Supply Chain Cyberattacks: How They Work & Spread

Supply chain attacks are a rapidly evolving class of cyber threats that exploit the complex web of trust between organizations and their external partners. In today’s interconnected digital landscape, businesses rely on a vast network of vendors, service providers, and open-source components to build, deliver, and maintain their software. This article will cover the definition of supply chain attacks, real-world examples, the risks they pose, and effective prevention strategies. It is intended for IT professionals, business leaders, and anyone responsible for organizational cybersecurity. Understanding supply chain attacks is crucial because these threats can bypass traditional defenses, target the weakest link in your network, and cause widespread operational, financial, and reputational damage.
What Are Supply Chain Attacks?
A software supply chain consists of all the external vendors, service providers, and open-source components that organizations rely on to build and operate their software. Supply chain attacks exploit the trust relationships between these entities, targeting the weakest link in the chain of trust.
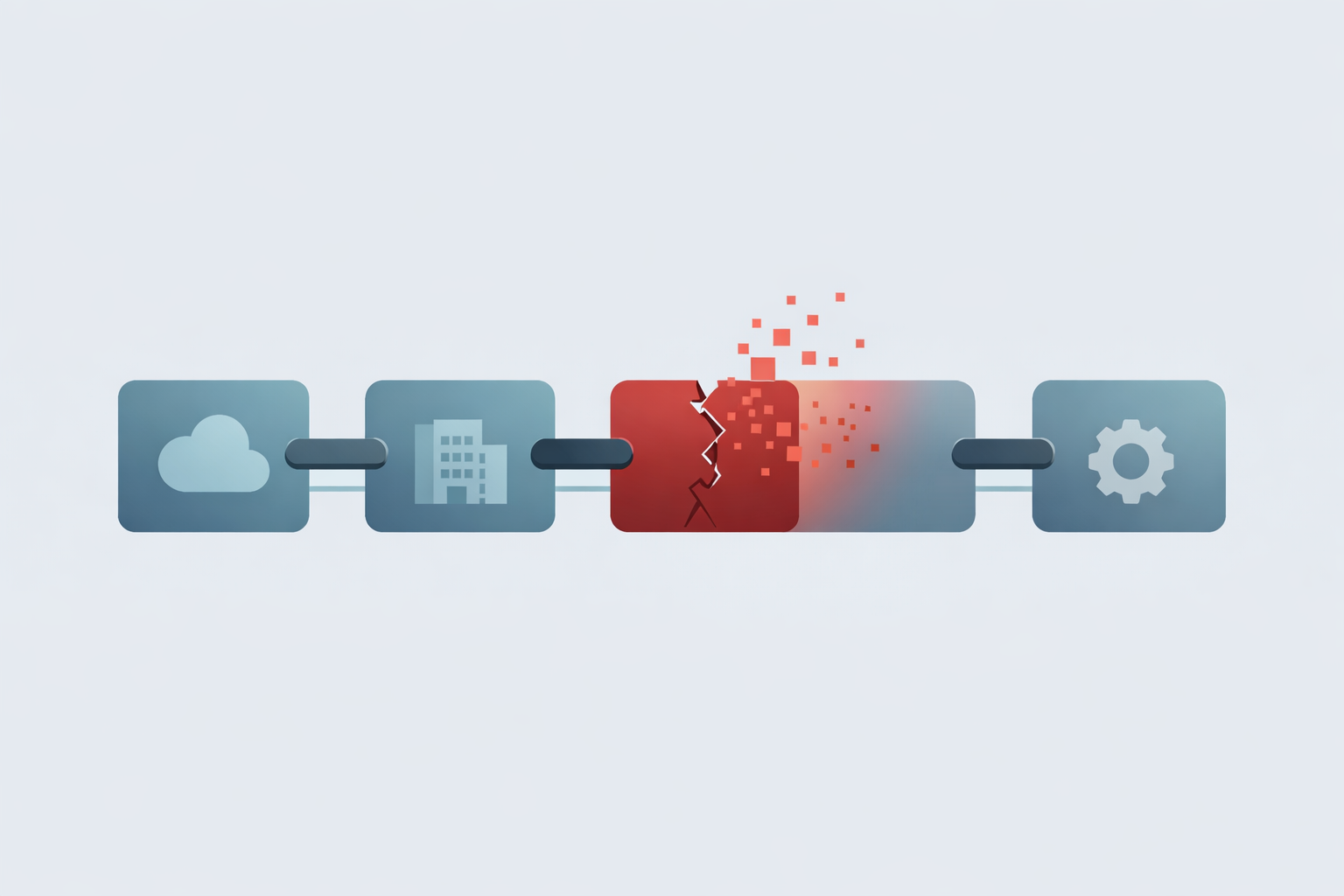
A supply chain attack is a cyber-attack that seeks to damage an organization by targeting less secure elements in the supply chain. Rather than attacking a company directly, threat actors infiltrate third-party software, vendors, or service providers to ultimately gain access to the intended target. Attackers understand that breaching a trusted vendor allows them to gain unauthorized access into a more secure network, often impacting multiple organizations simultaneously.
