Jones Day Discloses Data Breach Affecting 10 Clients Following Phishing Attack

Jones Day, one of the world's largest law firms, has confirmed that a targeted cyberattack resulted in unauthorized access to sensitive files belonging to 10 of its clients. The breach, which the firm describes as "limited" in scope, was carried out via a sophisticated phishing campaign and has been claimed by the cybercriminal syndicate known as Silent Ransom Group (SRG).
The Silent Ransom Intrusion
The breach was disclosed on Monday after the Silent Ransom Group — also known as Luna Moth or Chatty Spider — listed Jones Day on its extortion leak site. According to reports from Bloomberg and Reuters, the attackers gained entry to the firm's environment through a social engineering scheme that targeted specific employees.
Jones Day spokesperson Dave Petrou stated that the unauthorized third party accessed a "limited number of dated client files." While the firm has not publicly named the 10 affected clients, Jones Day’s roster includes high-profile global entities such as Goldman Sachs, McDonald’s, and General Motors. The firm confirmed that all impacted parties have been notified and that the breach did not involve a full-scale encryption of their primary network.
Silent Ransom Group’s Evolving Tactics
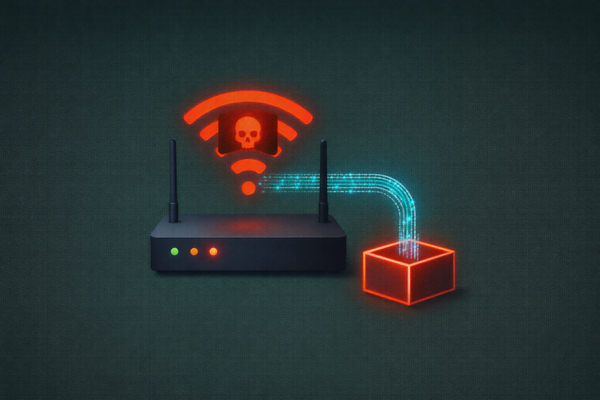
The attribution to Silent Ransom Group is significant for the legal industry. Unlike traditional ransomware groups that focus on "locking" systems, SRG specializes in "data-only" extortion. According to the FBI's IC3, this group frequently uses "callback phishing" — sending fake subscription invoices that prompt victims to call a fraudulent support number.
Once on the phone, the attackers trick employees into installing legitimate remote access tools (such as Zoho Assist or AnyDesk) to "fix" the issue, which then allows the hackers to quietly exfiltrate data using file transfer tools like WinSCP. This "living off the land" approach makes the attacks notoriously difficult for standard antivirus software to detect, as the tools being used are common in corporate IT environments.
A Repeat Target
This incident marks the second major data exposure for Jones Day in five years. In 2021, the firm was caught in the global Accellion FTA hack, where the Clop ransomware gang exfiltrated 100GB of data. Law360 notes that this latest breach underscores the persistent "bullseye" on top-tier law firms, which act as centralized repositories for the world’s most valuable intellectual property and litigation strategies.
Primary Intel & Reports: Bloomberg, Reuters, FBI IC3 Advisory on Silent Ransom Group, DataBreaches.net
The CyberSignal Analysis
The Jones Day breach highlights the critical vulnerability of Third-Party Legal Counsel in the corporate supply chain.
- Extortion Without Encryption: The Silent Ransom Group’s model proves that "Ransomware" is no longer about the "ware" — it’s about the Leverage. By focusing on data theft rather than system lockouts, attackers can operate for weeks or months without being detected. For law firms, this means that "Uptime" is no longer a metric of security; "Data Integrity" is the only metric that matters.
- The Weaponization of IT Support: This attack relied on the "IT Support" persona. In a hybrid or remote work world, employees are conditioned to grant remote access to "IT" to resolve technical hurdles. This creates a massive psychological opening. Law firms must implement Strict Out-of-Band Verification — where an employee must verify an IT request through a secondary, pre-approved channel before granting remote access.
- Operational Takeaway: Organizations must audit their Remote Access Tool (RAT) Policies. If your firm uses Splashtop, any instance of Zoho Assist or AnyDesk appearing on your network should trigger an immediate "High Priority" security alert. Standardizing on a single, sanctioned RAT and blocking all others at the firewall level is a fundamental defense against the SRG playbook.