30,000 Facebook Business Accounts Stolen via Google AppSheet Phishing — "AccountDumpling" Operation Exposed
Vietnamese-linked operation "AccountDumpling" has compromised 30,000 Facebook Business accounts by sending phishing emails from Google's legitimate AppSheet address — bypassing spam filters and running a criminal resale storefront for stolen accounts.
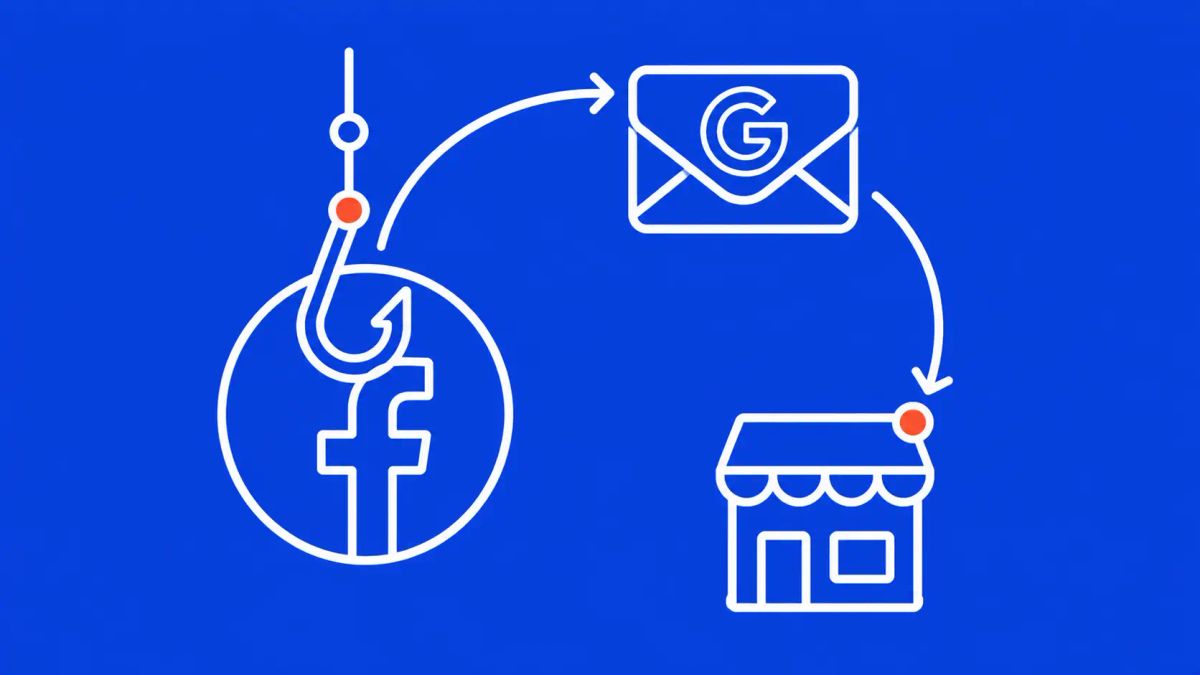
A Vietnamese-linked threat operation dubbed "AccountDumpling" has compromised approximately 30,000 Facebook Business accounts using Google AppSheet as a phishing relay — sending fraudulent emails from a legitimate Google address to bypass spam filters, then reselling stolen accounts through a criminal storefront run by the same group.
SAN FRANCISCO / HO CHI MINH CITY — Guardio security researchers disclosed the AccountDumpling campaign on May 1, 2026, revealing a sophisticated Vietnamese-linked operation that has compromised approximately 30,000 Facebook Business accounts by abusing Google AppSheet as a trusted phishing relay. Phishing emails sent from the legitimate "noreply@appsheet.com" Google address bypass traditional spam filters that would flag messages from unknown domains — giving the campaign an unusually high delivery rate to targeted Facebook Business account owners. The operation is not a simple phishing campaign: it features real-time operator panels, continuous evolution of lure types, and a criminal resale loop in which the same group that steals the accounts also runs an illicit storefront selling access back to the criminal market.