These attacks are especially dangerous and difficult to detect because they exploit the inherent trust between organizations and their partners.
With this foundation, let’s explore how the software supply chain operates and why it is a critical focus for cybersecurity.
Understanding the Software Supply Chain
Today's software development landscape relies on a complex web of organizations, third-party vendors, and service providers working together to build, deliver, and support the applications that power modern business. This sprawling ecosystem encompasses everything from established software vendors and managed service providers to open source maintainers and cloud infrastructure companies. The sheer number of players involved creates an inherently risky environment where cybercriminals can exploit multiple entry points, elevating supply chain security to a critical concern for enterprise defenders.
Attackers increasingly target these interconnected relationships, seeking out the most vulnerable participants to infiltrate entire networks or slip malicious code into legitimate software before it reaches end users. Security teams are responding with comprehensive monitoring of network traffic patterns, implementation of rigorous access control frameworks, and detailed vetting processes for third-party partnerships. Organizations that develop a thorough understanding of their software supply chain dependencies — and the potential attack vectors they create — are better positioned to deploy defensive measures that can withstand today's sophisticated supply chain compromises while building more resilient security architectures.
With this understanding of the software supply chain, let's examine why attacks on these systems are on the rise.
The Rise of Software Supply Chain Attacks
The surge in software supply chain attacks is closely tied to the growing reliance on open source components, third-party vendors, and cloud services. Between 2019 and 2022, these attacks increased by 742%, and by 2026, they are considered a primary enterprise risk.
The global cost of these attacks is projected to reach $60 billion annually by 2025, with breaches taking an average of 267 days to detect and contain.
These attacks are:
- Stealthy — bypass traditional perimeter defenses
- Scalable — impact thousands or even hundreds of millions of users
- Sophisticated — leverage trusted systems and legitimate software
- Focused — attackers often identify a primary target within the supply chain, such as a vulnerable vendor or system, to maximize impact
Supply chain attacks can be used to perform any type of cyber attack, such as data theft, sabotage, or ransom.
As the threat landscape evolves, it’s important to understand the various methods attackers use to compromise the software supply chain.
Types of Cyber Attacks
Software supply chain attacks continue to evolve in sophistication, with threat actors deploying an arsenal of techniques designed to infiltrate organizations through their most trusted digital pathways.
Malicious Code Injection
- Attackers inject malicious code directly into legitimate software updates or compromise third-party components that organizations rely on daily. This tactic turns routine maintenance into a potential security nightmare.
Watering Hole Attacks
- Cybercriminals strategically compromise websites that employees regularly visit, effectively transforming familiar digital destinations into malware distribution points.
Zero-Day Vulnerabilities
- Attackers exploit previously unknown software flaws, giving them a critical window of opportunity to strike before patches become available.
Other Attack Methods
- Phishing: Phishing campaigns often serve as the initial entry point for more sophisticated attacks.
- Ransomware: Ransomware incidents can bring entire organizations to a standstill.
- Denial-of-Service (DoS): DoS attacks can disrupt critical services when organizations can least afford downtime.
Given this multifaceted threat environment, security teams are increasingly turning to advanced malware prevention tools as a cornerstone of their defense strategy. However, technology alone isn't enough — maintaining constant vigilance against emerging threats remains essential for protecting the increasingly complex software supply chain that modern businesses depend on.
Understanding these attack methods sets the stage for examining how supply chain attacks unfold in practice.
