How Exploit Chains Work in Modern Cyberattacks

The term "exploit chain" refers to a series of coordinated exploits that cyber attackers use to compromise a system or network. Exploit chains are constructed by sequencing multiple exploits together. The technique of chaining several exploits together to perform a single attack is known as an exploit chain.
This article explores the mechanics of exploit chains, their components, common exploit types, and how attackers use multiple vulnerabilities to achieve full system compromise. It also covers real-world examples, detection challenges, and best practices for defending against these sophisticated attacks. The content is designed for security professionals, IT teams, and anyone responsible for protecting organizational assets. Understanding exploit chains is essential for modern cybersecurity because attackers increasingly rely on these multi-stage attacks to bypass defenses, escalate privileges, and gain persistent access to critical systems.
What Are Exploit Chains?
Exploit chains are cyberattacks that group together multiple exploits to compromise a target. By combining several weaknesses, attackers can bypass traditional defenses and achieve far greater impact than exploiting a single vulnerability alone. This approach has become a defining characteristic of sophisticated cyberattacks targeting enterprises, cloud systems, and critical infrastructure.
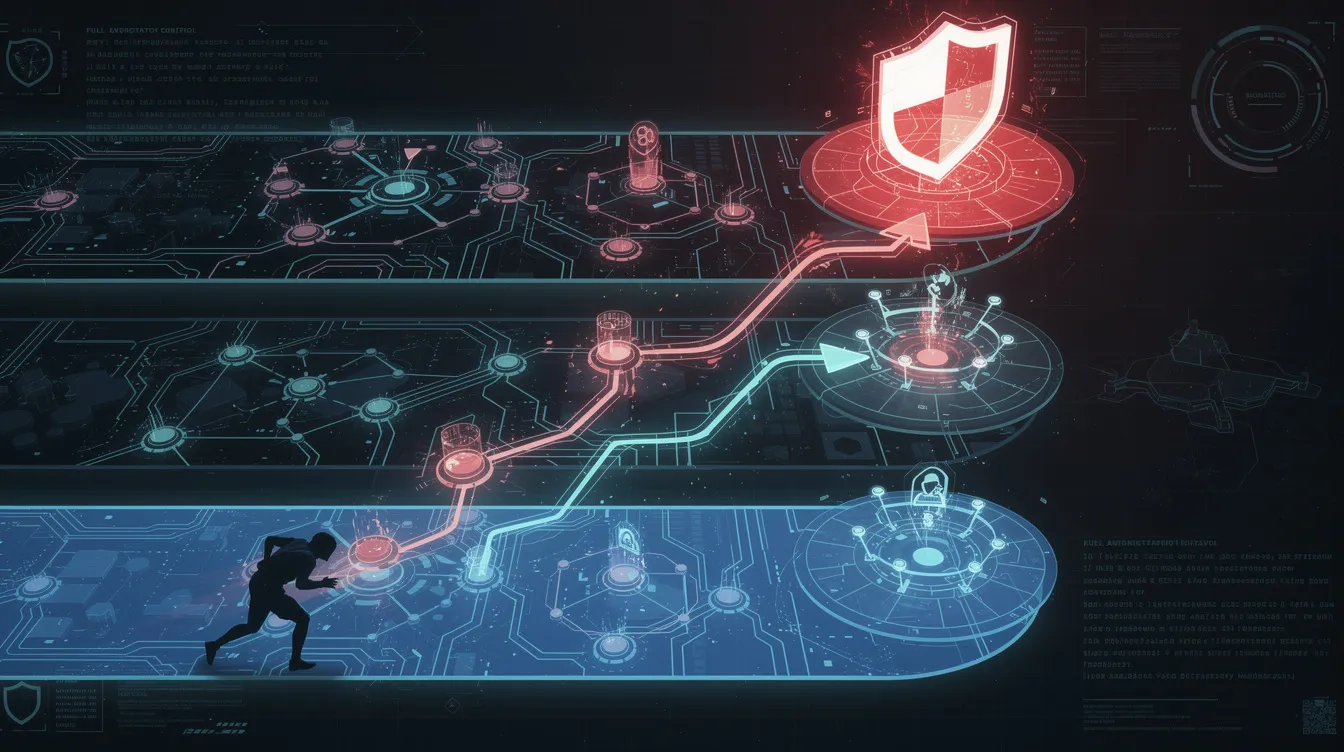
The concept of exploit chains is closely related to the attack lifecycle and frameworks like the Lockheed Martin Cyber Kill Chain, which emphasize the importance of defending against every stage in the process. Understanding the structure and function of exploit chains is the first step in building effective defenses.