Campaign Profile
The AppSheet Relay Technique
Traditional phishing detection relies heavily on sender domain reputation — emails from newly registered domains or known malicious addresses are flagged or blocked before reaching inboxes. AccountDumpling bypasses this by abusing Google AppSheet's legitimate email notification infrastructure. AppSheet is Google's no-code application platform, and its notification system sends emails from noreply@appsheet.com — a Google-owned domain with impeccable sender reputation. By creating AppSheet automations that trigger phishing email sends, attackers get their phishing content delivered via Google's own mail servers with Google's own DMARC, DKIM, and SPF records intact. The receiving spam filter sees a legitimate Google business email and passes it through. The phishing content claims to be from Meta Support, warns of imminent account disablement, and directs victims to Netlify-hosted fake Facebook help center pages that collect credentials and additional personal data in staged verification flows. Four distinct attack cluster variations were identified, each with different lure themes but the same underlying infrastructure pattern.
Why Facebook Business Accounts Are the Target
A compromised standard Facebook account has limited criminal value. A compromised Facebook Business account is significantly more valuable: it carries established ad spend history that allows immediate launch of fraudulent advertising campaigns before Meta's fraud detection flags the account, business verification status that bypasses many of Meta's protective restrictions, access to business payment methods, and the advertising infrastructure needed to run further phishing or scam campaigns at scale. The AccountDumpling criminal storefront sells not just account access but also the associated business identity and ad reputation — monetizing every component of the stolen account's value separately. For broader context on the most common cybersecurity threats in 2026. All phishing coverage is tracked on The CyberSignal.
What to do now
Facebook Business account owners should enable login alerts and two-factor authentication using a hardware security key or authenticator app — not SMS. Be highly skeptical of any email claiming to be from Meta Support regardless of the sending address, including emails appearing to come from Google domains. Never click links in account warning emails — navigate directly to business.facebook.com and check the Support Inbox there for any genuine communications from Meta. If you manage Facebook Business accounts on behalf of clients, audit business admin access and remove any unrecognized administrators. Enable Meta's Advanced Security settings and review active sessions for any unrecognized logins.
The CyberSignal Analysis
Signal 01 — Trusted Platform Abuse Has Outpaced Email Security
AccountDumpling's abuse of Google AppSheet reflects the same fundamental problem documented across dozens of phishing campaigns in 2025 and 2026: legitimate cloud platforms — Google, Microsoft, Salesforce, Dropbox, Notion — are being systematically abused as phishing relays precisely because their sending reputation bypasses the email security controls organizations have invested in. The more sophisticated email security becomes at detecting malicious domains, the more valuable legitimate cloud platform abuse becomes. This is an arms race that current email security architectures are structurally losing.
Signal 02 — The Criminal Resale Loop Is the Innovation
Guardio's description of AccountDumpling as "a living operation with real-time operator panels" is the key insight. This is not a theft-and-liquidate operation — it is a vertically integrated criminal business that steals accounts, maintains those accounts, and sells multiple components of their value (access, ad reputation, business identity, recovery services) through its own storefront. The sophistication of the commercial operation around the stolen accounts often exceeds the sophistication of the initial theft. This model maximizes revenue per compromised account and creates ongoing criminal infrastructure that persists well beyond any single campaign.
Signal 03 — Vietnamese Threat Actors Have Industrialized Facebook Business Account Fraud
AccountDumpling is the latest in a documented wave of Vietnamese-linked Facebook Business account fraud campaigns that have been active since at least 2023. The playbook — abuse of trusted platforms, fake Meta support pages, credential and cookie theft, criminal resale infrastructure — has been refined through dozens of iterations. Guardio noted that "the same AI-branded service ads are copied and pasted across multiple forums and Telegram channels" suggesting commoditization of the tooling and methodology across the Vietnamese cybercriminal ecosystem, not just a single group.