How Supply Chain Attacks Work
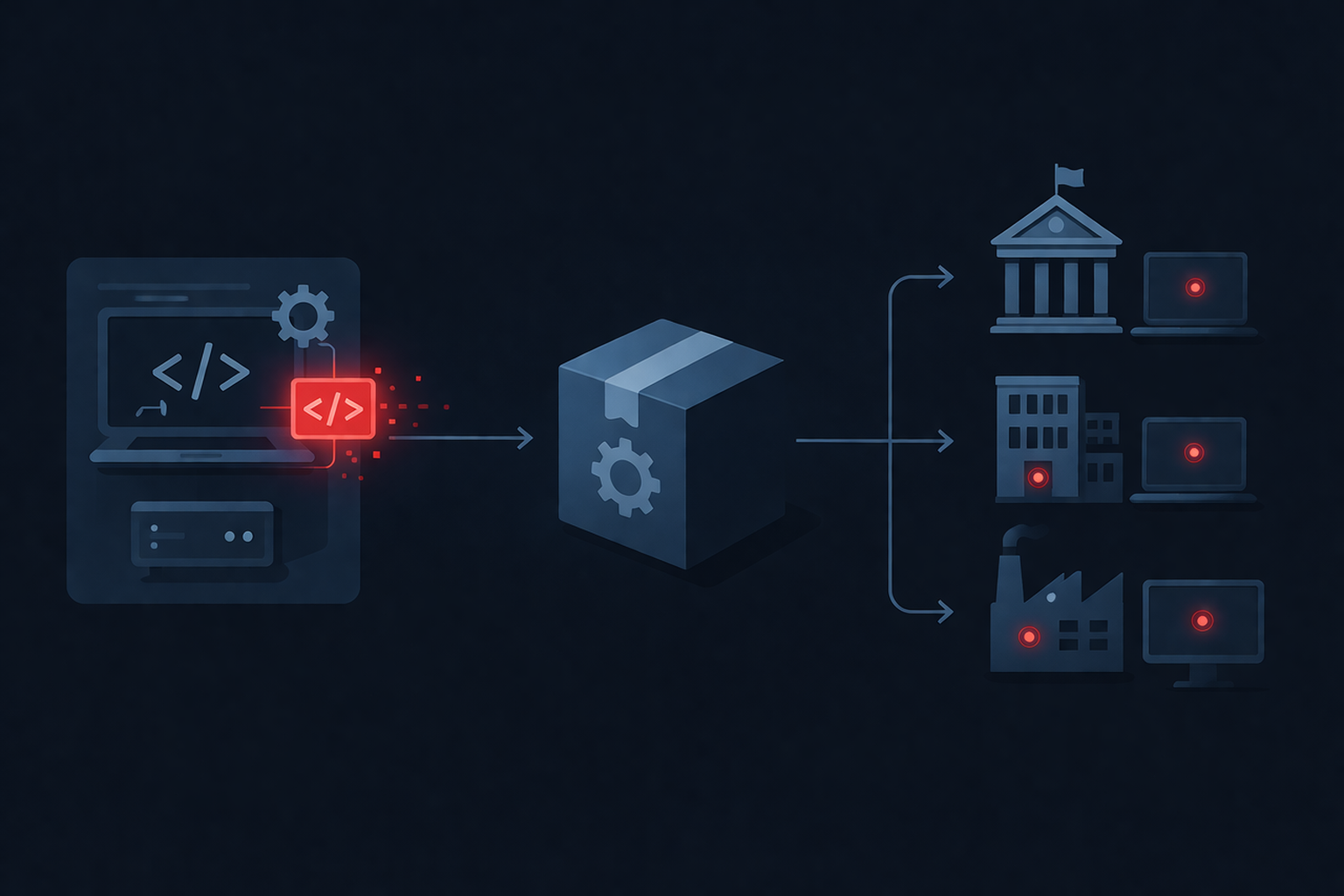
Understanding how supply chain attacks work is critical to defending against them. A typical attack follows this pattern:
- Reconnaissance
- Threat actors identify the weakest link in an organization’s supply chain.
- This could be a third-party supplier, managed service provider, or vulnerable software vendor.
- Initial Compromise
- Attackers exploit vulnerabilities, including any critical vulnerability, in software or infrastructure to gain initial access.
- Methods include:
- Compromising source code
- Exploiting development tools
- Watering hole attacks targeting employees by compromising websites frequently visited by employees of a targeted organization to infect them with malware
- Malicious Injection
- Attackers begin to insert malicious code into:
- Software updates
- Build pipelines (compromising the software build pipeline allows attackers to insert malicious artifacts directly into production releases)
- Open-source dependencies
- Attackers begin to insert malicious code into:
- Distribution
- The compromised component is distributed as legitimate software.