In the following sections, we will break down the key components of exploit chains and how each stage contributes to a successful attack.
Exploit Chain Components
In today's threat landscape, cybercriminals have perfected the art of chaining together multiple exploits to devastating effect. An exploit chain represents a sophisticated attack methodology where threat actors orchestrate several coordinated components, each targeting distinct vulnerabilities within a target system or network.
Initial Access
The attack typically begins with initial access exploits that establish the first foothold. These may target software flaws, misconfigurations, or weaknesses in web applications, operating systems, or even human behavior, such as phishing emails or compromised credentials.
Privilege Escalation
After gaining initial access, attackers use privilege escalation techniques to expand their control within the environment. This often involves exploiting additional vulnerabilities to move from low-level user access to higher privileges, such as administrator or root access.
Achieving Code Execution
The final stage focuses on achieving arbitrary code execution — the ultimate goal that gives cybercriminals complete system control. Once this level of access is secured, threat actors can deploy malicious software, exfiltrate sensitive data, or systematically disrupt business operations.
Every vulnerability in the chain serves as a critical stepping stone, whether it's a software flaw, misconfiguration, or process weakness that brings attackers closer to their ultimate objective.
Breaking these attack chains has become a cornerstone of modern cybersecurity strategy. The next section will examine the specific types of exploits commonly used in these chains.
Types of Exploits
Modern cyberthreat actors have mastered the art of exploit chaining, weaving together multiple attack vectors to punch through even sophisticated security defenses. These coordinated assault strategies become exponentially more dangerous when they incorporate zero-day exploits — attacks that weaponize previously unknown vulnerabilities before security teams can develop patches or detection signatures.
Common Exploit Types
The building blocks of these attack chains frequently involve tried-and-true techniques, including:
- SQL Injection: Attackers manipulate database queries through vulnerable input fields to extract sensitive data or execute malicious code on backend systems.
- Cross-Site Scripting (XSS): Malicious scripts are injected into legitimate websites, executing in victims' browsers to steal credentials or install malware.
- Buffer Overflow: Attackers overwrite system memory and hijack control flow to run their own code with elevated permissions.
- Remote Code Execution (RCE): Exploiting vulnerabilities that allow attackers to run arbitrary code on a target system.
- Authentication Bypass: Exploiting flaws that allow attackers to circumvent authentication mechanisms.
What makes these individual techniques particularly menacing is how threat actors package them into comprehensive exploit kits — ready-made toolkits that can simultaneously probe for multiple vulnerabilities across a target's infrastructure.
Understanding these exploit types is crucial for recognizing how attackers combine them into powerful exploit chains, as discussed in the next section.
How Exploit Chains Use Multiple Vulnerabilities
Modern exploit chains rely on multiple vulnerabilities, such as software flaws and security weaknesses, to achieve success. A single vulnerability may only provide limited access, but when combined with other flaws, it can lead to complete system compromise.
Typical Exploit Chain Lifecycle
Attackers often follow a sequence of steps to execute an exploit chain:
- Reconnaissance: Identify minor weaknesses, such as a cross-site scripting flaw or SQL injection vulnerability, to gain initial access.
- Initial Exploit: Use the discovered vulnerability to enter the system.
- Privilege Escalation: Exploit additional vulnerabilities to escalate privileges and execute malicious code.
- Lateral Movement: Move deeper into the system or network, seeking further vulnerabilities.
- Execution: Achieve arbitrary code execution and full system compromise.
Preparation for an exploit chain may include identifying a minor bug in a browser to execute code, while execution requires the user to visit a malicious site.
