Iran-Linked Handala Leaks 2,379 US Marines' Data and Sends Chilling WhatsApp Threats
Iran-linked Handala published the names and phone numbers of 2,379 US Marines and sent direct WhatsApp threats warning of drone and missile strikes — a hybrid psychological operation attributed to Iran's MOIS.
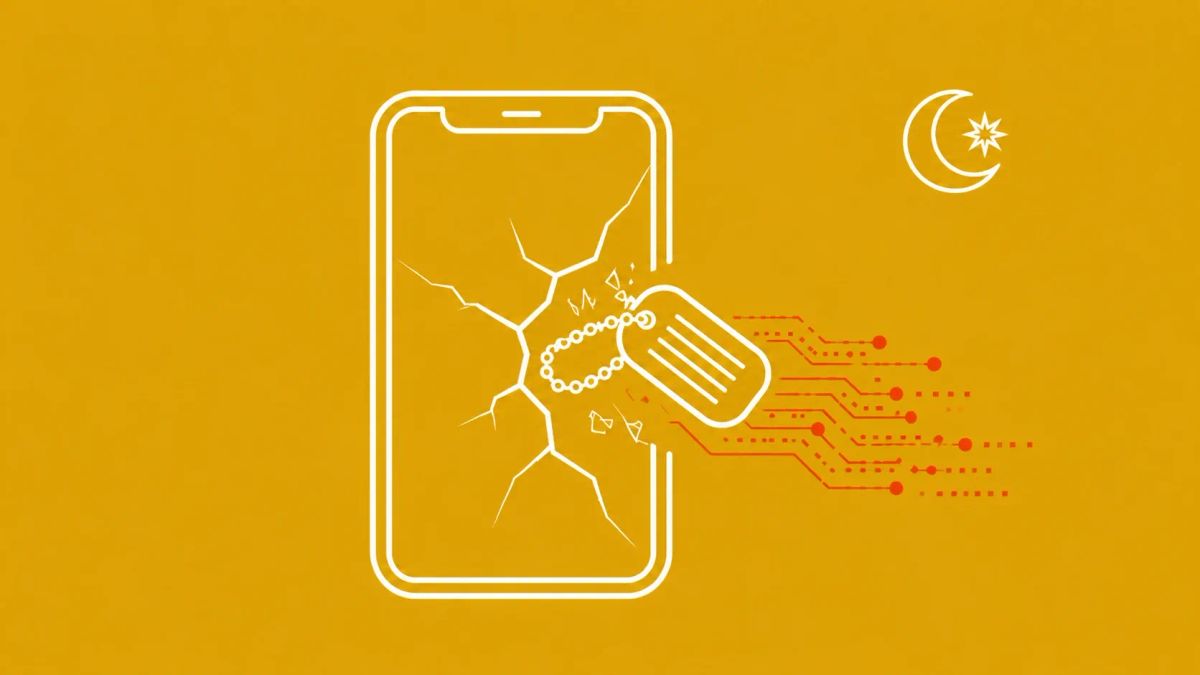
Iran-linked Handala published 2,379 US Marines' personal details and sent direct WhatsApp missile threats — a MOIS-attributed psychological operation targeting active-duty service members in Bahrain.
BAHRAIN — Active-duty US service members received messages from what appeared to be a Bahraini business phone number — most likely spoofed or hijacked. The messages, reviewed by Stars and Stripes, warned of targeting by Shahed drones and Kheibar and Ghadeer missiles and told recipients to "call your families now and say your final goodbyes." A day later, Handala published what it claimed were the personal details of 2,379 US Marines on Telegram, calling it proof of "intelligence superiority." The group claims to hold detailed data on tens of thousands of additional US personnel including home addresses, family details, and daily routines — though these claims have not been independently verified.
Incident profile
The operation: from WhatsApp to Telegram
The campaign unfolded in two phases. First, direct personal WhatsApp messages were sent to Marines in Bahrain referencing specific Iranian weapons systems. The number appeared to belong to a local Bahraini business, suggesting spoofing or SIM hijacking. The following day, Handala announced on Telegram it had published 2,379 Marines' personal details. US Central Command referred Stars and Stripes to NCIS, which did not immediately respond. The Navy had already warned service members this month to secure their personal devices against an "ongoing social engineering campaign" — the Handala operation is the materialization of that warning.
Handala's 2026 escalation
Handala appeared in December 2023, riding the wave of pro-Palestinian hacktivist activity following October 7. The DOJ publicly identifies it as a MOIS cover operation. In 2026 alone, the group has claimed a wiper attack against Stryker (tens of thousands of devices destroyed), the breach of FBI Director Kash Patel's personal Gmail, and the doxxing of 28 Lockheed Martin engineers in Israel. The Marines operation follows the same doctrine: psychological pressure through personal channels, targeting individuals and families rather than infrastructure alone. For broader context on how state-sponsored threat actors operate, see our coverage of the nation-state cyber threats driving the 2026 threat landscape.
Verification caveats
Handala has a documented history of recycling older breach data and padding leaks with open-source intelligence from data brokers and social media. The "2,379 Marines" dataset may have been assembled from directories, LinkedIn profiles, and commercially available data rather than any breach of military systems. What is not in doubt: the WhatsApp messages were real, were received by real service members, and had a genuine psychological impact. Whether Handala's claimed intelligence depth is real or constructed, the goal — making US troops feel personally surveilled — does not require the claims to be true.
What to do now
US military personnel and government employees with Middle East deployment history should immediately lock down social media profiles, remove location data and unit identifiers, and alert family members not to post about service member whereabouts. Any threatening messages received via personal devices should be reported to NCIS. Review LinkedIn and professional profile privacy settings — data brokers harvest extensively from professional networks. To understand how these operations fit into a broader pattern of advanced persistent threats, our explainer covers the full lifecycle of state-sponsored intrusion campaigns. This operation mirrors the extradition case of Silk Typhoon operative Xu Zewei — covered here — where state-directed actors target US institutions with impunity from abroad.
The CyberSignal Analysis
Signal 01 — This is a hybrid operation, not a breach
The Handala campaign combines psychological pressure with intelligence display regardless of whether the data came from a genuine breach or open-source aggregation. The goal is behavioral: make service members feel exposed and erode individual operational confidence. This is MOIS doctrine applied to the digital environment. The attack's effectiveness does not depend on the data being accurate — only on the target believing it might be.
Signal 02 — Personal devices are now front-line attack surfaces
Using WhatsApp to deliver threats to service members' personal phones exploits a fundamental security gap: the boundary between personal and professional life is permeable for individual personnel. Personal messaging apps, personal devices, and personal social media profiles are now adversary targeting surfaces that no amount of corporate firewall protects against.
Signal 03 — Iran is escalating direct confrontation with US personnel
Handala's shift from Israeli infrastructure and US corporations to directly messaging US Marines represents a doctrinal escalation timed precisely to US-Iran tensions following strikes on Iran in late February 2026. The psychological pressure campaign on individual service members compounds strategic pressure through military channels. This is not a one-off stunt — it is a deliberate escalation ladder.