Fake CAPTCHA / IRSF Scam and 120 Keitaro Campaigns Drive Global SMS, Crypto Fraud
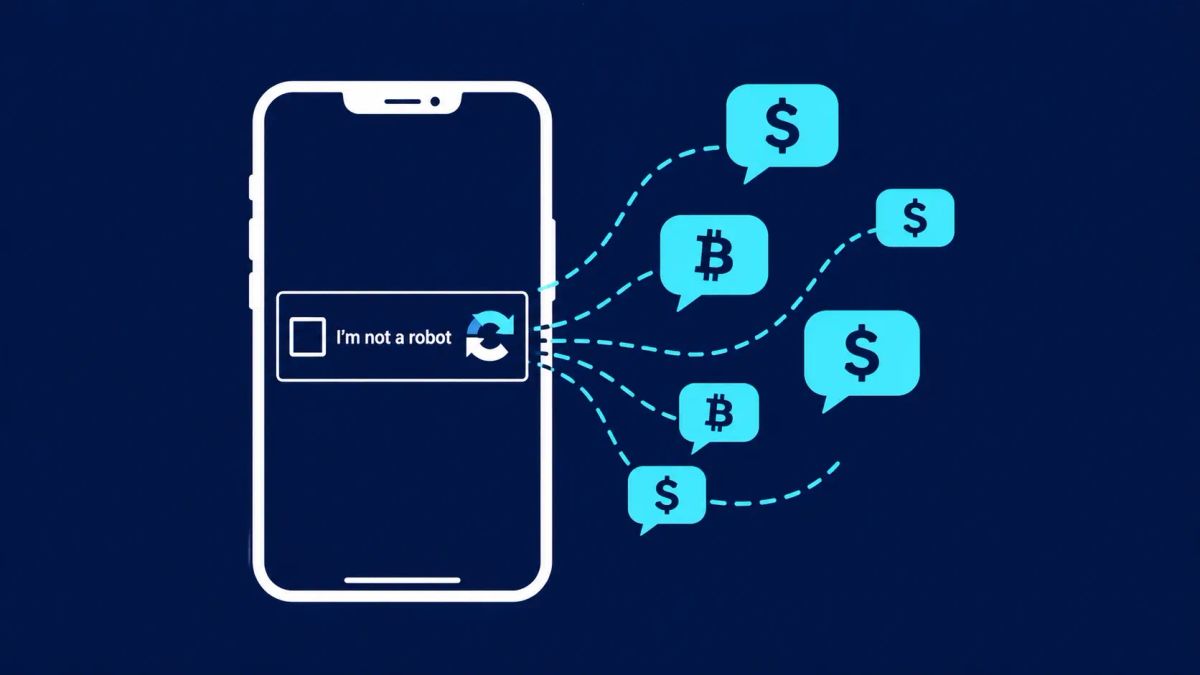
A newly-detailed telecommunications fraud campaign uses fake CAPTCHA verification prompts to trick users into sending up to 60 international SMS messages, quietly adding tens of dollars to phone bills while Keitaro traffic distribution campaigns drive parallel crypto-wallet drainer scams.
SANTA CLARA, CALIFORNIA — Security researchers have uncovered a massive, multi-channel fraud ecosystem that weaponizes the one thing internet users have been trained to trust: the CAPTCHA. By blending International Revenue Share Fraud (IRSF) with sophisticated crypto-wallet drainers, attackers are simultaneously draining physical phone bills and digital wallets. This operation, fueled by over 120 distinct traffic distribution campaigns, represents a "full-stack" approach to consumer fraud that bypasses traditional security awareness by mimicking legitimate human-verification checks.
Incident Profile: The CAPTCHA-to-IRSF Attack Chain
The Mechanism: How Fake CAPTCHAs Trigger IRSF
International Revenue Share Fraud (IRSF) is a classic telecom scam where attackers lease international numbers in regions with high termination fees. In this new variant, users are funneled through Keitaro Traffic Distribution Systems (TDS) via malicious ads or search redirects to a page that looks like a standard "I am not a robot" check.
Instead of clicking images, the user is prompted to click a button that opens their mobile messaging app with a pre-filled, multi-recipient SMS. The CAPTCHA claims that sending the code is required to verify the user’s session. In reality, a single "verification" flow can trick a user into sending up to 60 SMS messages to 15 different high-cost international numbers. This can add approximately $30 to a phone bill in seconds — charges that often go unnoticed until weeks later when the bill arrives.
Keitaro TDS: The Engine of Multi-Channel Fraud
Researchers from Infoblox have identified more than 120 distinct Keitaro-driven campaigns operating in parallel. While the fake CAPTCHA handles the telecom fraud, the TDS also redirects users to:
- AI-Themed Investment Lures: Using deepfake technology and fake news hype to steal fiat currency.
- Crypto Wallet Drainers: Promoting fake airdrops (e.g., SOL, Phantom, Jupiter) that trick users into signing malicious "SetApprovalForAll" transactions, instantly emptying their digital assets.
What to Do Now: Immediate Actions
- Never SMS for CAPTCHA: Treat any website that asks you to send an SMS to "prove you're human" as 100% malicious. Legitimate CAPTCHAs (like hCaptcha or reCAPTCHA) never require outgoing SMS.
- Audit Phone Bills: Check your monthly telecom statements for "International SMS" or "Premium Messaging" charges. If you see $20-$40 spikes, you may have been a victim of an IRSF flow.
- Disable SMS for Crypto 2FA: Move away from SMS-based 2FA for crypto exchanges and wallets. Use TOTP (Authenticator apps) or hardware keys (Yubikey) to prevent session hijacking.
- Block Pre-filled SMS: Be wary of pop-ups that attempt to open your "Messages" app with a list of unfamiliar international recipients.
The CyberSignal Analysis: Strategic Signals
Signal 01 — The "Micro-Loss" Aggregation Strategy
This campaign proves that attackers are moving away from "all-or-nothing" hacks toward high-volume, low-friction "micro-losses." By stealing $30 from 100,000 users via their phone bills, attackers generate $3 million in revenue with almost zero risk of law enforcement intervention, as most users won't file a police report over a $30 billing discrepancy.
Signal 02 — The Convergence of Telecom and Crypto Fraud
Attackers are no longer staying in their silos. By using a single TDS (Keitaro) to manage both IRSF and crypto wallet drainers, they maximize the "yield" of every single click. If a user isn't a crypto investor, the attacker still makes money via the SMS fraud.
Signal 03 — The "Delayed Billing" Security Gap
The primary strength of IRSF is the time-gap. Because phone bills are monthly, the victim remains unaware of the theft for up to 30 days. This creates a "memory gap" where the user cannot remember which website they visited that caused the charge, making it nearly impossible to trace the malicious domain before it is rotated by the Keitaro system.