Exploit chains are dangerous because individual vulnerabilities may appear low-risk in isolation. However, when combined, they can allow attackers to bypass security controls and achieve full compromise.
Many exploit chains involve multiple types of vulnerabilities, including remote code execution flaws, buffer overflows, and authentication bypass issues. This layered approach allows attackers to exploit weaknesses at different levels of the system.
The lifecycle of a zero-day exploit includes discovery, weaponization, delivery, and execution.
Understanding how attackers sequence these vulnerabilities is key to building effective defenses, which we will explore in the next section.
The Role of Privilege Escalation in Exploit Chains
One of the most critical stages in an exploit chain is privilege escalation. After gaining initial access, attackers seek to increase their level of control within the system.
Privilege escalation allows attackers to move from low-level user access to higher privileges, such as administrator or root access. This is often achieved by exploiting additional vulnerabilities within the operating system or applications.
Attackers may use several exploits in succession to escalate privileges repeatedly until they reach the highest level of access. Once they achieve this, they can execute arbitrary code, install malicious software, and gain complete control over the target system.
A third exploit targeting a kernel flaw can allow attackers to gain full system control, enabling malware installation, data theft, or unauthorized actions.
Privilege escalation is a pivotal step that enables attackers to maximize the impact of exploit chains, setting the stage for persistent compromise and lateral movement.
Zero Day Exploits and Zero Day Vulnerabilities
Zero day exploits play a major role in advanced exploit chains. Zero-day vulnerabilities are security flaws unknown to the software vendor, meaning no security patches exist at the time of exploitation.
Because these vulnerabilities are unknown, they are particularly dangerous. Attackers can exploit zero days without triggering traditional detection systems, allowing them to operate undetected for extended periods.
Exploits that remain unknown to everyone except the individuals who discovered them are referred to as zero-day or "0day" exploits. These vulnerabilities can remain undetected for months, quietly harvesting data or laying the groundwork for larger attacks.
Attackers often combine zero-day vulnerabilities into multi-stage exploit chains, where one flaw grants access and another escalates privileges. Once a zero-day successfully compromises a system, attackers establish persistence to maintain long-term access.
Zero-day vulnerabilities are a key enabler of sophisticated exploit chains, making proactive defense and threat intelligence essential.
Common Entry Points: SQL Injection and Cross Site Scripting
Many exploit chains begin with common vulnerabilities such as SQL injection or cross-site scripting. These flaws are often found in web applications and can provide attackers with an initial foothold.
- SQL Injection: Targets input fields in web applications, allowing attackers to execute arbitrary code against a database. This can expose sensitive data, user credentials, or system configurations.
- Cross-Site Scripting (XSS): Allows attackers to inject malicious scripts into web pages viewed by users. These scripts can steal session data, redirect users to malicious websites, or deliver additional payloads.
Attackers frequently use compromised websites to deliver these exploits, often through phishing or drive-by downloads, making it difficult for users to detect malicious activity until it is too late.
While these vulnerabilities may seem minor, they often serve as the first step in a larger exploit chain that leads to deeper system compromise.
Recognizing these entry points is vital for early detection and prevention, which leads us to the tools attackers use to automate these attacks.
Exploit Kits and Automated Exploitation
Modern attackers frequently rely on exploit kits and automated tools to execute exploit chains at scale. These kits contain pre-packaged exploits that target known vulnerabilities across different systems.
Exploit kits may include exploits that perform a sandbox escape to bypass browser restrictions and escalate privileges, allowing attackers to move beyond the initial browser environment and gain deeper access to the system.
Exploit kits can automatically scan for vulnerable systems, deliver malicious payloads, and execute multiple exploits in sequence. This automation allows attackers to launch large-scale attacks against multiple targets simultaneously.
The use of exploit chains is becoming more common as part of commoditized exploit toolkits used by ransomware groups and cybercriminal organizations. These tools lower the barrier to entry for attackers and increase the speed and scale of cyberattacks.
Understanding the role of automation in exploit chains highlights the need for robust, multi-layered defenses, which we will discuss next.
Achieving Code Execution and Complete Control
The ultimate goal of most exploit chains is to achieve code execution and gain complete control over the target system.
