PhantomCore Exploits TrueConf Vulnerabilities to Breach Russian Networks
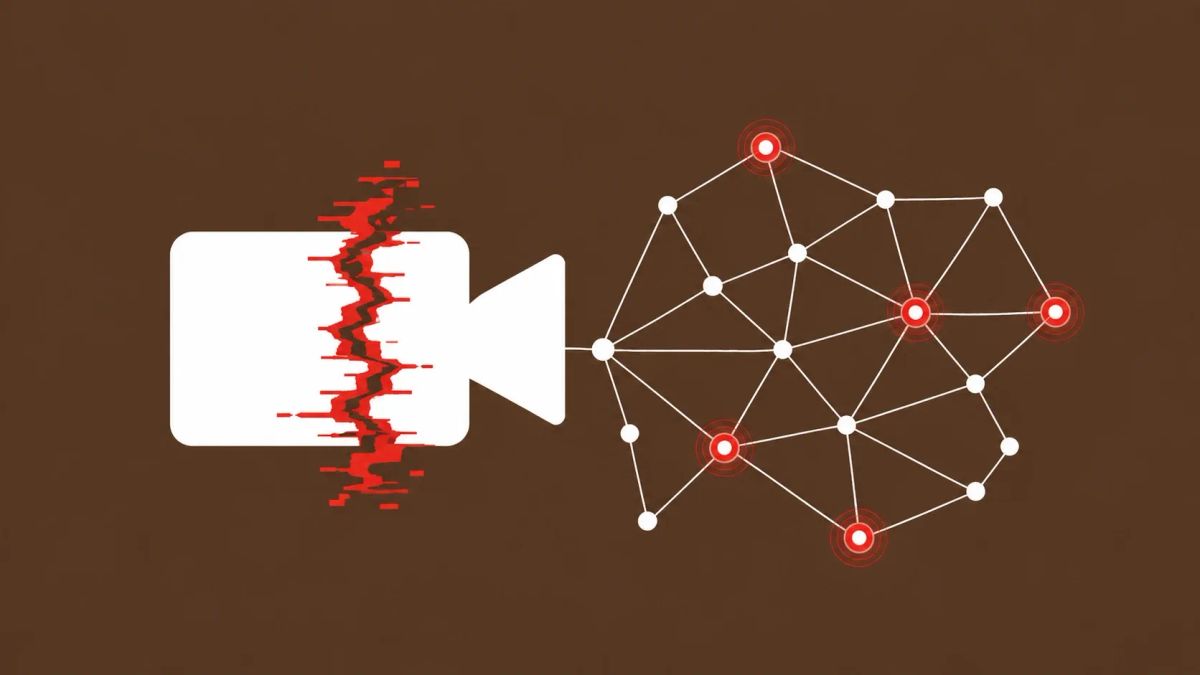
A pro-Ukrainian hacktivist group called PhantomCore has been exploiting three TrueConf video conferencing flaws (BDU-2025-10114, 10115, 10116) since September 2025 to breach Russian networks. By chaining these vulnerabilities, the group bypasses authentication and executes arbitrary OS commands, turning video conferencing servers into springboards for lateral movement and data harvesting.
ST. PETERSBURG, RUSSIA — Security researchers have identified a massive infiltration campaign targeting Russian government and private organizations, spearheaded by the pro-Ukrainian hacktivist collective known as PhantomCore (also tracked as Fairy-Trickster or Head-Mare). The group is leveraging a high-impact exploit chain within TrueConf Server, a dominant domestic video conferencing platform in the Russian market.
The campaign, which began shortly after patches were released in late August 2025, exploits a window of unpatched infrastructure. By chaining three distinct flaws, PhantomCore achieves full Remote Code Execution (RCE), allowing them to deploy web shells and establish persistent reverse SOCKS tunnels into the heart of Russian internal networks.
TrueConf RCE Chain (BDU-2025-10114/15/16)
Incident Analysis: Video Conferencing as a Network Pivot
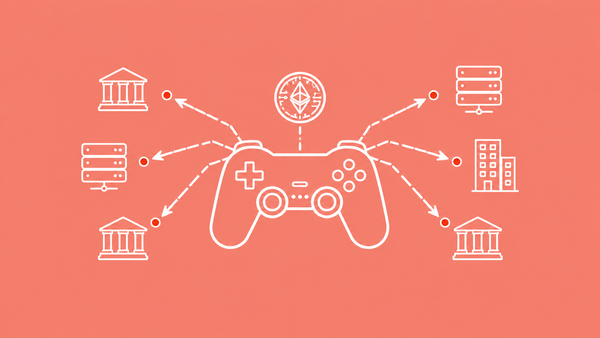
Collaboration tools like TrueConf are increasingly becoming the "soft underbelly" of enterprise security. Because these servers must be accessible to both internal and external users, they occupy a unique position in the network topology.
PhantomCore's tradecraft involves deploying a custom malicious client named PhantomPxPigeon. This tool acts as a reverse shell endpoint, routing commands through the compromised TrueConf server to masquerade malicious traffic as legitimate video conferencing data. Once established, the group moves laterally using open-source tools like Velociraptor and Memprocfs to harvest credentials and dump memory from adjacent workstations.
Geopolitical Hacktivism: The "Regional Software" Strategy
This campaign signals a refined strategy by pro-Ukrainian groups: the targeted hunting of vulnerabilities in domestic software vendors that have replaced Western alternatives (like Zoom or Teams) in Russia. By privately developing exploits for regional platforms like TrueConf, PhantomCore can achieve high-density infiltration across multiple sectors — government, critical infrastructure, and public administration — with a single exploit chain.
The CyberSignal Analysis: Strategic Signals
Signal 01 — The High Risk of the "Collaboration Pivot"
This incident proves that video conferencing platforms must be hardened with the same rigor as edge firewalls. PhantomCore used these servers not just for eavesdropping, but as high-velocity entry points for network-wide compromise. For defenders, this highlights the necessity of monitoring for unusual SOCKS tunnels and web shell processes originating from collaboration servers.
Signal 02 — The Evolution of Pro-Ukrainian Hacktivism
PhantomCore represents a shift from simple DDoS attacks to sophisticated geopolitical cyber operations. By utilizing custom-built RATs like MacTunnelRAT and advanced proxying techniques, they are operating with the technical depth of state-sponsored APTs, even while maintaining their hacktivist identity.
Signal 03 — The "Patch Window" Trap
Despite TrueConf releasing patches on August 27, exploitation began in earnest just two weeks later. This narrow window demonstrates how quickly hacktivist groups can reverse-engineer patches to develop working exploits. Organizations that delay "domestic software" updates are now prime targets for these rapid-response exploitation campaigns.