- End users unknowingly install malware through software updates.
- Execution & Expansion
- Malware enables:
- Remote code execution
- Data exfiltration
- Lateral movement across connected systems
- Compromised systems and affected servers can be leveraged for further attacks, increasing the scope and impact of the breach.
- Malware enables:
This allows attackers to achieve deep access into enterprise environments without triggering traditional defenses.
Now, let’s look at real-world incidents that demonstrate the impact of supply chain attacks.
Real-World Supply Chain Breaches
Several high-profile supply chain breach incidents highlight the severity of this threat:
- SolarWinds (2020)
In December 2020, FireEye identified a cyber breach involving the SolarWinds Orion software, which had been compromised prior to its discovery. This sophisticated supply chain attack impacted government agencies and financial institutions. Security researchers, including Check Point Research, played a key role in analyzing the attack and its implications. - Kaseya (2021)
The 2021 Kaseya attack exploited vulnerabilities in Kaseya's VSA software, delivering ransomware to downstream customers. Security researchers investigated the incident to help organizations detect and mitigate the threat. - MOVEit (2023)
In June 2023, the MOVEit supply chain attack targeted users of the MOVEit Transfer tool, owned by Progress Software, and affected numerous organizations globally. Security researchers analyzed the breach to understand its scope and impact. Compromised dependencies in such incidents can spread malware to end users or customers once the application is deployed or distributed. - 3CX (2023)
Malicious activity detected in software distribution systems. - Target Data Breach (2013)
The 2013 Target data breach was one of the largest data breaches in the history of the retail industry, affecting around 40 million customers. Attackers infiltrated via a third-party HVAC vendor, exposing massive amounts of customer data. - NotPetya (2017)
The 2017 NotPetya malware attack affected multiple industries in Ukraine and spread globally, impacting organizations in Russia, the United Kingdom, India, and the United States. The attack spread via compromised software updates, disrupting critical infrastructure. - Colonial Pipeline (2021)
The 2021 Colonial Pipeline ransomware attack was attributed to the Russian-linked cybercriminal group DarkSide, causing significant disruption to fuel supplies in the United States. - Microsoft/State Department (2023)
In July 2023, Chinese state-sponsored hackers targeted the United States Department of State, hacking several government employees' Microsoft email accounts.
These incidents demonstrate how supply chain attacks can cascade across ecosystems, impacting multiple organizations simultaneously. Security researchers and threat intelligence teams, such as Check Point Research, are essential in identifying, analyzing, and responding to these evolving threats.
With these examples in mind, it’s important to understand the risks supply chain attacks pose across different industries.
Supply Chain Risks Across Industries
Supply chain risks affect virtually every sector:
- Financial institutions — exposure of sensitive financial data
- Government agencies — national security implications
- Healthcare systems — compromise of sensitive patient data
- Critical infrastructure — operational disruption and sabotage. Risks to physical components are especially significant, as compromised physical components can be exploited to infiltrate systems and pose serious security threats.
Organizations should group vendors based on risk levels, security practices, and access to sensitive data to prioritize monitoring and improve supply chain security.
Supply chain attacks can exploit vulnerabilities in both the physical flow of assets and the virtual flow of data or software.
Supply chain attacks can:
- Steal sensitive information
- Disrupt operations
- Enable ransomware campaigns
- Compromise end user devices
- Perform ransom, sabotage, and intellectual property theft
Recognizing these risks is essential for understanding why supply chain attacks are so dangerous.
Why Supply Chain Attacks Are So Dangerous
These attacks are uniquely effective because they:
- Exploit trusted relationships
- Target the weakest link in the chain of trust
- Spread through legitimate software updates
- Bypass traditional perimeter defenses
A single compromised dependency can affect:
- Applications and services employees use
- Internal systems
- External customers
- Lead to compromised systems that serve as entry points for attackers
Supply chain breaches take an average of 267 days to identify and contain, which is longer than typical internal breaches.
This makes software supply chain attacks one of the most dangerous forms of modern cyber attacks.
Given the severity of these risks, it’s important to consider the financial implications of supply chain attacks.
Financial Implications of Cyber Attacks
Cybercriminals targeting software supply chains aren't just disrupting operations — they're wreaking havoc on corporate balance sheets. The financial carnage extends far beyond immediate incident response costs, encompassing legal battles, regulatory penalties, and the slow burn of reputational damage that can persist for years after headlines fade. Industry research puts the average breach price tag at $4.45 million, though organizations in critical sectors have watched losses balloon past the $100 million mark when attackers successfully compromise government systems or other high-value targets.