Arbitrary code execution allows attackers to run malicious code on a compromised system. This capability enables them to install malware, steal sensitive data, or manipulate system processes.
Once attackers achieve full control, they can establish persistence by creating backdoors, adding new user accounts, or modifying system configurations. These actions allow them to maintain access even if the initial vulnerability is patched.
Exploit chains often lead to full system compromise, where attackers gain complete control over devices, applications, and infrastructure.
With full control established, attackers can begin lateral movement, which is the focus of the next section.
Lateral Movement and Network Segmentation
After compromising a system, attackers often perform lateral movement to expand their access within the network. During this process, they gather more data as they move from one system to another to locate valuable information or additional vulnerabilities.

Lateral movement refers to attackers moving across the network to find valuable data or deploy ransomware. It allows attackers to target high-value systems, such as databases containing sensitive information or intellectual property. It is a critical phase in exploit chains, enabling attackers to maximize the impact of their attack.
Network segmentation can help limit the effectiveness of lateral movement by isolating systems and restricting access between network segments. Without proper segmentation, attackers can move freely across the network once initial access is gained.
Effective network segmentation is a key defense strategy, as we will see in the context of real-world attacks.
Real-World Example: Supply Chain Exploit Chains
One of the most notable examples of exploit chains in action is the SolarWinds attack. This incident involved a supply chain compromise where attackers inserted malicious code into a trusted software update.
By exploiting trust relationships between vendors and customers, attackers were able to bypass detection and gain access to multiple organizations. Attackers often leverage compromised infrastructure — systems that have already been infiltrated — to facilitate these exploit chains and further their reach. This type of chained attack demonstrates how exploit chains can combine multiple weaknesses across systems and organizations.
Supply chain exploit chains are particularly dangerous because they can impact large numbers of organizations simultaneously. Addressing exploit chains requires a coordinated effort between open-source communities and closed-source software vendors.
Learning from real-world incidents helps organizations understand the importance of comprehensive defense strategies, which we will discuss in the next section.
Why Exploit Chains Are Hard to Detect
Exploit chains are difficult to detect because they often mimic normal system behavior. Attackers use legitimate processes and existing system tools to blend in with normal network activity.
These attacks can involve multiple stages, each of which may appear harmless on its own. Intrusion detection systems may struggle to identify the full chain of events, especially when attackers use stealth techniques to evade detection.
Exploit chains also take advantage of gaps in security monitoring and are specifically designed to target vulnerabilities that may be hidden or unpatched, allowing attackers to operate undetected while progressing through different stages of the attack.
The complexity of exploit chains underscores the need for a multi-layered defense approach, which we will detail next.
Defending Against Exploit Chains
Defending against exploit chains requires a layered security strategy that addresses each stage of the attack lifecycle. Below are key defense strategies, each with its own role in breaking the attack chain.
Patch Management
- Regularly patch and update software to address known vulnerabilities.
- Stay updated on available patches to mitigate vulnerabilities before attackers can exploit them.
- Prioritize vulnerability management to reduce the attack surface.
Layered Security Controls
- Implement multiple layers of security controls, such as intrusion detection systems, endpoint protection, network monitoring, and application security tools.
- Use continuous monitoring and anomaly detection to identify unusual activity within the network.
- Employ defense-in-depth to ensure that if one layer fails, others can still provide protection.
Security Awareness
Security awareness training has emerged as one of the most effective countermeasures against sophisticated exploit chain attacks targeting modern organizations. The reality is stark: attackers consistently exploit human vulnerabilities as entry points, using convincing phishing campaigns, weaponized websites, and malicious attachments to establish their initial beachhead. Training programs that teach users to identify these threats — and understand why keeping systems patched matters — directly address the attack vectors that make exploit chains possible in the first place.
The connection between user education and vulnerability management represents a fundamental shift in how organizations approach defense. When users understand their role in the security ecosystem, they become active participants rather than passive targets. This awareness creates multiple failure points for attackers attempting to string together exploits. Well-informed employees who question suspicious emails and maintain updated systems effectively break the chain before it can fully develop, transforming the human element from the weakest link into a distributed early warning system that protects critical infrastructure and sensitive data.
