest in comprehensive training programs see measurable improvements in threat detection rates.
The protection of high-value assets, including proprietary intellectual property and sensitive personal data, requires sustained organizational commitment. When security becomes embedded in organizational culture rather than treated as an IT department responsibility, companies demonstrate significantly improved resilience against sophisticated attacks that target human vulnerabilities alongside technical ones.
Frequently Asked Questions (FAQ)
What is the difference between a zero-day vulnerability and a zero-day exploit?
- Zero-day vulnerability: A zero-day vulnerability is a software weakness that is found by attackers before the vendor has discovered the flaw.
- Zero-day exploit: A zero-day exploit is a cyberattack vector that takes advantage of an unknown or unaddressed security flaw in computer software, hardware, or firmware.
Why is it called "Zero-Day"?
The term zero-day refers to the fact that the developer has had "zero days" to fix the problem since they only just learned about it (or haven't learned about it yet).
Who discovers zero-day vulnerabilities?
They are discovered by security researchers (often called "White Hat" hackers), malicious actors, and government agencies.
Can antivirus software stop a zero-day attack?
Standard antivirus that relies on a database of known vulnerabilities is often ineffective. However, modern security software using behavior-based detection and machine learning can sometimes detect vulnerabilities by looking for unusual system behavior.
How common are zero-day attacks?
The number has exploded recently. While Cybersecurity Ventures once expected a new day exploit daily by 2021, the actual reported record of 83 zero-day exploits in 2021 shows that while not "daily" yet, they are a constant and escalating security risk.