Smart security leaders are treating supply chain protection as a business continuity imperative, not just an IT checkbox. Network segmentation, round-the-clock monitoring systems, and comprehensive security awareness programs represent the baseline defense posture that separates resilient organizations from future breach statistics. These investments do double duty — shrinking attack surfaces while containing blast radius when incidents occur. Meanwhile, cyber insurance has evolved from a nice-to-have into essential financial armor, helping organizations weather the storm when sophisticated threat actors inevitably test their defenses against an increasingly complex software ecosystem.
To mitigate these financial and operational risks, organizations must adopt robust prevention strategies.
Strengthening Supply Chain Security
To defend against supply chain attacks, organizations must build a comprehensive supply chain security strategy. Organizations can implement several strategies to reduce their risk of becoming victims of supply chain attacks. Creating a multifaceted supply chain security strategy involves coordinating with security and risk management leaders to understand threats, and may include input from a senior security researcher.
1. Inventory the Supply Chain
- Identify all third-party providers
- Map vendor relationships
- Track third-party dependency
2. Implement a Software Bill of Materials (SBOM)
- Maintain a detailed software bill
- Track all dependencies and off-the-shelf components
3. Enforce Strong Access Controls
- Limit privileged access
- Prevent attackers from gaining unauthorized access
4. Adopt Zero Trust Architecture
- Reduce lateral movement
- Continuously verify identity across the secure network
5. Monitor Continuously
- Analyze network traffic
- Detect anomalies in real time
6. Strengthen Development Security
- Conduct code reviews
- Protect source code
- Monitor build pipelines for malicious code
7. Vet Third-Party Vendors
- Assess cybersecurity posture
- Require certifications
- Evaluate risk from third-party service providers
8. Deploy Runtime Security
- Detect threats during execution
- Stop downloading malicious code in real time
9. Improve Vulnerability Management
- Patch critical vulnerabilities
- Track exposure across connected systems
10. Prepare for Incidents
- Develop response plans
- Simulate security incidents
- Ensure recovery readiness
By implementing these strategies, organizations can significantly reduce their risk of becoming victims of supply chain attacks.
As the threat landscape continues to evolve, it’s important to look ahead at how supply chain attacks may develop in the future.
The Future of Supply Chain Attacks
As organizations increasingly rely on cloud services, machine learning, and distributed development, the attack surface continues to expand. Infected updates, poisoned dependencies, and build pipeline infiltration are now common methods used to inject malicious payloads into software or services.
Cyber criminals are evolving tactics to:
- Exploit open source dependencies
- Target software development pipelines
- Compromise third-party vendors
- Demand payment to provide decryption keys after successful ransomware supply chain attacks
As of 2026:
- Nearly one-third of business leaders report increased supply chain attacks
- These attacks are considered advanced threats requiring proactive defense
Staying informed and proactive is essential for organizations to defend against these evolving threats.
Conclusion
Supply chain attacks represent a fundamental shift in how cyber threats operate. By targeting trust relationships and external dependencies, attackers can infiltrate even the most secure environments.
Organizations must recognize that their security is only as strong as their supply chain.
Building supply chain resilience requires:
- Visibility
- Continuous monitoring
- Strong vendor governance
- Modern security architectures
Without these measures, even a single compromised vendor can lead to a devastating data breach.
FAQ: Supply Chain Attacks
What is a supply chain attack?
A supply chain attack is a cyberattack that targets an organization by compromising third-party components such as vendors, software, or service providers.
Why are software supply chain attacks increasing?
The rise of open source software, cloud services, and third-party software has expanded attack surfaces, making these attacks more common.
How do attackers gain access in supply chain attacks?
Attackers exploit security vulnerabilities, compromise source code, or inject malicious code into trusted systems to gain access.
What is the biggest risk of a supply chain breach?
A supply chain breach can impact multiple organizations, leading to widespread data breaches, operational disruption, and financial loss.
How can organizations prevent supply chain attacks?
Organizations should:
- Implement zero trust
- Monitor third-party risks
- Use malware prevention tools
- Enforce strong security measures
What industries are most affected?
All industries are at risk, especially:
- Financial institutions
- Government agencies
- Critical infrastructure sectors