Network Segmentation
- Segment networks to limit lateral movement and contain breaches.
- Restrict access between network segments to prevent attackers from moving freely once initial access is gained.
Threat Intelligence
In today's rapidly evolving cyber landscape, threat intelligence stands as a critical cornerstone for organizations defending against sophisticated exploit chain attacks. Security teams that continuously collect and analyze emerging threat data — from new vulnerabilities to attacker methodologies — gain the strategic advantage needed to stay one step ahead of adversaries. Real-time monitoring of network traffic for anomalous patterns and exploitation indicators allows defenders to identify active exploit chains before attackers can establish persistent footholds or exfiltrate sensitive data.
The most effective defense strategies extend beyond internal capabilities through strategic collaboration with the broader security research community and intelligence sharing with industry partners. This collective approach significantly amplifies an organization's visibility into novel attack vectors and emerging exploitation techniques. When organizations effectively harness threat intelligence feeds, they can make informed decisions about patch prioritization, deploy targeted countermeasures, and build robust defensive architectures that address the specific risks facing their infrastructure and critical assets.
Incident Response
When exploit chain attacks strike, the difference between containment and catastrophe often comes down to preparation. Security teams that invest in comprehensive incident response frameworks — complete with specialized personnel trained for rapid threat assessment — find themselves better positioned to weather these sophisticated attacks. Modern intrusion detection systems serve as the early warning network, flagging malicious activity as attackers attempt to pivot through vulnerable systems. The window for effective response narrows quickly, making swift patch deployment and targeted mitigation strategies critical for breaking the attack chain before adversaries can establish deeper footholds.
The real test of any incident response plan lies in execution under pressure. Organizations that establish clear communication protocols with key stakeholders can coordinate more effectively during the crucial investigation and containment phases, avoiding the confusion that often hampers recovery efforts. A structured approach to managing these overlapping processes — from initial detection through full system restoration — enables security teams to respond with precision rather than panic. Those who act decisively during these critical moments not only minimize operational disruption but also emerge with stronger defensive postures, having identified and addressed the vulnerabilities that made the attack possible in the first place.
A robust cybersecurity program focuses on breaking every link in the chain. Even if attackers gain initial access, stopping later stages such as privilege escalation or lateral movement can prevent full system compromise.
The Future of Exploit Chains
Exploit chains are becoming more sophisticated as attackers continue to develop new techniques and tools in the context of an evolving cyber attack landscape. The increasing use of zero-day vulnerabilities and automated exploit kits is making these attacks more accessible and effective.
As organizations adopt complex environments, including cloud systems and distributed networks, the attack surface continues to grow. This creates more opportunities for attackers to chain vulnerabilities together. Attackers are also increasingly focusing on high value targets, such as critical infrastructure and sensitive data.
To stay ahead of these threats, organizations must adopt proactive security strategies, invest in advanced detection capabilities, and prioritize vulnerability remediation. Businesses will lose the game unless they have a strategy to address vulnerabilities before it is too late, prioritizing based on their own particular business needs.
Exploit chains represent one of the most advanced forms of cyberattack today, and defending against them requires a coordinated, multi-layered approach.
FAQ
What are exploit chains?
Exploit chains are cyberattacks that combine multiple exploits to compromise a system or network and achieve greater impact than a single vulnerability.
Why are exploit chains dangerous?
Exploit chains are dangerous because they combine multiple vulnerabilities, allowing attackers to escalate privileges, move laterally, and gain full system control.
What role do zero-day vulnerabilities play in exploit chains?
Zero-day vulnerabilities are often used in exploit chains because they are unknown to vendors and lack security patches, making them difficult to detect and defend against.
How do attackers achieve privilege escalation?
Attackers exploit additional vulnerabilities within a system to increase their access level, eventually gaining administrative or root privileges.
How can organizations defend against exploit chains?
Organizations can defend against exploit chains by implementing layered security controls, patching vulnerabilities, using network segmentation, and monitoring for suspicious activity.




